Virtual 312-50v10 Secret 2021
we provide Vivid EC-Council 312-50v10 free practice questions which are the best for clearing 312-50v10 test, and to get certified by EC-Council Certified Ethical Hacker v10. The 312-50v10 Questions & Answers covers all the knowledge points of the real 312-50v10 exam. Crack your EC-Council 312-50v10 Exam with latest dumps, guaranteed!
Also have 312-50v10 free dumps questions for you:
NEW QUESTION 1
You went to great lengths to install all the necessary technologies to prevent hacking attacks, such as expensive firewalls, antivirus software, anti-spam systems and intrusion detection/prevention tools in your company's network. You have configured the most secure policies and tightened every device on your network. You are confident that hackers will never be able to gain access to your network with complex security system in place.
Your peer, Peter Smith who works at the same department disagrees with you.
He says even the best network security technologies cannot prevent hackers gaining access to the network because of presence of "weakest link" in the security chain.
What is Peter Smith talking about?
- A. Untrained staff or ignorant computer users who inadvertently become the weakest link in your security chain
- B. "zero-day" exploits are the weakest link in the security chain since the IDS will not be able to detect these attacks
- C. "Polymorphic viruses" are the weakest link in the security chain since the Anti-Virus scanners will not be able to detect these attacks
- D. Continuous Spam e-mails cannot be blocked by your security system since spammers use different techniques to bypass the filters in your gateway
Answer: A
NEW QUESTION 2
When security and confidentiality of data within the same LAN is of utmost priority, which IPSec mode should you implement?
- A. AH Tunnel mode
- B. AH promiscuous
- C. ESP transport mode
- D. ESP confidential
Answer: C
NEW QUESTION 3
A zone file consists of which of the following Resource Records (RRs)?
- A. DNS, NS, AXFR, and MX records
- B. DNS, NS, PTR, and MX records
- C. SOA, NS, AXFR, and MX records
- D. SOA, NS, A, and MX records
Answer: D
NEW QUESTION 4
Which of the following defines the role of a root Certificate Authority (CA) in a Public Key Infrastructure (PKI)?
- A. The root CA is the recovery agent used to encrypt data when a user's certificate is lost.
- B. The root CA stores the user's hash value for safekeeping.
- C. The CA is the trusted root that issues certificates.
- D. The root CA is used to encrypt email messages to prevent unintended disclosure of data.
Answer: C
NEW QUESTION 5
An attacker runs netcat tool to transfer a secret file between two hosts.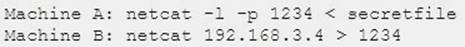
He is worried about information being sniffed on the network.
How would the attacker use netcat to encrypt the information before transmitting onto the wire?
- A. Machine A: netcat -l -p -s password 1234 < testfileMachine B: netcat <machine A IP> 1234
- B. Machine A: netcat -l -e magickey -p 1234 < testfileMachine B: netcat <machine A IP> 1234
- C. Machine A: netcat -l -p 1234 < testfile -pw passwordMachine B: netcat <machine A IP> 1234 -pw password
- D. Use cryptcat instead of netcat
Answer: D
NEW QUESTION 6
> NMAP -sn 192.168.11.200-215
The NMAP command above performs which of the following?
- A. A ping scan
- B. A trace sweep
- C. An operating system detect
- D. A port scan
Answer: A
Explanation:
NMAP -sn (No port scan)
This option tells Nmap not to do a port scan after host discovery, and only print out the available hosts that responded to the host discovery probes. This is often known as a “ping scan”, but you can also request that traceroute and NSE host scripts be run.
References: https://nmap.org/book/man-host-discovery.html
NEW QUESTION 7
In Trojan terminology, what is a covert channel?
- A. A channel that transfers information within a computer system or network in a way that violates the security policy
- B. A legitimate communication path within a computer system or network for transfer of data
- C. It is a kernel operation that hides boot processes and services to mask detection
- D. It is Reverse tunneling technique that uses HTTPS protocol instead of HTTP protocol to establish connections
Answer: A
NEW QUESTION 8
The company ABC recently discovered that their new product was released by the opposition before their premiere. They contract an investigator who discovered that the maid threw away papers with confidential information about the new product and the opposition found it in the garbage. What is the name of the technique used by the opposition?
- A. Hack attack
- B. Sniffing
- C. Dumpster diving
- D. Spying
Answer: C
NEW QUESTION 9
A certified ethical hacker (CEH) is approached by a friend who believes her husband is cheating. She offers to pay to break into her husband's email account in order to find proof so she can take him to court. What is the ethical response?
- A. Say no; the friend is not the owner of the account.
- B. Say yes; the friend needs help to gather evidence.
- C. Say yes; do the job for free.
- D. Say no; make sure that the friend knows the risk she’s asking the CEH to take.
Answer: A
NEW QUESTION 10
Which of the following program infects the system boot sector and the executable files at the same time?
- A. Stealth virus
- B. Polymorphic virus
- C. Macro virus
- D. Multipartite Virus
Answer: D
NEW QUESTION 11
Which of the following viruses tries to hide from anti-virus programs by actively altering and corrupting the chosen service call interruptions when they are being run?
- A. Cavity virus
- B. Polymorphic virus
- C. Tunneling virus
- D. Stealth virus
Answer: D
NEW QUESTION 12
Which of the following is not a Bluetooth attack?
- A. Bluedriving
- B. Bluejacking
- C. Bluesmacking
- D. Bluesnarfing
Answer: A
NEW QUESTION 13
A Certificate Authority (CA) generates a key pair that will be used for encryption and decryption of email. The integrity of the encrypted email is dependent on the security of which of the following?
- A. Public key
- B. Private key
- C. Modulus length
- D. Email server certificate
Answer: B
NEW QUESTION 14
What is the most common method to exploit the “Bash Bug” or “ShellShock" vulnerability?
- A. Through Web servers utilizing CGI (Common Gateway Interface) to send a malformed environment variable to a vulnerable Web server
- B. Manipulate format strings in text fields
- C. SSH
- D. SYN Flood
Answer: A
Explanation:
Shellshock, also known as Bashdoor, is a family of security bugs in the widely used Unix Bash shell. One specific exploitation vector of the Shellshock bug is CGI-based web servers.
Note: When a web server uses the Common Gateway Interface (CGI) to handle a document request, it passes various details of the request to a handler program in the environment variable list. For example, the variable HTTP_USER_AGENT has a value that, in normal usage, identifies the program sending the request. If the request handler is a Bash script, or if it executes one for example using the system call, Bash will receive the environment variables passed by the server and will process them. This provides a means for an attacker to trigger the Shellshock vulnerability with a specially crafted server request.
References: https://en.wikipedia.org/wiki/Shellshock_(software_bug)#Specific_exploitation_vectors
NEW QUESTION 15
Which of the following is an NMAP script that could help detect HTTP Methods such as GET, POST, HEAD, PUT, DELETE, TRACE?
- A. http-git
- B. http-headers
- C. http enum
- D. http-methods
Answer: D
NEW QUESTION 16
The network team has well-established procedures to follow for creating new rules on the firewall. This includes having approval from a manager prior to implementing any new rules. While reviewing the firewall configuration, you notice a recently implemented rule but cannot locate manager approval for it. What would be a good step to have in the procedures for a situation like this?
- A. Have the network team document the reason why the rule was implemented without prior manager approval.
- B. Monitor all traffic using the firewall rule until a manager can approve it.
- C. Do not roll back the firewall rule as the business may be relying upon it, but try to get manager approval as soon as possible.
- D. Immediately roll back the firewall rule until a manager can approve it
Answer: D
NEW QUESTION 17
The use of alert thresholding in an IDS can reduce the volume of repeated alerts, but introduces which of the following vulnerabilities?
- A. An attacker, working slowly enough, can evade detection by the IDS.
- B. Network packets are dropped if the volume exceeds the threshold.
- C. Thresholding interferes with the IDS’ ability to reassemble fragmented packets.
- D. The IDS will not distinguish among packets originating from different sources.
Answer: A
NEW QUESTION 18
Based on the following extract from the log of a compromised machine, what is the hacker really trying to steal?
- A. har.txt
- B. SAM file
- C. wwwroot
- D. Repair file
Answer: B
NEW QUESTION 19
Which of the following is used to indicate a single-line comment in structured query language (SQL)?
- A. --
- B. ||
- C. %%
- D. ''
Answer: A
NEW QUESTION 20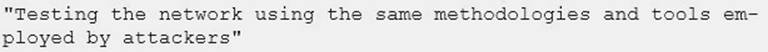
Identify the correct terminology that defines the above statement.
- A. Vulnerability Scanning
- B. Penetration Testing
- C. Security Policy Implementation
- D. Designing Network Security
Answer: B
NEW QUESTION 21
In many states sending spam is illegal. Thus, the spammers have techniques to try and ensure that no one knows they sent the spam out to thousands of users at a time. Which of the following best describes what spammers use to hide the origin of these types of e-mails?
- A. A blacklist of companies that have their mail server relays configured to allow traffic only to theirspecific domain name.
- B. Mail relaying, which is a technique of bouncing e-mail from internal to external mails servers continuously.
- C. A blacklist of companies that have their mail server relays configured to be wide open.
- D. Tools that will reconfigure a mail server's relay component to send the e-mail back to the spammers occasionally.
Answer: B
NEW QUESTION 22
You are performing information gathering for an important penetration test. You have found pdf, doc, and images in your objective. You decide to extract metadata from these files and analyze it.
What tool will help you with the task?
- A. Metagoofil
- B. Armitage
- C. Dimitry
- D. cdpsnarf
Answer: A
Explanation:
Metagoofil is an information gathering tool designed for extracting metadata of public documents (pdf,doc,xls,ppt,docx,pptx,xlsx) belonging to a target company.
Metagoofil will perform a search in Google to identify and download the documents to local disk and then will extract the metadata with different libraries like Hachoir, PdfMiner? and others. With the results it will generate a report with usernames, software versions and servers or machine names that will help Penetration testers in the information gathering phase.
References:
http://www.edge-security.com/metagoofil.php
NEW QUESTION 23
Bob is doing a password assessment for one of his clients. Bob suspects that security policies are not in place. He also suspects that weak passwords are probably the norm throughout the company he is evaluating. Bob is familiar with password weaknesses and key loggers.
Which of the following options best represents the means that Bob can adopt to retrieve passwords from his clients hosts and servers?
- A. Hardware, Software, and Sniffing.
- B. Hardware and Software Keyloggers.
- C. Passwords are always best obtained using Hardware key loggers.
- D. Software only, they are the most effective.
Answer: A
NEW QUESTION 24
What is the term coined for logging, recording and resolving events in a company?
- A. Internal Procedure
- B. Security Policy
- C. Incident Management Process
- D. Metrics
Answer: C
NEW QUESTION 25
Which of the following algorithms provides better protection against brute force attacks by using a 160-bit message digest?
- A. MD5
- B. SHA-1
- C. RC4
- D. MD4
Answer: B
NEW QUESTION 26
......
Recommend!! Get the Full 312-50v10 dumps in VCE and PDF From Passcertsure, Welcome to Download: https://www.passcertsure.com/312-50v10-test/ (New 736 Q&As Version)