A Review Of Pinpoint 156-215.81 Exam Question
Ucertify offers free demo for 156-215.81 exam. "Check Point Certified Security Administrator R81", also known as 156-215.81 exam, is a CheckPoint Certification. This set of posts, Passing the CheckPoint 156-215.81 exam, will help you answer those questions. The 156-215.81 Questions & Answers covers all the knowledge points of the real exam. 100% real CheckPoint 156-215.81 exams and revised by experts!
CheckPoint 156-215.81 Free Dumps Questions Online, Read and Test Now.
NEW QUESTION 1
Which of the following licenses are considered temporary?
- A. Plug-and-play (Trial) and Evaluation
- B. Perpetual and Trial
- C. Evaluation and Subscription
- D. Subscription and Perpetual
Answer: A
NEW QUESTION 2
Which of the following is NOT a valid deployment option for R80?
- A. All-in-one (stand-alone)
- B. CloudGuard
- C. Distributed
- D. Bridge Mode
Answer: B
NEW QUESTION 3
You are asked to check the status of several user-mode processes on the management server and gateway. Which of the following processes can only be seen on a Management Server?
- A. fwd
- B. fwm
- C. cpd
- D. cpwd
Answer: B
NEW QUESTION 4
Most Check Point deployments use Gaia but which product deployment utilizes special Check Point code (with unification in R81.10)?
- A. Enterprise Network Security Appliances
- B. Rugged Appliances
- C. Scalable Platforms
- D. Small Business and Branch Office Appliances
Answer: A
NEW QUESTION 5
Which type of Check Point license ties the package license to the IP address of the Security Management Server?
- A. Central
- B. Corporate
- C. Local
- D. Formal
Answer: A
Explanation:
https://supportcenter.checkpoint.com/supportcenter/portal?eventSubmit_doGoviewsolutiondetails=&solutionid=
NEW QUESTION 6
Access roles allow the firewall administrator to configure network access according to:
- A. remote access clients.
- B. a combination of computer or computer groups and networks.
- C. users and user groups.
- D. All of the above.
Answer: D
Explanation:
To create an access role:
The Access Role window opens.
Your selection is shown in the Networks node in the Role Preview pane.
A window opens. You can search for Active Directory entries or select them from the list. You can search for AD entries or select them from the list.
The access role is added to the Users and Administrators tree. https://sc1.checkpoint.com/documents/R81/WebAdminGuides/EN/CP_R81_SecurityManagement_AdminGuide
NEW QUESTION 7
You have created a rule at the top of your Rule Base to permit Guest Wireless access to the Internet. However, when guest users attempt to reach the Internet, they are not seeing the splash page to accept your Terms of Service, and cannot access the Internet. How can you fix this?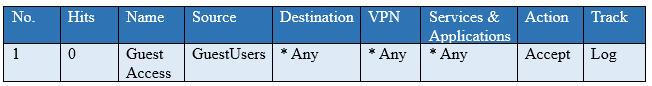
- A. Right click Accept in the rule, select “More”, and then check “Enable Identity Captive Portal”
- B. On the firewall object, Legacy Authentication screen, check “Enable Identity Captive Portal”
- C. In the Captive Portal screen of Global Properties, check “Enable Identity Captive Portal”
- D. On the Security Management Server object, check the box “Identity Logging”
Answer: A
NEW QUESTION 8
When logging in for the first time to a Security management Server through SmartConsole, a fingerprint is saved to the:
- A. Security Management Server’s /home/.fgpt file and is available for future SmartConsole authentications.
- B. Windows registry is available for future Security Management Server authentications.
- C. There is no memory used for saving a fingerprint anyway.
- D. SmartConsole cache is available for future Security Management Server authentications.
Answer: D
NEW QUESTION 9
If the Active Security Management Server fails or if it becomes necessary to change the Active to Standby, the following steps must be taken to prevent data loss. Providing the Active Security Management Server is responsible, which of these steps should NOT be performed:
- A. Rename the hostname of the Standby member to match exactly the hostname of the Active member.
- B. Change the Standby Security Management Server to Active.
- C. Change the Active Security Management Server to Standby.
- D. Manually synchronize the Active and Standby Security Management Servers.
Answer: A
NEW QUESTION 10
Fill in the blank: By default, the SIC certificates issued by R80 Management Server are based on the _______ algorithm.
- A. SHA-256
- B. SHA-200
- C. MD5
- D. SHA-128
Answer: A
NEW QUESTION 11
Name the file that is an electronically signed file used by Check Point to translate the features in the license into a code?
- A. Both License (.lic) and Contract (.xml) files
- B. cp.macro
- C. Contract file (.xml)
- D. license File (.lie)
Answer: B
Explanation:
https://supportcenter.checkpoint.com/supportcenter/portal?eventSubmit_doGoviewsolutiondetails=&solutionid=
NEW QUESTION 12
You noticed that CPU cores on the Security Gateway are usually 100% utilized and many packets were dropped. You don’t have a budget to perform a hardware upgrade at this time. To optimize drops you decide to use Priority Queues and fully enable Dynamic Dispatcher. How can you enable them?
- A. fw ctl multik dynamic_dispatching on
- B. fw ctl multik dynamic_dispatching set_mode 9
- C. fw ctl multik set_mode 9
- D. fw ctl miltik pq enable
Answer: C
NEW QUESTION 13
Which of the following describes how Threat Extraction functions?
- A. Detect threats and provides a detailed report of discovered threats
- B. Proactively detects threats
- C. Delivers file with original content
- D. Delivers PDF versions of original files with active content removed
Answer: B
NEW QUESTION 14
Choose what BEST describes the reason why querying logs now are very fast.
- A. The amount of logs being stored is less than previous versions.
- B. New Smart-1 appliances double the physical memory install.
- C. Indexing Engine indexes logs for faster search results.
- D. SmartConsole now queries results directly from the Security Gateway.
Answer: B
NEW QUESTION 15
Where is the “Hit Count” feature enabled or disabled in SmartConsole?
- A. On the Policy Package
- B. On each Security Gateway
- C. On the Policy layer
- D. In Global Properties for the Security Management Server
Answer: B
Explanation:
References:
NEW QUESTION 16
Which of the following is NOT a tracking log option in R80.x?
- A. Log
- B. Full Log
- C. Detailed Log
- D. Extended Log
Answer: C
NEW QUESTION 17
Choose what BEST describes users on Gaia Platform.
- A. There are two default users and neither can be deleted.
- B. There are two default users and one cannot be deleted.
- C. There is one default user that can be deleted.
- D. There is one default user that cannot be deleted.
Answer: A
Explanation:
These users are created by default and cannot be deleted: admin
Has full read/write capabilities for all Gaia features, from the Gaia Portal and the Gaia Clish. This user has a User ID of 0, and therefore has all of the privileges of a root user.
monitor
Has read-only capabilities for all features in the Gaia Portal and the Gaia Clish, and can change its own password.
You must give a password for this user before the account can be used. https://sc1.checkpoint.com/documents/R81/WebAdminGuides/EN/CP_R81_Gaia_AdminGuide/Topics-GAG/U
NEW QUESTION 18
What object type would you use to grant network access to an LDAP user group?
- A. Access Role
- B. User Group
- C. SmartDirectory Group
- D. Group Template
Answer: B
NEW QUESTION 19
......
P.S. Dumps-files.com now are offering 100% pass ensure 156-215.81 dumps! All 156-215.81 exam questions have been updated with correct answers: https://www.dumps-files.com/files/156-215.81/ (340 New Questions)