Avant-garde 400-251 Discount Pack 2021
Act now and download your Cisco 400-251 test today! Do not waste time for the worthless Cisco 400-251 tutorials. Download Update Cisco CCIE Security Written Exam exam with real questions and answers and begin to learn Cisco 400-251 with a classic professional.
Online 400-251 free questions and answers of New Version:
NEW QUESTION 1
Which two statements about application protocol detectors in the Cisco Fire? (Choose two)
- A. They can analyze network traffic for specific application fingerprints
- B. Port-based application protocol detectors can be modified for use as custom
- C. Port-based and Firepower-based application protocol detectors can be import
- D. firepower-based application protocol detectors are built in to the Firepower deactivated only by the system
- E. They can be activated by VDB updates, but must be deactivated manually
- F. They can detect web-based application activity in HTTP traffic
Answer: BE
NEW QUESTION 2
Which statement about the Sender Base functionality is true?
- A. SenderBase uses DNS-based blacklist as one of the sources of information to define reputation score of sender's IP address
- B. SenderBase uses spam complaints as one of the sources of information to define reputation score of receiver's IP address of the sender and receiver
- C. ESA uses destination address reputation information from SenderBase to configure mail policies.
- D. ESA sees a high positive score from SenderBase as very likely that sender is sending spam
- E. ESA sees a high negative score from SenderBase as very unlikely that sender is sending spam
- F. ESA uses source address reputation information from SenderBase to stop spam
- G. WSA uses SenderBase information to configure URL filtering policies
Answer: A
NEW QUESTION 3
Which action must happen before you enroll a device to a mobile device management service fro a different vendor?
- A. wipe the entire device and start from scratch
- B. Allow both vendor profiles remain on the device.
- C. Remove the profiles form the previous vendor from the device
- D. Alter the administrator so that they can remove this device form the network
Answer: C
NEW QUESTION 4
A customer is developing a strategy to deal with Wanna Cry variants that defect sandboxing attempts and mask their present analyzed. Which four mechanisms can be used in this strategy?
- A. Employ a DNS forwarder that responds to unknown domain names with a reachable IP (honey pot) that can mimic sandboxing containment responses and alert when a possible threat is detected.
- B. Apply route maps at the access layer that prevent all RPC and SMB communication throughout the network.
- C. Ensure that the standard desktop image used in the organization is an actively supported operating system and that security patches are applied.
- D. Run antimalware software on user endpoints and servers as well as ensure regular signature updates.
- E. Ensure that vulnerable services used for propagation of malware such as SMB are blocked on publicfacing segments.
- F. Employ URL/DNS inspection mechanisms that blackhole the reques
- G. This action prevents malware from communicating with unknown domains and thus prevents the WannaCry malware from becoming active.
- H. Apply ACLs at the access layer that prevents all RPC and SMP communication throughout the network..
Answer: DEFG
NEW QUESTION 5
Which authentication does WCCPv2 use to protect messages against Interception, inspection, and replay attacks?
- A. Clear text
- B. Two factor
- C. EAP
- D. MD5
- E. Kerberos
Answer: D
NEW QUESTION 6
Which three ESMTP extensions are supported by the Cisco ASA?Choose three
- A. NOOP
- B. PIPELINING
- C. SAML
- D. 8BITMIME
- E. STARTTLS
- F. ATRN
Answer: ACE
NEW QUESTION 7
Which two characteristics of DTLS are true? (Choose two.)
- A. It supports long data transfers and connectionless data transfers.
- B. It includes a retransmission method because it uses an unreliable datagram transport.
- C. It includes a congestion control mechanism.
- D. It is used mostly by applications that use application layer object-security protocols.
- E. It completes key negotiation and bulk data transfer over a single channel.
- F. It cannot be used if NAT exists along the path.
Answer: BC
NEW QUESTION 8
The SAML Single Sign-on ISE is supported by which four portals? (Choose four.)
- A. Sponsor Portal
- B. BYOD Portal
- C. Employee Portal
- D. Contractor Portal
- E. Guest Portal (sponsored and self-registered)
- F. My devices Portal
- G. Wireless Client Portal
- H. Certificate Provisioning Portal
Answer: AEFH
NEW QUESTION 9
Which two statements about 6to4 tunneling are true? (Choose two.)
- A. It provides a /128 address block.
- B. It supports static and BGPV4 routing.
- C. It provides a /48 address block.
- D. It supports managed NAT along the path of the tunnel.
- E. The prefix address of the tunnel is determined by the IPv6 configuration of the interface.
- F. It supports multihoming.
Answer: BC
NEW QUESTION 10
Which statement regarding the routing functions of the Cisco ASA is true running software version 9.2?
- A. The translation table cannot override the routing table for new connections.
- B. Routes to the NuLL0 interface cannot be configured to black-hole traffic.
- C. In a failover pair of ASAs, the standby firewall establishes a peer relationship with OSPF neighbors.
- D. The ASA supports policy-based routing with route maps.
Answer: A
NEW QUESTION 11
Which two protocols are supported when using TACACS+? (Choose two)
- A. MS-CHAP
- B. CHAP
- C. NASI
- D. HDLC
- E. AppleTalk
Answer: CE
NEW QUESTION 12
Drag and drop the protocols on the left onto their descriptions on the right.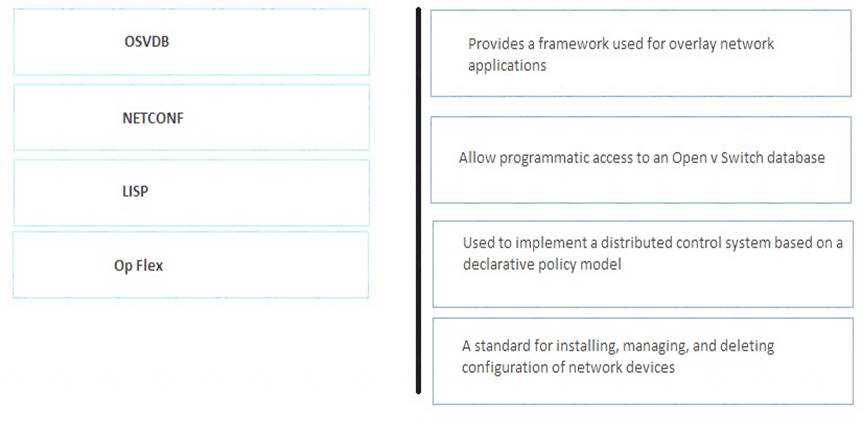
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
1-2, 2-4, 3-1, 4-3
NEW QUESTION 13
Which statement about ASA clustering requirements is true?
- A. Only routed mode is allowed in the single context mode
- B. Units in the cluster can be running different software version as long as they have identical hardware configuration
- C. Units in the cluster can have different hardware configuration as long as they are running same software version
- D. Units in the cluster can be in different geographical locations
- E. Units in the cluster can be in different security context modes
- F. Units in the cluster cannot have different software version even though they have identical hardware configuration.
Answer: F
NEW QUESTION 14
Which three statements about the SHA-2 algorithm are true? (Choose three.)
- A. It provides a fixed-length output using a collision-resistant cryptographic hash.
- B. It provides a variable-length output using a collision-resistant cryptographic hash.
- C. It generates a 512-bit message digest.
- D. It generates a 160-bit message digest.
- E. It is used for integrity verification
- F. It is the collective term for the SHA-224, SHA-256, SHA-384, and SHA-512 algorithms.
Answer: AEF
NEW QUESTION 15
Which of the following is used by WSA to extract session information from ISE and use that in access policies?
- A. RPC
- B. pxGrid
- C. SXP
- D. Proprietary protocol over TCP/8302
- E. EAP
- F. RADIUS
Answer: B
NEW QUESTION 16
Which two options are important considerations when you use NetFlow to obtain the full picture of network taffic? (Choose two)
- A. It monitors only TCP connections.
- B. It monitors only routed traffic.
- C. It monitors all traffic on the interface on which it is deployed.
- D. It monitors only ingress traffic on the interface on which it is deployed.
- E. It is unable to monitor over time.
Answer: BE
NEW QUESTION 17
Which two combinations of node are allowed in a Cisco ISE distributed deployment? (Choose two)
- A. ISE cluster with eight nodes
- B. Pair of passive ISE nodes for automatic failover
- C. One or more policy service ISE nodes for session failover standalone
- D. Primary and secondary administration ISE nodes for high availability
- E. Active and standby ISE notes for high availibilty
Answer: BD
NEW QUESTION 18
Which statement is true about Remote Triggered Black Hole Filtering feature (RTBH)?
- A. It drops malicious traffic at the customer edge router by forwarding it to a Null0 interface
- B. In RTBH filtering the trigger device redistributes static route to the iBGP peers
- C. The Null0 interface used for filtering is able to receive the traffic, but never forwards it
- D. It works in conjunction with QoS to drop the traffic that has less priority
- E. It helps mitigate DDoS attack based only on source address
- F. In FTBH filtering the trigger device is always an ISP edge router
Answer: B
NEW QUESTION 19
Drag and drop the Fire AMP Connector Policy types from the left on to the correct functions on the right.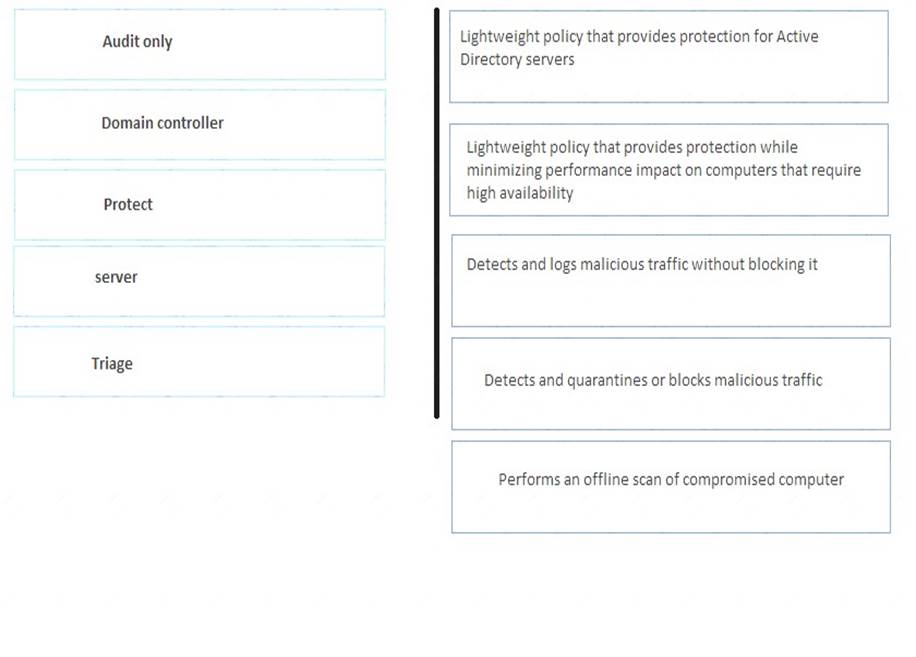
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
1-3, 2-1, 3-4, 4-2, 5-5
NEW QUESTION 20
Which three statements about 802.1x multiauthentication mode are true? (Choose three.)
- A. It is recommended for guest VLANs.
- B. On non-802.1x devices, it can support only one authentication method on a single port.
- C. Each multiauthentication port can support only one voice VLAN.
- D. It is recommended for auth-fall VLANs.
- E. It requires each connected client to authenticate individually.
- F. It can be deployed in conjunction with MDA functionality on voice VLANs.
Answer: CEF
NEW QUESTION 21
In a Cisco ISR with cloud Web Security Connector deployment, which command can you enter on the Cisco ISR G2 to verify connectivity to the CWS tower?
- A. Show policy-map
- B. Show service-policy
- C. Show ip nbar
- D. Show sw-module
- E. Mtrace
- F. Show content-scan summary
Answer: A
NEW QUESTION 22
Refer to the exhibit.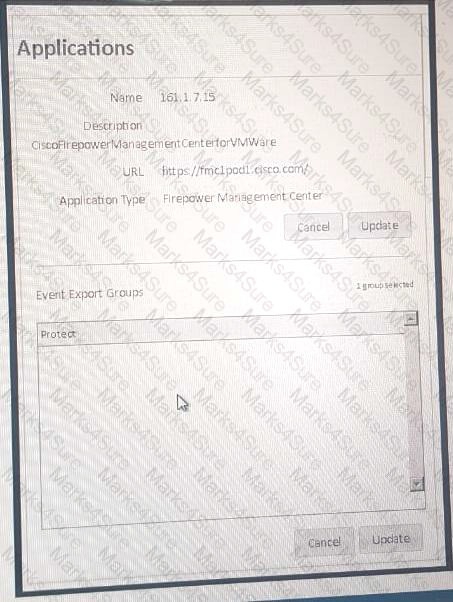
The AMP cloud is configured to report AMP Connector scan events from Windows machines that belong to the Audit group to the FMC However, the scanned events are not showing up in the PMC. Which possible cause is true?
- A. There is a possible issue with certificate download from the AMP cloud for FMC integration.
- B. The AMP cloud «s pointing to an incorrect FMC address.
- C. The event must be viewed as a malware event in the f MC.
- D. The DNS address is misconfigured on the FMC.
- E. An incorrect group is selected for the events export in the AMP cloud for FMC.
- F. The FMC is pointing to an incorrect AMP cloud address.
Answer: CE
NEW QUESTION 23
Which four task items need to be performed for an effective nsk assessment and to envaluate network posture? (Choose four.)
- A. discovery
- B. baselining
- C. scanning
- D. notification
- E. validation
- F. escalation
- G. mitigation
- H. profiling
Answer: ACEH
NEW QUESTION 24
Which two statements about MAB are true? (Choose two)
- A. It requires the administrator to create and maintain an accurate database of MAC addresses.
- B. It server at the primary authentication mechanism when deployed in conjunction with 802.1x.
- C. It operates at Layer 2 and Layer 3 of the OSI protocol stack.
- D. It can be used to authenticate network devices and users.
- E. MAC addresses stored in the MAB database can be spoofed.
- F. It is a strong authentication method.
Answer: AE
NEW QUESTION 25
Which statement is an advantage of network segmentation?
- A. It enables efficient network monitoring due to a flat network
- B. It takes less time to design a complex network with segmentation as one of the critical requirements
- C. It allows flat network design for better security implementation
- D. It allows efficient containment of a security incident as the effect will be limited to local subnet
- E. It improves network performance by having broadcast traffic not limited to local subnets
- F. It allows users to access the resource even though they won't need to for better visibility
Answer: D
NEW QUESTION 26
Which statement about x.509 certificates is true?
- A. The version number in the certificate is the OS version of the CA.
- B. The Subject distinguished name in the certificate is of the entity who issued the certificate
- C. The algorithm in the certificate is used by the subiect to encrypt the traffic
- D. The serial number in the certificate is common across the certificates issued by the same CA
- E. The algorithm in the certificate is used by the receiver to sign the certificate
- F. The Issuer distinguished name in the certificate is of the entity issuing the certificate
Answer: F
NEW QUESTION 27
......
Recommend!! Get the Full 400-251 dumps in VCE and PDF From 2passeasy, Welcome to Download: https://www.2passeasy.com/dumps/400-251/ (New 448 Q&As Version)