Download CAS-002 Free Practice Questions 2021
Our pass rate is high to 98.9% and the similarity percentage between our and real exam is 90% based on our seven-year educating experience. Do you want achievements in the CompTIA CAS-002 exam in just one try? I am currently studying for the . Latest , Try CompTIA CAS-002 Brain Dumps First.
Online CAS-002 free questions and answers of New Version:
NEW QUESTION 1
In a situation where data is to be recovered from an attacker’s location, which of the following are the FIRST things to capture? (Select TWO).
- A. Removable media
- B. Passwords written on scrap paper
- C. Snapshots of data on the monitor
- D. Documents on the printer
- E. Volatile system memory
- F. System hard drive
Answer: CE
NEW QUESTION 2
Company A needs to export sensitive data from its financial system to company B’s database, using company B’s API in an automated manner. Company A’s policy prohibits the use of any intermediary external systems to transfer or store its sensitive data, therefore the transfer must occur directly between company A’s financial system and company B’s destination server using the supplied API. Additionally, company A’s legacy financial software does not support encryption, while company B’s API supports encryption. Which of the following will provide end-to-end encryption for the data transfer while adhering to these requirements?
- A. Company A must install an SSL tunneling service on the financial system.
- B. Company A’s security administrator should use an HTTPS capable browser to transfer the data.
- C. Company A should use a dedicated MPLS circuit to transfer the sensitive data to company B.
- D. Company A and B must create a site-to-site IPSec VPN on their respective firewalls.
Answer: A
NEW QUESTION 3
A sensitive database needs its cryptographic integrity upheld. Which of the following controls meets this goal? (Select TWO).
- A. Data signing
- B. Encryption
- C. Perfect forward secrecy
- D. Steganography
- E. Data vaulting
- F. RBAC
- G. Lock and key
Answer: AF
NEW QUESTION 4
Staff from the sales department have administrator rights to their corporate standard operating environment, and often connect their work laptop to customer networks when onsite during meetings and presentations. This increases the risk and likelihood of a security incident when the sales staff reconnects to the corporate LAN. Which of the following controls would BEST protect the corporate network?
- A. Implement a network access control (NAC) solution that assesses the posture of the laptop before granting network access.
- B. Use an independent consulting firm to provide regular network vulnerability assessments and biannually qualitative risk assessments.
- C. Provide sales staff with a separate laptop with no administrator access just for sales visits.
- D. Update the acceptable use policy and ensure sales staff read and acknowledge the policy.
Answer: A
NEW QUESTION 5
A team is established to create a secure connection between software packages in order to list employee's remaining or unused benefits on their paycheck stubs. Which of the following business roles would be MOST effective on this team?
- A. Network Administrator, Database Administrator, Programmers
- B. Network Administrator, Emergency Response Team, Human Resources
- C. Finance Officer, Human Resources, Security Administrator
- D. Database Administrator, Facilities Manager, Physical Security Manager
Answer: C
NEW QUESTION 6
A corporation implements a mobile device policy on smartphones that utilizes a white list for allowed applications. Recently, the security administrator notices that a consumer cloud based storage application has been added to the mobile device white list. Which of the following security implications should the security administrator cite when recommending the application’s removal from the white list?
- A. Consumer cloud storage systems retain local copies of each file on the smartphone, as well as in the cloud, causing a potential data breach if the phone is lost or stolen.
- B. Smartphones can export sensitive data or import harmful data with this application causing the potential for DLP or malware issues.
- C. Consumer cloud storage systems could allow users to download applications to the smartphon
- D. Installing applications this way would circumvent the application white list.
- E. Smartphones using consumer cloud storage are more likely to have sensitive data remnants on them when they are repurposed.
Answer: B
NEW QUESTION 7
Company XYZ has had repeated vulnerability exploits of a critical nature released to the company’s flagship product. The product is used by a number of large customers. At the Chief Information Security Officer’s (CISO’s) request, the product manager now has to budget for a team of security consultants to introduce major product security improvements.
Here is a list of improvements in order of priority:
1. A noticeable improvement in security posture immediately.
2. Fundamental changes to resolve systemic issues as an ongoing process
3. Improvements should be strategic as opposed to tactical
4. Customer impact should be minimized
Which of the following recommendations is BEST for the CISO to put forward to the product manager?
- A. Patch the known issues and provide the patch to customer
- B. Make a company announcement to customers on the main website to reduce the perceived exposure of the application to alleviate customer concern
- C. Engage penetration testers and code reviewers to perform an in-depth review of the produc
- D. Based on the findings, address the defects and re-test the findings to ensure that any defects have been resolved.
- E. Patch the known issues and provide the patch to customer
- F. Engage penetration testers and code reviewers to perform an in-depth review of the produc
- G. Based on the findings, address the defects and re-test the findings to ensure that the defects have been resolve
- H. Introduce periodic code review and penetration testing of the product in question and consider including all relevant future projects going forward.
- I. Patch the known issues and provide the patch to customer
- J. Implement an SSDLC / SDL overlay on top of the SDL
- K. Train architects, designers, developers, testers and operators on security importance and ensure that security-relevant activities are performed within each of the SDLC phase
- L. Use the product as the primary focal point to close out issues and consider using the SSDLC / SDL overlay for all relevant future projects.
- M. Stop active support of the produc
- N. Bring forward end-of-life dates for the product so that it can be decommissione
- O. Start a new project to develop a replacement product and ensure that an SSDLC / SDL overlay on top of the SDLC is forme
- P. Train BAs, architects, designers, developers, testers and operators on security importance and ensure that security-relevant activities are performed within each of the SDLC phases.
Answer: C
NEW QUESTION 8
A company is deploying a new iSCSI-based SAN. The requirements are as follows: Which of the following design specifications meet all the requirements? (Select TWO).
- A. Targets use CHAP authentication
- B. IPSec using AH with PKI certificates for authentication
- C. Fiber channel should be used with AES
- D. Initiators and targets use CHAP authentication
- E. Fiber channel over Ethernet should be used
- F. IPSec using AH with PSK authentication and 3DES
- G. Targets have SCSI IDs for authentication
Answer: BD
NEW QUESTION 9
A security engineer has inherited an authentication project which integrates 1024-bit PKI certificates into the company infrastructure and now has a new requirement to integrate 2048-bit PKI certificates so that the entire company will be interoperable with its vendors when the project is completed. The project is now 25% complete, with 15% of the company staff being issued 1024-bit certificates. The provisioning of network based accounts has not occurred yet due to other project delays. The project is now expected to be over budget and behind its original schedule. Termination of the existing project and beginning a new project is a consideration because of the change in scope. Which of the following is the security engineer’s MOST serious concern with implementing this solution?
- A. Succession planning
- B. Performance
- C. Maintainability
- D. Availability
Answer: C
NEW QUESTION 10
A security architect has been engaged during the implementation stage of the SDLC to review a new HR software installation for security gaps. With the project under a tight schedule to meet market commitments on project delivery, which of the following security activities should be prioritized by the security architect? (Select TWO).
- A. Perform penetration testing over the HR solution to identify technical vulnerabilities
- B. Perform a security risk assessment with recommended solutions to close off high-rated risks
- C. Secure code review of the HR solution to identify security gaps that could be exploited
- D. Perform access control testing to ensure that privileges have been configured correctly
- E. Determine if the information security standards have been complied with by the project
Answer: BE
NEW QUESTION 11
A university requires a significant increase in web and database server resources for one week, twice a year, to handle student registration. The web servers remain idle for the rest
of the year. Which of the following is the MOST cost effective way for the university to securely handle student registration?
- A. Virtualize the web servers locally to add capacity during registration.
- B. Move the database servers to an elastic private cloud while keeping the web servers local.
- C. Move the database servers and web servers to an elastic private cloud.
- D. Move the web servers to an elastic public cloud while keeping the database servers local.
Answer: D
NEW QUESTION 12
The DLP solution has been showing some unidentified encrypted data being sent using FTP to a remote server. A vulnerability scan found a collection of Linux servers that are missing OS level patches. Upon further investigation, a technician notices that there are a few unidentified processes running on a number of the servers. What would be a key FIRST step for the data security team to undertake at this point?
- A. Capture process ID data and submit to anti-virus vendor for review.
- B. Reboot the Linux servers, check running processes, and install needed patches.
- C. Remove a single Linux server from production and place in quarantine.
- D. Notify upper management of a security breach.
- E. Conduct a bit level image, including RAM, of one or more of the Linux servers.
Answer: E
NEW QUESTION 13
Which of the following does SAML uses to prevent government auditors or law enforcement from identifying specific entities as having already connected to a service provider through an SSO operation?
- A. Transient identifiers
- B. Directory services
- C. Restful interfaces
- D. Security bindings
Answer: A
NEW QUESTION 14
A vulnerability scanner report shows that a client-server host monitoring solution operating in the credit card corporate environment is managing SSL sessions with a weak algorithm which does not meet corporate policy. Which of the following are true statements? (Select TWO).
- A. The X509 V3 certificate was issued by a non trusted public CA.
- B. The client-server handshake could not negotiate strong ciphers.
- C. The client-server handshake is configured with a wrong priority.
- D. The client-server handshake is based on TLS authentication.
- E. The X509 V3 certificate is expired.
- F. The client-server implements client-server mutual authentication with different certificates.
Answer: BC
NEW QUESTION 15
DRAG DROP
Drag and Drop the following information types on to the appropriate CIA category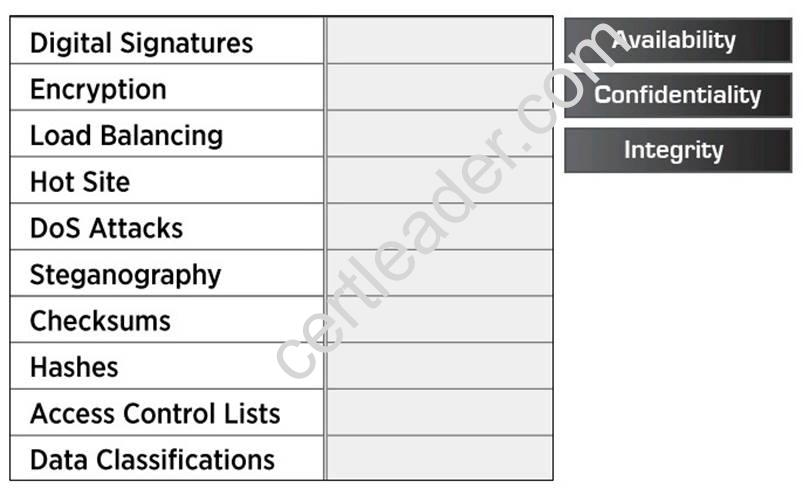
Answer:
Explanation: 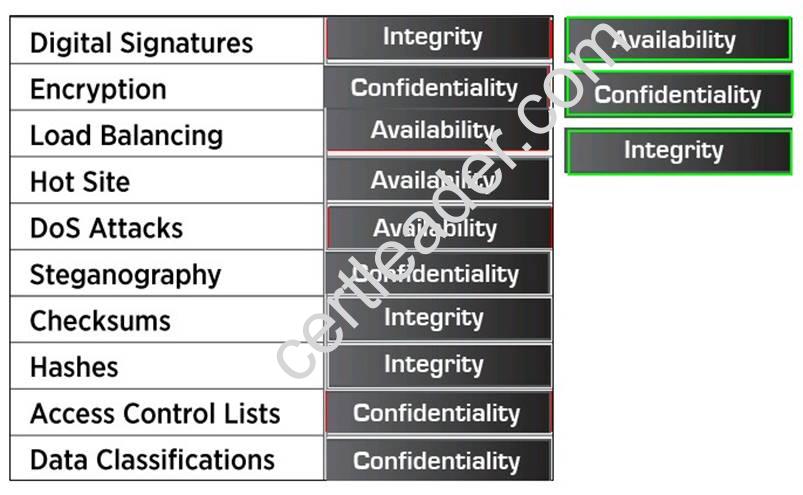
NEW QUESTION 16
A company has issued a new mobile device policy permitting BYOD and company-issued devices. The company-issued device has a managed middleware client that restricts the applications allowed on company devices and provides those that are approved. The middleware client provides configuration standardization for both company owned and BYOD to secure data and communication to the device according to industry best practices. The policy states that, “BYOD clients must meet the company’s infrastructure requirements to permit a connection.” The company also issues a memorandum separate from the policy, which provides instructions for the purchase, installation, and use of the middleware client on BYOD. Which of the following is being described?
- A. Asset management
- B. IT governance
- C. Change management
- D. Transference of risk
Answer: B
NEW QUESTION 17
In single sign-on, the secondary domain needs to trust the primary domain to do which of the following? (Select TWO).
- A. Correctly assert the identity and authorization credentials of the end user.
- B. Correctly assert the authentication and authorization credentials of the end user.
- C. Protect the authentication credentials used to verify the end user identity to the secondary domain for unauthorized use.
- D. Protect the authentication credentials used to verify the end user identity to the secondary domain for authorized use.
- E. Protect the accounting credentials used to verify the end user identity to the secondary domain for unauthorized use.
- F. Correctly assert the identity and authentication credentials of the end user.
Answer: DF
Explanation: Topic 4, Volume D
NEW QUESTION 18
The Information Security Officer (ISO) believes that the company has been targeted by cybercriminals and it is under a cyber attack. Internal services that are normally available to the public via the Internet are inaccessible, and employees in the office are unable to browse the Internet. The senior security engineer starts by reviewing the bandwidth at the border router, and notices that the incoming bandwidth on the router’s external interface is maxed out. The security engineer then inspects the following piece of log to try and determine the reason for the downtime, focusing on the company’s external router’s IP which is 128.20.176.19:
11:16:22.110343 IP 90.237.31.27.19 > 128.20.176.19.19: UDP, length 1400
11:16:22.110351 IP 23.27.112.200.19 > 128.20.176.19.19: UDP, length 1400
11:16:22.110358 IP 192.200.132.213.19 > 128.20.176.19.19: UDP, length 1400
11:16:22.110402 IP 70.192.2.55.19 > 128.20.176.19.19: UDP, length 1400
11:16:22.110406 IP 112.201.7.39.19 > 128.20.176.19.19: UDP, length 1400
Which of the following describes the findings the senior security engineer should report to the ISO and the BEST solution for service restoration?
- A. After the senior engineer used a network analyzer to identify an active Fraggle attack, the company’s ISP should be contacted and instructed to block the malicious packets.
- B. After the senior engineer used the above IPS logs to detect the ongoing DDOS attack, an IPS filter should be enabled to block the attack and restore communication.
- C. After the senior engineer used a mirror port to capture the ongoing amplification attack, a BGP sinkhole should be configured to drop traffic at the source networks.
- D. After the senior engineer used a packet capture to identify an active Smurf attack, an ACL should be placed on the company’s external router to block incoming UDP port 19 traffic.
Answer: A
NEW QUESTION 19
Joe, a penetration tester, is tasked with testing the security robustness of the protocol between a mobile web application and a RESTful application server. Which of the following security tools would be required to assess the security between the mobile web application and the RESTful application server? (Select TWO).
- A. Jailbroken mobile device
- B. Reconnaissance tools
- C. Network enumerator
- D. HTTP interceptor
- E. Vulnerability scanner
- F. Password cracker
Answer: DE
P.S. Easily pass CAS-002 Exam with 450 Q&As Surepassexam Dumps & pdf Version, Welcome to Download the Newest Surepassexam CAS-002 Dumps: https://www.surepassexam.com/CAS-002-exam-dumps.html (450 New Questions)