The Secret Of Cisco 200-201 Real Exam
Act now and download your Cisco 200-201 test today! Do not waste time for the worthless Cisco 200-201 tutorials. Download Refresh Cisco Understanding Cisco Cybersecurity Operations Fundamentals exam with real questions and answers and begin to learn Cisco 200-201 with a classic professional.
Cisco 200-201 Free Dumps Questions Online, Read and Test Now.
NEW QUESTION 1
Which security principle is violated by running all processes as root or administrator?
- A. principle of least privilege
- B. role-based access control
- C. separation of duties
- D. trusted computing base
Answer: A
NEW QUESTION 2
What is the practice of giving an employee access to only the resources needed to accomplish their job?
- A. principle of least privilege
- B. organizational separation
- C. separation of duties
- D. need to know principle
Answer: A
NEW QUESTION 3
Which action prevents buffer overflow attacks?
- A. variable randomization
- B. using web based applications
- C. input sanitization
- D. using a Linux operating system
Answer: C
NEW QUESTION 4
Which category relates to improper use or disclosure of PII data?
- A. legal
- B. compliance
- C. regulated
- D. contractual
Answer: C
NEW QUESTION 5
What is the difference between statistical detection and rule-based detection models?
- A. Rule-based detection involves the collection of data in relation to the behavior of legitimate users over a period of time
- B. Statistical detection defines legitimate data of users over a period of time and rule-based detection defines it on an IF/THEN basis
- C. Statistical detection involves the evaluation of an object on its intended actions before it executes that behavior
- D. Rule-based detection defines legitimate data of users over a period of time and statistical detection defines it on an IF/THEN basis
Answer: B
NEW QUESTION 6
Which type of data consists of connection level, application-specific records generated from network traffic?
- A. transaction data
- B. location data
- C. statistical data
- D. alert data
Answer: A
NEW QUESTION 7
Which two compliance frameworks require that data be encrypted when it is transmitted over a public network?
(Choose two.)
- A. PCI
- B. GLBA
- C. HIPAA
- D. SOX
- E. COBIT
Answer: AC
NEW QUESTION 8
An investigator is examining a copy of an ISO file that is stored in CDFS format. What type of evidence is this file?
- A. data from a CD copied using Mac-based system
- B. data from a CD copied using Linux system
- C. data from a DVD copied using Windows system
- D. data from a CD copied using Windows
Answer: B
NEW QUESTION 9
What does cyber attribution identity in an investigation?
- A. cause of an attack
- B. exploit of an attack
- C. vulnerabilities exploited
- D. threat actors of an attack
Answer: D
NEW QUESTION 10
An analyst discovers that a legitimate security alert has been dismissed. Which signature caused this impact on network traffic?
- A. true negative
- B. false negative
- C. false positive
- D. true positive
Answer: B
NEW QUESTION 11
What is an example of social engineering attacks?
- A. receiving an unexpected email from an unknown person with an uncharacteristic attachment from someone in the same company
- B. receiving an email from human resources requesting a visit to their secure website to update contact information
- C. sending a verbal request to an administrator who knows how to change an account password
- D. receiving an invitation to the department’s weekly WebEx meeting
Answer: B
NEW QUESTION 12
Refer to the exhibit.
What does the output indicate about the server with the IP address 172.18.104.139?
- A. open ports of a web server
- B. open port of an FTP server
- C. open ports of an email server
- D. running processes of the server
Answer: C
NEW QUESTION 13
Why is encryption challenging to security monitoring?
- A. Encryption analysis is used by attackers to monitor VPN tunnels.
- B. Encryption is used by threat actors as a method of evasion and obfuscation.
- C. Encryption introduces additional processing requirements by the CPU.
- D. Encryption introduces larger packet sizes to analyze and store.
Answer: B
NEW QUESTION 14
An intruder attempted malicious activity and exchanged emails with a user and received corporate information, including email distribution lists. The intruder asked the user to engage with a link in an email. When the fink launched, it infected machines and the intruder was able to access the corporate network.
Which testing method did the intruder use?
- A. social engineering
- B. eavesdropping
- C. piggybacking
- D. tailgating
Answer: A
NEW QUESTION 15
Which event is user interaction?
- A. gaining root access
- B. executing remote code
- C. reading and writing file permission
- D. opening a malicious file
Answer: D
NEW QUESTION 16
Drag and drop the technology on the left onto the data type the technology provides on the right.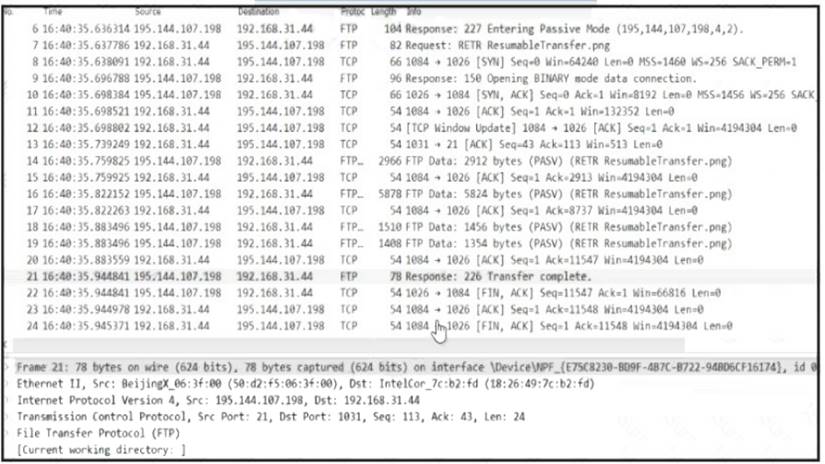
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 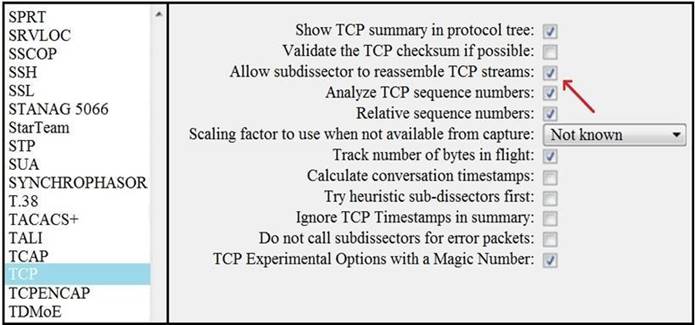
NEW QUESTION 17
How does an attacker observe network traffic exchanged between two users?
- A. port scanning
- B. man-in-the-middle
- C. command injection
- D. denial of service
Answer: B
NEW QUESTION 18
What is the difference between the ACK flag and the RST flag in the NetFlow log session?
- A. The RST flag confirms the beginning of the TCP connection, and the ACK flag responds when the data for the payload is complete
- B. The ACK flag confirms the beginning of the TCP connection, and the RST flag responds when the data for the payload is complete
- C. The RST flag confirms the receipt of the prior segment, and the ACK flag allows for the spontaneous termination of a connection
- D. The ACK flag confirms the receipt of the prior segment, and the RST flag allows for the spontaneous termination of a connection
Answer: D
NEW QUESTION 19
Refer to the exhibit.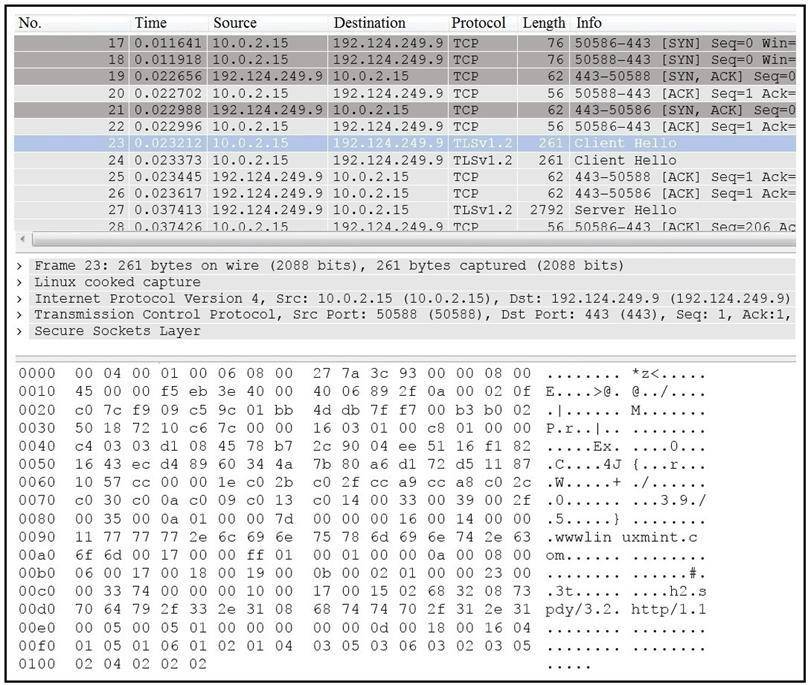
Drag and drop the element name from the left onto the correct piece of the PCAP file on the right.
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 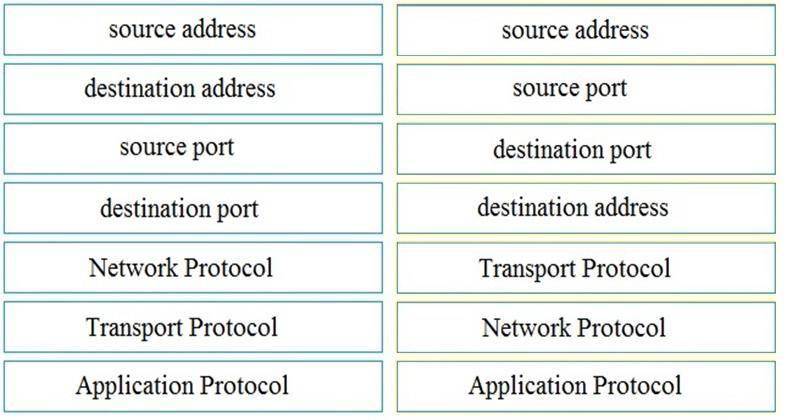
NEW QUESTION 20
What is personally identifiable information that must be safeguarded from unauthorized access?
- A. date of birth
- B. driver's license number
- C. gender
- D. zip code
Answer: B
NEW QUESTION 21
......
P.S. Easily pass 200-201 Exam with 98 Q&As Dumps-files.com Dumps & pdf Version, Welcome to Download the Newest Dumps-files.com 200-201 Dumps: https://www.dumps-files.com/files/200-201/ (98 New Questions)