The Avant-garde Guide To 350-701 Questions Pool
Master the 350-701 Implementing and Operating Cisco Security Core Technologies content and be ready for exam day success quickly with this Testking 350-701 training. We guarantee it!We make it a reality and give you real 350-701 questions in our Cisco 350-701 braindumps.Latest 100% VALID Cisco 350-701 Exam Questions Dumps at below page. You can use our Cisco 350-701 braindumps and pass your exam.
Online 350-701 free questions and answers of New Version:
NEW QUESTION 1
Which technology is used to improve web traffic performance by proxy caching?
- A. WSA
- B. Firepower
- C. FireSIGHT
- D. ASA
Answer: A
NEW QUESTION 2
Where are individual sites specified to be blacklisted in Cisco Umbrella?
- A. application settings
- B. content categories
- C. security settings
- D. destination lists
Answer: D
NEW QUESTION 3
What is the primary difference between an Endpoint Protection Platform and an Endpoint Detection and Response?
- A. EPP focuses on prevention, and EDR focuses on advanced threats that evade perimeter defenses.
- B. EDR focuses on prevention, and EPP focuses on advanced threats that evade perimeter defenses.
- C. EPP focuses on network security, and EDR focuses on device security.
- D. EDR focuses on network security, and EPP focuses on device security.
Answer: A
Explanation:
Reference: https://www.cisco.com/c/en/us/products/security/endpoint-security/what-is-endpoint-detection-response-edr.html
NEW QUESTION 4
Which functions of an SDN architecture require southbound APIs to enable communication?
- A. SDN controller and the network elements
- B. management console and the SDN controller
- C. management console and the cloud
- D. SDN controller and the cloud
Answer: A
NEW QUESTION 5
Which statement about IOS zone-based firewalls is true?
- A. An unassigned interface can communicate with assigned interfaces
- B. Only one interface can be assigned to a zone.
- C. An interface can be assigned to multiple zones.
- D. An interface can be assigned only to one zone.
Answer: D
Explanation:
Reference: https://www.cisco.com/c/en/us/support/docs/security/ios-firewall/98628-zone-design-guide.html
NEW QUESTION 6
What can be integrated with Cisco Threat Intelligence Director to provide information about security threats, which allows the SOC to proactively automate responses to those threats?
- A. Cisco Umbrella
- B. External Threat Feeds
- C. Cisco Threat Grid
- D. Cisco Stealthwatch
Answer: C
NEW QUESTION 7
An engineer configured a new network identity in Cisco Umbrella but must verify that traffic is being routed through the Cisco Umbrella network. Which action tests the routing?
- A. Ensure that the client computers are pointing to the on-premises DNS servers.
- B. Enable the Intelligent Proxy to validate that traffic is being routed correctly.
- C. Add the public IP address that the client computers are behind to a Core Identity.
- D. Browse to http://welcome.umbrella.com/ to validate that the new identity is working.
Answer: B
NEW QUESTION 8
What is the function of Cisco Cloudlock for data security?
- A. data loss prevention
- B. controls malicious cloud apps
- C. detects anomalies
- D. user and entity behavior analytics
Answer: A
Explanation:
Reference: https://umbrella.cisco.com/products/casb
NEW QUESTION 9
What is a characteristic of Cisco ASA Netflow v9 Secure Event Logging?
- A. It tracks flow-create, flow-teardown, and flow-denied events.
- B. It provides stateless IP flow tracking that exports all records of a specific flow.
- C. It tracks the flow continuously and provides updates every 10 seconds.
- D. Its events match all traffic classes in parallel.
Answer: A
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/security/asa/asa92/configuration/general/asa-general-cli/monitor-nsel.html
NEW QUESTION 10
Which two conditions are prerequisites for stateful failover for IPsec? (Choose two.)
- A. Only the IKE configuration that is set up on the active device must be duplicated on the standby device; the IPsec configuration is copied automatically.
- B. The active and standby devices can run different versions of the Cisco IOS software but must be the same type of device.
- C. The IPsec configuration that is set up on the active device must be duplicated on the standby device.
- D. Only the IPsec configuration that is set up on the active device must be duplicated on the standby device; the IKE configuration is copied automatically.
- E. The active and standby devices must run the same version of the Cisco IOS software and must be the same type of device.
Answer: BC
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/ios-xml/ios/sec_conn_vpnav/configuration/15-mt/sec-vpn-availability-15-mt-book/sec-state-fail-ipsec.html
NEW QUESTION 11
Which ID store requires that a shadow user be created on Cisco ISE for the admin login to work?
- A. RSA SecureID
- B. Internal Database
- C. Active Directory
- D. LDAP
Answer: C
NEW QUESTION 12
Refer to the exhibit.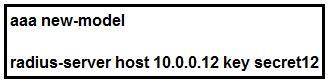
Which statement about the authentication protocol used in the configuration is true?
- A. The authentication request contains only a password
- B. The authentication request contains only a username
- C. The authentication and authorization requests are grouped in a single packet.
- D. There are separate authentication and authorization request packets.
Answer: C
NEW QUESTION 13
An administrator wants to ensure that all endpoints are compliant before users are allowed access on the corporate network. The endpoints must have the corporate antivirus application installed and be running the latest build of Windows 10. What must the administrator implement to ensure that all devices are compliant before they are allowed on the network?
- A. Cisco Identity Services Engine and AnyConnect Posture module
- B. Cisco Stealthwatch and Cisco Identity Services Engine integration
- C. Cisco ASA firewall with Dynamic Access Policies configured
- D. Cisco Identity Services Engine with PxGrid services enabled
Answer: A
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/security/vpn_client/anyconnect/anyconnect46/administration/guide/b_AnyConnect_Administrator_Guide_4-6/configure-posture.html
NEW QUESTION 14
What is the result of running the crypto isakmp key ciscXXXXXXXX address 172.16.0.0 command?
- A. authenticates the IKEv2 peers in the 172.16.0.0/16 range by using the key ciscXXXXXXXX
- B. authenticates the IP address of the 172.16.0.0/32 peer by using the key ciscXXXXXXXX
- C. authenticates the IKEv1 peers in the 172.16.0.0/16 range by using the key ciscXXXXXXXX
- D. secures all the certificates in the IKE exchange by using the key ciscXXXXXXXX
Answer: B
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/ios-xml/ios/security/a1/sec-a1-cr-book/sec-cr-c4.html#wp6039879000
NEW QUESTION 15
What is a characteristic of Dynamic ARP Inspection?
- A. DAI determines the validity of an ARP packet based on valid IP to MAC address bindings from the DHCP snooping binding database.
- B. In a typical network, make all ports as trusted except for the ports connecting to switches, which are untrusted.
- C. DAI associates a trust state with each switch.
- D. DAI intercepts all ARP requests and responses on trusted ports only.
Answer: A
NEW QUESTION 16
In a PaaS model, which layer is the tenant responsible for maintaining and patching?
- A. hypervisor
- B. virtual machine
- C. network
- D. application
Answer: D
Explanation:
Reference: https://www.bmc.com/blogs/saas-vs-paas-vs-iaas-whats-the-difference-and-how-to-choose/
NEW QUESTION 17
What is a characteristic of traffic storm control behavior?
- A. Traffic storm control drops all broadcast and multicast traffic if the combined traffic exceeds the level within the interval.
- B. Traffic storm control cannot determine if the packet is unicast or broadcast.
- C. Traffic storm control monitors incoming traffic levels over a 10-second traffic storm control interval.
- D. Traffic storm control uses the Individual/Group bit in the packet source address to determine if the packet is unicast or broadcast.
Answer: A
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/routers/7600/ios/12-1E/configuration/guide/storm.html
NEW QUESTION 18
An engineer needs a solution for TACACS+ authentication and authorization for device administration. The engineer also wants to enhance wired and wireless network security by requiring users and endpoints to use 802.1X, MAB, or WebAuth. Which product meets all of these requirements?
- A. Cisco Prime Infrastructure
- B. Cisco Identity Services Engine
- C. Cisco Stealthwatch
- D. Cisco AMP for Endpoints
Answer: B
NEW QUESTION 19
The Cisco ASA must support TLS proxy for encrypted Cisco Unified Communications traffic. Where must the ASA be added on the Cisco UC Manager platform?
- A. Certificate Trust List
- B. Endpoint Trust List
- C. Enterprise Proxy Service
- D. Secured Collaboration Proxy
Answer: A
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/security/asa/special/unified-communications/guide/unified-comm/unified-comm-tlsproxy.html
NEW QUESTION 20
Which VPN technology can support a multivendor environment and secure traffic between sites?
- A. SSL VPN
- B. GET VPN
- C. FlexVPN
- D. DMVPN
Answer: C
Explanation:
Reference: https://www.cisco.com/c/en/us/products/collateral/routers/asr-1000-series-aggregation-services-routers/data_sheet_c78-704277.html
NEW QUESTION 21
Which feature within Cisco Umbrella allows for the ability to inspect secure HTTP traffic?
- A. File Analysis
- B. SafeSearch
- C. SSL Decryption
- D. Destination Lists
Answer: C
NEW QUESTION 22
......
Thanks for reading the newest 350-701 exam dumps! We recommend you to try the PREMIUM Certstest 350-701 dumps in VCE and PDF here: https://www.certstest.com/dumps/350-701/ (102 Q&As Dumps)