How Many Questions Of 250-438 Test Preparation
Our pass rate is high to 98.9% and the similarity percentage between our 250-438 study guide and real exam is 90% based on our seven-year educating experience. Do you want achievements in the Symantec 250-438 exam in just one try? I am currently studying for the Symantec 250-438 exam. Latest Symantec 250-438 Test exam practice questions and answers, Try Symantec 250-438 Brain Dumps First.
Also have 250-438 free dumps questions for you:
NEW QUESTION 1
Which two actions are available for a “Network Prevent: Remove HTTP/HTTPS content” response rule when the content is unable to be removed? (Choose two.)
- A. Allow the content to be posted
- B. Remove the content through FlexResponse
- C. Block the content before posting
- D. Encrypt the content before posting
- E. Redirect the content to an alternative destination
Answer: AE
NEW QUESTION 2
Which two detection technology options run on the DLP agent? (Choose two.)
- A. Optical Character Recognition (OCR)
- B. Described Content Matching (DCM)
- C. Directory Group Matching (DGM)
- D. Form Recognition
- E. Indexed Document Matching (IDM)
Answer: BE
NEW QUESTION 3
Which option correctly describes the two-tier installation type for Symantec DLP?
- A. Install the Oracle database on the host, and install the Enforce server and a detection server on a second host.
- B. Install the Oracle database on a local physical host, and install the Enforce server and detection servers on virtual hosts in the Cloud.
- C. Install the Oracle database and a detection server in the same host, and install the Enforce server on a second host.
- D. Install the Oracle database and Enforce server on the same host, and install detection servers on separate hosts.
Answer: D
Explanation:
Reference: https://www.symantec.com/connect/forums/deployment-enforce-and-detection-servers
NEW QUESTION 4
Which two Infrastructure-as-a-Service providers are supported for hosting Cloud Prevent for Office 365? (Choose two.)
- A. Any customer-hosted private cloud
- B. Amazon Web Services
- C. AT&T
- D. Verizon
- E. Rackspace
Answer: BE
NEW QUESTION 5
Which two DLP products support the new Optical Character Recognition (OCR) engine in Symantec DLP 15.0? (Choose two.)
- A. Endpoint Prevent
- B. Cloud Service for Email
- C. Network Prevent for Email
- D. Network Discover
- E. Cloud Detection Service
Answer: BC
NEW QUESTION 6
Which two components can perform a file system scan of a workstation? (Choose two.)
- A. Endpoint Server
- B. DLP Agent
- C. Network Prevent for Web Server
- D. Discover Server
- E. Enforce Server
Answer: BD
NEW QUESTION 7
Which detection method depends on “training sets”?
- A. Form Recognition
- B. Vector Machine Learning (VML)
- C. Index Document Matching (IDM)
- D. Exact Data Matching (EDM)
Answer: B
Explanation:
Reference: http://eval.symantec.com/mktginfo/enterprise/white_papers/b-dlp_machine_learning.WP_en-us.pdf
NEW QUESTION 8
What is the correct order for data in motion when a customer has integrated their CloudSOC and DLP solutions?
- A. User > CloudSOC Gatelet > DLP Cloud Detection Service > Application
- B. User > Enforce > Application
- C. User > Enforce > CloudSOC > Application
- D. User > CloudSOC Gatelet > Enforce > Application
Answer: C
NEW QUESTION 9
Why is it important for an administrator to utilize the grid scan feature?
- A. To distribute the scan workload across multiple network discover servers
- B. To distribute the scan workload across the cloud servers
- C. To distribute the scan workload across multiple endpoint servers
- D. To distribute the scan workload across multiple detection servers
Answer: D
Explanation:
If you plan to use the grid scanning feature to distribute the scanning workload across multiple detection servers, retain the default value (1)
NEW QUESTION 10
A DLP administrator has enabled and successfully tested custom attribute lookups for incident data based on the Active Directory LDAP plugin. The Chief Information Security Officer (CISO) has attempted to generate a User Risk Summary report, but the report is empty. The DLP administrator confirms the Cisco’s role has the “User Reporting” privilege enabled, but User Risk reporting is still not working.
What is the probable reason that the User Risk Summary report is blank?
- A. Only DLP administrators are permitted to access and view data for high risk users.
- B. The Enforce server has insufficient permissions for importing user attributes.
- C. User attribute data must be configured separately from incident data attributes.
- D. User attributes have been incorrectly mapped to Active Directory accounts.
Answer: D
NEW QUESTION 11
What detection server is used for Network Discover, Network Protect, and Cloud Storage?
- A. Network Protect Storage Discover
- B. Network Discover/Cloud Storage Discover
- C. Network Prevent/Cloud Detection Service
- D. Network Protect/Cloud Detection Service
Answer: B
Explanation:
Reference: https://help.symantec.com/cs/dlp15.0/DLP/v16110606_v120691346/Modifying-the-Network-Discover-Cloud-Storage-Discover-Server-configuration?locale=EN_US
NEW QUESTION 12
Which Network Prevent action takes place when the Network Incident list shows the message is “Modified”?
- A. Remove attachments from an email
- B. Obfuscate text in the body of an email
- C. Add one or more SMTP headers to an email
- D. Modify content from the body of an email
Answer: C
NEW QUESTION 13
A DLP administrator is checking the System Overview in the Enforce management console, and all of the detection servers are showing as “unknown”. The Vontu services are up and running on the detection servers. Thousands of .IDC files are building up in the Incidents directory on the detection servers. There is good network connectivity between the detection servers and the Enforce server when testing with the telnet command.
How should the administrator bring the detection servers to a running state in the Enforce management console?
- A. Restart the Vontu Update Service on the Enforce server
- B. Ensure the Vontu Monitor Controller service is running in the Enforce server
- C. Delete all of the .BAD files in the Incidents folder on the Enforce server
- D. Restart the Vontu Monitor Service on all the affected detection servers
Answer: B
NEW QUESTION 14
What should an incident responder select in the Enforce management console to remediate multiple incidents simultaneously?
- A. Smart Response on the Incident page
- B. Automated Response on the Incident Snapshot page
- C. Smart Response on an Incident List report
- D. Automated Response on an Incident List report
Answer: B
NEW QUESTION 15
A divisional executive requests a report of all incidents generated by a particular region, summarized by department. What does the DLP administrator need to configure to generate this report?
- A. Custom attributes
- B. Status attributes
- C. Sender attributes
- D. User attributes
Answer: A
NEW QUESTION 16
Which channel does Endpoint Prevent protect using Device Control?
- A. Bluetooth
- B. USB storage
- C. CD/DVD
- D. Network card
Answer: B
Explanation:
Reference: https://support.symantec.com/en_US/article.HOWTO80865.html#v36651044
NEW QUESTION 17
Under the “System Overview” in the Enforce management console, the status of a Network Monitor detection server is shown as “Running Selected.” The Network Monitor server’s event logs indicate that the packet capture and filereader processes are crashing.
What is a possible cause for the Network Monitor server being in this state?
- A. There is insufficient disk space on the Network Monitor server.
- B. The Network Monitor server’s certificate is corrupt or missing.
- C. The Network Monitor server’s license file has expired.
- D. The Enforce and Network Monitor servers are running different versions of DLP.
Answer: D
NEW QUESTION 18
Which action is available for use in both Smart Response and Automated Response rules?
- A. Log to a Syslog Server
- B. Limit incident data retention
- C. Modify SMTP message
- D. Block email message
Answer: D
NEW QUESTION 19
Where should an administrator set the debug levels for an Endpoint Agent?
- A. Setting the log level within the Agent List
- B. Advanced configuration within the Agent settings
- C. Setting the log level within the Agent Overview
- D. Advanced server settings within the Endpoint server
Answer: C
Explanation:
Reference: https://support.symantec.com/en_US/article.TECH248581.html
NEW QUESTION 20
What is the default fallback option for the Endpoint Prevent Encrypt response rule?
- A. Block
- B. User Cancel
- C. Encrypt
- D. Notify
Answer: D
NEW QUESTION 21
Refer to the exhibit. Which type of Endpoint response rule is shown?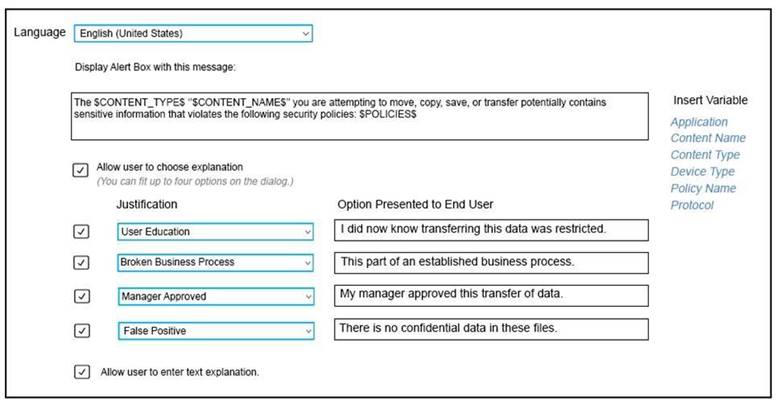
- A. Endpoint Prevent: User Notification
- B. Endpoint Prevent: Block
- C. Endpoint Prevent: Notify
- D. Endpoint Prevent: User Cancel
Answer: B
Explanation:
Reference: https://help.symantec.com/cs/dlp15.0/DLP/v27595430_v120691346/Configuring-the-Endpoint-Prevent:-Block-action?locale=EN_US
NEW QUESTION 22
An administrator is unable to log in to the Enforce management console as “sysadmin”. Symantec DLP is configured to use Active Directory authentication. The administrator is a member of two roles: “sysadmin” and “remediator.” How should the administrator log in to the Enforce console with the “sysadmin” role?
- A. sysadminusername
- B. sysadminusername@domain
- C. domainusername
- D. usernamesysadmin
Answer: C
NEW QUESTION 23
A DLP administrator created a new agent configuration for an Endpoint server. However, the endpoint agents fail to receive the new configuration. What is one possible reason that the agent fails to receive the new configuration?
- A. The new agent configuration was saved but not applied to any endpoint groups.
- B. The new agent configuration was copied and modified from the default agent configuration.
- C. The default agent configuration must be disabled before the new configuration can take effect.
- D. The Endpoint server needs to be recycled so that the new agent configuration can take effect.
Answer: C
NEW QUESTION 24
Which two detection technology options ONLY run on a detection server? (Choose two.)
- A. Form Recognition
- B. Indexed Document Matching (IDM)
- C. Described Content Matching (DCM)
- D. Exact Data Matching (EDM)
- E. Vector Machine Learning (VML)
Answer: BD
Explanation:
Reference: https://support.symantec.com/en_US/article.INFO5070.html
NEW QUESTION 25
......
P.S. Downloadfreepdf.net now are offering 100% pass ensure 250-438 dumps! All 250-438 exam questions have been updated with correct answers: https://www.downloadfreepdf.net/250-438-pdf-download.html (70 New Questions)