A Review Of Tested SC-100 Practice Test
Certleader SC-100 Questions are updated and all SC-100 answers are verified by experts. Once you have completely prepared with our SC-100 exam prep kits you will be ready for the real SC-100 exam without a problem. We have Abreast of the times Microsoft SC-100 dumps study guide. PASSED SC-100 First attempt! Here What I Did.
Microsoft SC-100 Free Dumps Questions Online, Read and Test Now.
NEW QUESTION 1
Your company has an office in Seattle.
The company has two Azure virtual machine scale sets hosted on different virtual networks. The company plans to contract developers in India.
You need to recommend a solution provide the developers with the ability to connect to the virtual machines over SSL from the Azure portal. The solution must meet the following requirements:
• Prevent exposing the public IP addresses of the virtual machines.
• Provide the ability to connect without using a VPN.
• Minimize costs.
Which two actions should you perform? Each correct answer presents part of the solution. NOTE: Each correct selection is worth one point.
- A. Deploy Azure Bastion to one virtual network.
- B. Deploy Azure Bastion to each virtual network.
- C. Enable just-in-time VM access on the virtual machines.
- D. Create a hub and spoke network by using virtual network peering.
- E. Create NAT rules and network rules in Azure Firewall.
Answer: DE
NEW QUESTION 2
You have an Azure subscription that contains several storage accounts. The storage accounts are accessed by legacy applications that are authenticated by using access keys.
You need to recommend a solution to prevent new applications from obtaining the access keys of the storage accounts. The solution must minimize the impact on the legacy applications.
What should you include in the recommendation?
- A. Apply read-only locks on the storage accounts.
- B. Set the AllowSharcdKeyAccess property to false.
- C. Set the AllowBlobPublicAcccss property to false.
- D. Configure automated key rotation.
Answer: A
NEW QUESTION 3
You receive a security alert in Microsoft Defender for Cloud as shown in the exhibit. (Click the Exhibit tab.)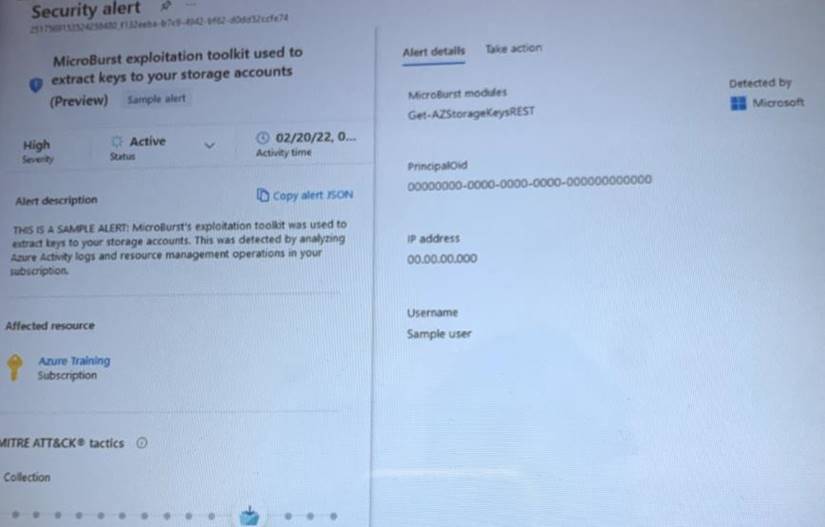
After remediating the threat which policy definition should you assign to prevent the threat from reoccurring?
- A. Storage account public access should be disallowed
- B. Azure Key Vault Managed HSM should have purge protection enabled
- C. Storage accounts should prevent shared key access
- D. Storage account keys should not be expired
Answer: A
NEW QUESTION 4
Your company is developing a modern application that will run as an Azure App Service web app. You plan to perform threat modeling to identify potential security issues by using the Microsoft Threat Modeling Tool.
Which type of diagram should you create?
- A. dataflow
- B. system flow
- C. process flow
- D. network flow
Answer: C
NEW QUESTION 5
You have an Azure subscription that has Microsoft Defender for Cloud enabled. You have an Amazon Web Services (AWS) implementation.
You plan to extend the Azure security strategy to the AWS implementation. The solution will NOT use Azure Arc. Which three services can you use to provide security for the AWS resources? Each correct answer presents a complete solution. NOTE: Each correct selection is worth one point.
- A. Azure Active Directory (Azure AD) Privileged Identity Management (PIM)
- B. Azure Active Directory (Azure AD) Conditional Access
- C. Microsoft Defender for servers
- D. Azure Policy
- E. Microsoft Defender for Containers
Answer: BE
NEW QUESTION 6
A customer is deploying Docker images to 10 Azure Kubernetes Service (AKS) resources across four Azure subscriptions. You are evaluating the security posture of the customer.
You discover that the AKS resources are excluded from the secure score recommendations. You need to produce accurate recommendations and update the secure score.
Which two actions should you recommend in Microsoft Defender for Cloud? Each correct answer presents part of the solution. NOTE: Each correct selection is worth one point.
- A. Configure auto provisioning.
- B. Assign regulatory compliance policies.
- C. Review the inventory.
- D. Add a workflow automation.
- E. Enable Defender plans.
Answer: BD
NEW QUESTION 7
Your company has a Microsoft 365 E5 subscription. The company wants to identify and classify data in Microsoft Teams, SharePoint Online, and Exchange Online. You need to recommend a solution to identify documents that contain sensitive information. What should you include in the recommendation?
- A. data classification content explorer
- B. data loss prevention (DLP)
- C. eDiscovery
- D. Information Governance
Answer: A
NEW QUESTION 8
You need to recommend a strategy for routing internet-bound traffic from the landing zones. The solution must meet the landing zone requirements.
What should you recommend as part of the landing zone deployment?
- A. service chaining
- B. local network gateways
- C. forced tunneling
- D. a VNet-to-VNet connection
Answer: A
NEW QUESTION 9
You are evaluating an Azure environment for compliance.
You need to design an Azure Policy implementation that can be used to evaluate compliance without changing any resources.
Which effect should you use in Azure Policy?
- A. Deny
- B. Disabled
- C. Modify
- D. Append
Answer: A
NEW QUESTION 10
Your company has on-premises Microsoft SQL Server databases. The company plans to move the databases to Azure.
You need to recommend a secure architecture for the databases that will minimize operational requirements for patching and protect sensitive data by using dynamic data masking. The solution must minimize costs.
What should you include in the recommendation?
- A. Azure SQL Managed Instance
- B. Azure Synapse Analytics dedicated SQL pools
- C. Azure SQL Database
- D. SQL Server on Azure Virtual Machines
Answer: D
NEW QUESTION 11
Your company is developing a serverless application in Azure that will have the architecture shown in the following exhibit.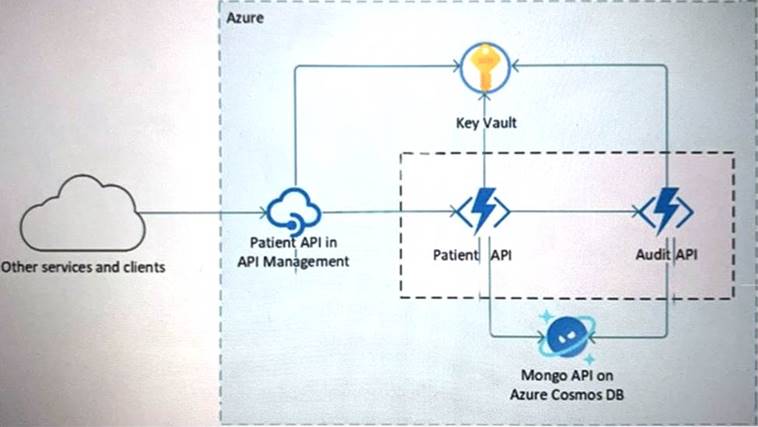
You need to recommend a solution to isolate the compute components on an Azure virtual network. What should you include in the recommendation?
- A. Azure Active Directory (Azure AD) enterprise applications
- B. an Azure App Service Environment (ASE)
- C. Azure service endpoints
- D. an Azure Active Directory (Azure AD) application proxy
Answer: B
NEW QUESTION 12
You need to recommend a solution to meet the security requirements for the InfraSec group. What should you use to delegate the access?
- A. a subscription
- B. a custom role-based access control (RBAC) role
- C. a resource group
- D. a management group
Answer: D
NEW QUESTION 13
You need to recommend a solution for securing the landing zones. The solution must meet the landing zone requirements and the business requirements.
What should you configure for each landing zone?
- A. Azure DDoS Protection Standard
- B. an Azure Private DNS zone
- C. Microsoft Defender for Cloud
- D. an ExpressRoute gateway
Answer: D
NEW QUESTION 14
Your company has a Microsoft 365 E5 subscription.
Users use Microsoft Teams, Exchange Online, SharePoint Online, and OneDrive for sharing and collaborating. The company identifies protected health information (PHI) within stored documents and communications. What should you recommend using to prevent the PHI from being shared outside the company?
- A. insider risk management policies
- B. data loss prevention (DLP) policies
- C. sensitivity label policies
- D. retention policies
Answer: A
NEW QUESTION 15
You have a Microsoft 365 subscription and an Azure subscription. Microsoft 365 Defender and Microsoft Defender for Cloud are enabled.
The Azure subscription contains 50 virtual machines. Each virtual machine runs different applications on Windows Server 2019.
You need to recommend a solution to ensure that only authorized applications can run on the virtual machines. If an unauthorized application attempts to run or be installed, the application must be blocked automatically until an administrator authorizes the application.
Which security control should you recommend?
- A. Azure Active Directory (Azure AD) Conditional Access App Control policies
- B. OAuth app policies in Microsoft Defender for Cloud Apps
- C. app protection policies in Microsoft Endpoint Manager
- D. application control policies in Microsoft Defender for Endpoint
Answer: A
NEW QUESTION 16
You need to recommend a solution to meet the compliance requirements.
What should you recommend? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.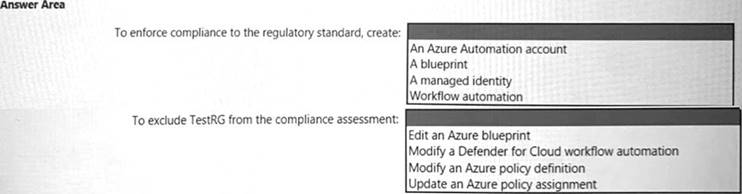
Solution:
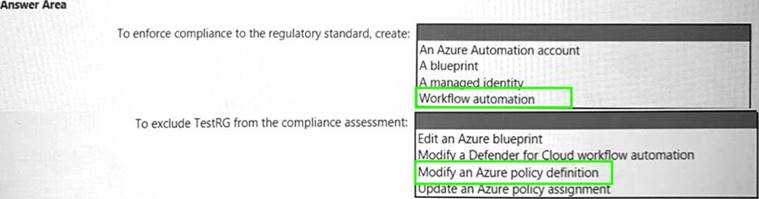
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 17
Your company has a Microsoft 365 subscription and uses Microsoft Defender for Identity. You are informed about incidents that relate to compromised identities.
You need to recommend a solution to expose several accounts for attackers to exploit. When the attackers attempt to exploit the accounts, an alert must be triggered. Which Defender for Identity feature should you include in the recommendation?
- A. standalone sensors
- B. honeytoken entity tags
- C. sensitivity labels
- D. custom user tags
Answer: D
NEW QUESTION 18
Your company has an on-premise network in Seattle and an Azure subscription. The on-premises network contains a Remote Desktop server.
The company contracts a third-party development firm from France to develop and deploy resources to the virtual machines hosted in the Azure subscription.
Currently, the firm establishes an RDP connection to the Remote Desktop server. From the Remote Desktop connection, the firm can access the virtual machines hosted in Azure by using custom administrative tools installed on the Remote Desktop server. All the traffic to the Remote Desktop server is captured by a firewall, and the firewall only allows specific connections from France to the server.
You need to recommend a modern security solution based on the Zero Trust model. The solution must minimize latency tor developers.
Which three actions should you recommend? Each correct answer presents part of the solution. NOTE: Each correct selection is worth one point.
- A. Configure network security groups (NSGs) to allow access from only specific logical groupings of IP address ranges.
- B. Implement Azure Firewall to restrict host pool outbound access.
- C. Configure Azure Active Directory (Azure AD) Conditional Access with multi-factor authentication (MFA) and named locations.
- D. Migrate from the Remote Desktop server to Azure Virtual Desktop.
- E. Deploy a Remote Desktop server to an Azure region located in France.
Answer: BDE
NEW QUESTION 19
......
100% Valid and Newest Version SC-100 Questions & Answers shared by Downloadfreepdf.net, Get Full Dumps HERE: https://www.downloadfreepdf.net/SC-100-pdf-download.html (New 105 Q&As)