Practical 352-001 Vce 2021
Master the 352-001 CCDE Written Exam content and be ready for exam day success quickly with this Examcollection 352-001 braindumps. We guarantee it!We make it a reality and give you real 352-001 questions in our Cisco 352-001 braindumps.Latest 100% VALID Cisco 352-001 Exam Questions Dumps at below page. You can use our Cisco 352-001 braindumps and pass your exam.
Online Cisco 352-001 free dumps demo Below:
NEW QUESTION 1
An enterprise campus is adopting a network virtualization design solution with these requirements
It must include the ability to virtualize the data plane and control plane by using VLANs and VRFs It must maintain end-to-end logical path transport separation across the network
resources available grouped at the access edge
Which two primary models can this network virtualization design be categorized? (Choose two)
- A. Path isolation
- B. Session isolation
- C. Group virtualization
- D. Services virtualization
- E. Edge isolation
Answer: AD
NEW QUESTION 2
Which main IoT migration aspect should be reviewed for a manufacturing plant?
- A. Sensors
- B. Security
- C. Applications
- D. Wi-Fi Infrastructure
- E. Ethernet Switches
Answer: A
NEW QUESTION 3
DRAG DROP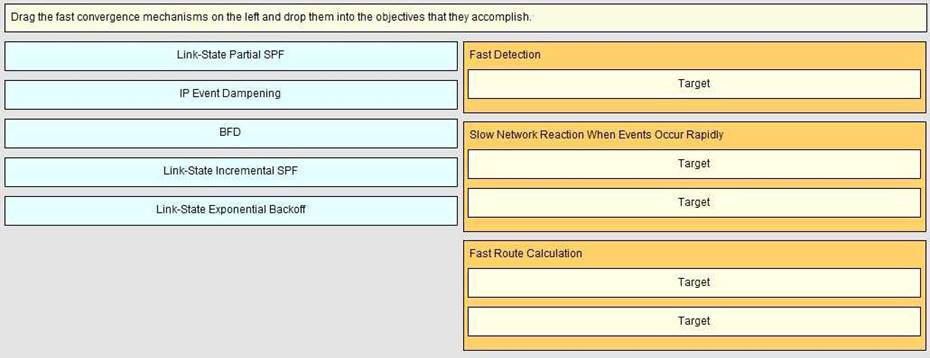
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 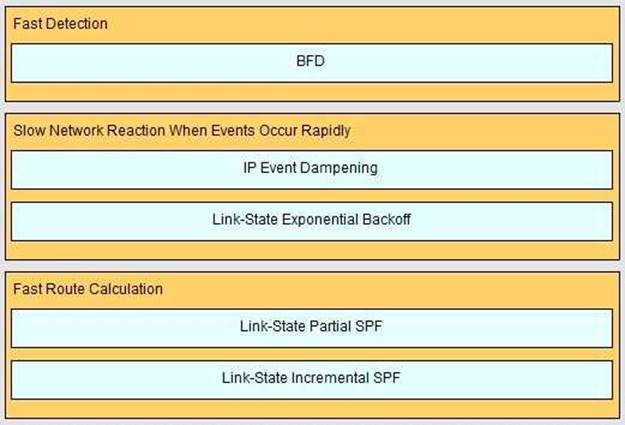
NEW QUESTION 4
Which mechanism does OSPF use to prevent loops in an MPLS Layer 3 VPNS environment?
- A. Sham link
- B. Down bit
- C. P-Bit
- D. Domain ID
- E. Routing bit
Answer: B
NEW QUESTION 5
A service provider must provide Internet connectivity to an MPLS Layer 3 VPN customer. Which
solution allows this customer to have Internet access?
- A. Implement a global default route with a next hop in the VRF late on PE
- B. Implement policy-based routing between PE and CE
- C. Implement a default route in the VRF with a next hop in the global routing table of PE
- D. Implement destination NAT between the VRF and the global RIB of PE
Answer: C
NEW QUESTION 6
DRAG DROP
Drag and drop the technology details or features support on the left into the corresponding Layer 2 multipath technologies on the right. Not all options will be used.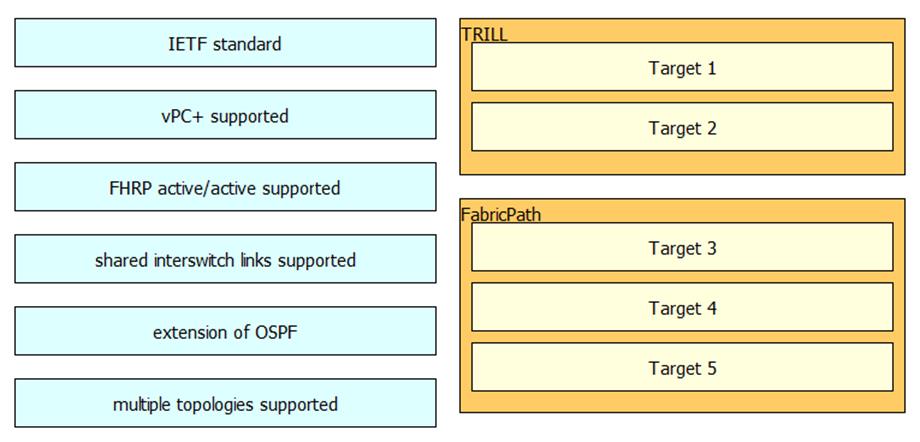
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 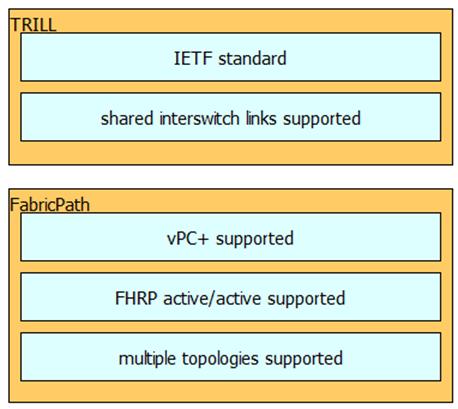
NEW QUESTION 7
Which open source message broker is in the Cisco Cloud Center?
- A. Apache kafka
- B. HornetQ
- C. RabbitMQ
- D. Fuse Message Broker
- E. Oracle Message Broker
Answer: C
NEW QUESTION 8
Which two statements about VXLAN are true? (Choose two)
- A. VXLAN is a Cisco proprietary solution
- B. VXLAN is an encapsulation method used to create a Layer 3 overlay network
- C. VXLAN can be used to enforce Layer 2 isolation in a multitenant infrastructure
- D. VXLAN uses the Spanning Tree protocol for loop prevention
- E. VXLAN overcomes the 802.1Q virtual LAN address space limitation
Answer: BE
NEW QUESTION 9
VPLS is implemented in a Layer 2 network with 2000 VLANs. Which must be the primary concern to
ensure successful deployment of VPLS?
- A. The underlying transport mechanism
- B. PE scalability
- C. Flooding is necessary to propagate MAC address reachability information
- D. VLAN scalability
Answer: C
Explanation:
[ I think B not 100% sure]
NEW QUESTION 10
You are presented with requirements to design a development, testing and production environments. These environment should communicate with each other, yet they should be kept as separate failure domains. Which routing protocol should be configured on the links between the networks to support the design requirements?
- A. OSPF
- B. EIGRP
- C. IS-IS
- D. BGP
Answer: D
NEW QUESTION 11
You are solving a design failure on a massive Hadoop cluster network that has an application with TCP incast behavior (also known as TCP Throughput collapse) affecting its many-to-one communications with packet loss at the last-hop network device. Which metric must be measured to ensure that the network provides the best performance for this application?
- A. Availability
- B. Bandwidth utilization
- C. Jitter values
- D. Buffer utilization
Answer: D
NEW QUESTION 12
Which IEEE standard is commonly used at the data link layer for an access network, in an IoT environment?
- A. Wireless Regional Area Network
- B. Low-Rate Wireless Network
- C. Wireless Local Area Network
- D. Broadband wireless metropolitan Network
Answer: B
NEW QUESTION 13
Which four resources does Cisco Cloud Center provision in an ACL environment? (Choose four)
- A. VLAN Pool
- B. Contracts
- C. End point Group (EPG)
- D. VRF
- E. Subject/Filters
- F. Application Network Profile (ANP)
Answer: BCEF
NEW QUESTION 14
Which option describes the fundamental design differences between an IP-based network design
and a SAN-based?
- A. An IP-based design has redundant connectivity in the fabric and high amounts of east-west traffic, whereas a SAN-based design uses redundancy from a dual-attached host, which uses separate fabrics and has very little east-west traffic
- B. An IP-based design has redundancy from the host and high amounts of east-west traffic, whereas a SAN-based design uses redundancy in the fabric and very little east-west traffic
- C. An IP-based design has redundant connectivity in the fabric and high amounts of east-west traffic, whereas a SAN-based design uses zoning based redundancy which uses separate fabrics and has very little east-west traffic
- D. An IP-based design has redundant connectivity in the fabric and very little east-west traffic, whereas a SAN-based design uses redundancy in the host, which uses separate fabrics and has high amounts of east-west traffic
Answer: A
NEW QUESTION 15
Refer to the Exhibit.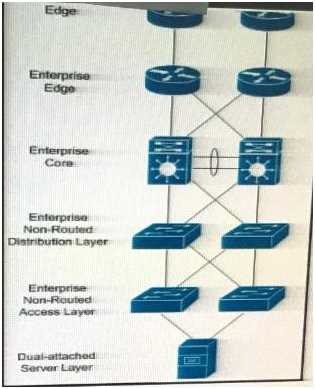
In which three Layers should you use nonstop Forwarding to reduce service impact in case of failure? (Choose three)
- A. Enterprise Edge
- B. Enterprise Core
- C. Service provider Edge
- D. Dual-attached sever Layer
- E. Enterprise Non-Routed Access Layer
- F. Enterprise Non-Routed Distribution Layer.
Answer: ABC
NEW QUESTION 16
Refer to the exhibit.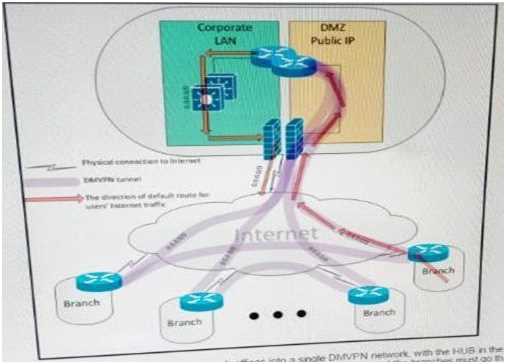
A customer interconnected hundreds of branch offices into a single DMVPN network, with the HUB
in the main data center. Due to security policies, the customer requires that the default route for all Internet traffic from the users at the branches must go through the tunnel and the only connections that are allowed to and from the branch router over the local internet circuit are the DMVPN tunnels. Which two combined actions must you take on the branch router to address these security requirements and keep the solution scalable? (Choose two)
- A. Place the WAN interface in a front-door VRF, leaving the tunnel interface in the default routing instance
- B. Protect the WAN interface by an inbound ACL that permits only IPsec-related traffic
- C. Implement a zone-based firewall that allows only IPsec-related traffic from zone UNTRUSTED to zone TRUSTED
- D. Add a host route for the public IP address of each remote branch and HUB routers that points directly to the local ISP, and add a default route that points to the tunnel
- E. Use a floating default route with the preferred path over the tunnel and a backup path over the Internet natively
Answer: AB
NEW QUESTION 17
Your customer asked you to redesign there is-IS network to reduce to a minimum the number of
adjacencies because the network has several routers running L1/L2 mode on the sme Ethernet segment. Which action do you recommend?
- A. Define only one router on the segment to be DIS
- B. Make the interface priority on the backup DIS lower than the primary DIS
- C. Change half the routers to L1 routers and half to L2 routers
- D. Change all routers to a single-level area
Answer: D
NEW QUESTION 18
A large ISP is analysing which IGP meets these following requirements Network must be resilient against unstable MTU in one side of newly released transmission pieces of equipment Network must support MPLS traffic engineering solution for future use Which IGP must be selected and why?
- A. ISIS : in case MTU changes your TE tunnels keep the LSP stable
- B. OSPF: adjacency remains up even if MTU changes
- C. OSPF: in case MTU changes your TE tunnels keep the LSP stable
- D. ISIS: adjacency remains up even if MTU changes
Answer: D
NEW QUESTION 19
Company ABC is using an Ethernet virtual circuit as its provider’s DCI solution. A goal is to reduce the
time to detect the link failure. Which protocol accomplishes this goal?
- A. UDLD
- B. Spanning tree bridge assurance
- C. Link aggregation group
- D. Ethernet OAM
Answer: D
NEW QUESTION 20
In a design around fast convergence in case of a link failure, what is the justification for using a point-
to-point OSPF network type on the Ethernet links between leaf-and-spine switches on a data center fabric?
- A. Link failure tears down neighbor relationships regardless of network type configured
- B. Type 1 LSAs are not generated on a point-to-point network type
- C. Adjacencies can be built faster without a DR/BDR on the segment
- D. The fabric memory requirements are significantly smaller than with a DR/BDR on each leaf and spine segment
- E. The point-to-point network type allows for NSF to be used in this design
Answer: C
NEW QUESTION 21
A switched network is being designed to support a manufacturing factory. Due to cost constraints,
fiber-based connectivity is not an option. Which design allows for a stable network when there is a risk of interference from the manufacturing hardware in use on the factory floor?
- A. Design the network to include UDLD to detect unidirectional links and take them out of service.
- B. Design the network to include Ether Channel bundles to prevent a single-link failure from taking down a switch interconnection point.
- C. Design the network to include loop guard to prevent a loop in the switched network when a link has too much interference.
- D. Design the network to include Backbone Fast on all devices to accelerate failure convergence times.
Answer: B
NEW QUESTION 22
Which solution prevents microloops from be formed during network convergence time?
- A. RSVP-TE
- B. LFA
- C. Prefix suppression
- D. RLFA
Answer: D
NEW QUESTION 23
Which two options are Loop-Free Alternate design considerations? (Choose two)
- A. MPLS TE must be enabled because it is used for building the backup paths
- B. Backup coverage and effectiveness is dependent on the network topology
- C. It can simplify the capacity planning by matching the backup path with the post-convergence path
- D. It provides an optional backup path by avoiding low bandwidth and edge links
- E. It can impact SLA-sensitive appliance by routing traffic to low bandwidth links while IGP convergence is in progress
Answer: BE
NEW QUESTION 24
Which are two open-source SDN controllers? (Choose two)
- A. Big Cloud Fabric
- B. OpenContrail
- C. Application Policy Infrastructure Controller
- D. Virtual Application Networks SDN controller
- E. OpenDaylight
Answer: BE
NEW QUESTION 25
What is an advantage of placing the IS-IS flooding domain boundary at the core Layer in a three-layer
hierarchical network?
- A. The L1 and L2 domains can easily overlap
- B. The L2 domain is contained and more stable
- C. It can be applied to any kind of topology
- D. It reduces the complexity of the L1 domains
Answer: A
NEW QUESTION 26
What is design considerations of policy-based routing?
- A. It decreases failure detection time
- B. It can create microloops during network reconvergence
- C. It routes traffic destined to a set of users through different exit points
- D. It uses RSVP to differentiate traffic flows, so queuing mechanisms can prioritize them
Answer: B
NEW QUESTION 27
Which two options are reasons for designing a large OSPF network with multiple areas connected to
the backbone? (Choose two)
- A. Reduce the number of routes within an area
- B. Route tagging capability
- C. Simplify logical topology
- D. Enhance failure detection
- E. Reduce SPF algorithm runs
Answer: AE
NEW QUESTION 28
When you design a network that uses IPsec, where can you reduce MTU to avoid network
fragmentation?
- A. on both ends of the TCP connection
- B. on the side closest to the client
- C. on the side closest to the server
- D. in the WAN
Answer: A
NEW QUESTION 29
......
Thanks for reading the newest 352-001 exam dumps! We recommend you to try the PREMIUM prep-labs.com 352-001 dumps in VCE and PDF here: https://www.prep-labs.com/dumps/352-001/ (249 Q&As Dumps)