Abreast Of The Times CEH-001 Preparation 2021
Our pass rate is high to 98.9% and the similarity percentage between our CEH-001 study guide and real exam is 90% based on our seven-year educating experience. Do you want achievements in the GAQM CEH-001 exam in just one try? I am currently studying for the GAQM CEH-001 exam. Latest GAQM CEH-001 Test exam practice questions and answers, Try GAQM CEH-001 Brain Dumps First.
NEW QUESTION 1
Jess the hacker runs L0phtCrack's built-in sniffer utility that grabs SMB password hashes and stores them for offline cracking. Once cracked, these passwords can provide easy access to whatever network resources the user account has access to. But Jess is not picking up hashes from the network. Why?
- A. The network protocol is configured to use SMB Signing
- B. The physical network wire is on fibre optic cable
- C. The network protocol is configured to use IPSEC
- D. L0phtCrack SMB sniffing only works through Switches and not Hubs
Answer: A
NEW QUESTION 2
A tester is attempting to capture and analyze the traffic on a given network and realizes that the network has several switches. What could be used to successfully sniff the traffic on this switched network? (Choose three.)
- A. ARP spoofing
- B. MAC duplication
- C. MAC flooding
- D. SYN flood
- E. Reverse smurf attack
- F. ARP broadcasting
Answer: ABC
NEW QUESTION 3
Which of the following tools are used for enumeration? (Choose three.)
- A. SolarWinds
- B. USER2SID
- C. Cheops
- D. SID2USER
- E. DumpSec
Answer: BDE
Explanation:
USER2SID, SID2USER, and DumpSec are three of the tools used for system enumeration. Others are tools such as NAT and Enum. Knowing which tools are used in each step of the hacking methodology is an important goal of the CEH exam. You should spend a portion of your time preparing for the test practicing with the tools and learning to understand their output.
NEW QUESTION 4
What type of encryption does WPA2 use?
- A. DES 64 bit
- B. AES-CCMP 128 bit
- C. MD5 48 bit
- D. SHA 160 bit
Answer: B
NEW QUESTION 5
You wish to determine the operating system and type of web server being used. At the same time you wish to arouse no suspicion within the target organization.
While some of the methods listed below work, which holds the least risk of detection?
- A. Make some phone calls and attempt to retrieve the information using social engineering.
- B. Use nmap in paranoid mode and scan the web server.
- C. Telnet to the web server and issue commands to illicit a response.
- D. Use the netcraft web site look for the target organization’s web site.
Answer: D
Explanation:
Netcraft is providing research data and analysis on many aspects of the Internet. Netcraft has explored the Internet since 1995 and is a respected authority on the market share of web servers, operating systems, hosting providers, ISPs, encrypted transactions, electronic commerce, scripting languages and content technologies on the internet.
NEW QUESTION 6
Bob has a good understanding of cryptography, having worked with it for many years. Cryptography is used to secure data from specific threats, but it does not secure the application from coding errors. It can provide data privacy; integrity and enable strong authentication but it cannot mitigate programming errors. What is a good example of a programming error that Bob can use to explain to the management how encryption will not address all their security concerns?
- A. Bob can explain that using a weak key management technique is a form of programming error
- B. Bob can explain that using passwords to derive cryptographic keys is a form of a programming error
- C. Bob can explain that a buffer overflow is an example of programming error and it is a common mistake associated with poor programming technique
- D. Bob can explain that a random number generator can be used to derive cryptographic keys but it uses a weak seed value and this is a form of a programming error
Answer: A
NEW QUESTION 7
Which of the following are advantages of adopting a Single Sign On (SSO) system? (Choose two.)
- A. A reduction in password fatigue for users because they do not need to know multiple passwords when accessing multiple applications
- B. A reduction in network and application monitoring since all recording will be completed at the SSO system
- C. A reduction in system administration overhead since any user login problems can be resolved at the SSO system
- D. A reduction in overall risk to the system since network and application attacks can only happen at the SSO point
Answer: AC
NEW QUESTION 8
A company firewall engineer has configured a new DMZ to allow public systems to be located away from the internal network. The engineer has three security zones set:
Untrust (Internet) – (Remote network = 217.77.88.0/24) DMZ (DMZ) – (11.12.13.0/24)
Trust (Intranet) – (192.168.0.0/24)
The engineer wants to configure remote desktop access from a fixed IP on the remote network to a remote desktop server in the DMZ. Which rule would best fit this requirement?
- A. Permit 217.77.88.0/24 11.12.13.0/24 RDP 3389
- B. Permit 217.77.88.12 11.12.13.50 RDP 3389
- C. Permit 217.77.88.12 11.12.13.0/24 RDP 3389
- D. Permit 217.77.88.0/24 11.12.13.50 RDP 3389
Answer: B
NEW QUESTION 9
Syslog is a standard for logging program messages. It allows separation of the software that generates messages from the system that stores them and the software that reports and analyzes them. It also provides devices, which would otherwise be unable to communicate a means to notify administrators of problems or performance.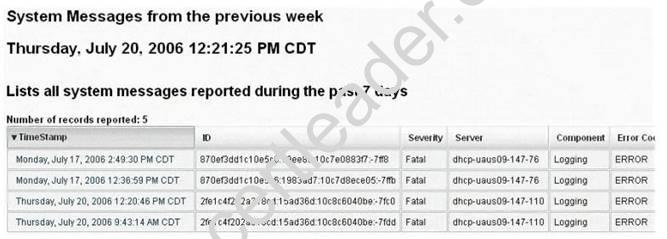
What default port Syslog daemon listens on?
- A. 242
- B. 312
- C. 416
- D. 514
Answer: D
NEW QUESTION 10
The following excerpt is taken from a honeyput log. The log captures activities across three days. There are several intrusion attempts; however, a few are successful. Study the log given below and answer the following question:
(Note: The objective of this questions is to test whether the student has learnt about passive OS fingerprinting (which should tell them the OS from log captures): can they tell a SQL injection attack signature; can they infer if a user ID has been created by an attacker and whether they can read plain source – destination entries from log entries.)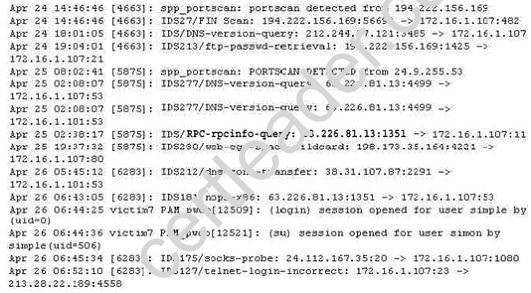
What can you infer from the above log?
- A. The system is a windows system which is being scanned unsuccessfully.
- B. The system is a web application server compromised through SQL injection.
- C. The system has been compromised and backdoored by the attacker.
- D. The actual IP of the successful attacker is 24.9.255.53.
Answer: A
NEW QUESTION 11
Ron has configured his network to provide strong perimeter security. As part of his network architecture, he has included a host that is fully exposed to attack. The system is on the public side of the demilitarized zone, unprotected by a firewall or filtering router. What would you call such a host?
- A. Honeypot
- B. DMZ host
- C. DWZ host
- D. Bastion Host
Answer: A
NEW QUESTION 12
TCP SYN Flood attack uses the three-way handshake mechanism.
1. An attacker at system A sends a SYN packet to victim at system B.
2. System B sends a SYN/ACK packet to victim A.
3. As a normal three-way handshake mechanism system A should send an ACK packet to system B, however, system A does not send an ACK packet to system B. In this case client B is waiting for an ACK packet from client A.
This status of client B is called
- A. "half-closed"
- B. "half open"
- C. "full-open"
- D. "xmas-open"
Answer: B
NEW QUESTION 13
What type of port scan is shown below?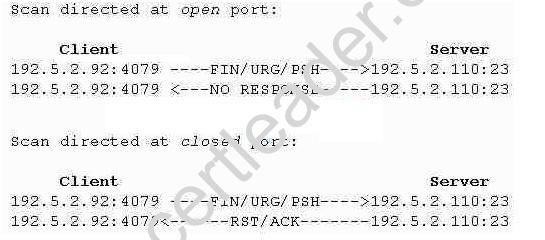
- A. Idle Scan
- B. Windows Scan
- C. XMAS Scan
- D. SYN Stealth Scan
Answer: C
Explanation:
An Xmas port scan is variant of TCP port scan. This type of scan tries to obtain information about the state of a target port by sending a packet which has multiple TCP flags set to 1 - "lit as an Xmas tree". The flags set for Xmas scan are FIN, URG and PSH. The purpose is to confuse and bypass simple firewalls. Some stateless firewalls only check against security policy those packets which have the SYN flag set (that is, packets that initiate connection according to the standards). Since Xmas scan packets are different, they can pass through these simple systems and reach the target host.
NEW QUESTION 14
When analyzing the IDS logs, the system administrator noticed an alert was logged when the external router was accessed from the administrator's computer to update the router configuration. What type of an alert is this?
- A. False positive
- B. False negative
- C. True positve
- D. True negative
Answer: A
NEW QUESTION 15
What type of session hijacking attack is shown in the exhibit?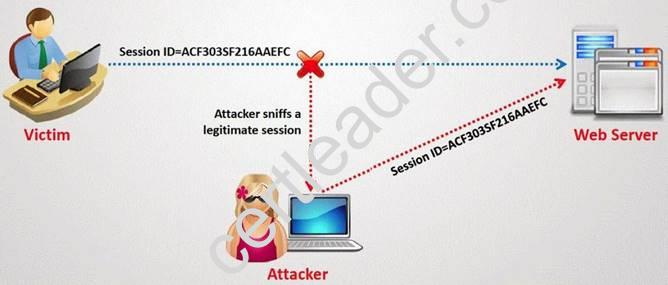
- A. Session Sniffing Attack
- B. Cross-site scripting Attack
- C. SQL Injection Attack
- D. Token sniffing Attack
Answer: A
NEW QUESTION 16
Which of the following tools would be the best choice for achieving compliance with PCI Requirement 11?
- A. Truecrypt
- B. Sub7
- C. Nessus
- D. Clamwin
Answer: C
NEW QUESTION 17
If the final set of security controls does not eliminate all risk in a system, what could be done next?
- A. Continue to apply controls until there is zero risk.
- B. Ignore any remaining risk.
- C. If the residual risk is low enough, it can be accepted.
- D. Remove current controls since they are not completely effective.
Answer: C
NEW QUESTION 18
Which of the following systems would not respond correctly to an nmap XMAS scan?
- A. Windows 2000 Server running IIS 5
- B. Any Solaris version running SAMBA Server
- C. Any version of IRIX
- D. RedHat Linux 8.0 running Apache Web Server
Answer: A
Explanation:
When running a XMAS Scan, if a RST packet is received, the port is considered closed, while no response means it is open|filtered. The big downside is that not all systems follow RFC 793 to the letter. A number of systems send RST responses to the probes regardless of whether the port is open or not. This causes all of the ports to be labeled closed. Major operating systems that do this are Microsoft Windows, many Cisco devices, BSDI, and IBM OS/400.
NEW QUESTION 19
Lee is using Wireshark to log traffic on his network. He notices a number of packets being directed to an internal IP from an outside IP where the packets are ICMP and their size is around 65, 536 bytes. What is Lee seeing here?
- A. Lee is seeing activity indicative of a Smurf attack.
- B. Most likely, the ICMP packets are being sent in this manner to attempt IP spoofing.
- C. Lee is seeing a Ping of death attack.
- D. This is not unusual traffic, ICMP packets can be of any size.
Answer: C
NEW QUESTION 20
You generate MD5 128-bit hash on all files and folders on your computer to keep a baseline check for security reasons?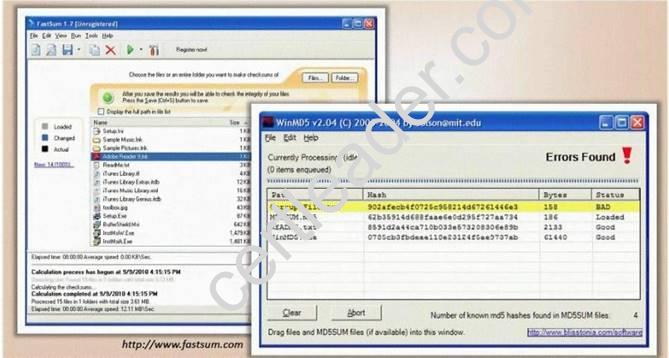
What is the length of the MD5 hash?
- A. 32 character
- B. 64 byte
- C. 48 char
- D. 128 kb
Answer: A
NEW QUESTION 21
Which solution can be used to emulate computer services, such as mail and ftp, and to capture information related to logins or actions?
- A. Firewall
- B. Honeypot
- C. Core server
- D. Layer 4 switch
Answer: B
NEW QUESTION 22
Which type of hacker represents the highest risk to your network?
- A. black hat hackers
- B. grey hat hackers
- C. disgruntled employees
- D. script kiddies
Answer: C
NEW QUESTION 23
David is a security administrator working in Boston. David has been asked by the office's manager to block all POP3 traffic at the firewall because he believes employees are spending too much time reading personal email. How can David block POP3 at the firewall?
- A. David can block port 125 at the firewall.
- B. David can block all EHLO requests that originate from inside the office.
- C. David can stop POP3 traffic by blocking all HELO requests that originate from inside the office.
- D. David can block port 110 to block all POP3 traffic.
Answer: D
NEW QUESTION 24
Which of the following techniques can be used to mitigate the risk of an on-site attacker from connecting to an unused network port and gaining full access to the network? (Choose three.)
- A. Port Security
- B. IPSec Encryption
- C. Network Admission Control (NAC)
- D. 802.1q Port Based Authentication
- E. 802.1x Port Based Authentication
- F. Intrusion Detection System (IDS)
Answer: ACE
NEW QUESTION 25
Which of the following are well know password-cracking programs?(Choose all that apply.
- A. L0phtcrack
- B. NetCat
- C. Jack the Ripper
- D. Netbus
- E. John the Ripper
Answer: AE
Explanation:
L0phtcrack and John the Ripper are two well know password-cracking programs. Netcat is considered the Swiss-army knife of hacking tools, but is not used for password cracking
NEW QUESTION 26
In the software security development life cyle process, threat modeling occurs in which phase?
- A. Design
- B. Requirements
- C. Verification
- D. Implementation
Answer: A
NEW QUESTION 27
This TCP flag instructs the sending system to transmit all buffered data immediately.
- A. SYN
- B. RST
- C. PSH
- D. URG
- E. FIN
Answer: C
NEW QUESTION 28
A certified ethical hacker (CEH) completed a penetration test of the main headquarters of a company almost two months ago, but has yet to get paid. The customer is suffering from financial problems, and the CEH is worried that the company will go out of business and end up not paying. What actions should the CEH take?
- A. Threaten to publish the penetration test results if not paid.
- B. Follow proper legal procedures against the company to request payment.
- C. Tell other customers of the financial problems with payments from this company.
- D. Exploit some of the vulnerabilities found on the company webserver to deface it.
Answer: B
NEW QUESTION 29
Stephanie works as senior security analyst for a manufacturing company in Detroit. Stephanie manages network security throughout the organization. Her colleague Jason told her in confidence that he was able to see confidential corporate information posted on the external website http://www.jeansclothesman.com. He tries random URLs on the company's website and finds confidential information leaked over the web. Jason says this happened about a month ago. Stephanie visits the said URLs, but she finds nothing. She is very concerned about this, since someone should be held accountable if there was sensitive information posted on the website.
Where can Stephanie go to see past versions and pages of a website?
- A. She should go to the web page Samspade.org to see web pages that might no longer be on the website
- B. If Stephanie navigates to Search.com; she will see old versions of the company website
- C. Stephanie can go to Archive.org to see past versions of the company website
- D. AddressPast.com would have any web pages that are no longer hosted on the company's website
Answer: C
NEW QUESTION 30
Which tool would be used to collect wireless packet data?
- A. NetStumbler
- B. John the Ripper
- C. Nessus
- D. Netcat
Answer: A
NEW QUESTION 31
......
Recommend!! Get the Full CEH-001 dumps in VCE and PDF From Passcertsure, Welcome to Download: https://www.passcertsure.com/CEH-001-test/ (New 878 Q&As Version)