Microsoft 70-744 Preparation 2021
Cause all that matters here is passing the Microsoft 70-744 exam. Cause all that you need is a high score of 70-744 Securing Windows Server 2021 exam. The only one thing you need to do is downloading Testking 70-744 exam study guides now. We will not let you down with our money-back guarantee.
Free demo questions for Microsoft 70-744 Exam Dumps Below:
NEW QUESTION 1
Your network contains an Active Directory domain named contoso.com. All servers in the domain run Windows Server 2021.All client computers run Windows 10.
Your company has deployed the Local Administrator Password Solution (LAPS).
Client computers in the finance department are located in an organizational unit (OU) named Finance.
Each finance computer has a custom administrative account named FinAdmin. You discover that the FinAdmin accounts are not managed by LAPS.
You need to ensure that the FinAdmin accounts are managed by LAPS. What should you do?
- A. On the finance computers, register the AdmPwd.ps Windows PowerShell module and then run the ResetAdmPwdPassword cmdlet
- B. Modify the Password Policy in a Group Policy object (GPO).
- C. Modify the LAPS settings in a Group Policy object (GPO).
- D. On the finance computer
- E. rename the FinAdmin accounts to Administrato
Answer: C
Explanation:
Use the GPO Setting “Name of administrator account to manage” for LAPS to manage secondary administrative accounts which is not named as “Administrator”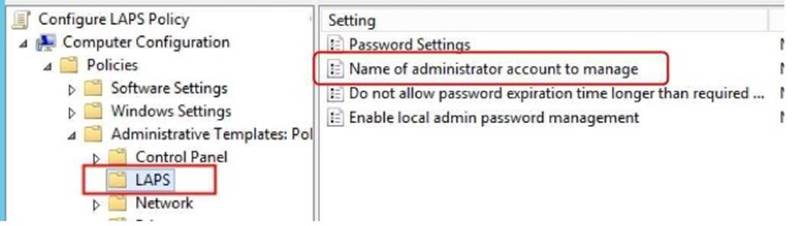
NEW QUESTION 2
You are building a guarded fabric. You need to configure Admin-trusted attestation. Which cmdlet should you use?
- A. Add-HgsAttestationHostGroup
- B. Add-HgsAttestationTpmHost
- C. Add-HgsAttestationCIPolicy
- D. Add-HgsAttestationTpmPolicy
Answer: A
Explanation:
Authorize Hyper-V hosts using Admin-trusted attestation
https://docs.microsoft.com/en-us/windows-server/virtualization/guarded-fabric-shieldedvm/ guarded-fabric-addhost-information-for-admin-trusted-attestation
NEW QUESTION 3
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this sections, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You manage a file server that runs Windows Server 2021. The file server contains the volumes configured as shown in the following table.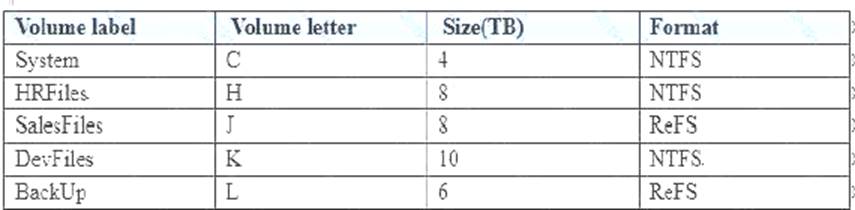
You need to encrypt DevFiles by using BitLocker Drive Encryption (ButLocker). Solution: You run the manage-bde.exe command and specify the –on parameter. Does this meet the goal?
- A. Yes
- B. No
Answer: A
Explanation:
References:
https://docs.microsoft.com/en-us/windows-server/administration/windows-commands/managebde- on
NEW QUESTION 4
Your data center contains 10 Hyper-V hosts that host 100 virtual machines.
You plan to secure access to the virtual machines by using the Datacenter Firewall service.
You have four servers available for the Datacenter Firewall service. The servers are configured as shown in the following table.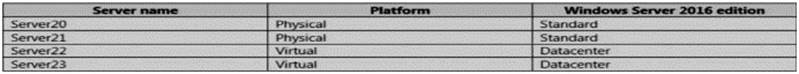
You need to install the required server roles for the planned deployment Which server role should you deploy? Choose Two.
- A. Server role to deploy: Multipoint Services
- B. Server role to deploy: Network Controller
- C. Server role to deploy: Network Policy and Access Services
- D. Servers on which to deploy the server role: Server20 and Server21
- E. Servers on which to deploy the server role: Server22 and Server23
Answer: BE
Explanation:
Datacenter Firewall is a new service included with Windows Server 2021. It is a network layer, 5- tuple (protocol, source and destination port numbers, source and destination IP addresses), stateful, multitenant firewall. When deployed and offered as a service by the serviceprovider, tenant administrators can install and configure firewall policies to help protect their virtual networks from unwanted traffic originating from Internet and intranet networks.
https://docs.microsoft.com/en-us/windows-server/networking/sdn/technologies/networkcontroller/ networkcontroller
Network Controller Features
The following Network Controller features allow you to configure and manage virtual and physical network
devices and services.
i) Firewall Management (Datacenter Firewall)
ii) Software Load Balancer Management
iii) Virtual Network Management
iv) RAS Gateway Management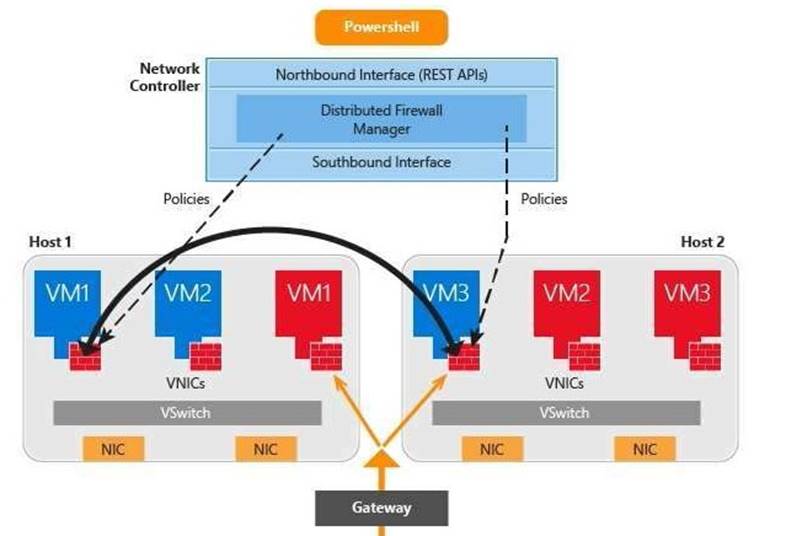
https://docs.microsoft.com/en-us/windows-server/networking/sdn/plan/installation-andpreparationrequirements- for-deploying-network-controller
Installation requirements
Following are the installation requirements for Network Controller.
For Windows Server 2021 deployments, you can deploy Network Controller on one or more computers, one or more VMs, or a combination of computers and VMs.
All VMs and computers planned as Network Controller nodes must be running Windows Server 2021 Datacenter edition.
NEW QUESTION 5
Note: This question is part of a series of questions that present the same scenario. Each question In the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question In this section, you will NOT be able to return to It. As a result, these questions will not appear in the review screen.
Your network contains an Active Directory domain named contoso.com. The domain contains a computer named Computer1 that runs Windows 10. Computer1 connects to a home network and a corporate network.
The corporate network uses the 172.16.0.0/24 address space internally. Computer1 runs an application named App1 that listens to port 8080.
You need to prevent connections to App1 when Computer1 is connected to the home network. Solution: From Group Policy Management, You create an Applocker rule.
- A. Yes
- B. No
Answer: B
Explanation:
AppLocker does not filter incoming network traffic, what you actually need is Windows Firewall Inbound Rule on the Private profile.
https://technet.microsoft.com/en-us/library/dd759068(v=ws.11).aspx
NEW QUESTION 6
The network contains an Active Directory domain named contoso.com. The domain contains the servers configured as shown in the following table.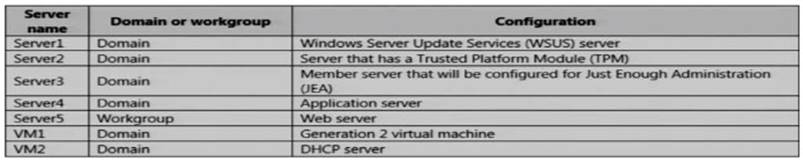
All servers run Windows Server 2021. All client computers run Windows 10 and are domain members.
All laptops are protected by using BitLocker Drive Encryption (BitLocker).You have an organizational unit (OU) named OU1 that contains the computer accounts of application servers.
An OU named OU2 contains the computer accounts of the computers in the marketing department. A Group Policy object (GPO) named GP1 is linked to OU1.
A GPO named GP2 is linked to OU2.
All computers receive updates from Server1. You create an update rule named Update1.
You need to implement BitLocker Network Unlock for all of the laptops. Which server role should you deploy to the network?
- A. Network Controller
- B. Windows Deployment Services
- C. Host Guardian Service
- D. Device Heath Attestation
Answer: B
Explanation:
https://docs.microsoft.com/en-us/windows/device-security/bitlocker/bitlocker-how-to-enablenetwork- unlock Network Unlock core requirements
Network Unlock must meet mandatory hardware and software requirements before the feature can automatically unlock domain joined systems. These
requirements include:
You must be running at least Windows 8 or Windows Server 2012.
Any supported operating system with UEFI DHCP drivers can be Network Unlock clients.
A server running the Windows Deployment Services (WDS) role on any supported server operating system.
BitLocker Network Unlock optional feature installed on any supported server operating system. A DHCP server, separate from the WDS server.
Properly configured public/private key pairing. Network Unlock Group Policy settings configured.
NEW QUESTION 7
Your network contains an Active Directory forest named contoso.com. The forest functional level is Windows Server 2012. The forest contains a single domain. The domain contains multiple Hyper-V hosts.
You plan to deploy guarded hosts.
You deploy a new server named Server22 to a workgroup.
You need to configure Server22 as a Host Guardian Service server.
What should you do before you initialize the Host Guardian Service on Server22?
- A. Install the Active Directory Domain Services server role on Server22.
- B. Obtain a certificate.
- C. Raise the forest functional level.
- D. Join Server22 to the domai
Answer: D
Explanation:
https://docs.microsoft.com/en-us/windows-server/virtualization/guarded-fabric-shieldedvm/guarded-fabricchoose-where-to-install-hgs
The only technical requirement for installing HGS in an existing forest is that it be added to the root domain;
non-root domains are not supported.
NEW QUESTION 8
You have a guarded fabric and a Host Guardian Service server named HGS1.
You deploy a Hyper-V host named Hyper1, and configure Hyper1 as part of the guarded fabric. You plan to deploy the first shielded virtual machine. You need to ensure that you can run the virtual machine on Hyper1.
What should you do?
- A. On Hyper1, run the Invoke-WebRequest cmdlet, and then run the Import-HgsGuardian cmdlet.
- B. On HGS1, run the Invoke-WebRequest cmdlet, and then run the Import-HgsGuardian cmdlet.
- C. On Hyper1, run the Export-HgsKeyProtectionState cmdlet, and then run the Import-HgsGuardian cmdlet.
- D. On HGS1, run the Export-HgsKeyProtectionState cmdlet, and then run the Import-HgsGuardian cmdlet
Answer: A
Explanation:
https://blogs.technet.microsoft.com/datacentersecurity/2021/06/06/step-by-step-creating-shieldedvms- withoutvmm/
The first step is to get the HGS guardian metadata from the HGS server, and use it to create the Key protector.
To do this, run the following PowerShell command
on a guarded host or any machine that can reach the HGS server:
Invoke-WebRequest http://<HGSServer”>FQDN>/KeyProtection/service/metadata/2014- 07/metadata.xml –
OutFile C:\HGSGuardian.xml Shield the VM
Each shielded VM has a Key Protector which contains one owner guardian, and one or more HGS guardians.
The steps below illustrate the process of getting the guardians, create the Key Protector in order to shield the VM.
Run the following cmdlets on a tenant host “Hyper1”:
# SVM is the VM name which to be shielded
$VMName = ‘SVM’
# Turn off the VM first. You can only shield a VM when it is powered off Stop-VM –VMName $VMName
# Create an owner self-signed certificate
$Owner = New-HgsGuardian –Name ‘Owner’ –GenerateCertificates
# Import the HGS guardian
$Guardian = Import-HgsGuardian -Path ‘C:\HGSGuardian.xml’ -Name ‘TestFabric’ – AllowUntrustedRoot
# Create a Key Protector, which defines which fabric is allowed to run this shielded VM
$KP = New-HgsKeyProtector -Owner $Owner -Guardian $Guardian -AllowUntrustedRoot
# Enable shielding on the VM
Set-VMKeyProtector –VMName $VMName –KeyProtector $KP.RawData
# Set the security policy of the VM to be shielded
Set-VMSecurityPolicy -VMName $VMName -Shielded $true
# Enable vTPM on the VM
Enable-VMTPM -VMName $VMName
NEW QUESTION 9
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to It. As a result, these questions will not appear in the review screen.
Your network contains an Active Directory domain named contoso.com. All servers run Windows Server 2021. All client computers run Windows 10.
The relevant objects in the domain are configured as shown in the following table.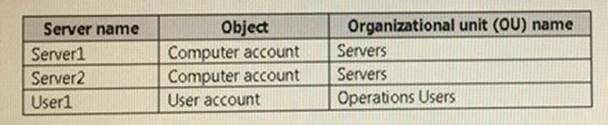
You need to assign User1 the right to restore files and folders on Server1 and Server2.
Solution: You create a Group Policy object (GPO), you link the GPO to the Servers OU, and then you modify the Users Rights Assignment in the GPO.
Does this meet the goat?
- A. Yes
- B. No
Answer: B
Explanation:
References:
https://technet.microsoft.com/en-us/library/cc771990(v=ws.11).aspx
NEW QUESTION 10
Your network contains an Active Directory domain named contoso.com.
You are deploying Microsoft Advanced Threat Analytics (ATA) to the domain.
You install the ATA Center on server named Server1 and the ATA Gateway on a server named Served. You need to ensure that Server2 can collect NTLM authentication events.
What should you configure?
- A. the domain controllers to forward Event ID 4776 to Server2
- B. the domain controllers to forward Event ID 1000 to Server1
- C. Server2 to forward Event ID 1026 to Server1
- D. Server1 to forward Event ID 1000 to Server2
Answer: A
Explanation:
https://docs.microsoft.com/en-us/advanced-threat-analytics/ata-architecture
ATA monitors your domain controller network traffic by utilizing port mirroring to an ATA Gateway using physical or virtual switches.
If you deploy the ATA Lightweight Gateway directly on your domain controllers, it removes the requirement for port mirroring.
In addition, ATA can leverage Windows events (forwarded directly from your domain controllers or from a SIEM server) and analyze the data for attacks and threats.
See the GREEN line in the following figure, forward event ID 4776 which indicates NTLM authentication is being used to ATA Gateway Server2.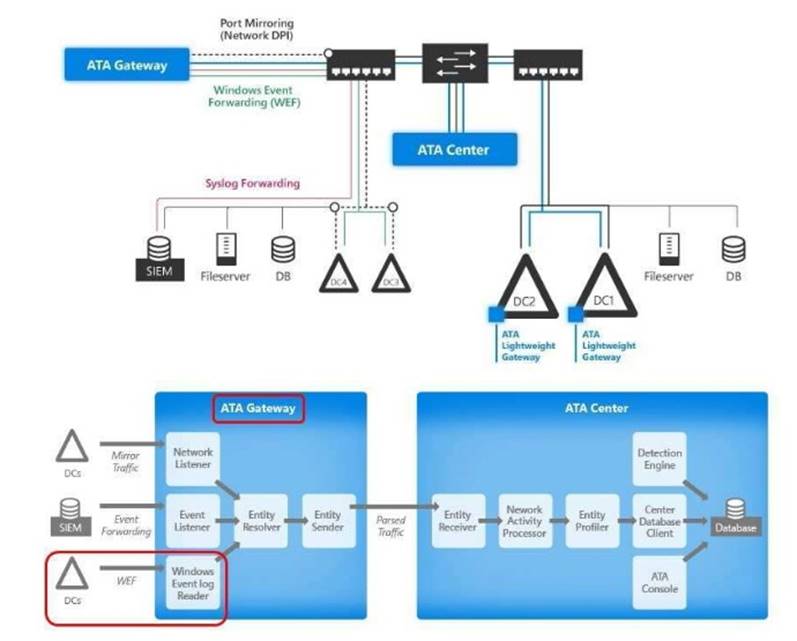
NEW QUESTION 11
HOTSPOT
Your network contains an Active Directory domain named contoso.com. You have an organizational unit (OU) named Secure that contains all servers.
You install Microsoft Security Compliance Manager (SCM) 4.0 on a server named Server1. You need to export the SCM Pnnt Server Secunty baseline and to deploy the baseline to a server named Server2.
What should you do? To answer, select the appropnate options in the answer area.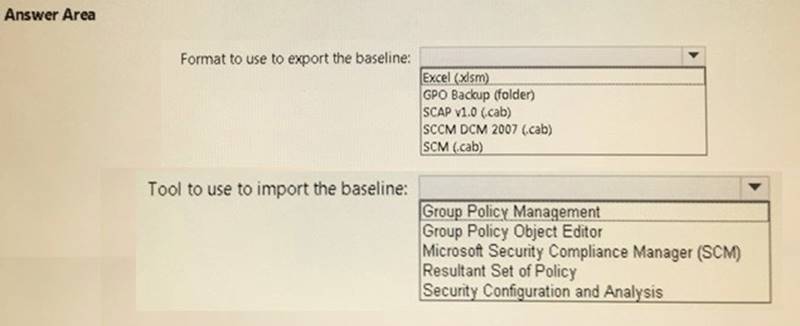
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
When the security settings is exported from SCM 4 in a GPO (folder) format, with a long GUID name
You have to import it to GPO by using “Group Policy Management”, right-click the GPO and use “Import
Settings” button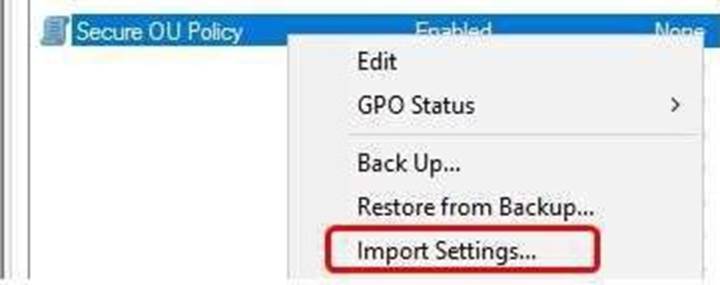
Do not confuse with security template .inf files. Only security template .INF file (which is a single file, not a
folder) could be imported to a GPO by Group Policy Object Editor
NEW QUESTION 12
Note: Thb question Is part of a series of questions that present the same scenario. Each question In the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you willNOTbeabletorrturntoit.Asa result, these questions will not appear in the review screen.
Your network contains an Active Directory domain named contoso.com. The domain contains multiple Hyper-V hosts.
You need to deploy several critical line-of-business applications to the network to meet the following requirements:
*The resources of the applications must be isolated from the physical host
*Each application must be prevented from accessing the resources of the other applications.
*The configurations of the applications must be accessible only from the operating system that hosts the application.
Solution: You deploy one Windows container to host all of the applications. Does this meet the goal?
- A. Yes
- B. No
Answer: B
Explanation:
References:
https://docs.microsoft.com/en-us/virtualization/windowscontainers/about/
NEW QUESTION 13
Your network contains an Active Directory domain named contoso.com. The domain contains several shielded virtual machines.
You deploy a new server named Server1 that runs Windows Server 2021. You install the Hyper-V server role on Server1.
You need to ensure that you can host shielded virtual machines on Server1. What should you install on Server1?
- A. Host Guardian Hyper-V Support
- B. BitLocker Network Unlock
- C. the Windows Biometric Framework (WBF)
- D. VM Shielding Tools for Fabric Management
Answer: A
Explanation:
This questions mentions “The domain contains several shielded virtual machines.”, which indicates a working Host Guardian Service deployment was completed.
https://docs.microsoft.com/en-us/windows-server/virtualization/guarded-fabric-shieldedvm/guarded-fabricguarded-host-prerequisites
For a new Hyper-V server to utilize an existing Host Guardian Service, install the “Host Guardian Hyper-V
Support”.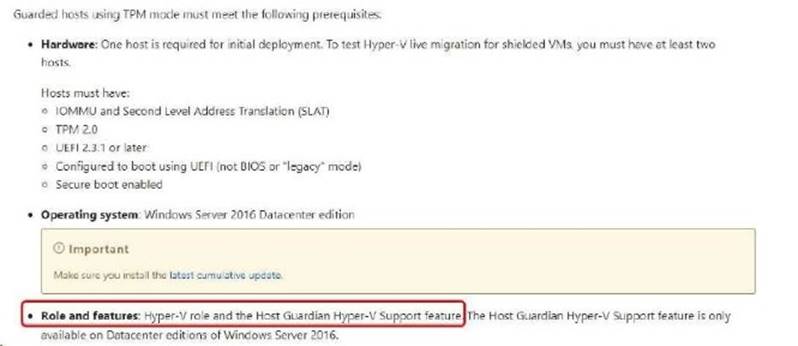
NEW QUESTION 14
DRAG DROP
Your network contains an Active Directory domain named contoso.com. The domain contains a user named User1 and a computer named Computer1. Remote Server Administration Tools (RSAT) is installed on Computer1.
You need to add User1 as a data recovery agent in the domain.
Which four actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.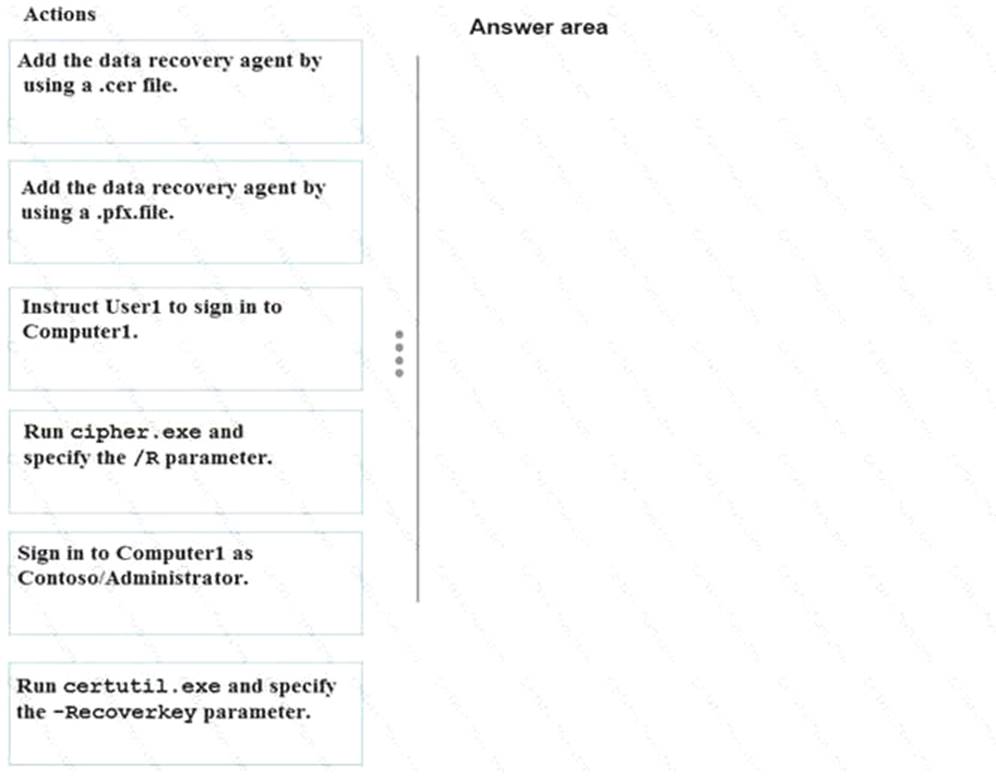
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
References:
https://msdn.microsoft.com/library/cc875821.aspx#EJAA
https://www.serverbrain.org/managing-security-2003/using-the-cipher-command-to-add-datarecovery- agent.html
NEW QUESTION 15
You have a server named Server1 that runs Windows Server 2021.
You need to identify whether IPsec tunnel authorization is configured on Server1. Which cmdlet should you use?
- A. Get-NetIPSecRule
- B. Get-NetFirewallRule
- C. Get-NetFirewallProfile
- D. Get-NetFirewallSetting
- E. Get-NetFirewallPortFilter
- F. Get-NetFirewallAddressFilter
- G. Get-NetFirewallSecurityFilter
- H. Get-NetFirewallApplicationFilter
Answer: A
Explanation:
https://technet.microsoft.com/en-us/itpro/powershell/windows/netsecurity/get-netipsecrule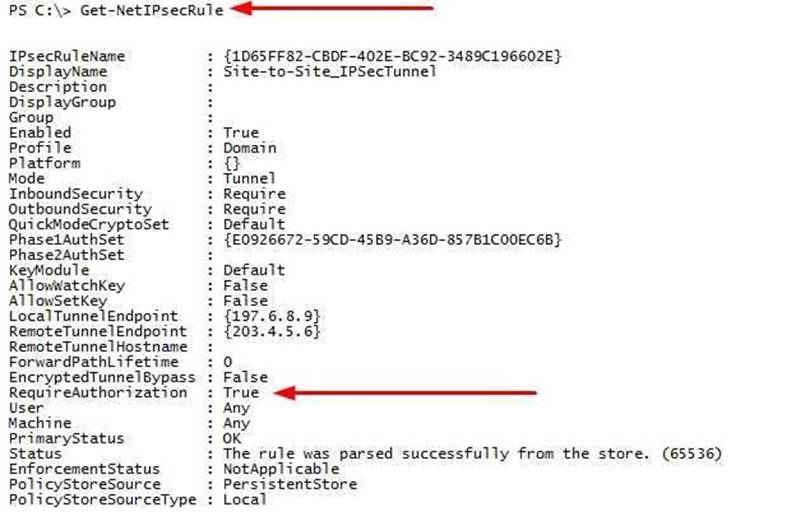
NEW QUESTION 16
You have a server named Server1 that runs Windows Server 2021.
You need to identify whether ICMP traffic is exempt from IPsec on Server1. Which cmdlet should you use?
- A. Get-NetIPSecRule
- B. Get-NetFirewallRule
- C. Get-NetFirewallProfile
- D. Get-NetFirewallSetting
- E. Get-NetFirewallPortFilter
- F. Get-NetFirewallAddressFilter
- G. Get-NetFirewallSecurityFilter
- H. Get-NetFirewallApplicationFilter
Answer: D
Explanation:
The Get-NetFirewallSetting cmdlet retrieves the global firewall settings of the target computer. The NetFirewallSetting object specifies properties that apply to the firewall and IPsec settings, no matter which
network profile is currently in use.
The global configurations include viewing the active profile, exemptions, specified certification validation levels, and user and computer authorization lists.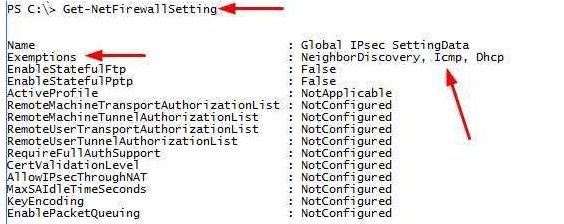
NEW QUESTION 17
Your network contains an Active Directory domain named contoso.com. The domain contains a computer named Computer1 that runs Windows 10. The network uses the 172.16.0.0/16 address space.
Computer1 has an application named App1.exe that is located in D:\Apps\. App1.exe is configured to accept connections on TCP port 8080.
You need to ensure that App1.exe can accept connections only when Computer1 is connected to the corporate network.
Solution: You configure an inbound rule that allows the TCP protocol on port 8080, uses a scope of 172.16.0.0/16 for local IP addresses, and applies to a private profile.
Does this meet the goal?
- A. Yes
- B. No
Answer: B
Explanation:
“You need to ensure that App1.exe can accept connections only when Computer1 is connected to the corporate network.”, you should create the firewall rule for “Domain” profile instead, not the “Private” profile.
https://technet.microsoft.com/en-us/library/getting-started-wfas-firewall-profilesipsec( v=ws.10).aspx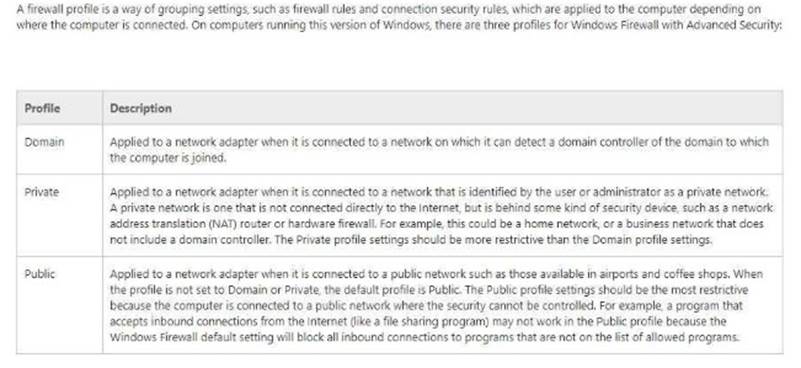
NEW QUESTION 18
Your network contains an Active Directory domain named contoso.com. The domain contains five servers. All servers run Windows Server 2021.
A new secunty policy states that you must modify the infrastructure to meet the following requirements:
*Limit the nghts of administrators.
*Minimize the attack surface of the forest
*Support Multi-Factor authentication for administrators.
You need to recommend a solution that meets the new secunty policy requirements. What should you recommend deploying?
- A. an administrative forest
- B. domain isolation
- C. an administrative domain in contoso.com
- D. the Local Administrator Password Solution (LAPS)
Answer: A
Explanation:
You have to “-Minimize the attack surface of the forest”, then you must create another forest for administrators.
https://docs.microsoft.com/en-us/windows-server/identity/securing-privileged-access/securingprivilegedaccess- reference-material#ESAE_BM
This section contains an approach for an administrative forest based on the Enhanced Security Administrative
Environment (ESAE) reference architecture deployed
by Microsoft’s cybersecurity professional services teams to protect customers against cybersecurity attacks.
Dedicated administrative forests allow organizations to host administrative accounts, workstations, and groups in an environment that has stronger security controls than the production environment.
NEW QUESTION 19
HOTSPOT
You have 100 computers that run Windows 10 and are members of a workgroup. You need to configure Windows Defender to meet the following requirements:
-Exclude a C:\Sales\Salesdb from malware scans.
-Configure a full scan to occur daily.
What should you run to meet each requirement?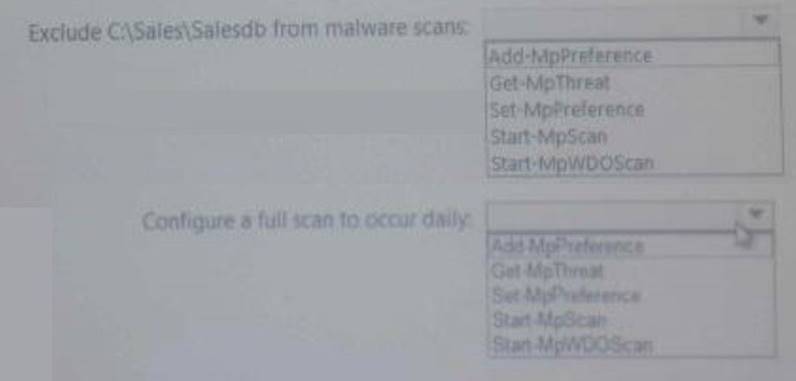
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
https://technet.microsoft.com/en-us/itpro/powershell/windows/defender/set-mppreference Set-MpPreference -ExclusionPath C:\Sales\Salesdb
Set-MpPreference -RemediationScheduleDay Everyday
NEW QUESTION 20
Your network contains an Active Directory domain named conioso.com. The domain contains 1,000 client computers that run Windows 8.1 and 1,000 client computers that run Windows 10.
You deploy a Windows Server Update Services (WSUS) server. You create a computer group tor each organizational unit (OU) that contains client computers. You configure all of the client computers to receive updates from WSUS.
You discover that all of the client computers appear m the Unassigned Computers computer group in the Update Services console.
You need to ensure that the client computers are added automatically to the computer group that corresponds to the location of the computer account in Active Directory.
Which two actions should you perform? Each correct answer presents part of the solution.
- A. From Group Policy objects (GPOs), configure the Enable client-side targeting setting.
- B. From the Update Services console, configure the Computers option.
- C. From Active Directory Users and Computers, create a domain local distribution group for each WSUS computer group.
- D. From Active Directory Users and Computers, modify the flags attnbute of each OU.
- E. From the Update Services console, run the WSUS Server Configuration Wizar
Answer: AB
NEW QUESTION 21
You implement Just Enough Administration (JEA) on several file servers that run Windows Server 2021.
The Role Capability file from a server named Server5 contains the following code.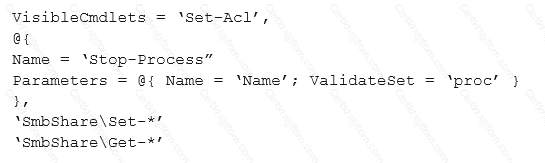
Which action can be performed by a user who connects to Server5?
- A. Create a new file share.
- B. Modify the properties of any share.
- C. Stop any process.
- D. View the NTFS permissions of any folder.
Answer: B
Explanation:
https://docs.microsoft.com/en-us/powershell/jea/role-capabilities Focus on the 3rd Visible Cmdlets in this question ‘SmbShare\Set-*’
The PowerShell “SmbShare” module has the following “Set-*” cmdlets, as reported by “Get- Command -Module
SmbShare” command:-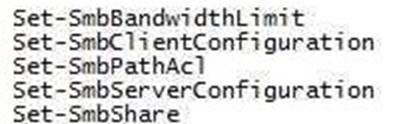
The “Set-SmbShare” cmdlet is then visible on Server5’s JEA endpoint, and allows JEA users to modify the
properties of any file share.
https://technet.microsoft.com/en-us/itpro/powershell/windows/smbshare/set-smbshare
NEW QUESTION 22
......
P.S. Certleader now are offering 100% pass ensure 70-744 dumps! All 70-744 exam questions have been updated with correct answers: https://www.certleader.com/70-744-dumps.html (221 New Questions)