Regenerate CISSP Dump 2021
We provide real CISSP exam questions and answers braindumps in two formats. Download PDF & Practice Tests. Pass ISC2 CISSP Exam quickly & easily. The CISSP PDF type is available for reading and printing. You can print more and practice many times. With the help of our ISC2 CISSP dumps pdf and vce product and material, you can easily pass the CISSP exam.
NEW QUESTION 1
A security professional is asked to provide a solution that restricts a bank teller to only perform a savings deposit transaction but allows a supervisor to perform corrections after the transaction. Which of the following is the MOST effective solution?
- A. Access is based on rules.
- B. Access is determined by the system.
- C. Access is based on user's role.
- D. Access is based on data sensitivity.
Answer: C
NEW QUESTION 2
Which security modes is MOST commonly used in a commercial environment because it protects the integrity
of financial and accounting data?
- A. Biba
- B. Graham-Denning
- C. Clark-Wilson
- D. Beil-LaPadula
Answer: C
NEW QUESTION 3
Which of the following mobile code security models relies only on trust?
- A. Code signing
- B. Class authentication
- C. Sandboxing
- D. Type safety
Answer: A
NEW QUESTION 4
Refer to the information below to answer the question.
A large organization uses unique identifiers and requires them at the start of every system session. Application access is based on job classification. The organization is subject to periodic independent reviews of access controls and violations. The organization uses wired and wireless networks and remote access. The organization also uses secure connections to branch offices and secure backup and recovery strategies for selected information and processes.
In addition to authentication at the start of the user session, best practice would require re-authentication
- A. periodically during a session.
- B. for each business process.
- C. at system sign-off.
- D. after a period of inactivity.
Answer: D
NEW QUESTION 5
Refer to the information below to answer the question.
A new employee is given a laptop computer with full administrator access. This employee does not have a personal computer at home and has a child that uses the computer to send and receive e-mail, search the web, and use instant messaging. The organization’s Information Technology (IT) department discovers that a peer-to-peer program has been installed on the computer using the employee's access.
Which of the following solutions would have MOST likely detected the use of peer-to-peer programs when the computer was connected to the office network?
- A. Anti-virus software
- B. Intrusion Prevention System (IPS)
- C. Anti-spyware software
- D. Integrity checking software
Answer: B
NEW QUESTION 6
Discretionary Access Control (DAC) is based on which of the following?
- A. Information source and destination
- B. Identification of subjects and objects
- C. Security labels and privileges
- D. Standards and guidelines
Answer: B
NEW QUESTION 7
In which order, from MOST to LEAST impacted, does user awareness training reduce the occurrence of the events below?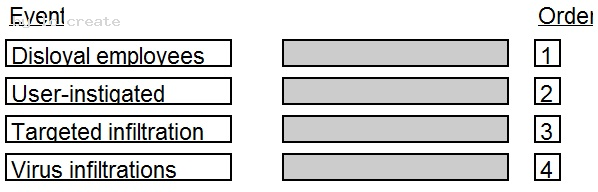
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 
NEW QUESTION 8
After a thorough analysis, it was discovered that a perpetrator compromised a network by gaining access to the network through a Secure Socket Layer (SSL) Virtual Private Network (VPN) gateway. The perpetrator guessed a username and brute forced the password to gain access. Which of the following BEST mitigates this issue?
- A. Implement strong passwords authentication for VPN
- B. Integrate the VPN with centralized credential stores
- C. Implement an Internet Protocol Security (IPSec) client
- D. Use two-factor authentication mechanisms
Answer: D
NEW QUESTION 9
What is the BEST method to detect the most common improper initialization problems in programming languages?
- A. Use and specify a strong character encoding.
- B. Use automated static analysis tools that target this type of weakness.
- C. Perform input validation on any numeric inputs by assuring that they are within the expected range.
- D. Use data flow analysis to minimize the number of false positives.
Answer: B
NEW QUESTION 10
Which of the following types of business continuity tests includes assessment of resilience to internal and external risks without endangering live operations?
- A. Walkthrough
- B. Simulation
- C. Parallel
- D. White box
Answer: B
NEW QUESTION 11
Recovery strategies of a Disaster Recovery planning (DRIP) MUST be aligned with which of the following?
- A. Hardware and software compatibility issues
- B. Applications’ critically and downtime tolerance
- C. Budget constraints and requirements
- D. Cost/benefit analysis and business objectives
Answer: D
NEW QUESTION 12
Who would be the BEST person to approve an organizations information security policy?
- A. Chief Information Officer (CIO)
- B. Chief Information Security Officer (CISO)
- C. Chief internal auditor
- D. Chief Executive Officer (CEO)
Answer: B
Explanation:
Section: Security Operations
NEW QUESTION 13
A Denial of Service (DoS) attack on a syslog server exploits weakness in which of the following protocols?
- A. Point-to-Point Protocol (PPP) and Internet Control Message Protocol (ICMP)
- B. Transmission Control Protocol (TCP) and User Datagram Protocol (UDP)
- C. Address Resolution Protocol (ARP) and Reverse Address Resolution Protocol (RARP)
- D. Transport Layer Security (TLS) and Secure Sockets Layer (SSL)
Answer: B
NEW QUESTION 14
In the Software Development Life Cycle (SDLC), maintaining accurate hardware and software inventories is a critical part of
- A. systems integration.
- B. risk management.
- C. quality assurance.
- D. change management.
Answer: D
NEW QUESTION 15
An organization's data policy MUST include a data retention period which is based on
- A. application dismissal.
- B. business procedures.
- C. digital certificates expiration.
- D. regulatory compliance.
Answer: D
NEW QUESTION 16
An organization lacks a data retention policy. Of the following, who is the BEST person to consult for such requirement?
- A. Application Manager
- B. Database Administrator
- C. Privacy Officer
- D. Finance Manager
Answer: C
NEW QUESTION 17
With what frequency should monitoring of a control occur when implementing Information Security Continuous Monitoring (ISCM) solutions?
- A. Continuously without exception for all security controls
- B. Before and after each change of the control
- C. At a rate concurrent with the volatility of the security control
- D. Only during system implementation and decommissioning
Answer: B
NEW QUESTION 18
In a basic SYN flood attack, what is the attacker attempting to achieve?
- A. Exceed the threshold limit of the connection queue for a given service
- B. Set the threshold to zero for a given service
- C. Cause the buffer to overflow, allowing root access
- D. Flush the register stack, allowing hijacking of the root account
Answer: A
NEW QUESTION 19
Which of the following assures that rules are followed in an identity management architecture?
- A. Policy database
- B. Digital signature
- C. Policy decision point
- D. Policy enforcement point
Answer: D
NEW QUESTION 20
Match the objectives to the assessment questions in the governance domain of Software Assurance Maturity Model (SAMM).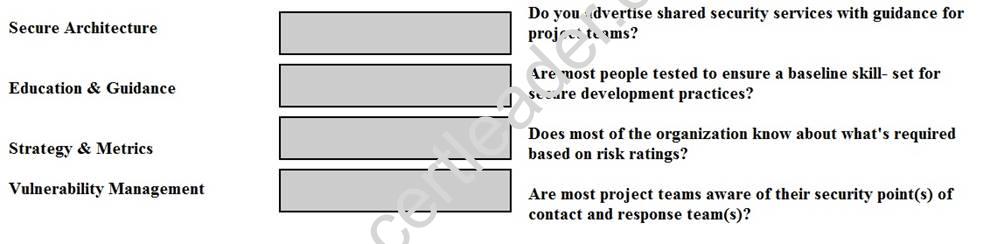
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 
NEW QUESTION 21
For network based evidence, which of the following contains traffic details of all network sessions in order to detect anomalies?
- A. Alert data
- B. User data
- C. Content data
- D. Statistical data
Answer: D
NEW QUESTION 22
An organization adopts a new firewall hardening standard. How can the security professional verify that the technical staff correct implemented the new standard?
- A. Perform a compliance review
- B. Perform a penetration test
- C. Train the technical staff
- D. Survey the technical staff
Answer: B
Explanation:
Section: Security Operations
NEW QUESTION 23
In general, servers that are facing the Internet should be placed in a demilitarized zone (DMZ). What is MAIN purpose of the DMZ?
- A. Reduced risk to internal systems.
- B. Prepare the server for potential attacks.
- C. Mitigate the risk associated with the exposed server.
- D. Bypass the need for a firewall.
Answer: A
NEW QUESTION 24
Which of the following is the MOST effective method to mitigate Cross-Site Scripting (XSS) attacks?
- A. Use Software as a Service (SaaS)
- B. Whitelist input validation
- C. Require client certificates
- D. Validate data output
Answer: B
NEW QUESTION 25
Which of the following methods of suppressing a fire is environmentally friendly and the MOST appropriate for a data center?
- A. Inert gas fire suppression system
- B. Halon gas fire suppression system
- C. Dry-pipe sprinklers
- D. Wet-pipe sprinklers
Answer: C
NEW QUESTION 26
A large university needs to enable student access to university resources from their homes. Which of the following provides the BEST option for low maintenance and ease of deployment?
- A. Provide students with Internet Protocol Security (IPSec) Virtual Private Network (VPN) client software.
- B. Use Secure Sockets Layer (SSL) VPN technology.
- C. Use Secure Shell (SSH) with public/private keys.
- D. Require students to purchase home router capable of VPN.
Answer: B
NEW QUESTION 27
......
P.S. Exambible now are offering 100% pass ensure CISSP dumps! All CISSP exam questions have been updated with correct answers: https://www.simply-pass.com/{factory}-exam/{productsort}-dumps.html (653 New Questions)