Renewal 400-007 Dump For Cisco Certified Design Expert (CCDE V3.0) Written Exam Certification
Exam Code: 400-007 (Practice Exam Latest Test Questions VCE PDF)
Exam Name: Cisco Certified Design Expert (CCDE v3.0) Written Exam
Certification Provider: Cisco
Free Today! Guaranteed Training- Pass 400-007 Exam.
Online 400-007 free questions and answers of New Version:
NEW QUESTION 1
What is a characteristic of a secure cloud architecture model?
- A. limited access to job function
- B. dedicated and restricted workstations
- C. multi-factor authentication
- D. software-defined network segmentation
Answer: C
NEW QUESTION 2
Refer to the exhibit.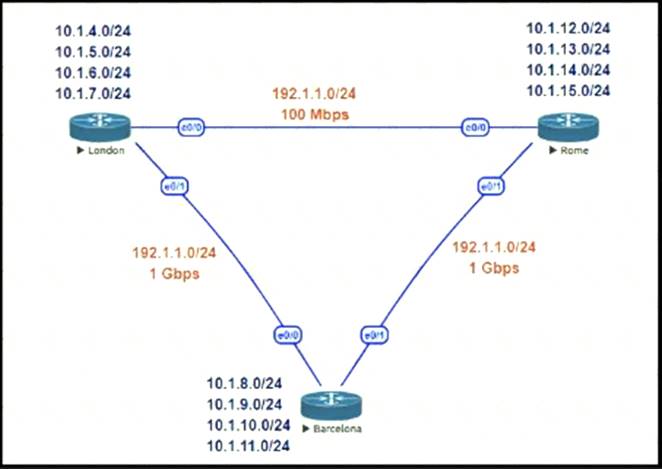
This network is running EIGRP as the routing protocol and the internal networks are being advertised in EIGRP. Based on the link speeds, all traffic between London and Rome is getting propagated via Barcelona and the direct link between London and Rome is not being utilized under normal working circumstances. The EIGRP design should allow for efficiency in the routing table by minimizing the routes being exchanged. The link between London and Rome should be utilized for specific routes. Which two steps accomplish this task? (Choose two.)
- A. Configure EIGRP route summarization on all the interfaces to summarize the internal LAN routes
- B. Filter the routes on the link between London and Barcelona
- C. Filter the routes on the link between London and Rome
- D. Configure route leaking of summary routes on the link between London and Rome
Answer: AD
NEW QUESTION 3
Which mechanism provides Layer 2 fault isolation between data centers?
- A. fabric path
- B. OTL
- C. advanced VPLS
- D. LISP
- E. TRILL
Answer: D
NEW QUESTION 4
Enterprise XYZ wants to implement fast convergence on their network and optimize timers for OSPF However they also want to prevent excess flooding of LSAs if there is a constantly flapping link on the network Which timers can help prevent excess flooding of LSAs for OSPF?
- A. OSPF propagation timers
- B. OSPF throttling timers
- C. OSPF delay timers
- D. OSPF flooding timers
Answer: B
NEW QUESTION 5
Company XYZ is designing the network for IPv6 security and they have these design requirements: A switch or router must deny access to traffic from sources with addresses that are correct, but are topologically incorrect
A switch or router must deny access to traffic from sources with addresses that are correct, but are topologically incorrect Devices must block Neighbor Discovery Protocol resolution for destination addresses that are not found in the binding table.
Devices must block Neighbor Discovery Protocol resolution for destination addresses that are not found in the binding table.
Which two IPv4 security features are recommended for this company? (Choose two)
- A. IPv6 DHCP Guard
- B. IPv6 Source Guard
- C. IPv6 Destination Guard
- D. IPv6 Prefix Guard
- E. IPv6 RA Guard
Answer: CD
Explanation:
https://www.cisco.com/c/dam/global/ja_jp/td/docs/ios-xml/ios/ipv6_fhsec/configuration/xe-16/ip6f-xe-16-book.
NEW QUESTION 6
Which solution component helps to achieve comprehensive threat protection and compliance for migration to multicloud SDX architectures?
- A. system-oriented architecture
- B. OSASE architecture
- C. platform-oriented architecture
- D. SASE architecture
Answer: D
NEW QUESTION 7
A European government passport agency considers upgrading its IT systems to increase performance and workload flexibility in response to constantly changing requirements. The budget manager wants to reduce capital expenses and IT staff and must adopt the lowest-cost technology. Which technology choice is suitable?
- A. on premises
- B. private cloud
- C. public cloud
- D. hybrid cloud
Answer: C
NEW QUESTION 8
A banking customer determines that it is operating POS and POI terminals that are noncompliant with PCI DSS requirements, as it is running TLSv1.0. The customer plans to migrate the terminals to TLSv1.2. What are two requirements to complete the migration? (Choose two.)
- A. Ensure that strong cryptography is applied for users who have administrative access through networks
- B. Apply strong cryptography and security protocols to safeguard sensitive cardholder data.
- C. Apply strong encryption for transmission of cardholder data across public networks.
- D. Protect all user systems against malware and frequently update antivirus software
- E. Maintain a policy that addresses information security for employees and third parties.
Answer: CE
NEW QUESTION 9
The Company XYZ network requires OSPF dead neighbor detection in a subsecond manner However the company network does not support BFD Which other feature can be used to fulfill the design requirement?
- A. STP
- B. fast hello
- C. LFA
- D. DPD
Answer: B
NEW QUESTION 10
What are two descriptions of network optimization? (Choose two.)
- A. maintain high availability
- B. proactive network management
- C. network redesign
- D. network health maintenance
- E. identify network requirements
Answer: AD
NEW QUESTION 11
The General Bank of Greece plans to upgrade its legacy end-of-life WAN network with a new flexible, manageable, and scalable solution. The mam requirements are ZTP support, end-to-end encryption application awareness and segmentation. The CTO states that the main goal of the bank is CAPEX reduction. Which WAN technology should be used for the solution?
- A. SD-branch
- B. DMVPN with PfR
- C. managed SD-WAN
- D. SD-WAN
Answer: C
NEW QUESTION 12
What advantage of placing the IS-IS layer 2 flooding domain boundary at the core Layer in a three-layer hierarchical network is true?
- A. The Layer 1 and Layer 2 domains can easily overlap
- B. It reduces the complexity of the Layer 1 domains
- C. It can be applied to any kind of topology
- D. The Layer 2 domain is contained and more stable
Answer: D
NEW QUESTION 13
Drag and drop the end-to-end network virtualization elements from the left onto the correct network areas on the right.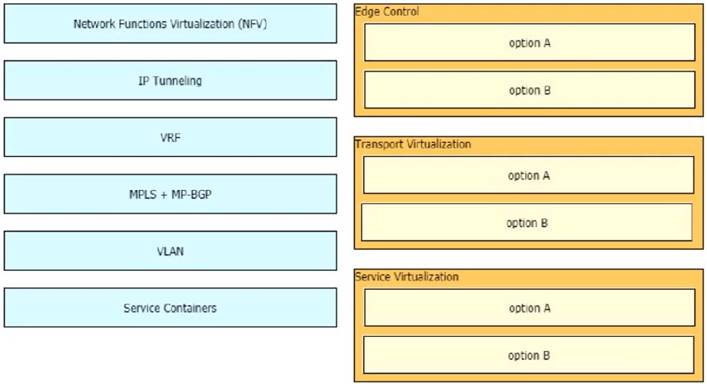
Solution:
Graphical user interface Description automatically generated with medium confidence
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 14
Which three items do you recommend for control plane hardening of an infrastructure device? (Choose three.)
- A. redundant AAA servers
- B. Control Plane Policing
- C. warning banners
- D. to enable unused .services
- E. SNMPv3
- F. routing protocol authentication
Answer: BEF
NEW QUESTION 15
Drag and drop the multicast protocols from the left onto the current design situation on the right.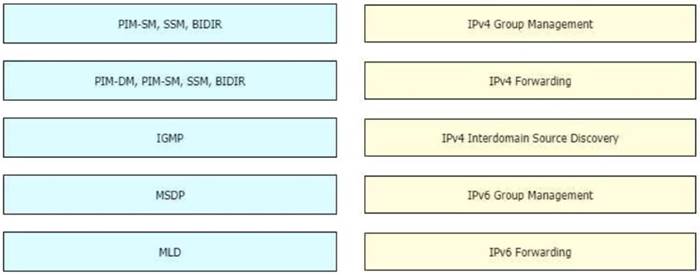
Solution:
A picture containing table Description automatically generated
IPv4:
Host Registration - IGMP
Router Registration - PIM-DM, PIM-SM, SSM, BIDIR Inter-Domain Source Discovery - MSDP
IPv6:
Host Registration - MLD
Router Registration - PIM-SM, SSM, BIDIR
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 16
Refer to the exhibit.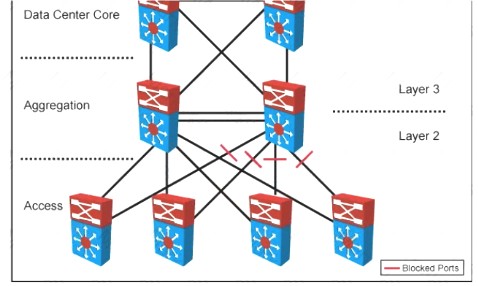
Your company designed a network to allow server VLANs to span all access switches in a data center In the design, Layer 3 VLAN interfaces and HSRP are configured on the aggregation switches Which two features improve STP stability within the network design? (Choose two.)
- A. BPDU guard on access ports
- B. BPDU guard on the aggregation switch downlinks toward access switches
- C. root guard on the aggregation switch downlinks toward access switches
- D. root guard on access ports
- E. edge port on access ports
- F. access switch pairs explicitly determined to be root and backup root bridges
Answer: AE
NEW QUESTION 17
Software-defined networking architecture is used for cost-effective, adaptable, and easily manageable applications. In which two software-defined networks is SDN commonly used? (Choose two.)
- A. wide area network
- B. mobile network
- C. metro network
- D. application network
- E. control network
Answer: AE
NEW QUESTION 18
How must the queue sizes be designed to ensure that an application functions correctly?
- A. Each individual device queuing delay in the chain must be less than or equal to the application required delay.
- B. The queuing delay on every device in the chain must be exactly the same to the application required delay.
- C. The default queue sizes are good for any deployment as it compensates the serialization delay.
- D. The sum of the queuing delay of all devices plus serialization delay in the chain must be less than or equal to the application required delay.
Answer: D
NEW QUESTION 19
You are designing the routing design for two merging companies that have overlapping IP address space. Which of these must you consider when developing the routing and NAT design?
- A. Local to global NAT translation is done after routing
- B. Global to local NAT translation is done before routing.
- C. Local to global NAT translation is done before policy-based routing
- D. Global to local NAT translation is done after policy-based routing.
Answer: B
NEW QUESTION 20
In an OSPF network with routers connected together with Ethernet cabling, which topology typically takes the longest to converge?
- A. partial mesh
- B. full mesh
- C. ring
- D. squared
- E. triangulated
Answer: B
NEW QUESTION 21
......
Recommend!! Get the Full 400-007 dumps in VCE and PDF From Dumps-hub.com, Welcome to Download: https://www.dumps-hub.com/400-007-dumps.html (New 330 Q&As Version)