Update 156-215.81 Preparation Labs For Check Point Certified Security Administrator R81 Certification
Cause all that matters here is passing the CheckPoint 156-215.81 exam. Cause all that you need is a high score of 156-215.81 Check Point Certified Security Administrator R81 exam. The only one thing you need to do is downloading Examcollection 156-215.81 exam study guides now. We will not let you down with our money-back guarantee.
Also have 156-215.81 free dumps questions for you:
NEW QUESTION 1
When configuring Spoof Tracking, which tracking actions can an administrator select to be done when spoofed packets are detected?
- A. Log, send snmp trap, email
- B. Drop packet, alert, none
- C. Log, alert, none
- D. Log, allow packets, email
Answer: C
Explanation:
Configure Spoof Tracking - select the tracking action that is done when spoofed packets are detected:
NEW QUESTION 2
In R80 Management, apart from using SmartConsole, objects or rules can also be modified using:
- A. 3rd Party integration of CLI and API for Gateways prior to R80.
- B. A complete CLI and API interface using SSH and custom CPCode integration.
- C. 3rd Party integration of CLI and API for Management prior to R80.
- D. A complete CLI and API interface for Management with 3rd Party integration.
Answer: B
NEW QUESTION 3
URL Filtering cannot be used to:
- A. Control Bandwidth issues
- B. Control Data Security
- C. Improve organizational security
- D. Decrease legal liability
Answer: D
Explanation:
https://sc1.checkpoint.com/documents/R81/WebAdminGuides/EN/CP_R81_SecurityManagement_AdminGuide
NEW QUESTION 4
You can see the following graphic: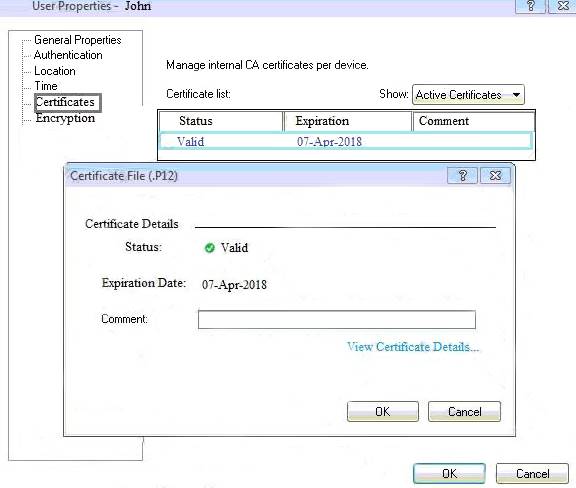
What is presented on it?
- A. Properties of personal .p12 certificate file issued for user John.
- B. Shared secret properties of John’s password.
- C. VPN certificate properties of the John’s gateway.
- D. Expired .p12 certificate properties for user John.
Answer: A
NEW QUESTION 5
Fill in the blanks: There are ______ types of software containers ______.
- A. Three; security management, Security Gateway, and endpoint security
- B. Three; Security gateway, endpoint security, and gateway management
- C. Two; security management and endpoint security
- D. Two; endpoint security and Security Gateway
Answer: A
Explanation:
There are three types of Software Containers: Security Management, Security Gateway, and Endpoint Security.
NEW QUESTION 6
When an Admin logs into SmartConsole and sees a lock icon on a gateway object and cannot edit that object, what does that indicate?
- A. The gateway is not powered on.
- B. Incorrect routing to reach the gateway.
- C. The Admin would need to login to Read-Only mode
- D. Another Admin has made an edit to that object and has yet to publish the change.
Answer: D
NEW QUESTION 7
Which of the following commands is used to monitor cluster members in CLI?
- A. show cluster state
- B. show active cluster
- C. show clusters
- D. show running cluster
Answer: A
NEW QUESTION 8
What is the SOLR database for?
- A. Used for full text search and enables powerful matching capabilities
- B. Writes data to the database and full text search
- C. Serves GUI responsible to transfer request to the DLE server
- D. Enables powerful matching capabilities and writes data to the database
Answer: A
NEW QUESTION 9
When defining group-based access in an LDAP environment with Identity Awareness, what is the BEST object type to represent an LDAP group in a Security Policy?
- A. Access Role
- B. User Group
- C. SmartDirectory Group
- D. Group Template
Answer: A
NEW QUESTION 10
What are the three types of UserCheck messages?
- A. inform, ask, and block
- B. block, action, and warn
- C. action, inform, and ask
- D. ask, block, and notify
Answer: A
Explanation:
Inform User Inform
Shows when the action for the ruleClosed is inform. It informs users what the company policy is for that site. Blocked Message
Block
Shows when a request is blocked. Ask User
Ask
Shows when the action for the rule is ask. It informs users what the company policy is for that site and they must click OK to continue to the site.
https://sc1.checkpoint.com/documents/R81/WebAdminGuides/EN/CP_R81_DataLossPrevention_AdminGuide/
NEW QUESTION 11
Fill in the blank: An LDAP server holds one or more ______.
- A. Server Units
- B. Administrator Units
- C. Account Units
- D. Account Servers
Answer: C
NEW QUESTION 12
The competition between stateful inspection and proxies was based on performance, protocol support, and security. Considering stateful Inspections and Proxies, which statement is correct?
- A. Stateful Inspection is limited to Layer 3 visibility, with no Layer 4 to Layer 7 visibility capabilities.
- B. When it comes to performance, proxies were significantly faster than stateful inspection firewalls.
- C. Proxies offer far more security because of being able to give visibility of the payload (the data).
- D. When it comes to performance, stateful inspection was significantly faster than proxies.
Answer: C
NEW QUESTION 13
Security Gateway software blades must be attached to what?
- A. Security Gateway
- B. Security Gateway container
- C. Management server
- D. Management container
Answer: B
Explanation:
Security Management and Security Gateway Software Blades must be attached to a Software Container to be licensed. https://downloads.checkpoint.com/dc/download.htm?ID=11608
NEW QUESTION 14
One of major features in R80.x SmartConsole is concurrent administration. Which of the following is NOT possible considering that AdminA, AdminB, and AdminC are editing the same Security Policy?
- A. AdminC sees a lock icon which indicates that the rule is locked for editing by another administrator.
- B. AdminA and AdminB are editing the same rule at the same time.
- C. AdminB sees a pencil icon next the rule that AdminB is currently editing.
- D. AdminA, AdminB and AdminC are editing three different rules at the same time.
Answer: B
NEW QUESTION 15
What type of NAT is a one-to-one relationship where each host is translated to a unique address?
- A. Source
- B. Static
- C. Hide
- D. Destination
Answer: B
NEW QUESTION 16
In Logging and Monitoring, the tracking options are Log, Detailed Log and Extended Log. Which of the following options can you add to each Log, Detailed Log and Extended Log?
- A. Accounting
- B. Suppression
- C. Accounting/Suppression
- D. Accounting/Extended
Answer: C
NEW QUESTION 17
Which of these is NOT a feature or benefit of Application Control?
- A. Eliminate unknown and unwanted applications in your network to reduce IT complexity and application risk.
- B. Identify and control which applications are in your IT environment and which to add to the IT environment.
- C. Scans the content of files being downloaded by users in order to make policy decisions.
- D. Automatically identify trusted software that has authorization to run
Answer: C
Explanation:
File scanning is a job for ThreatCloud and it sandboxes/scrubs files.
NEW QUESTION 18
In what way is Secure Network Distributor (SND) a relevant feature of the Security Gateway?
- A. SND is a feature to accelerate multiple SSL VPN connections
- B. SND is an alternative to IPSec Main Mode, using only 3 packets
- C. SND is used to distribute packets among Firewall instances
- D. SND is a feature of fw monitor to capture accelerated packets
Answer: C
NEW QUESTION 19
......
P.S. 2passeasy now are offering 100% pass ensure 156-215.81 dumps! All 156-215.81 exam questions have been updated with correct answers: https://www.2passeasy.com/dumps/156-215.81/ (340 New Questions)