Improve 210-255 Braindumps 2021
we provide Vivid Cisco 210-255 simulations which are the best for clearing 210-255 test, and to get certified by Cisco Implementing Cisco Cybersecurity Operations. The 210-255 Questions & Answers covers all the knowledge points of the real 210-255 exam. Crack your Cisco 210-255 Exam with latest dumps, guaranteed!
Cisco 210-255 Free Dumps Questions Online, Read and Test Now.
NEW QUESTION 1
Which element is included in an incident response plan?
- A. organization mission
- B. junior analyst approval
- C. day-to-day firefighting
- D. siloed approach to communications
Answer: A
Explanation:
The incident response plan should include the following elements:
– Mission– Strategies and goals– Senior management approval– Organizational approach to incident response– How the incident response team will communicate with the rest of the organization and with other organizations– Metrics for measuring the incident response capability and its effectiveness– Roadmap for maturing the incident response capability– How the program fits into the overall organization.
NEW QUESTION 2
What is the difference between deterministic and probabilistic assessment method? (Choose Two)
- A. At deterministic method we know the facts beforehand and at probabilistic method we make assumptions
- B. At probabilistic method we know the facts beforehand and at deterministic method we make assumptions
- C. Probabilistic method has an absolute nature
- D. Deterministc method has an absolute nature
Answer: AD
NEW QUESTION 3
A CMS plugin creates two files that are accessible from the Internet myplugin.html and exploitable.php. A newly discovered exploit takes advantage of an injection vulnerability in exploitable.php. To exploit the vulnerability, one must send an HTTP POST with specific variables to exploitable.php. You see traffic to your webserver that consists of only HTTP GET requests to myplugin.html. Which category best describes this activity?
- A. weaponization
- B. exploitation
- C. installation
- D. reconnaissance
Answer: D
NEW QUESTION 4
Which CSIRT category provides incident handling services to their parent organization such as a bank, a manufacturing company, a university, or a federal agency?
- A. internal CSIRT
- B. national CSIRT
- C. coordination centers
- D. analysis centers
- E. vendor teams
- F. incident response providers
Answer: A
NEW QUESTION 5
Refer to exhibit.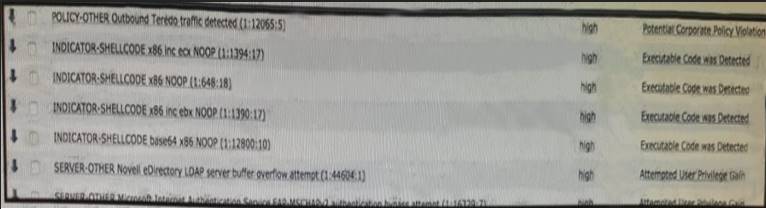
Which option is the logical source device for these events?
- A. web server
- B. NetFlow collector
- C. proxy server
- D. IDS/IPS
Answer: A
NEW QUESTION 6
Which technology is the leading industry approach used to automatically enforce NAC?
- A. SNMP
- B. port security
- C. IGMP
- D. 802.1x
Answer: D
NEW QUESTION 7
You have run a suspicious file in a sandbox analysis tool to see what the file does. The analysis report shows that outbound callouts were made post infection. Which two pieces of information from the analysis report are needed or required to investigate the callouts? (Choose two.)
- A. file size
- B. domain names
- C. dropped files
- D. signatures
- E. host IP addresses
Answer: BE
NEW QUESTION 8
What is the process of remediation the network and systems and/or reconstructing so the responsible threat actor can be revealed?
- A. Data analysis
- B. Assets distribution
- C. Evidence collection
- D. Threat actor distribution
Answer: A
NEW QUESTION 9
Which of the following are not components of the 5-tuple of a flow in NetFlow? (Choose two.)
- A. Source IP address
- B. Flow record ID
- C. Gateway
- D. Source port
- E. Destination port
Answer: BC
NEW QUESTION 10
Refer to the exhibit.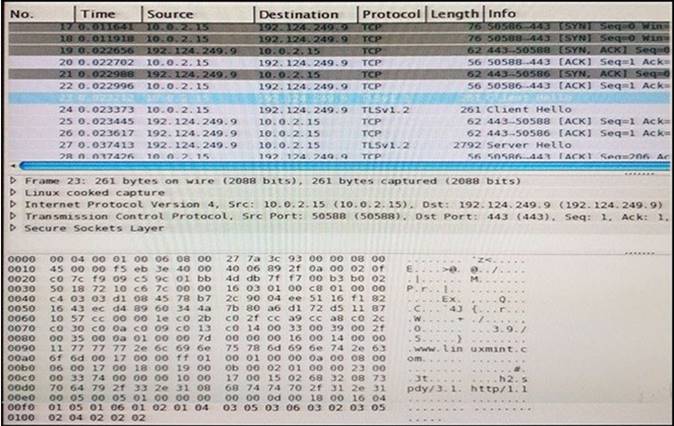
Refer to the exhibit. Drag and drop the element name from the left onto the correct piece of the PCAP file on the right.
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
Source address, source port, destination port, destination address, transport protocol, network protocol, application protocol.
NEW QUESTION 11
What is a listening port?
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
A port that remains open and waiting for incoming connections
NEW QUESTION 12
Filtering ports in wireshark?
- A. tcp.port == 80
- B. tcp port equals 80
- C. tcp.port 80
- D. port 80
Answer: A
NEW QUESTION 13
Refer to the exhibit.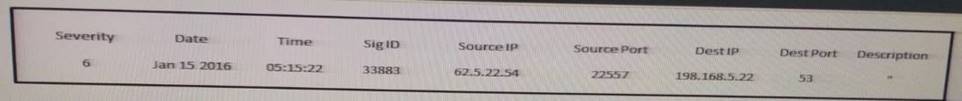
Which type of log is this an example of?
- A. syslog
- B. NetFlow log
- C. proxy log
- D. IDS log
Answer: B
Explanation:
A typical output of a NetFlow command line tool (nfdump in this case) when printing the stored flows may look as follows:
Date flow start Duration Proto Src IP Addr:Port Dst IP Addr:Port Packets Bytes Flows2010-09-01 00:00:00.459 0.000 UDP 127.0.0.1:24920 -> 192.168.0.1:22126 1 46 12010-09-01 00:00:00.363 0.000 UDP 192.168.0.1:22126 -> 127.0.0.1:24920 1 80 1
NEW QUESTION 14
Which type of analysis shows what the outcome is as well how likely each outcome is?
- A. exploratory
- B. descriptive
- C. probabilistic
- D. deterministic
Answer: D
NEW QUESTION 15
Which description of a retrospective malware detection is true?
- A. You use Wireshark to identify the malware source.
- B. You use historical information from one or more sources to identify the affected host or file.
- C. You use information from a network analyzer to identify the malware source.
- D. You use Wireshark to identify the affected host or file.
Answer: B
NEW QUESTION 16
When incident data is collected, it is important that evidentiary cross-contamination is prevented. How is this accomplished?
- A. by allowing unrestricted access to impacted devices
- B. by not allowing items of evidence to physically touch
- C. by ensuring power is removed to all devices involved
- D. by not permitting a device to store evidence if it is the evidence itself.
Answer: D
NEW QUESTION 17
Refer to exhibit.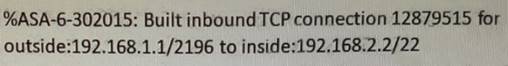
Drag and drop the items from the left onto the correct 5-tuples on the right.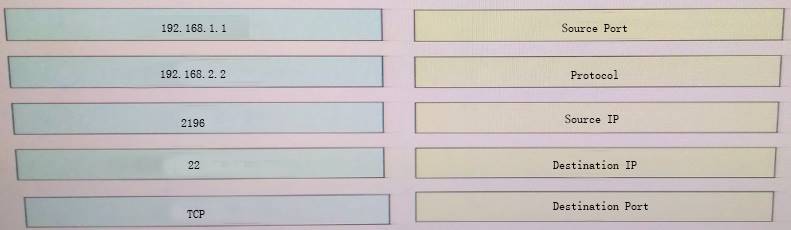
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
192.168.1.1 = source ip 192.168.2.2 = destination ip 2196 = Source port
22 = Destination port TCP = protocol
NEW QUESTION 18
Which of the following is not an example of the VERIS main schema categories?
- A. Incident tracking
- B. Victim demographics
- C. Incident descriptions
- D. Incident forensics ID
Answer: D
NEW QUESTION 19
What are the metric values of the confidentiality based on the CVSS framework?
- A. Low-high
- B. Low –Medium-high
- C. High-Low-none
- D. High-none
Answer: C
NEW QUESTION 20
What are the metric values for confidentiality impact in the CVSS v3.0 framework?
- A. high, low, none
- B. open, closed, obsolete
- C. high, low
- D. high, medium, none
Answer: A
NEW QUESTION 21
Which of the following is one of the main goals of the CSIRT?
- A. To configure the organization's firewalls
- B. To monitor the organization's IPS devices
- C. To minimize and control the damage associated with incidents, provide guidance for mitigation, and work to prevent future incidents
- D. To hire security professionals who will be part of the InfoSec team of the organization.
Answer: C
NEW QUESTION 22
Which file system has 32 bits assigned to the address clusters of the allocation table?
- A. FAT32
- B. NTFS
- C. EXT4
- D. FAT16
Answer: A
NEW QUESTION 23
......
P.S. Exambible now are offering 100% pass ensure 210-255 dumps! All 210-255 exam questions have been updated with correct answers: https://www.exambible.com/210-255-exam/ (160 New Questions)