The Secret Of Paloalto-Networks PSE-Cortex Free Demo
It is impossible to pass Paloalto-Networks PSE-Cortex exam without any help in the short term. Come to Passleader soon and find the most advanced, correct and guaranteed Paloalto-Networks PSE-Cortex practice questions. You will get a surprising result by our Latest Palo Alto Networks System Engineer - Cortex Professional practice guides.
Paloalto-Networks PSE-Cortex Free Dumps Questions Online, Read and Test Now.
NEW QUESTION 1
Which process in the causality chain does the Cortex XDR agent identify as triggering an event sequence?
- A. the relevant shell
- B. The causality group owner
- C. the adversary's remote process
- D. the chain's alert initiator
Answer: B
NEW QUESTION 2
How do sub-playbooks affect the Incident Context Data?
- A. When set to private, task outputs do not automatically get written to the root context
- B. When set to private, task outputs automatically get written to the root context
- C. When set to global, allows parallel task execution.
- D. When set to global, sub-playbook tasks do not have access to the root context
Answer: A
NEW QUESTION 3
Which two log types should be configured for firewall forwarding to the Cortex Data Lake for use by Cortex XDR? (Choose two)
- A. Security Event
- B. HIP
- C. Correlation
- D. Analytics
Answer: AB
NEW QUESTION 4
An EDR project was initiated by a CISO. Which resource will likely have the most heavy influence on the project?
- A. desktop engineer
- B. SOC manager
- C. SOC analyst IT
- D. operations manager
Answer: B
NEW QUESTION 5
An Administrator is alerted to a Suspicious Process Creation security event from multiple users.
The users believe that these events are false positives Which two steps should the administrator take to confirm the false positives and create an exception? (Choose two )
- A. With the Malware Security profile, disable the "Prevent Malicious Child Process Execution" module
- B. Within the Malware Security profile add the specific parent process, child process, and command line argument to the child process whitelist
- C. In the Cortex XDR security event, review the specific parent process, child process, and command line arguments
- D. Contact support and ask for a security exception.
Answer: BC
NEW QUESTION 6
The images show two versions of the same automation script and the results they produce when executed in Demisto. What are two possible causes of the exception thrown in the second Image? (Choose two.)
SUCCESS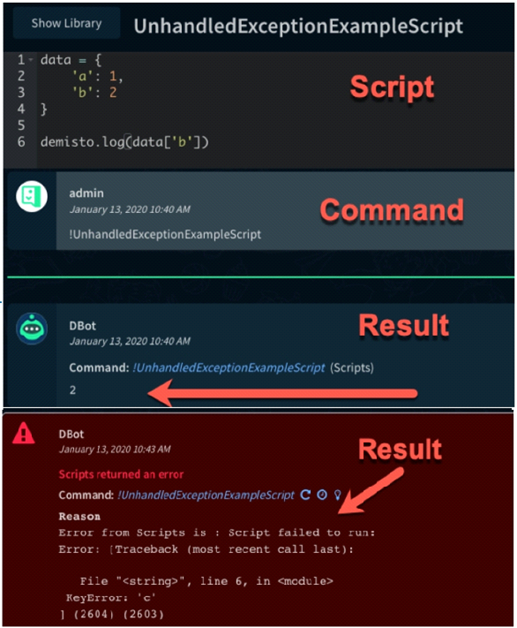
- A. The modified scnpt was run in the wrong Docker image
- B. The modified script required a different parameter to run successfully.
- C. The dictionary was defined incorrectly in the second script.
- D. The modified script attempted to access a dictionary key that did not exist in the dictionary named "data”
Answer: A
NEW QUESTION 7
How can you view all the relevant incidents for an indicator?
- A. Linked Incidents column in Indicator Screen
- B. Linked Indicators column in Incident Screen
- C. Related Indicators column in Incident Screen
- D. Related Incidents column in Indicator Screen
Answer: D
NEW QUESTION 8
Which four types of Traps logs are stored within Cortex Data Lake?
- A. Threat, Config, System, Data
- B. Threat, Config, System, Analytic
- C. Threat, Monito
- D. System, Analytic
- E. Threat, Config, Authentication, Analytic
Answer: B
NEW QUESTION 9
An administrator of a Cortex XDR protected production environment would like to test its ability to protect users from a known flash player exploit.
What is the safest way to do it?
- A. The administrator should attach a copy of the weapomzed flash file to an email, send the email to a selected group of employees, and monitor the Events tab on the Cortex XDR console
- B. The administrator should use the Cortex XDR tray icon to confirm his corporate laptop is fully protected then open the weaponized flash file on his machine, and monitor the Events tab on the Cortex XDR console.
- C. The administrator should create a non-production Cortex XDR test environment that accurately represents the production environment, introduce the weaponized flash file, and monitor the Events tab on the Cortex XDR console.
- D. The administrator should place a copy of the weaponized flash file on several USB drives, scatter them around the office and monitor the Events tab on the Cortex XDR console
Answer: C
NEW QUESTION 10
If a customer activates a TMS tenant and has not purchased a Cortex Data Lake instance. Palo Alto Networks will provide the customer with a free instance
What size is this free Cortex Data Lake instance?
- A. 1 TB
- B. 10 GB
- C. 100 GB
- D. 10 TB
Answer: C
NEW QUESTION 11
Which two entities can be created as a BIOC? (Choose two.)
- A. file
- B. registry
- C. event log
- D. alert log
Answer: AB
Explanation:
https://docs.paloaltonetworks.com/cortex/cortex-xdr/cortex-xdr-pro-admin/investigation-and-response/cortex-xd
NEW QUESTION 12
What method does the Traps agent use to identify malware during a scheduled scan?
- A. Heuristic analysis
- B. Local analysis
- C. Signature comparison
- D. WildFire hash comparison and dynamic analysis
Answer: D
NEW QUESTION 13
When a Demisto Engine is part of a Load-Balancing group it?
- A. Must be in a Load-Balancing group with at least another 3 members
- B. It must have port 443 open to allow the Demisto Server to establish a connection
- C. Can be used separately as an engine, only if connected to the Demisto Server directly
- D. Cannot be used separately and does not appear in the in the engines drop-down menu when configuring an integration instance
Answer: D
NEW QUESTION 14
Which option is required to prepare the VDI Golden Image?
- A. Configure the Golden Image as a persistent VDI
- B. Use the Cortex XDR VDI tool to obtain verdicts for all PE files
- C. Install the Cortex XOR Agent on the local machine
- D. Run the Cortex VDI conversion tool
Answer: B
NEW QUESTION 15
Which CLI query would bring back Notable Events from Splunk?
A)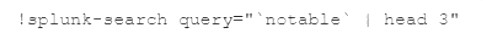
B)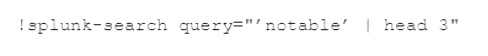
C)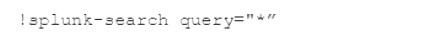
D)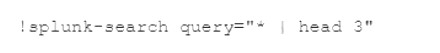
- A. Option A
- B. Option B
- C. Option C
- D. Option D
Answer: D
NEW QUESTION 16
Cortex XDR can schedule recurring scans of endpoints for malware. Identify two methods for initiating an on-demand malware scan (Choose two )
- A. Response > Action Center
- B. the local console
- C. Telnet
- D. Endpoint > Endpoint Management
Answer: AD
NEW QUESTION 17
Which Cortex XDR capability extends investigations to an endpoint?
- A. Log Stitching
- B. Causality Chain
- C. Sensors
- D. Live Terminal
Answer: A
Explanation:
https://docs.paloaltonetworks.com/cortex/cortex-xdr/cortex-xdr-pro-admin/cortex-xdr-overview/cortex-xdr-conc
NEW QUESTION 18
What is the result of creating an exception from an exploit security event?
- A. White lists the process from Wild Fire analysis
- B. exempts the user from generating events for 24 hours
- C. exempts administrators from generating alerts for 24 hours
- D. disables the triggered EPM for the host and process involve
Answer: D
NEW QUESTION 19
......
Thanks for reading the newest PSE-Cortex exam dumps! We recommend you to try the PREMIUM Certshared PSE-Cortex dumps in VCE and PDF here: https://www.certshared.com/exam/PSE-Cortex/ (60 Q&As Dumps)