A Review Of Best Quality 400-007 Exams
Our pass rate is high to 98.9% and the similarity percentage between our 400-007 study guide and real exam is 90% based on our seven-year educating experience. Do you want achievements in the Cisco 400-007 exam in just one try? I am currently studying for the Cisco 400-007 exam. Latest Cisco 400-007 Test exam practice questions and answers, Try Cisco 400-007 Brain Dumps First.
Check 400-007 free dumps before getting the full version:
NEW QUESTION 1
Which three tools are used for ongoing monitoring and maintenance of a voice and video environment? (Choose three.)
- A. flow-based analysis to measure bandwidth mix of applications and their flows
- B. call management analysis to identify network convergence-related failures
- C. call management analysis to identify CAC failures and call quality issues
- D. active monitoring via synthetic probes to measure loss, latency, and jitter
- E. passive monitoring via synthetic probes to measure loss, latency, and jitter
- F. flow-based analysis with PTP time-stamping to measure loss, latency, and jitter
Answer: ACD
NEW QUESTION 2
Refer to the diagram.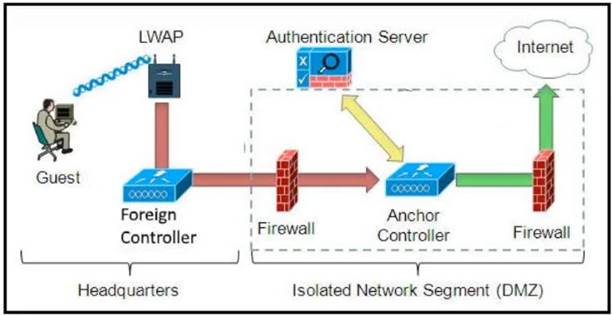
Which solution must be used to send traffic from the foreign wireless LAN controller to the anchor wireless LAN controller?
- A. Send packets from the foreign controller to the anchor controller via Layer 3 MPLS VPN or VRF-Lite
- B. Send packets without encapsulation to the anchor controller over the routed network.
- C. Encapsulate packets into an EoIP tunnel and send them to the anchor controller.
- D. Send packets from the foreign controller to the anchor controller via IPinIP or IPsec tunnel.
Answer: C
NEW QUESTION 3
Drag and drop the design characteristics from the left onto the correct network filter techniques on the right. Not all options are used.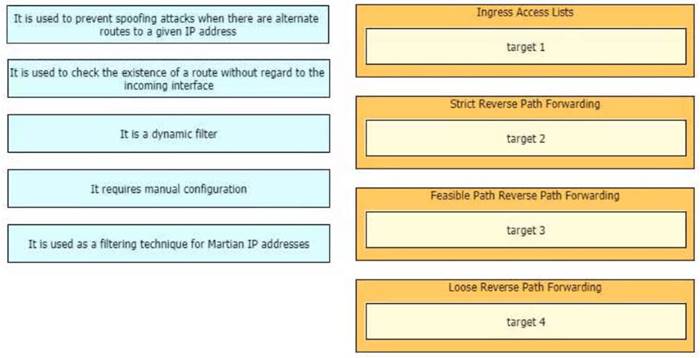
Solution:
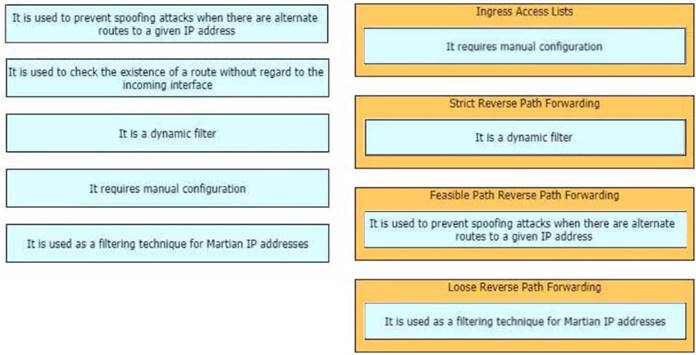
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 4
Refer to the exhibit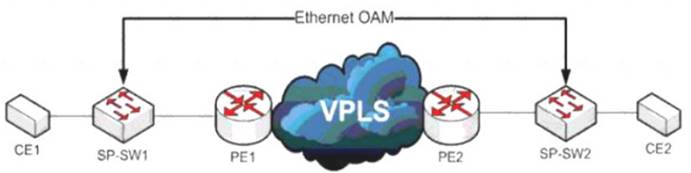
A service provider has a requirement to use Ethernet OAM to detect end-to-end connectivity failures between SP-SW1 and SP- SW2 Which two ways to design this solution are true? (Choose two)
- A. Enable unicast heartbeat messages to be periodically exchanged between MEPs
- B. Enable Connectivity Fault Management on the SP switches
- C. Use upward maintenance endpoints on the SP switches
- D. Forward E-LMI PDUs over VPLS
- E. Forward LLD PDUs over the VPLS
Answer: BC
NEW QUESTION 5
Your company wants to deploy a new data center infrastructure Based on the requirements you have chosen VXLAN as encapsulation technology The customer is concerned about miss-configuration of Layer 2 devices and DC wide outages caused by Layer 2 loops What do you answer?
- A. VXLAN offers native loop avoidance mechanism
- B. Storm Control should be enabled on all ports
- C. VPC+ could prevent L2 loop on access ports
- D. BPDU Guard should be enabled on all VTEP access ports
Answer: D
NEW QUESTION 6
Which aspect of BGP-LS makes it scalable in large network when multiarea topology information must be gathered?
- A. transmit flow control
- B. open-loop flow control
- C. hardware flow control
- D. TCP-based flow control
Answer: A
NEW QUESTION 7
Which two statements explain the operation of BFD asynchronous mode? (Choose two )
- A. BFD asynchronous mode with echo packets combines the control packets and echo packets into a single packet.
- B. BFD asynchronous mode without echo packets uses control packets, and BFD asynchronous mode with echo packets does not.
- C. BFD asynchronous mode with and without echo packets use control packets.
- D. BFD asynchronous without echo packets has control packets sent back to the originating router, which echoes the control packet to detect failures.
- E. BFD asynchronous mode with echo packets uses separate control packets and echo packets.
Answer: CE
NEW QUESTION 8
Which two control plane policer designs must be considered to achieve high availability? (Choose two.)
- A. Control plane policers are enforced in hardware to protect the software path, but they are hardware platform dependent in terms of classification ability.
- B. Control plane policers are really needed only on externally facing devices.
- C. Control plane policers can cause the network management systems to create false alarms.
- D. Control plane policers must be processed before a forwarding decision is made.
- E. Control plane policers require that adequate protocols overhead are factored in to allow protocol convergence.
Answer: AD
NEW QUESTION 9
Refer to the exhibit.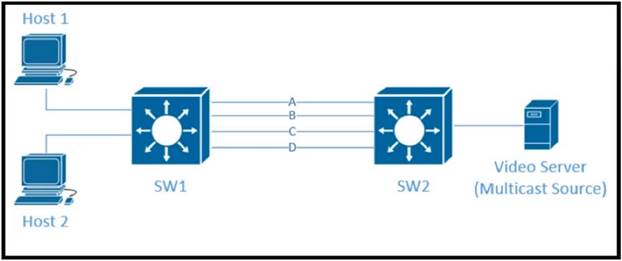
Traffic was equally balanced between Layer 3 links on core switches SW1 and SW2 before an introduction of the new video server in the network. This video server uses multicast to send video streams to hosts and now one of the links between core switches is over utilized Which design solution solves this issue?
- A. Add more links between core switches.
- B. Aggregate links Layer 2 link aggregation.
- C. Apply a more granular load- balancing method on SW1.
- D. Apply a more granular load-balancing method on SW2.
- E. Filter IGMP joins on an over -utilized link.
Answer: B
NEW QUESTION 10
Refer to the exhibit.
The WAN network of the General Bank of Greece has experienced several outages It takes too long to activate a new branch site The networking department of the bank plans to upgrade the legacy end-of-life WAN network with a new flexible manageable, and scalable in-house solution The number of branches will increase exponentially in the next fiscal year The CTO states that the bank’s mam goal is OPEX reduction The network engineering team prepares a table to evaluate the available options Which WAN technology can be used for the solution?
- A. DMVPN over L3VPN
- B. Managed SD-WAN
- C. SD-WAN over L3VPN
- D. SD-WAN over L2VPN
Answer: B
NEW QUESTION 11
An enterprise network has two core routers that connect to 200 distribution routers and uses full-mesh IBGP peering between these routers as its routing method. The distribution routers are experiencing high CPU utilization due to the BGP process. Which design solution is the most cost effective?
- A. Implement route reflectors on the two core routers
- B. Increase the memory on the core routers
- C. Implement e BGP between the core and distribution routers
- D. Increase the memory on the distribution routers
- E. Increase bandwidth between the core routers
Answer: A
NEW QUESTION 12
What are two key design principles when using a hierarchical core-distribution-access network model? (Choose two )
- A. A hierarchical network design model aids fault isolation
- B. The core layer is designed first, followed by the distribution layer and then the access layer
- C. The core layer provides server access in a small campus.
- D. A hierarchical network design facilitates changes
- E. The core layer controls access to resources for security
Answer: AD
NEW QUESTION 13
Drag and drop the FCAPS network management reference models from the left onto the correct definitions on the right.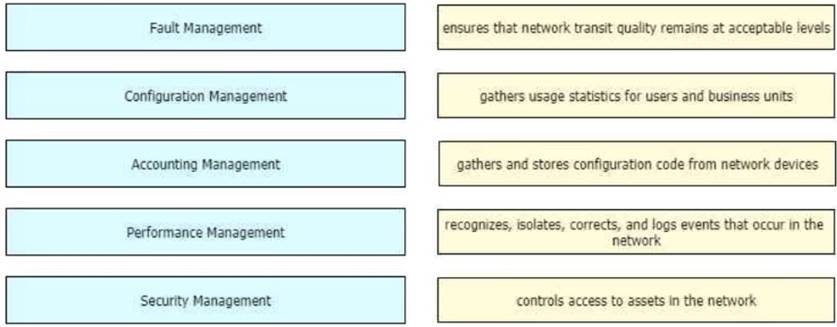
Solution:
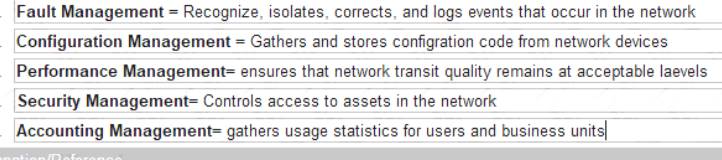
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 14
What are two advantages of controller-based networks versus traditional networks? (Choose two.)
- A. the ability to have forwarding tables at each device
- B. more flexible configuration per device
- C. more consistent device configuration
- D. programmatic APIs that are available per device
- E. the ability to configure the features for the network rather than per device
Answer: CE
NEW QUESTION 15
A service provider hires you to design its new managed CE offering to meet these requirements
• The CEs cannot run a routing protocol with the PE
• Provide the ability for equal or unequal ingress load balancing in dual-homed CE scenarios.
• Provide support for IPv6 customer routes
• Scale up to 250.000 CE devices per customer.
• Provide low operational management to scale customer growth.
• Utilize low-end (inexpensive) routing platforms for CE functionality. Which tunneling technology do you recommend?
- A. FlexVPN
- B. point-to-point GRE
- C. DMVPN
- D. LISP
Answer: D
NEW QUESTION 16
Company XYZ has 30 sites using MPLS L3 VPN and the company is now concerned about data integrity. The company wants to redesign the security aspect of their network based on these requirements:
• Securely transfer the corporate data over the private WAN
• Use a centralized configuration model.
• Minimize overhead on the tunneled traffic.
Which technology can be used in the new design to meet the company's requirements?
- A. S-VTI
- B. DMVPN
- C. MGRE
- D. GET VPN
Answer: D
NEW QUESTION 17
Which feature is supported by NETCONF but is not supported by SNMP?
- A. distinguishing between configuration data and operational data
- B. taking administrative actions
- C. collecting the status of specific fields
- D. changing the configuration of specific fields
Answer: A
NEW QUESTION 18
A business customer deploys workloads in the public cloud. Now the customer network faces governance issues with the flow of IT traffic and must ensure the security of data and intellectual property. Which action helps to identify the issue for further resolution?
- A. Set up a secure tunnel from customer routers to ensure that traffic is protected as it travels to the cloud service providers.
- B. Send IPFIX telemetry data from customer routers to a centralized collector to identify traffic to cloud service providers
- C. Build a zone-based firewall policy on Internet edge firewalls that collects statistics on traffic sent to cloud service providers
- D. Apply workload policies that dictate the security requirements to the workloads that are placed in the cloud.
Answer: B
NEW QUESTION 19
Organizations that embrace Zero Trust initiatives ranging from business policies to technology infrastructure can reap business and security benefits. Which two domains should be covered under Zero Trust initiatives? (Choose two)
- A. workload
- B. work domain
- C. workplace
- D. workgroup
- E. workspace
Answer: AC
NEW QUESTION 20
Which three elements help network designers to construct secure systems that protect information and resources (such as devices, communication, and data) from unauthorized access, modification, inspection, or destruction? (Choose three.)
- A. confidential
- B. serviceability
- C. reliability
- D. availability
- E. integrity
- F. scalability
Answer: ADE
NEW QUESTION 21
......
Recommend!! Get the Full 400-007 dumps in VCE and PDF From Dumps-files.com, Welcome to Download: https://www.dumps-files.com/files/400-007/ (New 330 Q&As Version)