What Download PCNSA Exam Dumps Is
Actualtests PCNSA Questions are updated and all PCNSA answers are verified by experts. Once you have completely prepared with our PCNSA exam prep kits you will be ready for the real PCNSA exam without a problem. We have Up to date Paloalto-Networks PCNSA dumps study guide. PASSED PCNSA First attempt! Here What I Did.
Free PCNSA Demo Online For Paloalto-Networks Certifitcation:
NEW QUESTION 1
A security administrator has configured App-ID updates to be automatically downloaded and installed. The company is currently using an application identified by App-ID as SuperApp_base. On a content update notice, Palo Alto Networks is adding new app signatures labeled SuperApp_chat and SuperApp_download, which will be deployed in 30 days. Based on the information, how is the SuperApp traffic affected after the 30 days have passed?
- A. All traffic matching the SuperApp_chat, and SuperApp_download is denied because it no longer matches the SuperApp-base application
- B. No impact because the apps were automatically downloaded and installed
- C. No impact because the firewall automatically adds the rules to the App-ID interface
- D. All traffic matching the SuperApp_base, SuperApp_chat, and SuperApp_download is denied until the security administrator approves the applications
Answer: C
NEW QUESTION 2
An administrator receives a global notification for a new malware that infects hosts. The infection will result in the infected host attempting to contact a command-and-control (C2) server. Which two security profile components will detect and prevent this threat after the firewall’s signature database has been updated? (Choose two.)
- A. vulnerability protection profile applied to outbound security policies
- B. anti-spyware profile applied to outbound security policies
- C. antivirus profile applied to outbound security policies
- D. URL filtering profile applied to outbound security policies
Answer: BD
NEW QUESTION 3
In the example security policy shown, which two websites would be blocked? (Choose two.)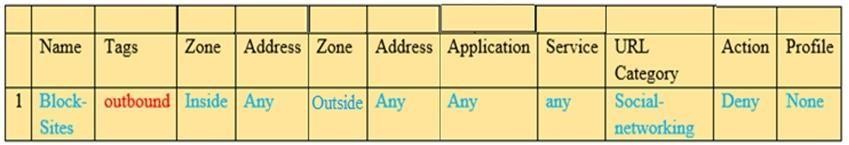
- A. LinkedIn
- B. Facebook
- C. YouTube
- D. Amazon
Answer: AB
NEW QUESTION 4
What are two differences between an implicit dependency and an explicit dependency in App- ID? (Choose two.)
- A. An implicit dependency does not require the dependent application to be added in the security policy
- B. An implicit dependency requires the dependent application to be added in the security policy
- C. An explicit dependency does not require the dependent application to be added in the security policy
- D. An explicit dependency requires the dependent application to be added in the security policy
Answer: AD
NEW QUESTION 5
Which administrator type provides more granular options to determine what the administrator can view and modify when creating an administrator account?
- A. Root
- B. Dynamic
- C. Role-based
- D. Superuser
Answer: C
NEW QUESTION 6
Which statement is true regarding a Best Practice Assessment?
- A. The BPA tool can be run only on firewalls
- B. It provides a percentage of adoption for each assessment data
- C. The assessment, guided by an experienced sales engineer, helps determine the areas of greatest risk where you should focus prevention activities
- D. It provides a set of questionnaires that help uncover security risk prevention gaps across all areas of network and security architecture
Answer: B
NEW QUESTION 7
Identify the correct order to configure the PAN-OS integrated USER-ID agent.
3. add the service account to monitor the server(s)
2. define the address of the servers to be monitored on the firewall
4. commit the configuration, and verify agent connection status
1. create a service account on the Domain Controller with sufficient permissions to execute the User- ID agent
- A. 2-3-4-1
- B. 1-4-3-2
- C. 3-1-2-4
- D. 1-3-2-4
Answer: D
NEW QUESTION 8
Which five Zero Trust concepts does a Palo Alto Networks firewall apply to achieve an integrated approach to prevent threats? (Choose five.)
- A. User identification
- B. Filtration protection
- C. Vulnerability protection
- D. Antivirus
- E. Application identification
- F. Anti-spyware
Answer: ACDEF
NEW QUESTION 9
Which Palo Alto Networks firewall security platform provides network security for mobile endpoints by inspecting traffic deployed as internet gateways?
- A. GlobalProtect
- B. AutoFocus
- C. Aperture
- D. Panorama
Answer: CD
Explanation:
 44. Given the scenario, which two statements are correct regarding multiple static default routes? (Choose two.)
44. Given the scenario, which two statements are correct regarding multiple static default routes? (Choose two.)
A. Path monitoring does not determine if route is useable
B. Route with highest metric is actively used
C. Path monitoring determines if route is useable
D. Route with lowest metric is actively used
NEW QUESTION 10
Which data-plane processor layer of the graphic shown provides uniform matching for spyware and vulnerability exploits on a Palo Alto Networks Firewall?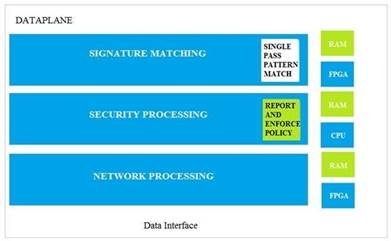
- A. Signature Matching
- B. Network Processing
- C. Security Processing
- D. Security Matching
Answer: A
NEW QUESTION 11
Which file is used to save the running configuration with a Palo Alto Networks firewall?
- A. running-config.xml
- B. run-config.xml
- C. running-configuration.xml
- D. run-configuratin.xml
Answer: A
NEW QUESTION 12
DRAG DROP
Match the Palo Alto Networks Security Operating Platform architecture to its description.
Select and Place: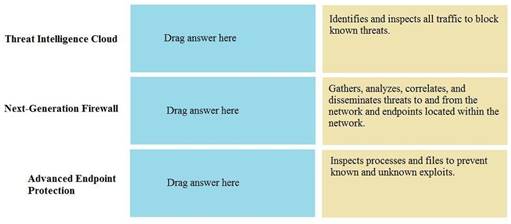
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 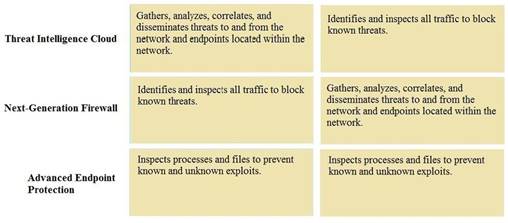
NEW QUESTION 13
Which firewall plane provides configuration, logging, and reporting functions on a separate processor?
- A. control
- B. network processing
- C. data
- D. security processing
Answer: A
NEW QUESTION 14
Which two security profile types can be attached to a security policy? (Choose two.)
- A. antivirus
- B. DDoS protection
- C. threat
- D. vulnerability
Answer: AD
NEW QUESTION 15
Which option shows the attributes that are selectable when setting up application filters?
- A. Category, Subcategory, Technology, and Characteristic
- B. Category, Subcategory, Technology, Risk, and Characteristic
- C. Name, Category, Technology, Risk, and Characteristic
- D. Category, Subcategory, Risk, Standard Ports, and Technology
Answer: B
NEW QUESTION 16
Your company requires positive username attribution of every IP address used by wireless devices to support a new compliance requirement. You must collect IP –to-user mappings as soon as possible with minimal downtime and minimal configuration changes to the wireless devices themselves. The wireless devices are from various manufactures.
Given the scenario, choose the option for sending IP-to-user mappings to the NGFW.
- A. syslog
- B. RADIUS
- C. UID redistribution
- D. XFF headers
Answer: A
NEW QUESTION 17
How many zones can an interface be assigned with a Palo Alto Networks firewall?
- A. two
- B. three
- C. four
- D. one
Answer: BC
Explanation:
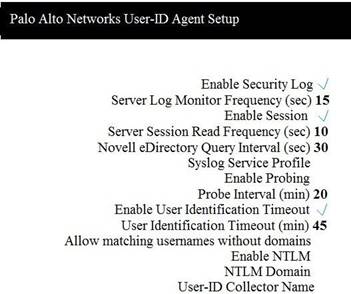 5. Which two configuration settings shown are not the default? (Choose two.)
5. Which two configuration settings shown are not the default? (Choose two.)
A. Enable Security Log
B. Server Log Monitor Frequency (sec)
C. Enable Session
D. Enable Probing
NEW QUESTION 18
Which interface does not require a MAC or IP address?
- A. Virtual Wire
- B. Layer3
- C. Layer2
- D. Loopback
Answer: A
NEW QUESTION 19
DRAG DROP
Match the Cyber-Attack Lifecycle stage to its correct description.
Select and Place: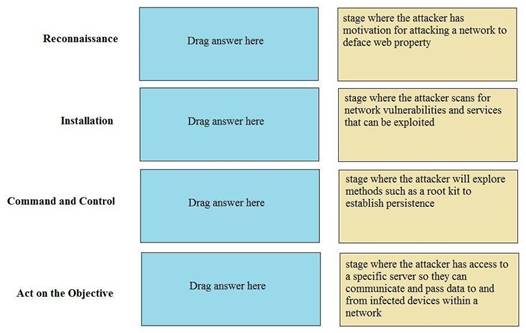
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 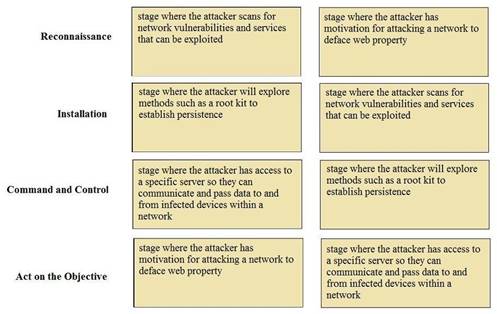
NEW QUESTION 20
......
Recommend!! Get the Full PCNSA dumps in VCE and PDF From Surepassexam, Welcome to Download: https://www.surepassexam.com/PCNSA-exam-dumps.html (New 115 Q&As Version)