IBM P2150-870 Braindumps 2021
Actualtests P2150-870 Questions are updated and all P2150-870 answers are verified by experts. Once you have completely prepared with our P2150-870 exam prep kits you will be ready for the real P2150-870 exam without a problem. We have Renovate IBM P2150-870 dumps study guide. PASSED P2150-870 First attempt! Here What I Did.
Check P2150-870 free dumps before getting the full version:
NEW QUESTION 1
Besides a QRadar Console, which additional types of appliance does a typical QRadar Incident Forensics deployment contain?
One or more QRadar Incident Forensics appliances, and:
- A. one or more QRadar Event Collector appliances.
- B. one or more QRadar QFlow Collector appliances.
- C. one or more QRadar Vulnerability Scanner appliances
- D. one or more QRadar Network Packet Capture appliances
Answer: A
NEW QUESTION 2
Which TCP/IP protocols are at layer 4 of the OSI model (Select 2)
- A. TCP
- B. UDP
- C. ARP
- D. ICMP
- E. IGMP
Answer: AB
NEW QUESTION 3
What is a benefit of having QRadar on Cloud? IBM is responsible for:
- A. generating new use cases.
- B. alerting the user regarding offenses.
- C. providing 24 hour
- D. 7 days a week health monitoring and system management of the QRadar Deployment.
- E. providing health monitoring and system management of the QRadar Deployment during normal business hours only.
Answer: D
NEW QUESTION 4
What is a difference between rules and building blocks?
- A. Rules have responses and Building Blocks do not.
- B. Rules can be used for reporting and Building Blocks cannot.
- C. Building Blocks have responses and Rules do not.
- D. Building Blocks only use flows and Rules only use events.
Answer: A
NEW QUESTION 5
What is the least secure of the five transmission types?
- A. Wireless
- B. Fiber Optic
- C. Coaxial Cable
- D. Shielded Twisted Pair
- E. Unshielded Twisted Pair
Answer: C
NEW QUESTION 6
Which categorizes a threat to a type of attack?
- A. Sniffin
- B. Interruption
- C. SQL injection, Interception
- D. Man in the middle, Fabrication
- E. Denial of Service, Modification
Answer: B
NEW QUESTION 7
Which IBM artificial intelligence service can be used to speed up analysis of external threats?
- A. QRadar Incident Overview
- B. QRadar Advisor with Watson
- C. QRadar Machine Learning Analytics
- D. QRadar Artificial Intelligence toolbox
Answer: D
NEW QUESTION 8
In this diagram, showing the Ariel Search Flow, what is the name of the components as ‘X’, running on the Console?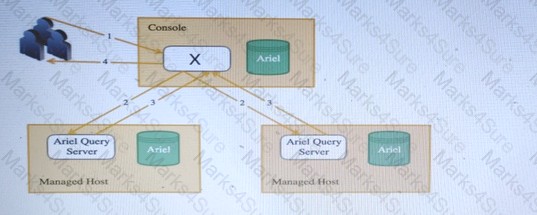
- A. AQL Processor
- B. Ariel Proxy Server
- C. Ariel Query Server
- D. REST -API endpoint
Answer: A
NEW QUESTION 9
What does QRadar Network Insight (QNI) create?
- A. An Offense from Events.
- B. A demilitarized zone from Apple Airport data.
- C. OSI Layer 7 packet from OSI Layer 3 flow information.
- D. IPFIX records with deep security content from SPAN or TAN port data.
Answer: C
NEW QUESTION 10
How can QRadar Network Security improve security posture for companies? By using QRadar Network Security, companies can:
- A. implement an application firewall.
- B. perform event monitoring.
- C. perform vulnerability scanning to detect vulnerabilities.
- D. perform application contro
- E. SSL inspection, and disrupt advanced malware
Answer: A
NEW QUESTION 11
Which is a valid use case for implementing QRadar reference data collections?
- A. Change all incoming events to add an additional field value.
- B. Provide an index for all data (events and flow data) in real time.
- C. Store hash values and test each incoming hash against this set
- D. Speed up dashboard functions due to caching common widget data sets
Answer: C
NEW QUESTION 12
How can assets be used to help in investigations?
- A. As valuable data sources.
- B. Make searching for offenses easier.
- C. Help connect an offense to a device.
- D. Provide external threat intelligence.
Answer: D
NEW QUESTION 13
To view flow data in QRadar, which tab should a user navigate to?
- A. Assets
- B. Log Activity
- C. User Analytics
- D. Network Activity
Answer: A
NEW QUESTION 14
Which case shows how approximately 1000 Events per second, using an encrypted channel, can be sent from a private cloud to a QRader processor?
- A. Place an event processor in the private cloud, and forward the events to another event collector.
- B. Place a risk manager appliance in the private cloud, and forward the events to another event collector.
- C. Place a packet capture appliance in the private cloud, and forward the events to a cloud events processor.
- D. Place an event collector in the private cloud, and forward the event to the customers event processor.
Answer: A
NEW QUESTION 15
Which metrics are defined for the three virtual appliance system specification (Minimum/Medium/High). (select 4)
- A. NICs
- B. IOPS
- C. Memory
- D. Storage
- E. CPU cores/speed
- F. Maximum Latency
- G. Virtual Networks
Answer: ACEG
NEW QUESTION 16
Which QRadar Apps integrate with the User Behaviour Analytics App to enhance its detection capabilities?
- A. QRadar Risk Manager and QRadar Network Security
- B. QRadar Machine Learning App and Reference Data Import - LDAP
- C. QRadar Asset Profiler App and Palo Alto Networks App for QRadar
- D. QRadar Incident Remediation App and QRadar Artificial Analysis App
Answer: C
NEW QUESTION 17
......
P.S. Certstest now are offering 100% pass ensure P2150-870 dumps! All P2150-870 exam questions have been updated with correct answers: https://www.certstest.com/dumps/P2150-870/ (40 New Questions)