A Review Of Free 200-201 Dumps Questions
It is impossible to pass Cisco 200-201 exam without any help in the short term. Come to Actualtests soon and find the most advanced, correct and guaranteed Cisco 200-201 practice questions. You will get a surprising result by our Latest Understanding Cisco Cybersecurity Operations Fundamentals practice guides.
Free demo questions for Cisco 200-201 Exam Dumps Below:
NEW QUESTION 1
An analyst is investigating a host in the network that appears to be communicating to a command and control server on the Internet. After collecting this packet capture the analyst cannot determine the technique and payload used for the communication.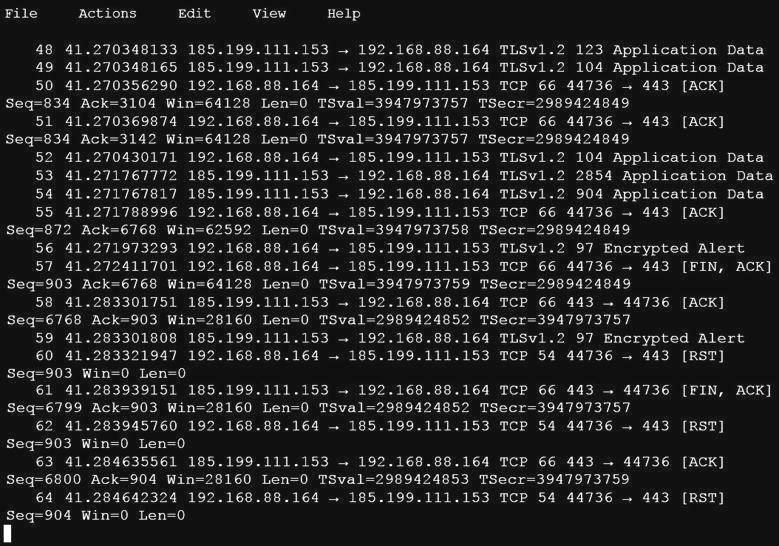
Which obfuscation technique is the attacker using?
- A. Base64 encoding
- B. transport layer security encryption
- C. SHA-256 hashing
- D. ROT13 encryption
Answer: B
NEW QUESTION 2
What is the difference between a threat and a risk?
- A. Threat represents a potential danger that could take advantage of a weakness in a system
- B. Risk represents the known and identified loss or danger in the system
- C. Risk represents the nonintentional interaction with uncertainty in the system
- D. Threat represents a state of being exposed to an attack or a compromise either physically or logically
Answer: A
NEW QUESTION 3
Refer to the exhibit.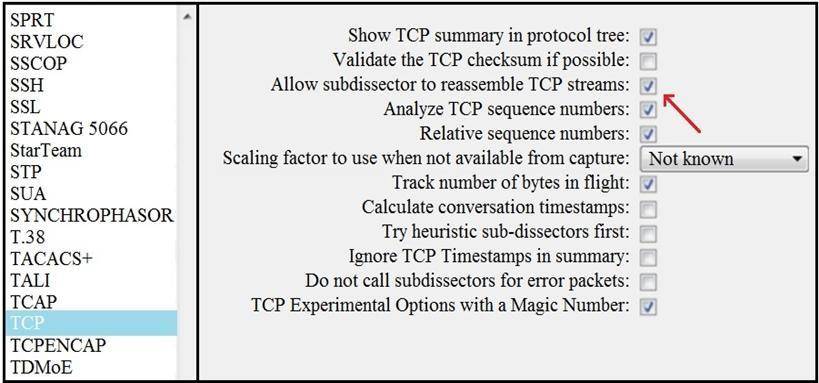
What is the expected result when the "Allow subdissector to reassemble TCP streams" feature is enabled?
- A. insert TCP subdissectors
- B. extract a file from a packet capture
- C. disable TCP streams
- D. unfragment TCP
Answer: D
NEW QUESTION 4
When communicating via TLS, the client initiates the handshake to the server and the server responds back with its certificate for identification.
Which information is available on the server certificate?
- A. server name, trusted subordinate CA, and private key
- B. trusted subordinate CA, public key, and cipher suites
- C. trusted CA name, cipher suites, and private key
- D. server name, trusted CA, and public key
Answer: D
NEW QUESTION 5
Which event artifact is used to identify HTTP GET requests for a specific file?
- A. destination IP address
- B. URI
- C. HTTP status code
- D. TCP ACK
Answer: B
NEW QUESTION 6
Which step in the incident response process researches an attacking host through logs in a SIEM?
- A. detection and analysis
- B. preparation
- C. eradication
- D. containment
Answer: A
NEW QUESTION 7
A system administrator is ensuring that specific registry information is accurate.
Which type of configuration information does the HKEY_LOCAL_MACHINE hive contain?
- A. file extension associations
- B. hardware, software, and security settings for the system
- C. currently logged in users, including folders and control panel settings
- D. all users on the system, including visual settings
Answer: B
NEW QUESTION 8
Refer to the exhibit.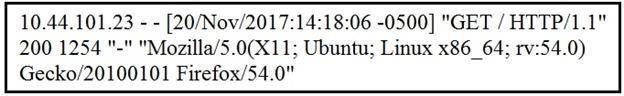
What does the message indicate?
- A. an access attempt was made from the Mosaic web browser
- B. a successful access attempt was made to retrieve the password file
- C. a successful access attempt was made to retrieve the root of the website
- D. a denied access attempt was made to retrieve the password file
Answer: C
NEW QUESTION 9
An analyst is exploring the functionality of different operating systems.
What is a feature of Windows Management Instrumentation that must be considered when deciding on an operating system?
- A. queries Linux devices that have Microsoft Services for Linux installed
- B. deploys Windows Operating Systems in an automated fashion
- C. is an efficient tool for working with Active Directory
- D. has a Common Information Model, which describes installed hardware and software
Answer: D
NEW QUESTION 10
In a SOC environment, what is a vulnerability management metric?
- A. code signing enforcement
- B. full assets scan
- C. internet exposed devices
- D. single factor authentication
Answer: D
NEW QUESTION 11
Which type of attack occurs when an attacker is successful in eavesdropping on a conversation between two IP phones?
- A. known-plaintext
- B. replay
- C. dictionary
- D. man-in-the-middle
Answer: D
NEW QUESTION 12
Which evasion technique is indicated when an intrusion detection system begins receiving an abnormally high volume of scanning from numerous sources?
- A. resource exhaustion
- B. tunneling
- C. traffic fragmentation
- D. timing attack
Answer: A
NEW QUESTION 13
An organization has recently adjusted its security stance in response to online threats made by a known hacktivist group.
What is the initial event called in the NIST SP800-61?
- A. online assault
- B. precursor
- C. trigger
- D. instigator
Answer: B
NEW QUESTION 14
Which two elements are assets in the role of attribution in an investigation? (Choose two.)
- A. context
- B. session
- C. laptop
- D. firewall logs
- E. threat actor
Answer: AE
NEW QUESTION 15
Which list identifies the information that the client sends to the server in the negotiation phase of the TLS handshake?
- A. ClientStart, ClientKeyExchange, cipher-suites it supports, and suggested compression methods
- B. ClientStart, TLS versions it supports, cipher-suites it supports, and suggested compression methods
- C. ClientHello, TLS versions it supports, cipher-suites it supports, and suggested compression methods
- D. ClientHello, ClientKeyExchange, cipher-suites it supports, and suggested compression methods
Answer: C
NEW QUESTION 16
An engineer receives a security alert that traffic with a known TOR exit node has occurred on the network. What is the impact of this traffic?
- A. ransomware communicating after infection
- B. users downloading copyrighted content
- C. data exfiltration
- D. user circumvention of the firewall
Answer: D
NEW QUESTION 17
When trying to evade IDS/IPS devices, which mechanism allows the user to make the data incomprehensible without a specific key, certificate, or password?
- A. fragmentation
- B. pivoting
- C. encryption
- D. stenography
Answer: D
NEW QUESTION 18
Which process is used when IPS events are removed to improve data integrity?
- A. data availability
- B. data normalization
- C. data signature
- D. data protection
Answer: B
NEW QUESTION 19
What is a difference between SOAR and SIEM?
- A. SOAR platforms are used for threat and vulnerability management, but SIEM applications are not
- B. SIEM applications are used for threat and vulnerability management, but SOAR platforms are not
- C. SOAR receives information from a single platform and delivers it to a SIEM
- D. SIEM receives information from a single platform and delivers it to a SOAR
Answer: A
NEW QUESTION 20
While viewing packet capture data, an analyst sees that one IP is sending and receiving traffic for multiple devices by modifying the IP header.
Which technology makes this behavior possible?
- A. encapsulation
- B. TOR
- C. tunneling
- D. NAT
Answer: D
NEW QUESTION 21
......
Thanks for reading the newest 200-201 exam dumps! We recommend you to try the PREMIUM Dumps-files.com 200-201 dumps in VCE and PDF here: https://www.dumps-files.com/files/200-201/ (98 Q&As Dumps)