High Value 70-411 Discount Pack 2021
We provide real 70-411 exam questions and answers braindumps in two formats. Download PDF & Practice Tests. Pass Microsoft 70-411 Exam quickly & easily. The 70-411 PDF type is available for reading and printing. You can print more and practice many times. With the help of our Microsoft 70-411 dumps pdf and vce product and material, you can easily pass the 70-411 exam.
Free demo questions for Microsoft 70-411 Exam Dumps Below:
NEW QUESTION 1
HOTSPOT
Your network contains an Active Directory domain named contoso.com. The domain contains three servers named Server2, Server3, and Server4.
Server2 and Server4 host a Distributed File System (DFS) namespace named Namespace1.
You open the DFS Management console as shown in the exhibit. (Click the Exhibit button.)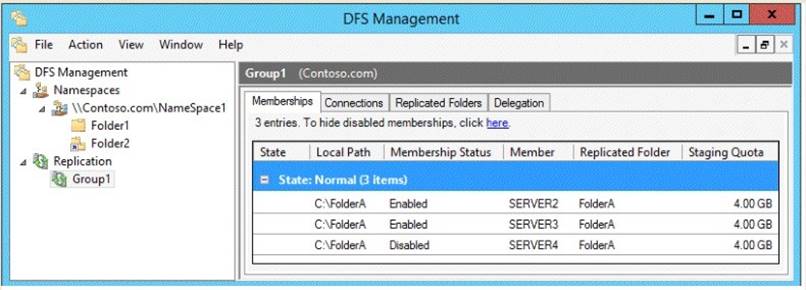
To answer, complete each statement according to the information presented in the exhibit. Each correct selection is worth one point.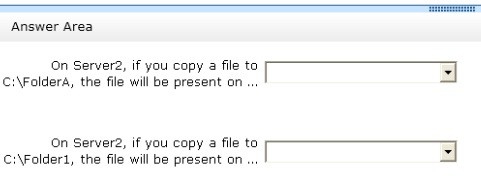
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 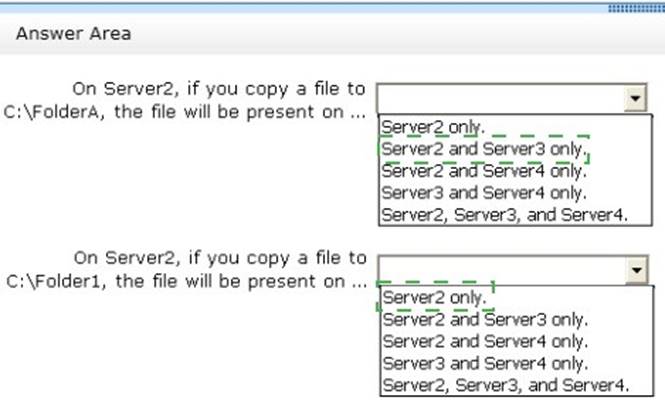
NEW QUESTION 2
HOTSPOT
You have a server named Server1 that runs Windows Server 2012 R2. You configure Network Access Protection (NAP) on Server1.
Your company implements a new security policy stating that all client computers must have the latest updates installed. The company informs all employees that they have two weeks
to update their computer accordingly.
You need to ensure that if the client computers have automatic updating disabled, they are provided with full access to the network until a specific date and time.
Which two nodes should you configure?
To answer, select the appropriate two nodes in the answer area.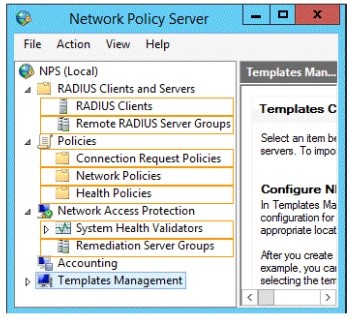
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 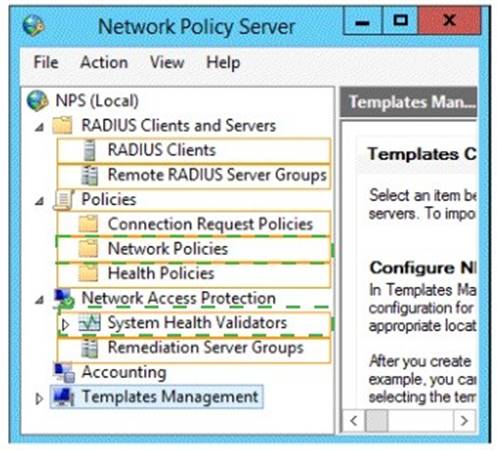
NEW QUESTION 3
HOTSPOT
Your network contains an Active Directory domain named contoso.com. You implement DirectAccess.
You need to view the properties of the DirectAccess connection.
Which connection properties should you view? To answer, select the appropriate connection properties in the answer area.
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 
NEW QUESTION 4
Your network contains an Active Directory domain named contoso.com. The domain contains a domain controller named DC1. DC1 is a DNS server for contoso.com. The properties of the contoso.com zone are configured as shown in the exhibit. (Click the Exhibit button.)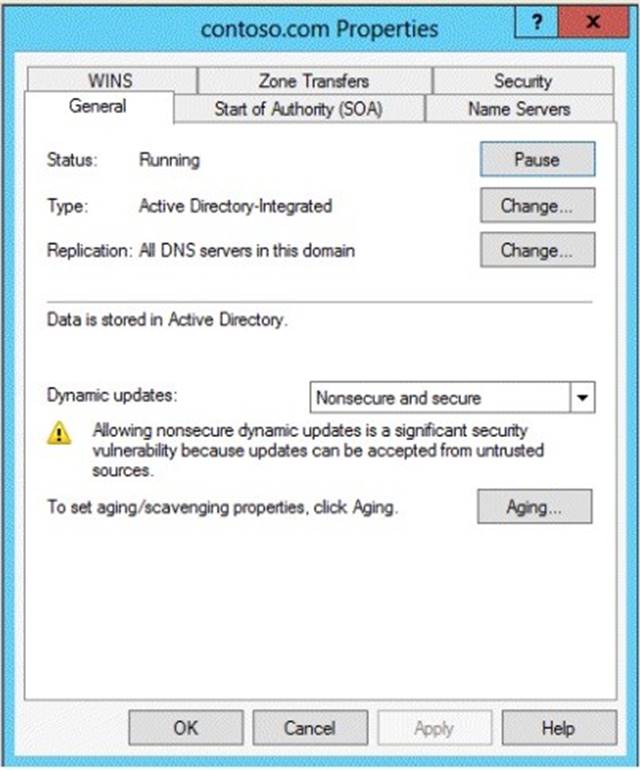
The domain contains a server named Server1 that is part of a workgroup named Workgroup. Server1 is configured to use DC1 as a DNS server.
You need to ensure that Server1 dynamically registers a host (A) record in the contoso.com zone.
What should you configure?
- A. The workgroup name of Server1
- B. The Security settings of the contoso.com zone
- C. The Dynamic updates setting of the contoso.com zone
- D. The primary DNS suffix of Server1
Answer: D
Explanation:
When any computer or a standalone server is added to a domain as a member, the network identifies that computer with its Fully Qualified Domain Name or FQDN. A Fully Qualified Domain Name consist of a hostname and the DNs suffix separated by a “. ” called period. An example for this can be server01. msftdomain.com where “server01 is the hostname of the computer and “msftdomain.com” is the DNS suffix which follows the hostname. A complete FQDN of a client computer or a member server uniquely identifies that computer in the entire domain.
Primary DNS suffix must manually be added in Windows 8 computer to change its hostname to Fully Qualified Domain Name so that it becomes eligible to send queries and receive responses from the DNS server. Following are the steps which can be implemented to add primary DNS suffix to a Windows 8 computer hostname:
✑ Log on to Windows 8 computer with administrator account.
✑ From the options available on the screen click Control Panel.
✑ On the opened window click More Settings from the left pane.
✑ On the next window click System and Security category and on the appeared window click System.
✑ On View basic information about your computer window click Change settings under Computer name, domain, and workgroup settings section.
✑ On System Properties box make sure that Computer Name tab is selected and click Change button.
✑ On Computer Name/Domain Changes box click More button.
✑ On DNS Suffix and NetBIOS Computer Name box type in the DNS domain name as the DNS suffix to the Windows 8 computer under Primary DNS suffix of this computer field.
✑ Click Ok button on all the boxes and restart the computer to allow changes to take effect.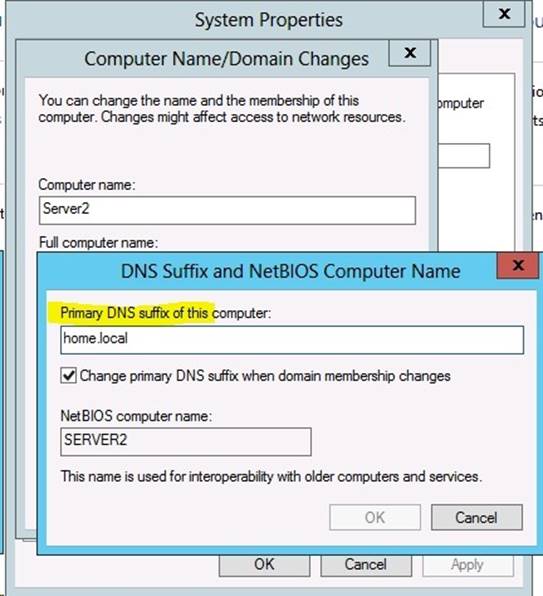
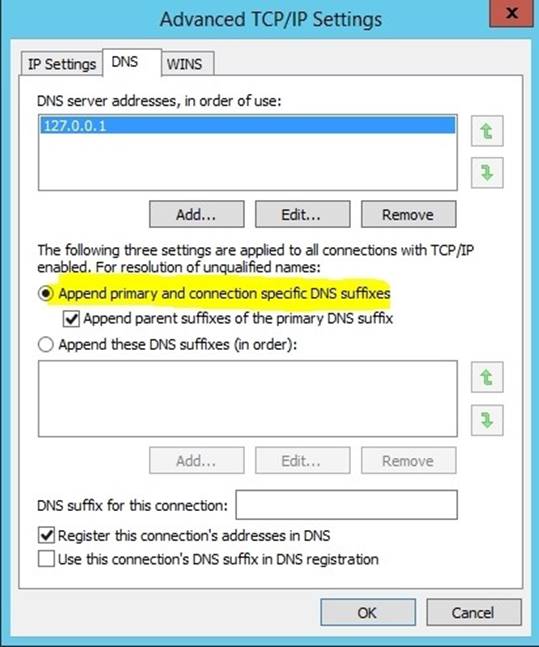
For years, Windows DNS has supported dynamic updates, whereas a DNS client host registers and dynamically updates the resource records with a DNS server. If a host’s IP address changes, the resource record (particularly the A record) for the host is automatically updated, while the host utilizes the DHCP server to dynamically update its Pointer (PTR) resource record. Therefore, when a user or service needs to contact a client PC, it can look up the IP address of the host. With larger organizations, this becomes an essential feature, especially for clients that frequently move or change locations and use DHCP to automatically obtain an IP address. For dynamic DNS updates to succeed, the zone must be configured to accept dynamic updates: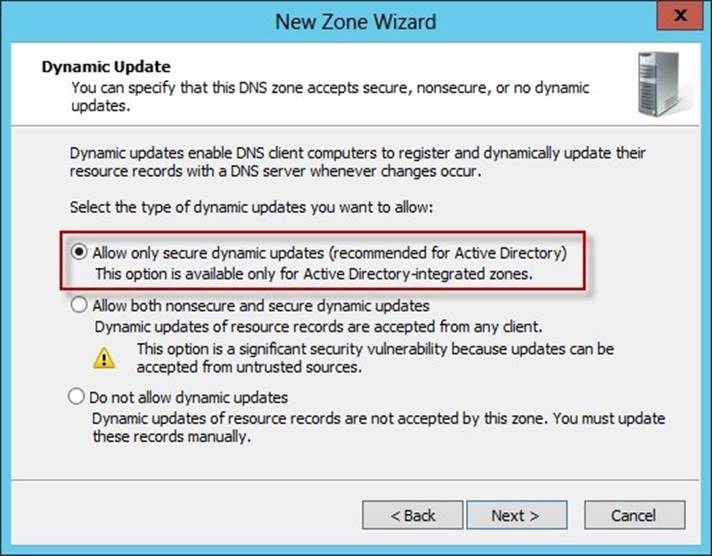
References:
http: //technet. microsoft. com/en-us/library/cc778792%28v=ws. 10%29. aspx
http: //technet. microsoft. com/en-us/library/cc778792%28v=ws. 10%29. aspx
http: //www. advicehow. com/adding-primary-dns-suffix-in-microsoft-windows-8/
http: //technet. microsoft. com/en-us/library/cc959611. aspx
NEW QUESTION 5
Your network contains one Active Directory domain named contoso.com. The forest functional level is Windows Server 2012. All servers run Windows Server 2012 R2. All client computers run Windows 8.1.
The domain contains 10 domain controllers and a read-only domain controller (RODC) named RODC01. All domain controllers and RODCs are hosted on a Hyper-V host that runs Windows Server 2012 R2.
You need to identify which domain controllers are authorized to be cloned by using virtual domain controller cloning.
Which cmdlet should you use?
- A. Get-ADGroupMember
- B. Get-ADDomainControllerPasswordReplicationPolicy
- C. Get-ADDomainControllerPasswordReplicationPolicyUsage
- D. Get-ADDomain
- E. Get-ADOptionalFeature
- F. Get-ADAccountAuthorizationGroup
Answer: D
Explanation:
One requirement for cloning a domain controller is an existing Windows Server 2012 DC that hosts the PDC emulator role. You can run the Get-ADDomain and retrieve which server has the PDC emulator role.
Example: Command Prompt: C:PS> Get-ADDomain
Output wouldinclude a line such as: PDCEmulator : Fabrikam-DC1.Fabrikam.com Reference: Step-by-Step: Domain Controller Cloning
http://blogs.technet.com/b/canitpro/archive/2013/06/12/step-by-step-domain-controller- cloning.aspx
Reference: Get-ADDomain https://technet.microsoft.com/en-us/library/ee617224.aspx
NEW QUESTION 6
Your network contains an Active Directory domain named contoso.com. The domain contains a file server named Server1 that runs Windows Server 2012 R2.
You view the effective policy settings of Server1 as shown in the exhibit. (Click the Exhibit button.)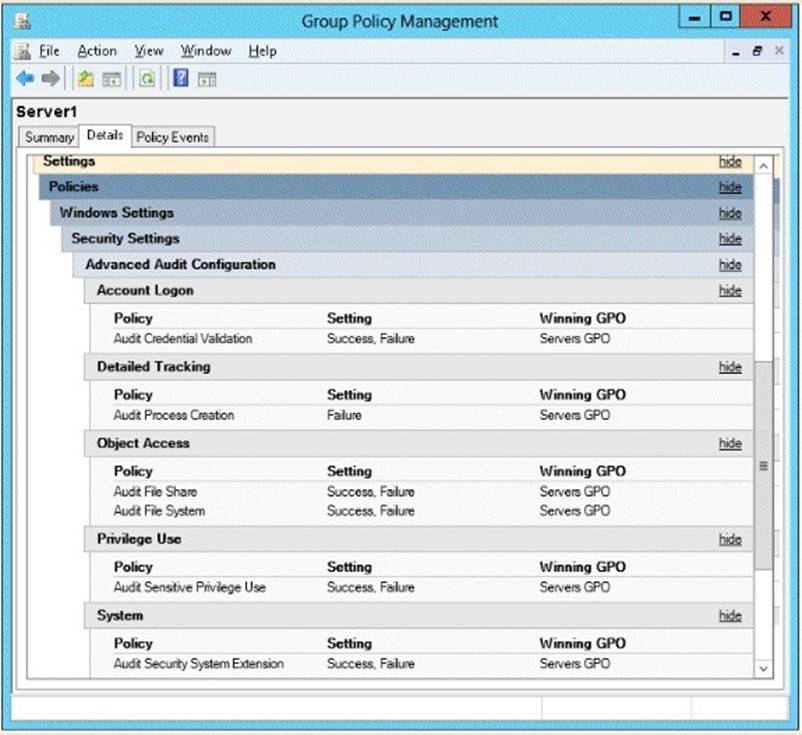
On Server1, you have a folder named C:Share1 that is shared as Share1. Share1 contains confidential data. A group named Group1 has full control of the content in Share1.
You need to ensure that an entry is added to the event log whenever a member of Group1 deletes a file in Share1.
What should you configure?
- A. the Audit File Share setting of Servers GPO
- B. the Sharing settings of C:Share1
- C. the Audit File System setting of Servers GPO
- D. the Security settings of C:Share1
Answer: D
Explanation:
You can use Computer Management to track all connections to shared resources on a Windows Server 2008 R2 system.
Whenever a user or computer connects to a shared resource, Windows Server 2008 R2 lists a connection in the Sessions node.
File access, modification and deletion can only be tracked, if the object access auditing is enabled you can see the entries in the event log.
To view connections to shared resources, type net session at a command prompt or follow these steps:
✑ In Computer Management, connect to the computer on which you created the
shared resource.
✑ In the console tree, expand System Tools, expand Shared Folders, and then select Sessions. You can now view connections to shares for users and computers.
To enable folder permission auditing, you can follow the below steps:
✑ Click start and run "secpol. msc" without quotes.
✑ Open the Local PoliciesAudit Policy
✑ Enable the Audit object access for "Success" and "Failure".
✑ Go to target files and folders, right click the folder and select properties.
✑ Go to Security Page and click Advanced.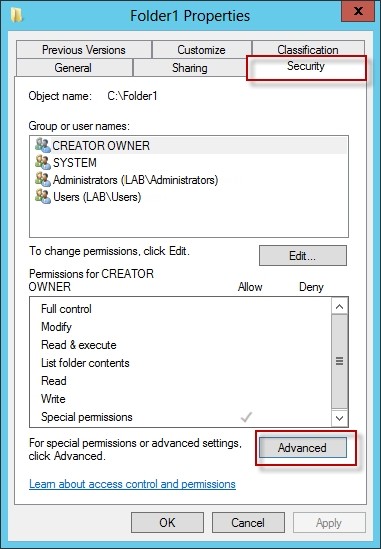
✑ Click Auditing and Edit.
✑ Click add, type everyone in the Select User, Computer, or Group.
✑ Choose Apply onto: This folder, subfolders and files.
✑ Tick on the box “Change permissions”
✑ Click OK.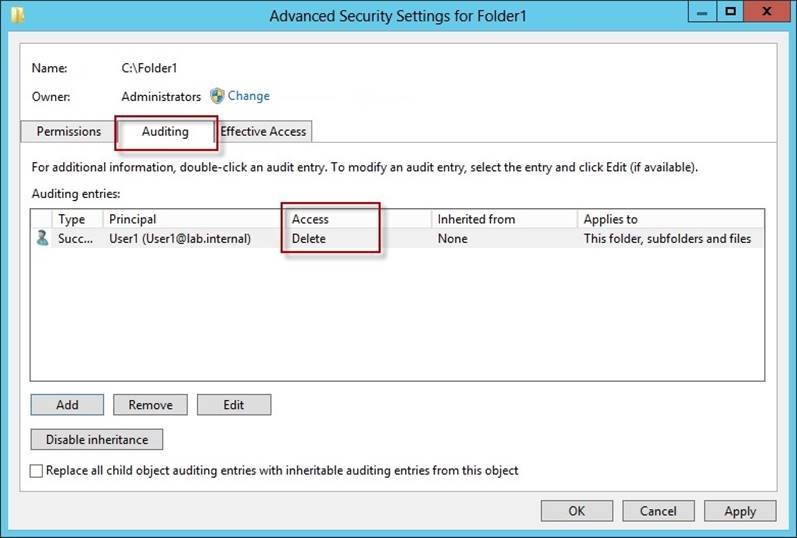
After you enable security auditing on the folders, you should be able to see the folder permission changes in the server's Security event log. Task Category is File System.
References:
http: //social. technet. microsoft. com/Forums/en-US/winservergen/thread/13779c78-0c73- 4477-8014-f2eb10f3f10f/
http: //technet. microsoft. com/en-us/library/cc753927(v=ws. 10). aspx
http: //social. technet. microsoft. com/Forums/en-US/winservergen/thread/13779c78-0c73- 4477-8014-f2eb10f3f10f/
http: //support. microsoft. com/kb/300549
http: //www. windowsitpro. com/article/permissions/auditing-folder-permission-changes http: //www. windowsitpro. com/article/permissions/auditing-permission-changes-on-a- folder
NEW QUESTION 7
Your network contains an Active Directory domain named contoso.com. The domain contains a domain controller named DC1.
You run ntdsutil as shown in the exhibit. (Click the Exhibit button.)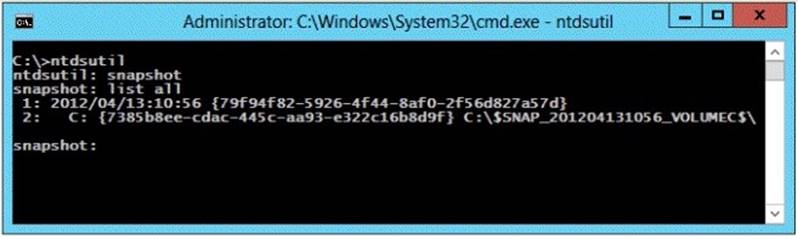
You need to ensure that you can access the contents of the mounted snapshot. What should you do?
- A. From the snapshot context of ntdsutil, run activate instance "NTDS".
- B. From a command prompt, run dsamain.exe -dbpath c:$snap_201204131056_volumec$windowsntdsntd
- C. dit -Idapport 389.
- D. From the snapshot context of ntdsutil, run mount {79f94f82-5926-4f44-8af0- 2f56d827a57d}.
- E. From a command prompt, run dsamain.exe -dbpath c:$snap_201204131056_volumec$windowsntdsntd
- F. dit -Idapport 33389.
Answer: D
Explanation:
By default, only members of the Domain Admins group and the Enterprise Admins group are allowed to view the snapshots because they contain sensitive AD DS data. If you want to access snapshot data from an old domain or forest that has been deleted, you can allow nonadministrators to access the data when you run Dsamain.exe.
If you plan to view the snapshot data on a domain controller, specify ports that are different from the ports that the domain controller will use.
A client starts an LDAP session by connecting to an LDAP server, called a Directory System Agent (DSA), by default on TCP port and UDP [7] port 389. The client then sends
an operation request to the server, and the server sends responses in return. With some exceptions, the client does not need to wait for a response before sending the next request, and the server may send the responses in any order. All information is transmitted using Basic Encoding Rules (BER).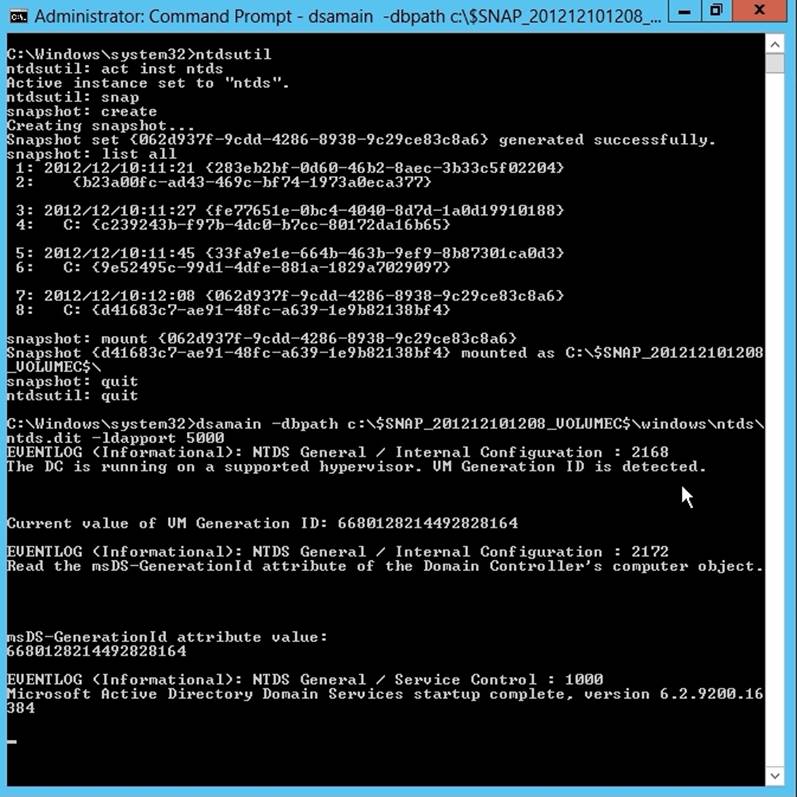
References:
http: //technet. microsoft. com/en-us/library/cc753609(v=ws. 10). aspx
NEW QUESTION 8
Your network contains one Active Directory domain named contoso.com. You pilot DirectAccess on the network.
During the pilot deployment, you enable DirectAccess only (or a group named
ContosoTest Computers.
Once the pilot is complete, you need to enable DirectAccess for all of the client computers in the domain.
What should you do?
- A. From Windows PowerShell, run the Set-DAServer cmdlet.
- B. From Remote Access Management Console, run the remote access Server Setup wizard.
- C. From Group Policy Management, modify the security filtering of an object named Direct Access Server Setting Group Policy
- D. From Group Policy Management, modify the security filtering of an object named Direct Access Client Setting Group Policy.
Answer: D
Explanation:
The simplified Direct Access wizard creates two GPOs and liks them to the domain: “DirectAccess Server Settings” contains Connection Security Settings and Firewall inboud rules for Direct Access. “DirectAccess Clients Settings” sets name resolution policy for NLS validation. Both GPOs have security filtering applied, with DirectAccess Clients Settings applied only to the DirectAccess enabled clients.
http://www.windowsecurity.com/articles-tutorials/Windows_Server_2012_Security/windows-server-2012-simplified-directaccess-wizard-overview-Part1.html
NEW QUESTION 9
Your network contains an Active Directory domain named contoso.com. You have a standard primary zone named contoso.com.
You need to ensure that only users who are members of a group named Group1 can create DNS records in the contoso.com zone. All other users must be prevented from creating, modifying, or deleting DNS records in the zone.
What should you do first?
- A. From the properties of the zone, change the zone type.
- B. From the properties of the zone, modify the start of authority (SOA) record.
- C. Run the New Delegation wizard for the zone.
- D. Run the Zone signing Wizard for the zone.
Answer: A
NEW QUESTION 10
Your network contains a single Active Directory domain named contoso.com. The domain contains a domain controller named DC1 that hosts the primary DNS zone for contoso.com.
All servers dynamically register their host names.
You install two new Web servers that host identical copies of your company's intranet website. The servers are configured as shown in the following table.
You need to use DNS records to load balance name resolution queries for intranet.contoso.com between the three Web servers.
What is the minimum number of DNS records that you should create manually?
- A. 1
- B. 2
- C. 3
- D. 4
Answer: B
NEW QUESTION 11
HOTSPOT
Your network contains an Active Directory domain named contoso.com. The domain contains servers named Server1 and Server2. Both servers have the DFS Replication role service installed.
You need to configure the DFS Replication environment to meet the following requirements:
✑ Increase the quota limit of the staging folder.
✑ Configure the staging folder cleanup process to provide the highest amount of free space possible.
Which cmdlets should you use to meet each requirement? To answer, select the appropriate options in the answer area.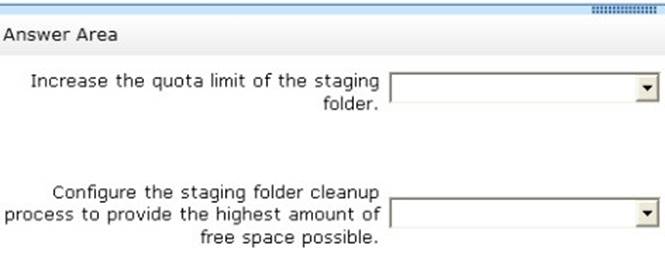
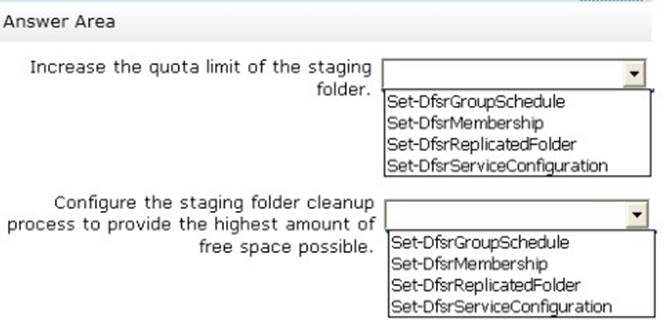
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 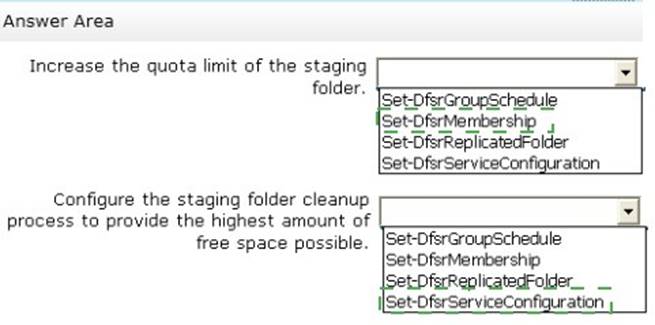
NEW QUESTION 12
Your network contains two servers named Server1 and Server2. Both servers run Windows Server 2012 R2.
On Server1, you create a Data Collector Set (DCS) named Data1. You need to export Data1 to Server2.
What should you do first?
- A. Right-click Data1 and click Data Manager.
- B. Right-click Data1 and click Export list.
- C. Right-click Data1 and click Properties.
- D. Right-click Data1 and click Save template.
Answer: D
NEW QUESTION 13
DRAG DROP
Your network contains an Active Directory domain named contoso.com. The domain contains a domain controller named DC1.
You need to create an Active Directory snapshot on DC1. Which four commands should you run?
To answer, move the four appropriate commands from the list of commands to the answer area and arrange them in the correct order.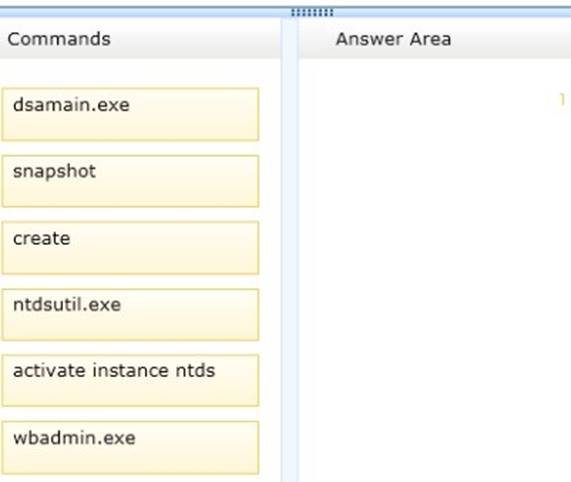
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
Box 1: ntdsutil
Box 2: snapshot
Box 3: activate instance ntds Box 4: create
Note:
Create a snapshot of AD DS in Windows Server 2012 R2 by using NTDSUTIL
1 – On the domain server, open command prompt and type ntdsutil and press Enter. 2- Next, type snapshot and press Enter.
3 – Next, type activate instance ntds and press Enter.
4 – Next, type create (this create command is to generate a snapshot of my AD) and press Enter.
NEW QUESTION 14
Your network contains an Active Directory domain named adatum.com. The domain contains a file server named Server1 that runs Windows Server 2012 R2.
All client computers run Windows 7.
You need to ensure that user settings are saved to \Server1Users. What should you do?
- A. From the properties of each user account, configure the Home folder settings.
- B. From a Group Policy object (GPO), configure the Folder Redirection settings.
- C. From the properties of each user account, configure the User profile settings.
- D. From a Group Policy object (GPO), configure the Drive Maps preference.
Answer: C
Explanation:
If a computer is running Windows 2000 Server or later on a network, users can store their profiles on the server. These profiles are called roaming user profiles.
NEW QUESTION 15
Your network contains an Active Directory domain named contoso.com. All domain controllers run Windows Server 2012 R2. The domain contains 500 client computers that run Windows 8 Enterprise.
You implement a Group Policy central store.
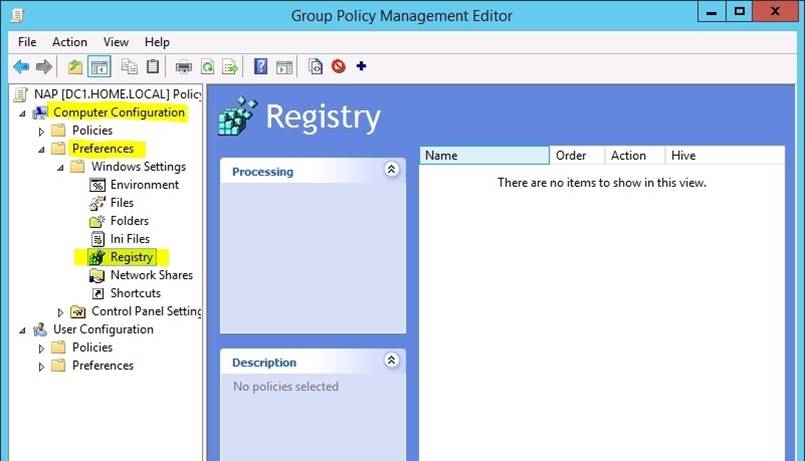
You have an application named App1. App1 requires that a custom registry setting be deployed to all of the computers.
You need to deploy the custom registry setting. The solution must minimize administrator effort.
What should you configure in a Group Policy object (GPO)?
- A. The Software Installation settings
- B. The Administrative Templates
- C. An application control policy
- D. The Group Policy preferences
Answer: D
Explanation:
✑ Open the Group Policy Management Console. Right-click the Group Policy object (GPO) that should contain the new preference item, and then click Edit.
✑ In the console tree under Computer Configuration or User Configuration, expand
the Preferences folder, and then expand the Windows Settings folder.
✑ Right-click the Registry node, point to New, and select Registry Item.
Group Policy preferences provide the means to simplify deployment and standardize configurations. They add to Group Policy a centralized system for deploying preferences (that is, settings that users can change later).
You can also use Group Policy preferences to configure applications that are not Group Policy-aware. By using Group Policy preferences, you can change or delete almost any registry setting, file or folder, shortcut, and more. You are not limited by the contents of Administrative Template files. The Group Policy Management
Editor (GPME) includes Group Policy preferences. References:
http: //technet.microsoft.com/en-us/library/gg699429.aspx
http: //www. unidesk. com/blog/gpos-set-custom-registry-entries-virtual-desktops-disabling- machine-password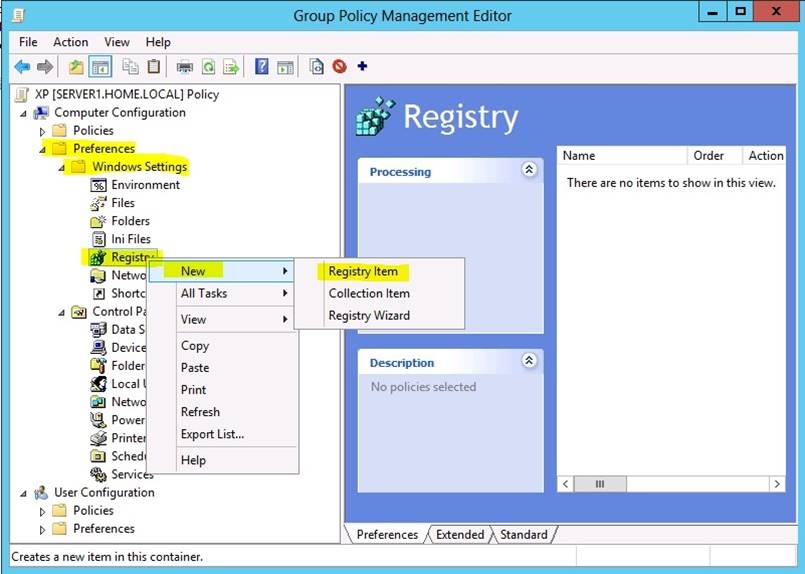
NEW QUESTION 16
HOTSPOT
Your network contains an Active Directory domain named contoso.com. The domain
contains a server named Print1.
Your company implements DirectAccess.
A user named User1 frequently works at a customer's office. The customer's office contains a print server named Print1.
While working at the customer's office, User1 attempts to connect to Print1. User1 connects to the Print1 server in contoso.com instead of the Print1 server at the customer's office.
You need to provide User1 with the ability to connect to the Print1 server in the customer's office.
Which Group Policy option should you configure?
To answer, select the appropriate option in the answer area.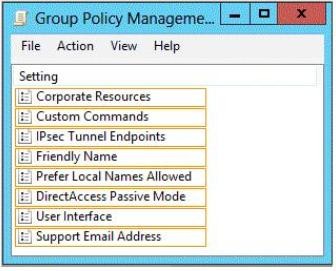
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 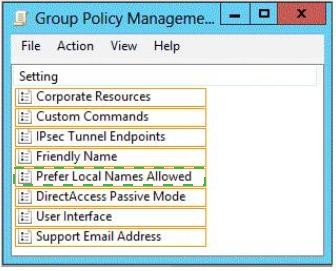
NEW QUESTION 17
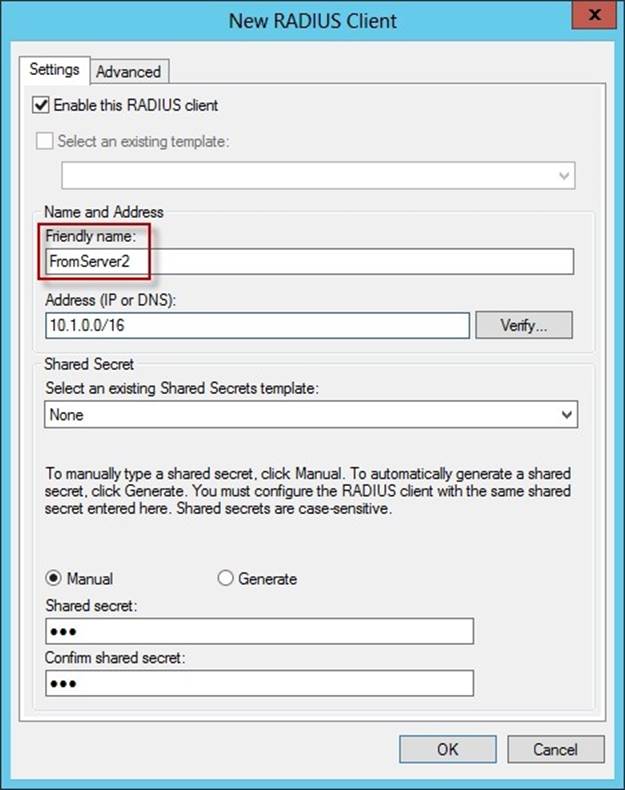
Your network contains an Active Directory domain named contoso.com. The domain contains a RADIUS server named Server1 that runs Windows Server 2012 R2.
You add a VPN server named Server2 to the network. On Server1, you create several network policies.
You need to configure Server1 to accept authentication requests from Server2. Which tool should you use on Server1?
- A. Server Manager
- B. Routing and Remote Access
- C. New-NpsRadiusClient
- D. Connection Manager Administration Kit (CMAK)
Answer: C
Explanation:
New-NpsRadiusClient -Name "NameOfMyClientGroup" -Address "10.1.0.0/16" - AuthAttributeRequired 0 -NapCompatible 0 -SharedSecret "SuperSharedSecretxyz" - VendorName "RADIUS Standard"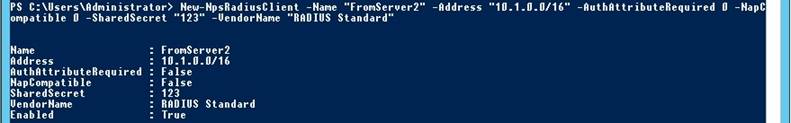
Reference:
http: //technet. microsoft. com/en-us/library/hh918425(v=wps. 620). aspx
http: //technet. microsoft. com/en-us/library/jj872740(v=wps. 620). aspx
http: //technet. microsoft. com/en-us/library/dd469790. aspx
NEW QUESTION 18
Your network contains an Active Directory forest. The forest contains two domains named contoso.com and fabrikam.com. All of the DNS servers in both of the domains run Windows Server 2012 R2.
The network contains two servers named Server1 and Server2. Server1 hosts an Active Directory-integrated zone for contoso.com. Server2 hosts an Active Directory-integrated zone for fabrikam.com. Server1 and Server2 connect to each other by using a WAN link.
Client computers that connect to Server1 for name resolution cannot resolve names in fabrikam.com.
You need to configure Server1 to resolve names in fabrikam.com. The solution must NOT require that changes be made to the fabrikam.com zone on Server2.
What should you create?
- A. A trust anchor
- B. A stub zone
- C. A zone delegation
- D. A secondary zone
Answer: B
Explanation:
A stub zone is a copy of a zone that contains only those resource records necessary to identify the authoritative Domain Name System (DNS) servers for that zone. A stub zone is used to resolve names between separate DNS namespaces. This type of resolution may be necessary when a corporate merger requires that the DNS servers for two separate DNS namespaces resolve names for clients in both namespaces.
NEW QUESTION 19
Your network contains an Active Directory domain named contoso.com. The domain contains more than 100 Group Policy objects (GPOs). Currently, there are no enforced GPOs.
A network administrator accidentally deletes the Default Domain Policy GPO. You do not have a backup of any of the GPOs.
You need to recreate the Default Domain Policy GPO. What should you use?
- A. Dcgpofix
- B. Get-GPOReport
- C. Gpfixup
- D. Gpresult
- E. Gpedi
- F. msc
- G. Import-GPO
- H. Restore-GPO
- I. Set-GPInheritance
- J. Set-GPLink
- K. Set-GPPermission
- L. Gpupdate
- M. Add-ADGroupMember
Answer: A
Explanation:
Dcgpofix
Restores the default Group Policy objects to their original state (that is, the default state after initial installation).
Reference: http: //technet. microsoft. com/en-us/library/hh875588(v=ws. 10). aspx
NEW QUESTION 20
Note: This question is part of a series of questions that use the same or similar answer choices. An answer choice may be correct for more than one question in the series. Each question is independent of the other questions in this series. Information and details provided in a question apply only to that question.
Your network contains an Active Directory domain named contoso.com. The domain contains more than 100 Group Policy objects (GPOs). Currently, there are no enforced GPOs.
You have a GPO named GPO1 that is linked to the domain. You need to configure GPO1 to apply settings to Group1 only. You need to configure GPO1 to apply settings to Group1 only. What should you use?
- A. Dcgpofix
- B. Get-GPOReport
- C. Gpfixup
- D. Gpresult
- E. Gpedi
- F. msc
- G. Import-GPO
- H. Restore-GPO
- I. Set-GPInheritance
- J. Set-GPLink
- K. Set-GPPermission
- L. Gpupdate
- M. Add-ADGroupMember
Answer: C
NEW QUESTION 21
You have a server named Server1 that runs Windows Server 2012 R2. Server1 has the File Server Resource Manager role service installed.
Server1 has a folder named Folder1 that is used by the sales department.
You need to ensure that an email notification is sent to the sales manager when a File Screening Audit report is generated.
What should you configure on Server1?
- A. a file group
- B. a file screen
- C. a file screen exception
- D. a storage report task
Answer: D
Explanation:
From the Storage Reports Management node, you can generate reports that will help you understand file use on the storage server. You can use the storage reports to monitor disk usage patterns (by file type or user), identify duplicate files and dormant files, track quota usage, and audit file screening.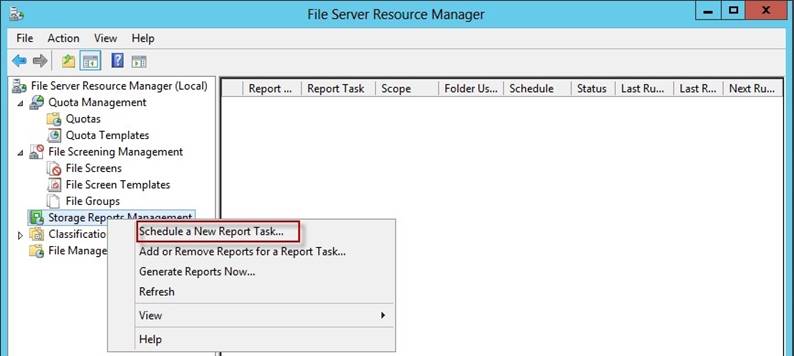
Before you run a File Screen Audit report, in the File Server Resource Manager Options dialog box, on the File Screen Audit tab, verify that the Record file screening activity in the auditing database check box is selected.
Reference:
http: //technet. microsoft. com/en-us/library/cc755988. aspx
http: //technet. microsoft. com/en-us/library/cc730822. aspx
http: //technet. microsoft. com/en-us/library/cc770594. aspx
http: //technet. microsoft. com/en-us/library/cc771212. aspx
http: //technet. microsoft.com/en-us/library/cc732074. aspx
NEW QUESTION 22
Your network contains an Active Directory domain named contoso.com. All domain controllers run Windows Server 2012 R2.
The domain contains 200 Group Policy objects (GPOs).
An administrator named Admin1 must be able to add new WMI filters from the Group Policy Management Console (GPMC).
You need to delegate the required permissions to Admin1. The solution must minimize the number of permissions assigned to Admin1.
What should you do?
- A. From Active Directory Users and Computers, add Admin1 to the WinRMRemoteWMIUsers group.
- B. From Group Policy Management, assign Creator Owner to Admin1 for the WMI Filters container.
- C. From Active Directory Users and Computers, add Admin1 to the Domain Admins group.
- D. From Group Policy Management, assign Full control to Admin1 for the WMI Filters container.
Answer: D
Explanation:
Users with Full control permissions can create and control all WMI filters in the domain, including WMI filters created by others.
Users with Creator owner permissions can create WMI filters, but can only control WMI filters that they create.
Reference: http://technet.microsoft.com/en-us/library/cc757429(v=ws.10).aspx
NEW QUESTION 23
Your network contains a Hyper-V host named Hyperv1. Hyperv1 runs Windows Server 2012 R2.
Hyperv1 hosts four virtual machines named VM1, VM2, VM3, and VM4. AH of the virtual machines run Windows Server 2008 R2.
You need to view the amount of memory resources and processor resources that VM4 currently uses.
Which tool should you use on Hyperv1?
- A. Windows System Resource Manager (WSRM)
- B. Task Manager
- C. Hyper-V Manager
- D. Resource Monitor
Answer: C
Explanation:
Hyper-V Performance Monitoring Tool
Know which resource is consuming more CPU. Find out if CPUs are running at full capacity or if they are being underutilized. Metrics tracked include Total CPU utilization, Guest CPU utilization, Hypervisor CPU utilization, idle CPU utilization, etc.
WSRM is deprecated starting with Windows Server 2012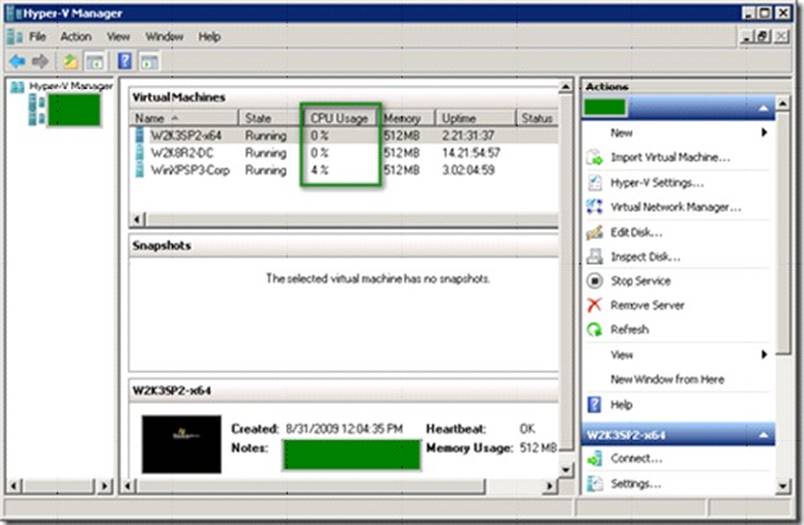
NEW QUESTION 24
Your network contains an Active Directory domain named contoso.com. The domain contains two member servers named Server1 and Server2. All servers run Windows Server
2012 R2.
Server1 and Server2 are nodes in a Hyper-V cluster named Cluster1. Cluster1 hosts 10 virtual machines. All of the virtual machines run Windows Server 2012 R2 and are members of the domain.
You need to ensure that the first time a service named Service1 fails on a virtual machine, the virtual machine is moved to a different node.
You configure Service1 to be monitored from Failover Cluster Manager. What should you configure on the virtual machine?
- A. From the General settings, modify the Startup type.
- B. From the General settings, modify the Service status.
- C. From the Recovery settings of Service1, set the First failure recovery action to Take No Action.
- D. From the Recovery settings of Service1, set the First failure recovery action to Restart the Service.
Answer: C
Explanation:
Configure the virtual machine to take no action through Hyper-V if the physical computer shuts down by modifying the Automatic Stop Action setting to None. Virtual machine state must be managed through the Failover Clustering feature.
Virtual machine application monitoring and management
In clusters running Windows Server 2012, administrators can monitor services on clustered virtual machines that are also running Windows Server 2012. This functionality extends the high-level monitoring of virtual machines that is implemented in Windows Server 2008 R2 failover clusters. If a monitored service in a virtual machine fails, the service can be restarted, or the clustered virtual machine can be restarted or moved to another node (depending on service restart settings and cluster failover settings).
This feature increases the uptime of high availability services that are running on virtual machines within a failover cluster.
Windows Server 2012 Failover Cluster introduces a new capability for Hyper-V virtual machines (VMs), which is a basic monitoring of a service within the VM which causes the VM to be rebooted should the monitored service fail three times. For this feature to work the following must be configured:
✑ Both the Hyper-V servers must be Windows Server 2012 and the guest OS running in the VM must be Windows Server 2012.
✑ The host and guest OSs are in the same or at least trusting domains.
✑ The Failover Cluster administrator must be a member of the local administrator's group inside the VM.
Ensure the service being monitored is set to Take No Action (see screen shot below) within the guest VM for Subsequent failures (which is used after the first and second failures) and is set via the Recovery tab of the service properties within the Services application (services. msc).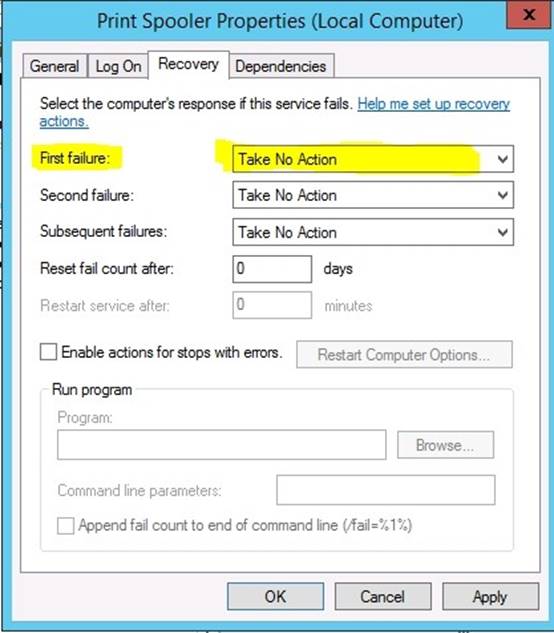
Within the guest VM, ensure the Virtual Machine Monitoring firewall exception is enabled for the Domain network by using the Windows Firewall with Advanced Security application or by using the Windows PowerShell command below: Set-NetFirewallRule -DisplayGroup "Virtual Machine Monitoring" -Enabled True.
After the above is true, enabling the monitoring is a simple process:
✑ Launch the Failover Cluster Manager tool.
✑ Navigate to the cluster - Roles.
✑ Right click on the virtual machine role you wish to enable monitoring for and under More Actions select Configure Monitoring.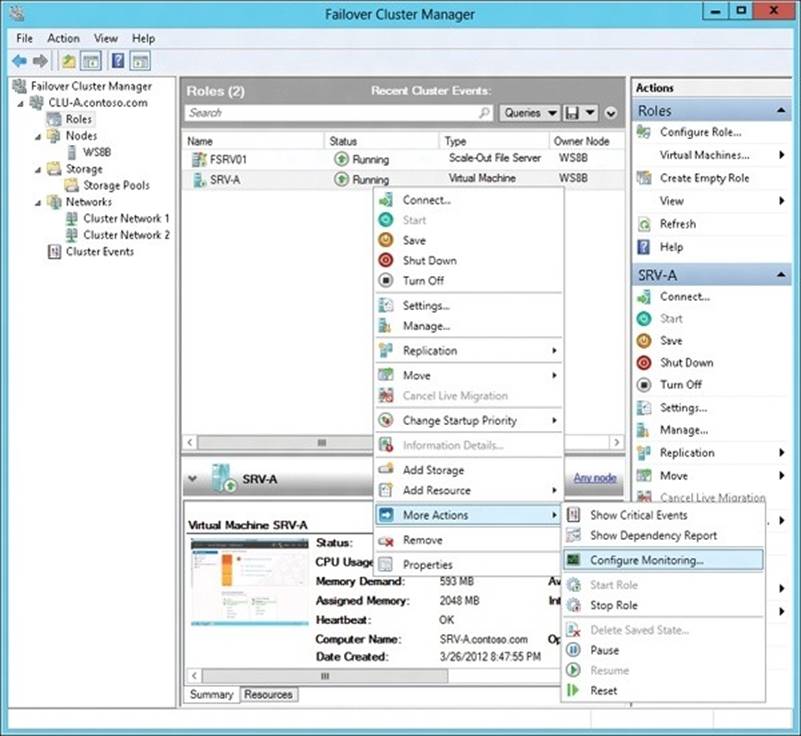
✑ The services running inside the VM will be gathered and check the box for the services that should be monitored and click OK.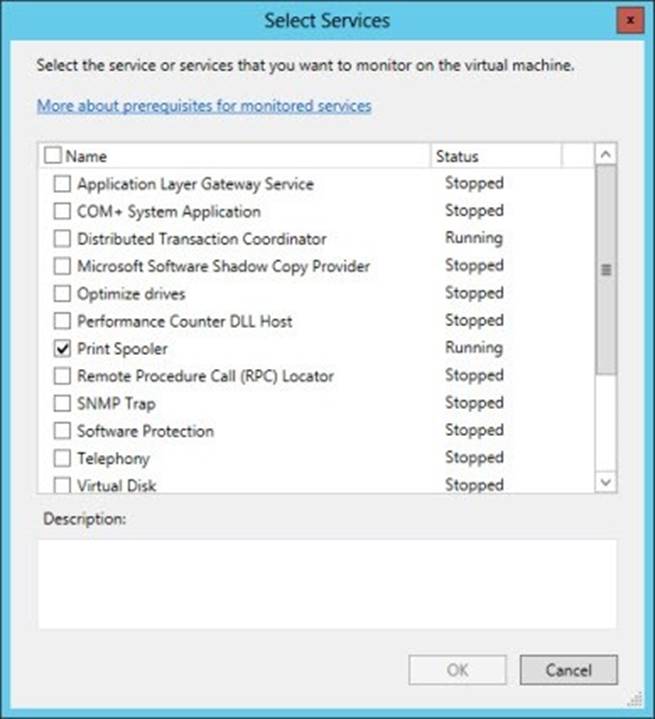
You are done!
Monitoring can also be enabled using the Add-ClusterVMMonitoredItemcmdlet and - VirtualMachine, with the -Service parameters, as the example below shows: PS C:Windowssystem32> Add-ClusterVMMonitoredItem -VirtualMachine savdaltst01 - Service spooler
References:
http: //sportstoday. us/technology/windows-server-2012---continuous-availability-%28part- 4%29---failover-clustering-enhancements---virtual-machine-monitoring-. aspx
http: //windowsitpro. com/windows-server-2012/enable-windows-server-2012-failover- cluster-hyper-v-vm-monitoring
http: //technet. microsoft. com/en-us/library/cc742396. aspx
NEW QUESTION 25
HOTSPOT
Your network contains an Active Directory domain named contoso.com. The domain contains the users shown in the following table.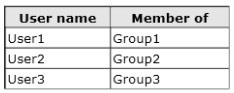
You have a Network Policy Server (NPS) server that has the network policies shown in the following table.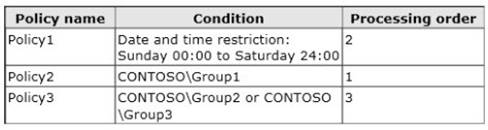
User1, User2, and User3 plan to connect to the network by using a VPN. You need to identify which network policy will apply to each user.
What should you identify?
To answer, select the appropriate policy for each user in the answer area.

- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
When you configure multiple network policies in NPS, the policies are an ordered list of rules. NPS evaluates the policies in listed order from first to last. If there is a network policy that matches the connection request, NPS uses the policy to determine whether to grant or deny access to the user or computer connection.
Network policies are evaulated according to the processing order. Once a match is found, no further network policy is processed.
Policies are processed in this order:
-Policy2 (applies only to members of Group1)
-Policy1 (applies to all users during specified time slot)
-Policy3 (applies only to members of Group2)
Since policy1 will always apply (sunday 0:00 to saturday 24:00 = always), policy3 will never be evaluated.
Correct answer is : User1: Policy2 User2: Policy1 User3: Policy1
https://technet.microsoft.com/en-us/library/cc732724(v=ws.10).aspx
NEW QUESTION 26
HOTSPOT
Your company has two offices. The offices are located in Montreal and Seattle.
The network contains an Active Directory domain named contoso.com. The domain contains servers named Server1 and Server2. Server1 is located in the Seattle office. Server2 is located in the Montreal office. Both servers run Windows Server 2012 R2 and have the Windows Server Update Services (WSUS) server role installed.
You need to configure Server2 to download updates that are approved on Server1 only.
What cmdlet should you run? To answer, select the appropriate options in the answer area.
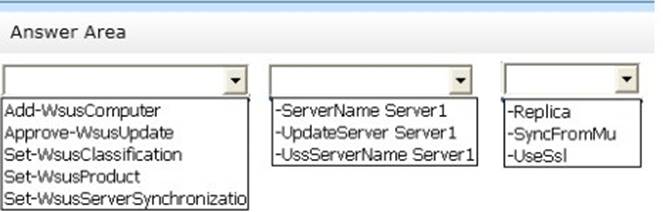
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 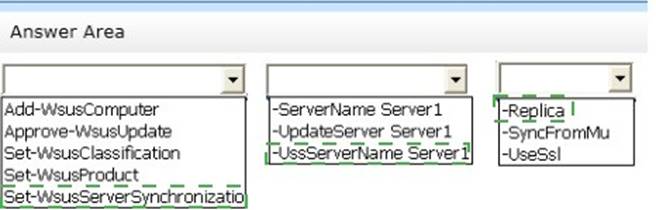
NEW QUESTION 27
You have a server named Server1 that runs Windows Server 2012 R2. Server1 has the Windows Server Update Services server role installed.
Server1 stores update files locally in C:Updates.
You need to change the location in which the update files are stored to D:Updates. What should you do?
- A. From the Update Services console, run the Windows Server Update Services Configuration Wizard.
- B. From a command prompt, run wsusutil.exe and specify the movecontent parameter.
- C. From the Update Services console, configure the Update Files and Languages option.
- D. From a command prompt, run wsusutil.exe and specify the export parameter.
Answer: B
Explanation:
You might need to change the location where WSUS stores updates locally. This might be required if the disk becomes full and there is no longer any room for new updates. You might also have to do this if the disk where updates are stored fails and the replacement disk uses a new drive letter.
You accomplish this move with the movecontent command of WSUSutil.exe, a command- line tool that is copied to the file system of the WSUS server during WSUS Setup. By default, Setup copies WSUSutil.exe to the following location: WSUSInstallationDrive:Program FilesMicrosoft Windows Server Update ServicesTools
NEW QUESTION 28
Your network contains two Active Directory forests named contoso.com and dev.contoso.com. The contoso.com forest contains a domain controller named DC1. The dev.contoso.com forest contains a domain controller named DC2. Each domain contains an organizational unit (OU) named OU1.
Dev.contoso.com has a Group Policy object (GPO) named GPO1. GPO1 contains 200 settings, including several settings that have network paths. GPO1 is linked to OU1.
You need to copy GPO1 from dev.contoso.com to contoso.com. What should you do first on DC2?
- A. From the Group Policy Management console, right-click GPO1 and select Copy.
- B. Run the mtedit.exe command and specify the /Domaintcontoso.com /DC: DC 1 parameter.
- C. Run the Save-NetGpocmdlet.
- D. Run the Backup-Gpocmdlet.
Answer: A
Explanation:
To copy a Group Policy object:
In the GPMC console tree, right-click the GPO that you want to copy, and then click Copy. To create a copy of the GPO in the same domain as the source GPO, right-click Group Policy objects, click Paste, specify permissions for the new GPO in the Copy GPO box, and then click OK.
For copy operations to another domain, you may need to specify a migration table.
The Migration Table Editor (MTE) is provided with Group Policy Management Console (GPMC) to facilitate the editing of migration tables. Migration tables are used for copying or importing Group Policy objects (GPOs) from one domain to another, in cases where the GPOs include domain-specific information that must be updated during copy or import. Source WS2008R2: Backup the existing GPOs from the GPMC, you need to ensure that the “Group Policy Objects” container is selected for the “Backup Up All” option to be available.
Copy a Group Policy Object with the Group Policy Management Console (GPMC)
You can copy a Group Policy object (GPO) either by using the drag-and-drop method or right-click method.
Applies To: Windows 8, Windows Server 2008 R2, Windows Server 2012
References:
http://technet.microsoft.com/en-us/library/cc785343(v=WS.10).aspx http://technet.microsoft.com/en-us/library/cc733107.aspx
NEW QUESTION 29
......
Thanks for reading the newest 70-411 exam dumps! We recommend you to try the PREMIUM Dumpscollection 70-411 dumps in VCE and PDF here: http://www.dumpscollection.net/dumps/70-411/ (294 Q&As Dumps)