Breathing CAS-002 Braindumps 2021
Exam Code: CAS-002 (), Exam Name: CompTIA Advanced Security Practitioner (CASP), Certification Provider: CompTIA Certifitcation, Free Today! Guaranteed Training- Pass CAS-002 Exam.
Free CAS-002 Demo Online For Microsoft Certifitcation:
NEW QUESTION 1
CORRECT TEXT
An administrator wants to install a patch to an application. Given the scenario, download, verify and install the patch in the most secure manner. Instructions The last install that is completed will be the final submission
Answer:
NEW QUESTION 2
A security administrator is tasked with implementing two-factor authentication for the company VPN. The VPN is currently configured to authenticate VPN users against a backend RADIUS server. New company policies require a second factor of authentication, and the Information Security Officer has selected PKI as the second factor. Which of the following should the security administrator configure and implement on the VPN concentrator to implement the second factor and ensure that no error messages are displayed to the user during the VPN connection? (Select TWO).
- A. The user’s certificate private key must be installed on the VPN concentrator.
- B. The CA’s certificate private key must be installed on the VPN concentrator.
- C. The user certificate private key must be signed by the CA.
- D. The VPN concentrator’s certificate private key must be signed by the CA and installed on the VPN concentrator.
- E. The VPN concentrator’s certificate private key must be installed on the VPN concentrator.
- F. The CA’s certificate public key must be installed on the VPN concentrator.
Answer: EF
NEW QUESTION 3
The sales team is considering the deployment of a new CRM solution within the enterprise. The IT and Security teams are members of the project; however, neither team has expertise or experience with the proposed system. Which of the following activities should be performed FIRST?
- A. Visit a company who already has the technology, sign an NDA, and read their latest risk assessment.
- B. Contact the top vendor, assign IT and Security to work together to implement a demo and pen test the system.
- C. Work with Finance to do a second ROI calculation before continuing further with the project.
- D. Research the market, select the top vendors and solicit RFPs from those vendors.
Answer: D
NEW QUESTION 4
Which of the following technologies prevents an unauthorized HBA from viewing iSCSI target information?
- A. Deduplication
- B. Data snapshots
- C. LUN masking
- D. Storage multipaths
Answer: C
NEW QUESTION 5
A popular commercial virtualization platform allows for the creation of virtual hardware. To virtual machines, this virtual hardware is indistinguishable from real hardware. By implementing virtualized TPMs, which of the following trusted system concepts can be implemented?
- A. Software-based root of trust
- B. Continuous chain of trust
- C. Chain of trust with a hardware root of trust
- D. Software-based trust anchor with no root of trust
Answer: C
NEW QUESTION 6
A security engineer is a new member to a configuration board at the request of management. The company has two new major IT projects starting this year and wants to plan security into the application deployment. The board is primarily concerned with the applications’ compliance with federal assessment and authorization standards. The security engineer asks for a timeline to determine when a security assessment of both applications should occur and does not attend subsequent configuration board meetings. If the security engineer is only going to perform a security assessment, which of the following steps in system authorization has the security engineer omitted?
- A. Establish the security control baseline
- B. Build the application according to software development security standards
- C. Review the results of user acceptance testing
- D. Consult with the stakeholders to determine which standards can be omitted
Answer: A
NEW QUESTION 7
The Chief Information Security Officer (CISO) regularly receives reports of a single department repeatedly violating the corporate security policy. The head of the department in question informs the CISO that the offending behaviors are a result of necessary business activities. The CISO assigns a junior security administrator to solve the issue. Which of the following is the BEST course of action for the junior security administrator to take?
- A. Work with the department head to find an acceptable way to change the business needs so the department no longer violates the corporate security policy.
- B. Draft an RFP for the purchase of a COTS product or consulting services to solve the problem through implementation of technical controls.
- C. Work with the CISO and department head to create an SLA specifying the response times of the IT security department when incidents are reported.
- D. Draft an MOU for the department head and CISO to approve, documenting the limits of the necessary behavior, and actions to be taken by both teams.
Answer: D
NEW QUESTION 8
A large enterprise introduced a next generation firewall appliance into the Internet facing DMZ. All Internet traffic passes through this appliance. Four hours after implementation the network engineering team discovered that traffic through the DMZ now has un-acceptable
latency, and is recommending that the new firewall be taken offline. At what point in the implementation process should this problem have been discovered?
- A. During the product selection phase
- B. When testing the appliance
- C. When writing the RFP for the purchase process
- D. During the network traffic analysis phase
Answer: B
NEW QUESTION 9
At 10:35 a.m. a malicious user was able to obtain a valid authentication token which allowed read/write access to the backend database of a financial company. At 10:45 a.m. the security administrator received multiple alerts from the company’s statistical anomaly- based IDS about a company database administrator performing unusual transactions. At 10:55 a.m. the security administrator resets the database administrator’s password.
At 11:00 a.m. the security administrator is still receiving alerts from the IDS about unusual transactions from the same user. Which of the following is MOST likely the cause of the alerts?
- A. The IDS logs are compromised.
- B. The new password was compromised.
- C. An input validation error has occurred.
- D. A race condition has occurred.
Answer: D
NEW QUESTION 10
A small company’s Chief Executive Officer (CEO) has asked its Chief Security Officer (CSO) to improve the company’s security posture quickly with regard to targeted attacks. Which of the following should the CSO conduct FIRST?
- A. Survey threat feeds from services inside the same industry.
- B. Purchase multiple threat feeds to ensure diversity and implement blocks for malicious traffic.
- C. Conduct an internal audit against industry best practices to perform a qualitative analysis.
- D. Deploy a UTM solution that receives frequent updates from a trusted industry vendor.
Answer: A
NEW QUESTION 11
After three vendors submit their requested documentation, the CPO and the SPM can better understand what each vendor does and what solutions that they can provide. But now they want to see the intricacies of how these solutions can adequately match the
requirements needed by the firm. Upon the directive of the CPO, the CISO should submit which of the following to the three submitting firms?
- A. A T&M contract
- B. An RFP
- C. A FFP agreement
- D. A new RFQ
Answer: B
NEW QUESTION 12
DRAG DROP
IT staff within a company often conduct remote desktop sharing sessions with vendors to troubleshoot vendor product-related issues. Drag and drop the following security controls to match the associated security concern. Options may be used once or not at all.
Answer:
Explanation: 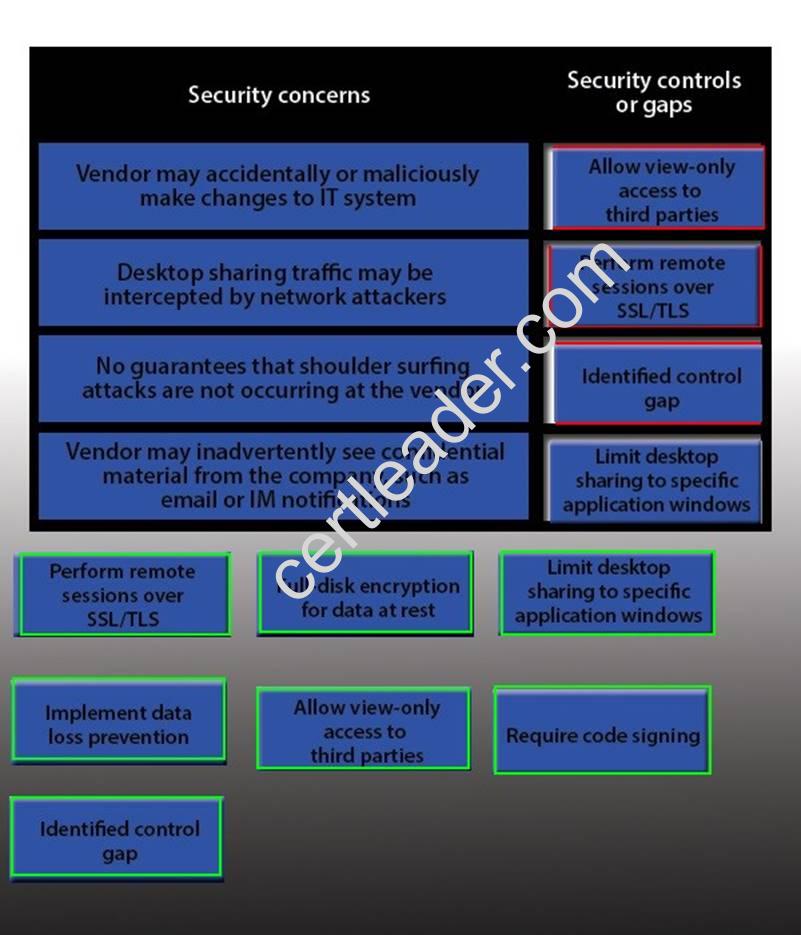
NEW QUESTION 13
After being notified of an issue with the online shopping cart, where customers are able to arbitrarily change the price of listed items, a programmer analyzes the following piece of code used by a web based shopping cart.
SELECT ITEM FROM CART WHERE ITEM=ADDSLASHES($USERINPUT);
The programmer found that every time a user adds an item to the cart, a temporary file is created on the web server /tmp directory. The temporary file has a name which is generated by concatenating the content of the $USERINPUT variable and a timestamp in the form of MM-DD-YYYY, (e.g. smartphone-12-25-2013.tmp) containing the price of the item being purchased. Which of the following is MOST likely being exploited to manipulate the price of a shopping cart’s items?
- A. Input validation
- B. SQL injection
- C. TOCTOU
- D. Session hijacking
Answer: C
NEW QUESTION 14
In order for a company to boost profits by implementing cost savings on non-core business activities, the IT manager has sought approval for the corporate email system to be hosted in the cloud. The compliance officer has been tasked with ensuring that data lifecycle issues are taken into account. Which of the following BEST covers the data lifecycle end- to-end?
- A. Creation and secure destruction of mail accounts, emails, and calendar items
- B. Information classification, vendor selection, and the RFP process
- C. Data provisioning, processing, in transit, at rest, and de-provisioning
- D. Securing virtual environments, appliances, and equipment that handle email
Answer: C
NEW QUESTION 15
A security manager is collecting RFQ, RFP, and RFI publications to help identify the technology trends which a government will be moving towards in the future. This information is available to the public. By consolidating the information, the security manager will be able to combine several perspectives into a broader view of technology trends. This is an example of which of the following? (Select TWO).
- A. Supervisory control and data acquisition
- B. Espionage
- C. Hacktivism
- D. Data aggregation
- E. Universal description discovery and integration
- F. Open source intelligence gathering
Answer: DF
NEW QUESTION 16
A company’s security policy states that its own internally developed proprietary Internet facing software must be resistant to web application attacks. Which of the following methods provides the MOST protection against unauthorized access to stored database information?
- A. Require all development to follow secure coding practices.
- B. Require client-side input filtering on all modifiable fields.
- C. Escape character sequences at the application tier.
- D. Deploy a WAF with application specific signatures.
Answer: A
NEW QUESTION 17
A security manager has received the following email from the Chief Financial Officer (CFO):
“While I am concerned about the security of the proprietary financial data in our ERP application, we have had a lot of turnover in the accounting group and I am having a difficult time meeting our monthly performance targets. As things currently stand, we do not allow employees to work from home but this is something I am willing to allow so we can get back on track. What should we do first to securely enable this capability for my group?”
Based on the information provided, which of the following would be the MOST appropriate response to the CFO?
- A. Remote access to the ERP tool introduces additional security vulnerabilities and should not be allowed.
- B. Allow VNC access to corporate desktops from personal computers for the users working from home.
- C. Allow terminal services access from personal computers after the CFO provides a list of the users working from home.
- D. Work with the executive management team to revise policies before allowing any remote access.
Answer: D
NEW QUESTION 18
An administrator wishes to replace a legacy clinical software product as it has become a security risk. The legacy product generates $10,000 in revenue a month. The new software product has an initial cost of $180,000 and a yearly maintenance of $2,000 after the first year. However, it will generate $15,000 in revenue per month and be more secure. How many years until there is a return on investment for this new package?
- A. 1
- B. 2
- C. 3
- D. 4
Answer: D
NEW QUESTION 19
The Chief Information Security Officer (CISO) is asking for ways to protect against zero-day exploits. The CISO is concerned that an unrecognized threat could compromise corporate data and result in regulatory fines as well as poor corporate publicity. The network is mostly flat, with split staff/guest wireless functionality. Which of the following equipment MUST be deployed to guard against unknown threats?
- A. Cloud-based antivirus solution, running as local admin, with push technology for definition updates.
- B. Implementation of an offsite data center hosting all company data, as well as deployment of VDI for all client computing needs.
- C. Host based heuristic IPS, segregated on a management VLAN, with direct control of the perimeter firewall ACLs.
- D. Behavior based IPS with a communication link to a cloud based vulnerability and threat feed.
Answer: D
Recommend!! Get the Full CAS-002 dumps in VCE and PDF From Surepassexam, Welcome to Download: https://www.surepassexam.com/CAS-002-exam-dumps.html (New 450 Q&As Version)