Far Out FCSS FortiSASE 23 Administrator FCSS_SASE_AD-23 Braindump
Our pass rate is high to 98.9% and the similarity percentage between our FCSS_SASE_AD-23 study guide and real exam is 90% based on our seven-year educating experience. Do you want achievements in the Fortinet FCSS_SASE_AD-23 exam in just one try? I am currently studying for the Fortinet FCSS_SASE_AD-23 exam. Latest Fortinet FCSS_SASE_AD-23 Test exam practice questions and answers, Try Fortinet FCSS_SASE_AD-23 Brain Dumps First.
Also have FCSS_SASE_AD-23 free dumps questions for you:
NEW QUESTION 1
Which two deployment methods are used to connect a FortiExtender as a FortiSASE LAN extension? (Choose two.)
- A. Connect FortiExtender to FortiSASE using FortiZTP
- B. Enable Control and Provisioning Wireless Access Points (CAPWAP) access on the FortiSASE portal.
- C. Enter the FortiSASE domain name in the FortiExtender GUI as a static discovery server
- D. Configure an IPsec tunnel on FortiSASE to connect to FortiExtender.
Answer: AC
Explanation:
There are two deployment methods used to connect a FortiExtender as a FortiSASE LAN extension:
✑ Connect FortiExtender to FortiSASE using FortiZTP:
✑ Enter the FortiSASE domain name in the FortiExtender GUI as a static discovery server:
References:
✑ FortiOS 7.2 Administration Guide: Details on FortiExtender deployment methods and configurations.
✑ FortiSASE 23.2 Documentation: Explains how to connect and configure FortiExtender with FortiSASE using FortiZTP and static discovery.
NEW QUESTION 2
Which role does FortiSASE play in supporting zero trust network access (ZTNA) principles9
- A. It offers hardware-based firewalls for network segmentation.
- B. It integrateswith software-defined network (SDN) solutions.
- C. It can identify attributes on the endpoint for security posture check.
- D. It enables VPN connections for remote employees.
Answer: C
Explanation:
FortiSASE supports zero trust network access (ZTNA) principles by identifying attributes on the endpoint for security posture checks. ZTNA principles require continuous verification of user and device credentials, as well as their security posture, before granting access to network resources.
✑ Security Posture Check:
✑ Zero Trust Network Access (ZTNA):
References:
✑ FortiOS 7.2 Administration Guide: Provides information on ZTNA and endpoint security posture checks.
✑ FortiSASE 23.2 Documentation: Details on how FortiSASE implements ZTNA
principles.
NEW QUESTION 3
Refer to the exhibits.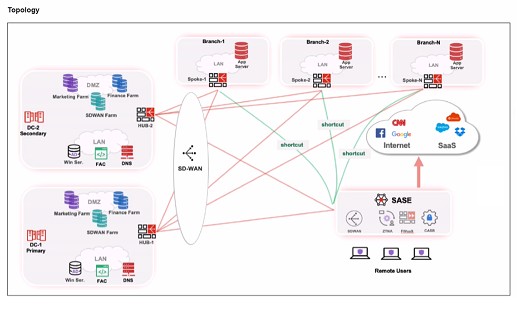

When remote users connected to FortiSASE require access to internal resources on Branch-2. how will traffic be routed?
- A. FortiSASE will use the SD-WAN capability and determine that traffic will be directed to HUB-2. which will then route traffic to Branch-2.
- B. FortiSASE will use the AD VPN protocol and determine that traffic will be directed to Branch-2 directly, using a static route
- C. FortiSASE will use the SD-WAN capability and determine that traffic will be directed to HUB-1, which will then route traffic to Branch-2.
- D. FortiSASE will use the AD VPN protocol and determine that traffic will be directed to Branch-2 directly, using a dynamic route
Answer: C
Explanation:
When remote users connected to FortiSASE require access to internal resources on Branch-2, the following process occurs:
✑ SD-WAN Capability:
✑ Traffic Routing Decision:
✑ Branch-2 Access:
References:
✑ FortiOS 7.2 Administration Guide: Details on SD-WAN configurations and priority settings.
✑ FortiSASE 23.2 Documentation: Explains how FortiSASE integrates with SD-WAN to route traffic based on defined priorities and performance metrics.
NEW QUESTION 4
When accessing the FortiSASE portal for the first time, an administrator must select data center locations for which three FortiSASE components? (Choose three.)
- A. Endpoint management
- B. Points of presence
- C. SD-WAN hub
- D. Logging
- E. Authentication
Answer: ABD
Explanation:
When accessing the FortiSASE portal for the first time, an administrator must select data center locations for the following FortiSASE components:
✑ Endpoint Management:
✑ Points of Presence (PoPs):
✑ Logging:
References:
✑ FortiOS 7.2 Administration Guide: Details on initial setup and configuration steps for FortiSASE.
✑ FortiSASE 23.2 Documentation: Explains the importance of selecting data center locations for various FortiSASE components.
NEW QUESTION 5
When you configure FortiSASE Secure Private Access (SPA) with SD-WAN integration, you must establish a routing adjacency between FortiSASE and the FortiGate SD-WAN hub. Which routing protocol must you use?
- A. BGP
- B. IS-IS
- C. OSPF
- D. EIGRP
Answer: A
Explanation:
When configuring FortiSASE Secure Private Access (SPA) with SD-WAN integration, establishing a routing adjacency between FortiSASE and the FortiGate SD- WAN hub requires the use of the Border Gateway Protocol (BGP).
✑ BGP (Border Gateway Protocol):
✑ Routing Adjacency:
References:
✑ FortiOS 7.2 Administration Guide: Provides information on configuring BGP for SD-WAN integration.
✑ FortiSASE 23.2 Documentation: Details on setting up routing adjacencies using BGP for Secure Private Access with SD-WAN.
NEW QUESTION 6
Refer to the exhibits.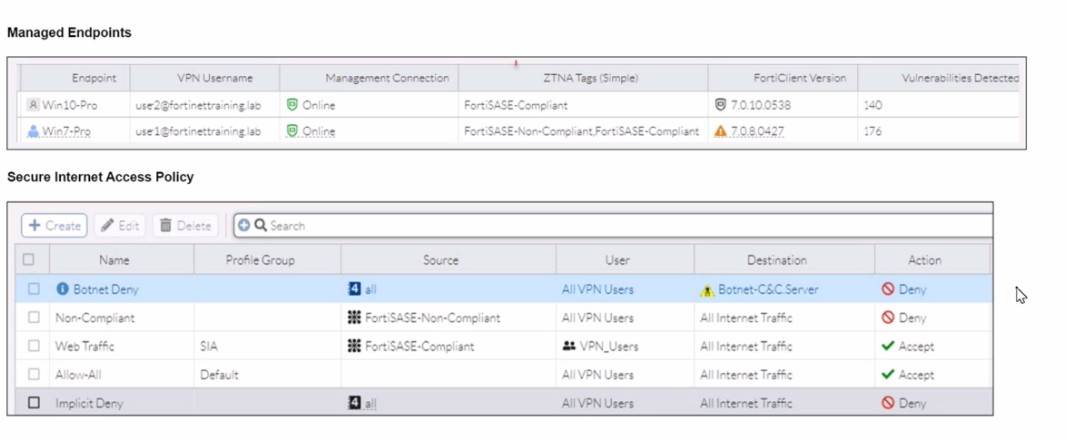
WiMO-Pro and Win7-Pro are endpoints from the same remote location. WiMO-Pro can
access the internet though FortiSASE, while Wm7-Pro can no longer access the internet Given the exhibits, which reason explains the outage on Wm7-Pro?
- A. The Win7-Pro device posture has changed.
- B. Win7-Pro cannot reach the FortiSASE SSL VPN gateway
- C. The Win7-Pro FortiClient version does not match the FortiSASE endpoint requirement.
- D. Win-7 Pro has exceeded the total vulnerability detected threshold.
Answer: D
Explanation:
Based on the provided exhibits, the reason why the Win7-Pro endpoint can no longer access the internet through FortiSASE is due to exceeding the total vulnerability detected threshold. This threshold is used to determine if a device is compliant with the security requirements to access the network.
✑ Endpoint Compliance:
✑ Vulnerability Threshold:
✑ Impact on Network Access:
References:
✑ FortiOS 7.2 Administration Guide: Provides information on endpoint compliance and vulnerability management.
✑ FortiSASE 23.2 Documentation: Explains how vulnerability thresholds are used to determine endpoint compliance and access control.
NEW QUESTION 7
Which FortiSASE feature ensures least-privileged user access to all applications?
- A. secure web gateway (SWG)
- B. SD-WAN
- C. zero trust network access (ZTNA)
- D. thin branch SASE extension
Answer: C
Explanation:
Zero Trust Network Access (ZTNA) is the FortiSASE feature that ensures least-privileged user access to all applications. ZTNA operates on the principle of "never trust, always verify," providing secure access based on the identity of users and devices, regardless of their location.
✑ Zero Trust Network Access (ZTNA):
✑ Implementation:
References:
✑ FortiOS 7.2 Administration Guide: Provides detailed information on ZTNA and its role in ensuring least-privileged access.
✑ FortiSASE 23.2 Documentation: Explains the implementation and benefits of ZTNA within the FortiSASE environment.
NEW QUESTION 8
Which two additional components does FortiSASE use for application control to act as an inline-CASB? (Choose two.)
- A. intrusion prevention system (IPS)
- B. SSL deep inspection
- C. DNS filter
- D. Web filter with inline-CASB
Answer: BD
Explanation:
FortiSASE uses the following components for application control to act as an inline-CASB (Cloud Access Security Broker):
✑ SSL Deep Inspection:
✑ Web Filter with Inline-CASB:
References:
✑ FortiOS 7.2 Administration Guide: Details on SSL deep inspection and web filtering configurations.
✑ FortiSASE 23.2 Documentation: Explains how FortiSASE acts as an inline-CASB using SSL deep inspection and web filtering.
NEW QUESTION 9
Refer to the exhibit.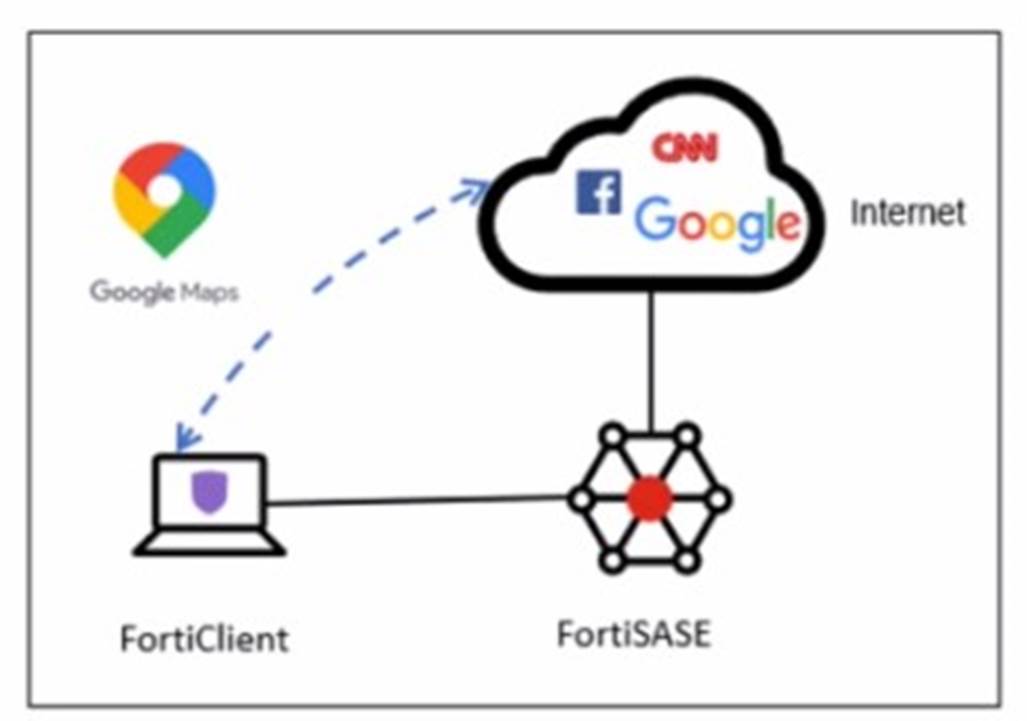
A company has a requirement to inspect all the endpoint internet traffic on FortiSASE, and exclude Google Maps traffic from the FortiSASE VPN tunnel and redirect it to the endpoint physical Interface.
Which configuration must you apply to achieve this requirement?
- A. Exempt the Google Maps FQDN from the endpoint system proxy settings.
- B. Configure a static route with the Google Maps FQDN on the endpoint to redirect traffic
- C. Configure the Google Maps FQDN as a split tunneling destination on the FortiSASE endpoint profile.
- D. Change the default DNS server configuration on FortiSASE to use the endpoint system DNS.
Answer: C
Explanation:
To meet the requirement of inspecting all endpoint internet traffic on FortiSASE while excluding Google Maps traffic from the FortiSASE VPN tunnel and redirecting it to the endpoint's physical interface, you should configure split tunneling. Split tunneling allows specific traffic to bypass the VPN tunnel and be routed directly through the endpoint's local interface.
✑ Split Tunneling Configuration:
✑ Implementation Steps:
References:
✑ FortiOS 7.2 Administration Guide: Provides details on split tunneling configuration.
✑ FortiSASE 23.2 Documentation: Explains how to set up and manage split tunneling for specific destinations.
NEW QUESTION 10
......
Recommend!! Get the Full FCSS_SASE_AD-23 dumps in VCE and PDF From Thedumpscentre.com, Welcome to Download: https://www.thedumpscentre.com/FCSS_SASE_AD-23-dumps/ (New 30 Q&As Version)