How Many Questions Of C9510-401 Free Question
we provide Verified IBM C9510-401 exam answers which are the best for clearing C9510-401 test, and to get certified by IBM IBM WebSphere Application Server Network Deployment V8.5.5 and Liberty Profile, System Administration. The C9510-401 Questions & Answers covers all the knowledge points of the real C9510-401 exam. Crack your IBM C9510-401 Exam with latest dumps, guaranteed!
Free demo questions for IBM C9510-401 Exam Dumps Below:
NEW QUESTION 1
An EJB application posts a request message into a JMS destination and waits for a response message on a different JMS destination. To correlate the response message to the request message, the application uses the JMS correlationId of the message. The application waits up to five seconds for a response before timing out the request.
A Message Driven Bean (MDB) running on a different cluster is responsible for consuming the request message, process it and post a response message.
The destinations are defined in a Service Integration Bus (SIB) within the cell.
Intermittent timeout exceptions have occurred for the requester application. How can a system administrator correlate and analyze the debug information from both requester and consumer applications?
- A. Enable High Performance Extensible Logging (HPEL).Use HPEL logViewer command to see debug information.
- B. Enable a diagnostic trace in both requester and consumer servers.Use the Integrated Solutions Console (ISC) to set the admin=all trace.Analyze the trace.
- C. Enable High Performance Extensible Logging (HPEL).Enable Cross Component Trace (XCT) to include request IDs in log and trace records.Use HPEL logViewer command with appropriate filters to see debug information.
- D. Using the Integrated Solutions Console (ISC), browse the request message that has timed out and look for any key application data.Search for exceptions using the key application data in both requester and consumer in native_stderr.log and native_stdout.log.
Answer: C
Explanation:
Cross Component Trace (XCT) annotates the logs so that log entries that are related to a request that is serviced by more than one thread, process, or even server are identified as
belonging to the same unit of work. XCT helps identify the root cause of problems across components.
References: WebSphere Application Server V8.5 Administration and Configuration Guide for the Full Profile (July 2013), page 1091
NEW QUESTION 2
A system administrator has deployed an application. The development team has updated a new version of this application. The administrator needs to immediately deploy this updated application and guarantee that only this new edition is used by clients and that any service requests for the application are queued during the deployment of the new application.
How can the administrator achieve this task without any downtime to the application?
- A. Perform a soft rollout.
- B. Perform a hard rollout.
- C. Perform an atomic rollout.
- D. Perform a concurrent activation rollout.
Answer: C
Explanation:
Performing an atomic rollout activates the new edition on half of the cluster first, and then activates the edition on the remaining half of the cluster. While the first half of the cluster is taken offline and updated, application requests are routed to the second half of the cluster. Verify that half the cluster can handle the entire load during the rollout period.
References: http://www.aiotestking.com/ibm/how-can-the-administrator-achieve-this-task-without-any-downtime-to-the-application/
NEW QUESTION 3
A system administrator is required to create a star topology for multi-cell performance management for three WebSphere Application Server cells.
How should the administrator configure the Application Placement Controller (APC) in a star topology?
Configure the cell custom property CenterCell to:
- A. false in all three WebSphere Application Server cells.
- B. false in one WebSphere Application Server celltrue in the other two WebSphere Application Server cells.
- C. true in all three WebSphere Application Server cells.
- D. true in one WebSphere Application Server cellfalse in the other two WebSphere Application Server cells.
Answer: D
NEW QUESTION 4
A system administrator runs a Python script that creates and configures several servers and realizes that the script fails before completing. Although many tasks succeeded, they are rolled back when the script fails.
Before running the script again, what can the administrator add to the script after each task so the completed tasks are committed even if other tasks fail?
- A. AdminApp.update ()
- B. AdminConfig.save()
- C. AdminControl.invoke(server, 'sync’)
- D. AdminTask.backupJobManager('server')
Answer: C
NEW QUESTION 5
A system administrator has created a Jython script that will run in WebSphere Network cell where administrative security is enabled. This script is named doUpdate.py and will be run by using the following:
wsadmin –connType RMI –f doUpdate.py
How can the administrator suppress a user/password prompt from appearing when this script is run?
Set the user and password in the:
- A. sas.client.props file.
- B. ssl.client.props file.
- C. soap.client.props file.
- D. wsadmin.properties file.
Answer: A
Explanation:
The user Id and password needed for wsadmin to connect to a secured server can be
supplied as command line options and in properties files. If used together, command line options take precedence over what is in the properties files. The properties files are located at Profile_root/properties.
If you use a Remote Method Invocation (RMI) connector or a JSR160RMI connector, set the following properties in the sas.client.props file with the appropriate values: com.ibm.CORBA.loginUserid=
com.ibm.CORBA.loginPassword=
References: https://www.ibm.com/support/knowledgecenter/SSAW57_8.5.5/com.ibm.websphere.nd.doc
/ae/txml_security.html
NEW QUESTION 6
A web application is hosted on an application server that receives HTTP requests from a third party application named myApp. The URIGroup mapping for this application is called default_host_myApp.
The development team asks a system administrator to configure the HTTP plug-in to prevent routing requests to any application server except server1.
The following exhibit shows the parts of the plugin-cfg.xml file that are relevant for myApp. The UriGroups for other applications are not shown in the exhibit.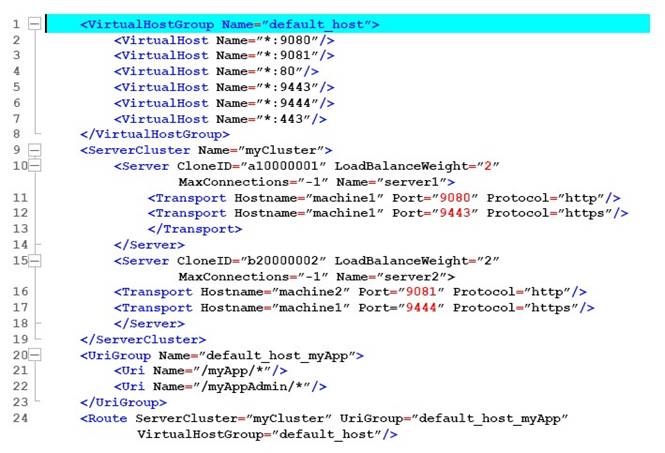
What should the administrator do to the plugin-cfg.xml file to ensure that requests for default_host_myApp URIGroup are routed only to machine1?
- A. Delete the Server tag for CloneId=”b20000002”Delete all of the tags within the Server tag
- B. Delete the UriGroup tag for default_host_myAppDelete all of the tags within the UriGroup tag
- C. Delete the VirtualHostGroup tag for default_hostDelete all of the tags within the VirtualHostGroup tag
- D. Edit the LoadBalanceWeight for server1 to 20Edit the LoadBalanceWeight for server2 to 2
Answer: A
NEW QUESTION 7
The application placement controller has been configured with elasticity mode enabled. Intermittently, all instances of a dynamic cluster are removed. After further review, the system administrator noticed that it occurs during peak load on another dynamic cluster.
The administrator wants to keep at least one instance available. Which configuration is needed in the dynamic clusters?
- A. Enable application lazy start with elasticity mode.
- B. Set the proactiveIdleStop custom property to true.
- C. Set the Number of instances to a value greater than zero.
- D. Disable the option “If other dynamic clusters need resources, stop all instances of this cluster during periods of inactivity”.
Answer: D
Explanation:
It is not recommended to enable elasticity mode when the following option is set in the administrative console for one or more dynamic clusters:
If other dynamic clusters need resources, stop all instances of this cluster during periods of inactivity.
If you have elasticity mode enabled and the option set, the application placement controller can remove all of the custom nodes in the cell.
References: https://www.ibm.com/support/knowledgecenter/en/SSAW57_8.5.5/com.ibm.websphere.nd. doc/ae/twve_cfgelastic.html
NEW QUESTION 8
An organization updated their LDAP directories and modified user roles. The roles that were configured to have access to a highly secured enterprise application were deleted and new roles with new names were created. The application then had security related exceptions.
How can a system administrator resolve the exceptions and restore security for the
application?
- A. Modify the mapping of security roles of the application to the new LDAP roles.
- B. Modify the application and remove all security constraints and redeploy the application.
- C. Modify the application to have a runAs role for each new LDAP role and redeploy the application.
- D. Create an administrative authorization group with administrator privileges scoped for the application with an administrative group role for the new LDAP roles.
Answer: A
NEW QUESTION 9
Which one of the following options describes the runtime flow starting from the client browser in a clustered WebSphere Application Server Network Deployment topology?
- A. HTTP server -> job manager -> admin agent -> HTTP server plug-in
- B. Load balancer -> HTTP server -> HTTP server plug-in -> application server
- C. Application server -> node agent -> deployment manager -> load balancer
- D. Deployment manager -> node agent -> HTTP server plug-in -> HTTP server
Answer: B
NEW QUESTION 10
A system administrator, Admin1, with Administrator privileges has archived full repository checkpoints. Another administrator, Configurator1, with Configurator privileges has copied the checkpoint contents directory from one of the archived check points to its original location. Configurator1 tries to restore the configuration using the copied archived checkpoint contents and the restore fails.
How can Configurator1 restore the configuration using the copied archived full repository checkpoint?
- A. Copy the archived checkpoint metadata directory to its original location.
- B. Increase the Automatic checkpoint depth to keep all the delta checkpoint.
- C. Delete the delta checkpoint taken after the full repository checkpoint was taken.
- D. Ask an administrator to update the privileges for Configurator1 to match Admin1.
Answer: A
Explanation:
You must archive both the checkpoint metadata and content directories to store a checkpoint for later restoration.
References: http://www- 01.ibm.com/support/knowledgecenter/SSD28V_8.5.5/com.ibm.websphere.nd.doc/ae/twve_archive_checkpoint.html
NEW QUESTION 11
A customer has enabled LTPA as their authentication mechanism and has web resources that are not secured by proper security constraints. A system administrator is required to ensure that all web resources are secured.
How should the administrator accomplish this?
- A. Enable “Authenticate when any URI is accessed”.
- B. Enable “Authenticate only when the URI is protected”.Disable “Use available authentication data when an unprotected URI is accessed”.
- C. Enable “Authenticate only when the URI is protected”.Enable “Use available authentication data when an unprotected URI is accessed”.
- D. Map the application security roles to the configured user registry’s groups.
Answer: A
Explanation:
Authenticate only when the URI is protected
The application server challenges the web client to provide authentication data when the web client accesses a Uniform Resource Identifier (URI) that is protected by a Java Platform, Enterprise Edition (Java EE) role. The authenticated identity is available only when the web client accesses a protected URI.
This option is the default Java EE web authentication behavior that is also available in previous releases of WebSphere® Application Server.
References: https://www.ibm.com/support/knowledgecenter/SSAW57_8.5.5/com.ibm.websphere.base.d oc/ae/usec_webauth.html
NEW QUESTION 12
A system administrator discovers an issue that requires a change to a federated server. In this cell, WebSphere administrative security is enabled, but application security is not enabled.
How should the administrator make this change? The administrator should use:
- A. a web browser to connect to the node agent https port.
- B. a web browser to connect to the deployment manager admin_host port.
- C. the job manager to submit a job to update the unmanaged server.
- D. an ssh connection to the node and modify the client_types.xml file.
Answer: B
Explanation:
The admin_host virtual host is used for access to the WebSphere administrative console. At installation time, the host is configured to match requests on the wc_adminhost and wc_adminhost_secure ports for the stand-alone server or deployment manager.
References: WebSphere Application Server V8.5 Administration and Configuration Guide for the Full Profile (July 2013), page 303
NEW QUESTION 13
A system administrator completed a WebSphere Application Server installation by using the Installation Manager. During installation, all defaults were selected for the installation root directories and the shared resources directory. Over time, the administrator has updated the installation with various interim fixes and fix packs. The administrator notices that the shared resources directory is very large in size and grows larger each time the Installation Manager is run.
How can the administrator decrease the size and remove some of the content from the shared resources directory?
- A. Manually delete content from the directory.
- B. During an update, create a new shared resources directory.
- C. Clear the Delete Saved Files option for the Installation Manager.
- D. Set the preserveDownloadedArtifacts preference to false.
Answer: D
Explanation:
Because product payloads are cached in this directory, space requirements can grow very large over the lifetime of the product, as service updates are applied. The WebSphere Application Server product image is large, so if this content is permitted to accumulate, then this directory will grow to be many gigabytes in size over the course of multiple fix pack applications. You should never manually delete the content in this folder. Instead, during any installation or maintenance operation, you can specify the following preference to remove some of the content in this folder:
–preferences com.ibm.cic.common.core.preferences.preserveDownloadedArtifacts=false
References: https://www.ibm.com/support/knowledgecenter/en/SSAW57_7.0.0/com.ibm.websphere.inst allation.soafepnd.doc/info/ae/ae/tins_installfp_dist.html
NEW QUESTION 14
A web application has a configured session timeout of eight hours and a default LTPA token timeout of two hours. After every two hours, the users have to log in again from their HTTP browser. The system administrator is required to make configuration changed so users only have to log in once, while keeping the above mentioned timeouts the same. The authentication mechanism available is Kerberos.
How should the administrator do this?
- A. Configure the SIP digest authentication.
- B. Configure the SPNEGO Web or SPNEGO TAI.
- C. Enable Session Management Security Integration.
- D. Ensure Web Inbound security attribute propagation is enabled.
Answer: B
Explanation:
In WebSphere Application Server Version 6.1, a trust association interceptor (TAI) that uses the Simple and Protected GSS-API Negotiation Mechanism (SPNEGO) to securely
negotiate and authenticate HTTP requests for secured resources was introduced. This function was deprecated In WebSphere Application Server 7.0. SPNEGO web authentication has taken its place to provide dynamic reload of the SPNEGO filters and to enable fallback to the application login method.
References: https://www.ibm.com/support/knowledgecenter/en/SSAW57_8.5.5/com.ibm.websphere.nd. doc/ae/csec_ssovo.html
NEW QUESTION 15
The administrator needs to identify any security role references and security constraints in a web application.
How can the administrator identify these roles and constraints?
- A. ibm-application-ext.xml file using a text editor.
- B. ibmconfig folder in the application after using the EARExpander command.
- C. Web deployment descriptor using IBM Assembly and Deploy Tools.
- D. Security role to user/group mapping by using the Integrated Solutions Console (ISC).
Answer: C
Explanation:
Securing web applications using an assembly tool.
You can use three types of web login authentication mechanisms to configure a web application: basic authentication, form-based authentication and client certificate-based authentication. Protect web resources in a web application by assigning security roles to those resources.
References: https://www.ibm.com/support/knowledgecenter/SS7JFU_8.5.5/com.ibm.websphere.nd.doc/ ae/tsec_secweb_atk.html
NEW QUESTION 16
A system administrator needs to view the list of certificates for unmanaged web server located on a remote system.
How should the administrator do this?
- A. View the plugin-cfg.xml
- B. Look at the SSL configuration in the httpd.conf
- C. Use iKeyman to view the keyring.
- D. Use the administrative console to check the content of the cell default keystore.
Answer: C
Explanation:
You do not have a secure network connection until you have created a key for secure network communications and received a certificate from a certificate authority (CA) who is designated as a trusted CA on your server. Use IKEYMAN to create the key database file, public-private key pair, and certificate request. After you receive the CA-signed certificate, use IKEYMAN to receive the certificate into the key database where you created the original certificate request.
References: http://www- 01.ibm.com/software/webservers/httpservers/doc/v10/ibm/9atikeyu.htm
NEW QUESTION 17
A performance test team was testing the capacity of concurrent users of a web application deployed on a multi-processor server. While testing 250 concurrent users, the administrator discovers connections to the database are failing.
In response, a system administrator increased the connection pool to the maximum limit which the database allows and increased the prepared statement cache size. The test passed, but the application response time was slower.
How should the system administrator tune the data source properties to improve the application response time?
- A. Change connection pools purge policy.
- B. Decrease connection pool reap time.
- C. Decrease number of free pool partitions.
- D. Decrease the prepared statement cache size.
Answer: D
Explanation:
The higher the statement cache, the more system resources are delayed. Therefore, if you set the number too high, you might lack resources because your system cannot open multiple prepared statements.
References: http://www.ibm.com/support/knowledgecenter/en/SSAW57_8.5.5/com.ibm.websphere.nd.d oc/ae/udat_jdbcdatasorprops.html
NEW QUESTION 18
A system administrator has configured a network deployment cell containing multiple nodes and global security enabled with an LDAP repository. To increase capacity, the administrator needs to add additional nodes to the cell. After adding the nodes by using both scripts and the Integrated Solutions Console (ISC), the administrator examines the System.out log for the deployment manager and notices the following message: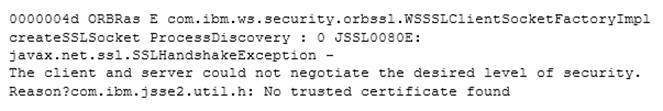
How can the administrator resolve this problem?
- A. Disable Java 2 security.
- B. Restart the deployment manager.
- C. Increase the RSA token timeout value.
- D. Change the number of active LTPA keys.
Answer: B
Explanation:
When nodes are added while LDAP security is enabled, the following exception is generated in the deployment manager System.out log under certain circumstances. If this happens, restart the deployment manager to resolve the problem.
0000004d ORBRas E com.ibm.ws.security.orbssl.WSSSLClientSocketFactoryImpl createSSLSocket ProcessDiscovery : 0 JSSL0080E: javax.net.ssl.SSLHandshakeException -
The client and server could not negotiate the desired level of security. Reason?com.ibm.jsse2.util.h: No trusted certificate found
References: https://www.ibm.com/support/knowledgecenter/en/SSAW57_8.0.0/com.ibm.websphere.nd. doc/info/ae/ae/tagt_svr_conf_nodes.html
NEW QUESTION 19
The installation of WebSphere Application Server did not complete successfully, and a system administrator needs to troubleshoot the installation.
What can the administrator do to identify the cause of the installation failure?
- A. Run the installver command with the appropriate command line options.
- B. Check the files under the Agent data location of IBM Installation Manager.
- C. Check the files under the logs directory of IBM Installation Manager installation directory.
- D. Check the log.txt under <WebSphere Application Server install directory><logdirectory>.
Answer: C
Explanation:
Installation Manager creates log files that you can use to troubleshoot any installation problems. Consider verifying the log files after any installation to ensure that everything in that process went successfully.
To examine the logs manually, locate the Installation Manager logs directory. The default location for this directory varies according to the operating system:
Windows: C:\ProgramData\IBM\Installation Manager\logs UNIX: /var/ibm/InstallationManager/logs
NEW QUESTION 20
A system administrator has created a Python script that will run in WebSphere Network cell where administrative security is enabled. This script is named doUpdate.py and will be run by using the following:
wsadmin -connType RMI -f doUpdate.py
How can the administrator suppress a user/password prompt from appearing when this script is run?
Set the user and password in the:
- A. sas.client.props file.
- B. ssl.client.props file.
- C. soap.client.props file.
- D. wsadmin.properties file.
Answer: D
NEW QUESTION 21
......
Recommend!! Get the Full C9510-401 dumps in VCE and PDF From Surepassexam, Welcome to Download: https://www.surepassexam.com/C9510-401-exam-dumps.html (New 73 Q&As Version)