Tested EC-Council 412-79v9 Practice Question Online
we provide Guaranteed EC-Council 412-79v9 book which are the best for clearing 412-79v9 test, and to get certified by EC-Council EC-Council Certified Security Analyst (ECSA) v9. The 412-79v9 Questions & Answers covers all the knowledge points of the real 412-79v9 exam. Crack your EC-Council 412-79v9 Exam with latest dumps, guaranteed!
Online EC-Council 412-79v9 free dumps demo Below:
NEW QUESTION 1
The Web parameter tampering attack is based on the manipulation of parameters exchanged between client and server in order to modify application data, such as user credentials and permissions, price and quantity of products, etc. Usually, this information is stored in cookies, hidden form fields, or URL Query Strings, and is used to increase application functionality and control.
This attack takes advantage of the fact that many programmers rely on hidden or fixed fields (such as a hidden tag in a form or a parameter in a URL) as the only security measure for certain operations. Attackers can easily modify these parameters to bypass the security mechanisms that rely on them.
What is the best way to protect web applications from parameter tampering attacks?
- A. Validating some parameters of the web application
- B. Minimizing the allowable length of parameters
- C. Using an easily guessable hashing algorithm
- D. Applying effective input field filtering parameters
Answer: D
NEW QUESTION 2
A framework is a fundamental structure used to support and resolve complex issues. The framework that delivers an efficient set of technologies in order to develop applications which are more secure in using Internet and Intranet is:
- A. Microsoft Internet Security Framework
- B. Information System Security Assessment Framework (ISSAF)
- C. Bell Labs Network Security Framework
- D. The IBM Security Framework
Answer: A
NEW QUESTION 3
Traceroute is a computer network diagnostic tool for displaying the route (path) and measuring transit delays of packets across an Internet Protocol (IP) network. It sends a sequence of three Internet Control Message Protocol (ICMP) echo request packets addressed to a destination host.
The time-to-live (TTL) value, also known as hop limit, is used in determining the intermediate routers being traversed towards the destination.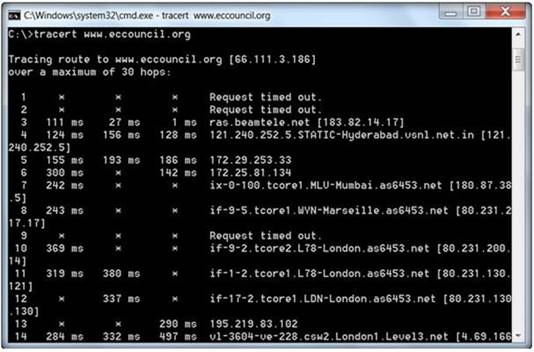
During routing, each router reduces packets' TTL value by
- A. 3
- B. 1
- C. 4
- D. 2
Answer: B
Explanation:
Reference: http://www.packetu.com/2009/10/09/traceroute-through-the-asa/
NEW QUESTION 4
Firewall and DMZ architectures are characterized according to its design. Which one of the following architectures is used when routers have better high-bandwidth data stream handling capacity?
- A. Weak Screened Subnet Architecture
- B. "Inside Versus Outside" Architecture
- C. "Three-Homed Firewall" DMZ Architecture
- D. Strong Screened-Subnet Architecture
Answer: A
NEW QUESTION 5
Which of the following acts is a proprietary information security standard for organizations that handle cardholder information for the major debit, credit, prepaid, e-purse, ATM, and POS cards and applies to all entities involved in payment card processing?
- A. PIPEDA
- B. PCI DSS
- C. Human Rights Act 1998
- D. Data Protection Act 1998
Answer: B
Explanation:
Reference: http://en.wikipedia.org/wiki/Payment_Card_Industry_Data_Security_Standard
NEW QUESTION 6
During the process of fingerprinting a web application environment, what do you need to do in order to analyze HTTP and HTTPS request headers and the HTML source code?
- A. Examine Source of the Available Pages
- B. Perform Web Spidering
- C. Perform Banner Grabbing
- D. Check the HTTP and HTML Processing by the Browser
Answer: D
NEW QUESTION 7
Identify the type of testing that is carried out without giving any information to the employees or administrative head of the organization.
- A. Unannounced Testing
- B. Double Blind Testing
- C. Announced Testing
- D. Blind Testing
Answer: B
NEW QUESTION 8
A directory traversal (or path traversal) consists in exploiting insufficient security validation/sanitization of user-supplied input file names, so that characters representing "traverse to parent directory" are passed through to the file APIs.
The goal of this attack is to order an application to access a computer file that is not intended to be accessible. This attack exploits a lack of security (the software is acting exactly as it is supposed to) as opposed to exploiting a bug in the code.
To perform a directory traversal attack, which sequence does a pen tester need to follow to manipulate variables of reference files?
- A. dot-dot-slash (../) sequence
- B. Denial-of-Service sequence
- C. Brute force sequence
- D. SQL Injection sequence
Answer: A
Explanation:
Reference: https://www.cs.ucsb.edu/~vigna/publications/2010_doupe_cova_vigna_dimva10.pdf (pae 7, directory traversal)
NEW QUESTION 9
Identify the transition mechanism to deploy IPv6 on the IPv4 network from the following diagram.
- A. Translation
- B. Tunneling
- C. Dual Stacks
- D. Encapsulation
Answer: B
NEW QUESTION 10
Internet Control Message Protocol (ICMP) messages occur in many situations, such as whenever a datagram cannot reach the destination or the gateway does not have the buffering capacity to forward a datagram. Each ICMP message contains three fields: type, code, and checksum. Different types of Internet Control Message Protocols (ICMPs) are identified by a TYPE field. If the destination is not reachable, which one of the following are generated?
- A. Type 8 ICMP codes
- B. Type 12 ICMP codes
- C. Type 3 ICMP codes
- D. Type 7 ICMP codes
Answer: C
NEW QUESTION 11
Which one of the following 802.11 types has WLAN as a network support?
- A. 802.11b
- B. 802.11-Legacy
- C. 802.11n
- D. 802.11g
Answer: C
NEW QUESTION 12
Variables are used to define parameters for detection, specifically those of your local network and/or specific servers or ports for inclusion or exclusion in rules. These are simple substitution variables set with the var keyword. Which one of the following operator is used to define meta-variables?
- A. “$”
- B. “#”
- C. “*”
- D. “?”
Answer: A
NEW QUESTION 13
Black-box testing is a method of software testing that examines the functionality of an application (e.g. what the software does) without peering into its internal structures or workings. Black-box testing is used to detect issues in SQL statements and to detect SQL injection vulnerabilities.
Most commonly, SQL injection vulnerabilities are a result of coding vulnerabilities during the Implementation/Development phase and will likely require code changes.
Pen testers need to perform this testing during the development phase to find and fix the SQL injection vulnerability.
What can a pen tester do to detect input sanitization issues?
- A. Send single quotes as the input data to catch instances where the user input is not sanitized
- B. Send double quotes as the input data to catch instances where the user input is not sanitized
- C. Send long strings of junk data, just as you would send strings to detect buffer overruns
- D. Use a right square bracket (the “]” character) as the input data to catch instances wherethe user input is used as part of a SQL identifier without any input sanitization
Answer: D
NEW QUESTION 14
A penetration test consists of three phases: pre-attack phase, attack phase, and post- attack phase.
Active reconnaissance which includes activities such as network mapping, web profiling, and perimeter mapping is a part which phase(s)?
- A. Post-attack phase
- B. Pre-attack phase and attack phase
- C. Attack phase
- D. Pre-attack phase
Answer: D
Explanation:
Reference: https://www.duo.uio.no/bitstream/handle/10852/34904/Shrestha-masterthesis.pdf?sequence=1 (page 28, first para)
NEW QUESTION 15
Today, most organizations would agree that their most valuable IT assets reside within applications and databases. Most would probably also agree that these are areas that have the weakest levels of security, thus making them the prime target for malicious activity from system administrators, DBAs, contractors, consultants, partners, and customers.
Which of the following flaws refers to an application using poorly written encryption code to securely encrypt and store sensitive data in the database and allows an attacker to steal or modify weakly protected data such as credit card numbers, SSNs, and other authentication credentials?
- A. SSI injection attack
- B. Insecure cryptographic storage attack
- C. Hidden field manipulation attack
- D. Man-in-the-Middle attack
Answer: B
NEW QUESTION 16
Identify the policy that defines the standards for the organizational network connectivity and security standards for computers that are connected in the organizational network.
- A. Information-Protection Policy
- B. Special-Access Policy
- C. Remote-Access Policy
- D. Acceptable-Use Policy
Answer: C
NEW QUESTION 17
What information can be collected by dumpster diving?
- A. Sensitive documents
- B. Email messages
- C. Customer contact information
- D. All the above
Answer: A
Explanation:
Reference: http://www.spamlaws.com/dumpster-diving.html
NEW QUESTION 18
Transmission Control Protocol (TCP) is a connection-oriented four layer protocol. It is responsible for breaking messages into segments, re-assembling them at the destination
station, and re-sending. Which one of the following protocols does not use the TCP?
- A. Reverse Address Resolution Protocol (RARP)
- B. HTTP (Hypertext Transfer Protocol)
- C. SMTP (Simple Mail Transfer Protocol)
- D. Telnet
Answer: A
NEW QUESTION 19
Application security assessment is one of the activity that a pen tester performs in the attack phase. It is designed to identify and assess threats to the organization through bespoke, proprietary applications or systems. It checks the application so that a malicious user cannot access, modify, or destroy data or services within the system.
Identify the type of application security assessment which analyzes the application-based code to confirm that it does not contain any sensitive information that an attacker might use to exploit an application.
- A. Web Penetration Testing
- B. Functionality Testing
- C. Authorization Testing
- D. Source Code Review
Answer: D
NEW QUESTION 20
Many security and compliance projects begin with a simple idea: assess the organization's risk, vulnerabilities, and breaches. Implementing an IT security risk assessment is critical to the overall security posture of any organization.
An effective security risk assessment can prevent breaches and reduce the impact of realized breaches.
What is the formula to calculate risk?
- A. Risk = Budget x Time
- B. Risk = Goodwill x Reputation
- C. Risk = Loss x Exposure factor
- D. Risk = Threats x Attacks
Answer: C
NEW QUESTION 21
Identify the data security measure which defines a principle or state that ensures that an action or transaction cannot be denied.
- A. Availability
- B. Integrity
- C. Authorization
- D. Non-Repudiation
Answer: D
Explanation:
Reference: http://en.wikipedia.org/wiki/Information_security (non-repudiation)
NEW QUESTION 22
An external intrusion test and analysis identify security weaknesses and strengths of the client's systems and networks as they appear from outside the client's security perimeter, usually from the Internet. The goal of an external intrusion test and analysis is to demonstrate the existence of known vulnerabilities that could be exploited by an external attacker.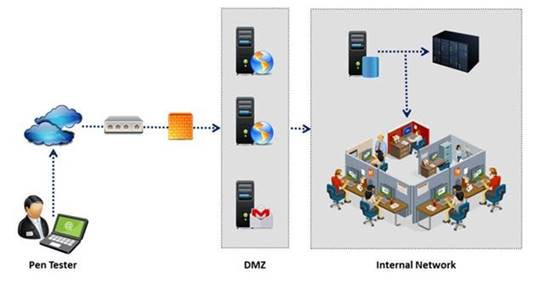
During external penetration testing, which of the following scanning techniques allow you to determine a port’s state without making a full connection to the host?
- A. XMAS Scan
- B. SYN scan
- C. FIN Scan
- D. NULL Scan
Answer: B
NEW QUESTION 23
Packet filtering firewalls are usually a part of a router. In a packet filtering firewall, each packet is compared to a set of criteria before it is forwarded.
Depending on the packet and the criteria, the firewall can: i)Drop the packet
ii) Forward it or send a message to the originator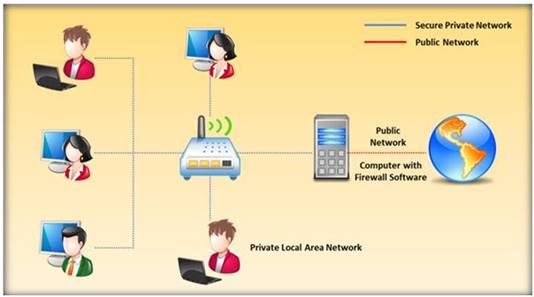
At which level of the OSI model do the packet filtering firewalls work?
- A. Application layer
- B. Physical layer
- C. Transport layer
- D. Network layer
Answer: D
Explanation:
Reference: http://books.google.com.pk/books?id=KPjLAyA7HgoC&pg=PA208&lpg=PA208&dq=At+whi ch+level+of+the+OSI+model+do+the+packet+filtering+firewalls+work&source=bl&ots=zRrbcmY3pj&sig=I3vuS3VA7r- 3VF8lC6xq_c_r31M&hl=en&sa=X&ei=wMcfVMetI8HPaNSRgPgD&ved=0CC8Q6AEwAg#v
=onepage&q=At%20which%20level%20of%20the%20OSI%20model%20do%20the%20pa cket%20filtering%20firewalls%20work&f=false (packet filters)
NEW QUESTION 24
Identify the type of authentication mechanism represented below: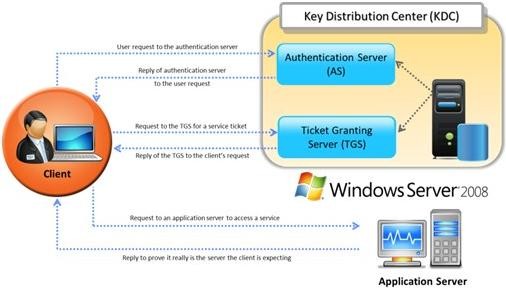
- A. NTLMv1
- B. NTLMv2
- C. LAN Manager Hash
- D. Kerberos
Answer: D
Explanation:
The client authenticates itself to the Authentication Server (AS) which forwards the username to a key distribution center (KDC). The KDC issues a ticket granting ticket (TGT), which is time stamped, encrypts it using the user's password and returns the encrypted result to the user's workstation. This is done infrequently, typically at user logon; the TGT expires at some point, though may be transparently renewed by the user's session manager while they are logged in.
When the client needs to communicate with another node ("principal" in Kerberos parlance) the client sends the TGT to the ticket granting service (TGS), which usually shares the same host as the KDC. After verifying the TGT is valid and the user is permitted to access the requested service, the TGS issues a ticket and session keys, which are returned to the client. The client then sends the ticket to the service server (SS) along with its service request.
Reference: http://en.wikipedia.org/wiki/Kerberos_(protocol)
NEW QUESTION 25
Which of the following is the objective of Gramm-Leach-Bliley Act?
- A. To ease the transfer of financial information between institutions and banks
- B. To protect the confidentiality, integrity, and availability of data
- C. To set a new or enhanced standards for all U.
- D. public company boards, management and public accounting firms
- E. To certify the accuracy of the reported financial statement
Answer: A
Explanation:
Reference: http://www.itap.purdue.edu/security/policies/glb_safeguards_rule_training_general.pdf
NEW QUESTION 26
Transmission control protocol accepts data from a data stream, divides it into chunks, and adds a TCP header creating a TCP segment.
The TCP header is the first 24 bytes of a TCP segment that contains the parameters and state of an end-to-end TCP socket. It is used to track the state of communication between two TCP endpoints.
For a connection to be established or initialized, the two hosts must synchronize. The synchronization requires each side to send its own initial sequence number and to receive a confirmation of exchange in an acknowledgment (ACK) from the other side
The below diagram shows the TCP Header format:
How many bits is a acknowledgement number?
- A. 16 bits
- B. 32 bits
- C. 8 bits
- D. 24 bits
Answer: B
Explanation:
Reference: http://en.wikipedia.org/wiki/Transmission_Control_Protocol (acknowledgement number)
NEW QUESTION 27
......
Recommend!! Get the Full 412-79v9 dumps in VCE and PDF From Surepassexam, Welcome to Download: https://www.surepassexam.com/412-79v9-exam-dumps.html (New 203 Q&As Version)