The Abreast Of The Times Guide To CISSP Exam Topics
Proper study guides for Improved ISC2 Certified Information Systems Security Professional (CISSP) certified begins with ISC2 CISSP preparation products which designed to deliver the Verified CISSP questions by making you pass the CISSP test at your first time. Try the free CISSP demo right now.
Online ISC2 CISSP free dumps demo Below:
NEW QUESTION 1
What should be the FIRST action to protect the chain of evidence when a desktop computer is involved?
- A. Take the computer to a forensic lab
- B. Make a copy of the hard drive
- C. Start documenting
- D. Turn off the computer
Answer: C
NEW QUESTION 2
A digitally-signed e-mail was delivered over a wireless network protected with Wired Equivalent Privacy (WEP) protocol. Which of the following principles is at risk?
- A. Availability
- B. Non-Repudiation
- C. Confidentiality
- D. Integrity
Answer: B
NEW QUESTION 3
Which of the following is an essential element of a privileged identity lifecycle management?
- A. Regularly perform account re-validation and approval
- B. Account provisioning based on multi-factor authentication
- C. Frequently review performed activities and request justification
- D. Account information to be provided by supervisor or line manager
Answer: A
NEW QUESTION 4
If a content management system (CMC) is implemented, which one of the following would occur?
- A. Developers would no longer have access to production systems
- B. The applications placed into production would be secure
- C. Patching the systems would be completed more quickly
- D. The test and production systems would be running the same software
Answer: D
NEW QUESTION 5
A database administrator is asked by a high-ranking member of management to perform specific changes to the accounting system database. The administrator is specifically instructed to not track or evidence the change in a ticket. Which of the following is the BEST course of action?
- A. Ignore the request and do not perform the change.
- B. Perform the change as requested, and rely on the next audit to detect and report the situation.
- C. Perform the change, but create a change ticket regardless to ensure there is complete traceability.
- D. Inform the audit committee or internal audit directly using the corporate whistleblower process.
Answer: D
NEW QUESTION 6
Given a file containing ordered number, i.e. “123456789,” match each of the following redundant Array of independent Disks (RAID) levels to the corresponding visual representation visual representation. Note: P() = parity.
Drag each level to the appropriate place on the diagram.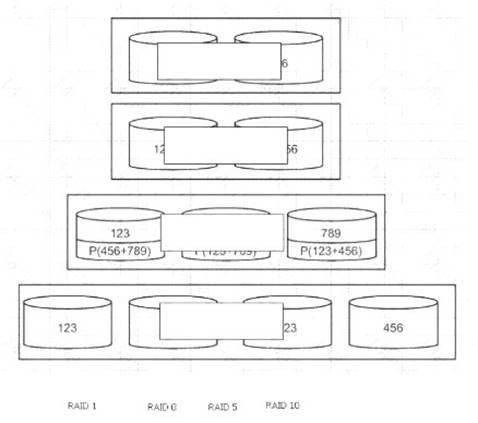
Solution:
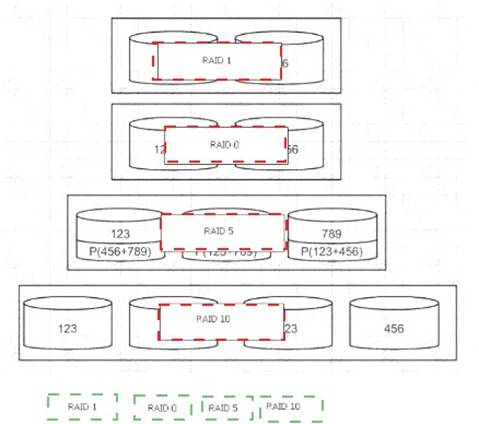
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 7
What does the Maximum Tolerable Downtime (MTD) determine?
- A. The estimated period of time a business critical database can remain down before customers are affected.
- B. The fixed length of time a company can endure a disaster without any Disaster Recovery (DR) planning
- C. The estimated period of time a business can remain interrupted beyond which it risks never recovering
- D. The fixed length of time in a DR process before redundant systems are engaged
Answer: C
NEW QUESTION 8
Which of the following is BEST achieved through the use of eXtensible Access Markup Language (XACML)?
- A. Minimize malicious attacks from third parties
- B. Manage resource privileges
- C. Share digital identities in hybrid cloud
- D. Defined a standard protocol
Answer: B
NEW QUESTION 9
Refer to the information below to answer the question.
In a Multilevel Security (MLS) system, the following sensitivity labels are used in increasing levels of sensitivity: restricted, confidential, secret, top secret. Table A lists the clearance levels for four users, while Table B lists the security classes of four different files.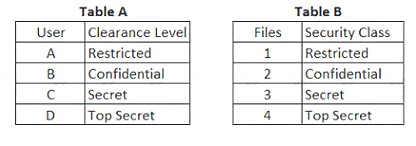
In a Bell-LaPadula system, which user has the MOST restrictions when writing data to any of the four files?
- A. User A
- B. User B
- C. User C
- D. User D
Answer: D
NEW QUESTION 10
What is the PRIMARY goal of fault tolerance?
- A. Elimination of single point of failure
- B. Isolation using a sandbox
- C. Single point of repair
- D. Containment to prevent propagation
Answer: A
NEW QUESTION 11
Why is planning the MOST critical phase of a Role Based Access Control (RBAC) implementation?
- A. The criteria for measuring risk is defined.
- B. User populations to be assigned to each role is determined.
- C. Role mining to define common access patterns is performed.
- D. The foundational criteria are defined.
Answer: B
NEW QUESTION 12
When developing a business case for updating a security program, the security program owner MUST do which of the following?
- A. Identify relevant metrics
- B. Prepare performance test reports
- C. Obtain resources for the security program
- D. Interview executive management
Answer: A
NEW QUESTION 13
Which one of the following transmission media is MOST effective in preventing data interception?
- A. Microwave
- B. Twisted-pair
- C. Fiber optic
- D. Coaxial cable
Answer: C
NEW QUESTION 14
What is the most effective form of media sanitization to ensure residual data cannot be retrieved?
- A. Clearing
- B. Destroying
- C. Purging
- D. Disposal
Answer: B
NEW QUESTION 15
The PRIMARY characteristic of a Distributed Denial of Service (DDoS) attack is that it
- A. exploits weak authentication to penetrate networks.
- B. can be detected with signature analysis.
- C. looks like normal network activity.
- D. is commonly confused with viruses or worms.
Answer: C
NEW QUESTION 16
......
Thanks for reading the newest CISSP exam dumps! We recommend you to try the PREMIUM DumpSolutions.com CISSP dumps in VCE and PDF here: https://www.dumpsolutions.com/CISSP-dumps/ (1487 Q&As Dumps)