The Secret Of EC-Council ECSAv10 Simulations
Proper study guides for Most up-to-date EC-Council EC-Council Certified Security Analyst (ECSA) v10 : Penetration Testing certified begins with EC-Council ECSAv10 preparation products which designed to deliver the Downloadable ECSAv10 questions by making you pass the ECSAv10 test at your first time. Try the free ECSAv10 demo right now.
Free demo questions for EC-Council ECSAv10 Exam Dumps Below:
NEW QUESTION 1
An external intrusion test and analysis identify security weaknesses and strengths of the client's systems and networks as they appear from outside the client's security perimeter, usually from the Internet.
The goal of an external intrusion test and analysis is to demonstrate the existence of known vulnerabilities that could be exploited by an external attacker.
During external penetration testing, which of the following scanning techniques allow you to determine a port’s state without making a full connection to the host?
- A. XMAS Scan
- B. SYN scan
- C. FIN Scan
- D. NULL Scan
Answer: B
NEW QUESTION 2
What sort of vulnerability assessment approach starts by building an inventory of protocols found on the machine?
- A. Inference-based Assessment
- B. Service-based Assessment Solutions
- C. Product-based Assessment Solutions
- D. Tree-based Assessment
Answer: A
NEW QUESTION 3
Which of the following is NOT related to the Internal Security Assessment penetration testing strategy?
- A. Testing to provide a more complete view of site security
- B. Testing focused on the servers, infrastructure, and the underlying software, including the target
- C. Testing including tiers and DMZs within the environment, the corporate network, or partner company connections
- D. Testing performed from a number of network access points representing each logical and physical segment
Answer: B
NEW QUESTION 4
What will the following URL produce in an unpatched IIS Web Server?
- A. Execute a buffer flow in the C: drive of the web server
- B. Insert a Trojan horse into the C: drive of the web server
- C. Directory listing of the C:windowssystem32 folder on the web server
- D. Directory listing of C: drive on the web server
Answer: D
NEW QUESTION 5
Logs are the record of the system and network activities. Syslog protocol is used for delivering log information across an IP network. Syslog messages can be sent via which one of the following?
- A. UDP and TCP
- B. TCP and SMTP
- C. SMTP
- D. UDP and SMTP
Answer: A
NEW QUESTION 6
What is the following command trying to accomplish?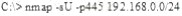
- A. Verify that NETBIOS is running for the 192.168.0.0 network
- B. Verify that TCP port 445 is open for the 192.168.0.0 network
- C. Verify that UDP port 445 is open for the 192.168.0.0 network
- D. Verify that UDP port 445 is closed for the 192.168.0.0 networks
Answer: C
NEW QUESTION 7
Which one of the following scans starts, but does not complete the TCP handshake sequence for each port selected, and it works well for direct scanning and often works well through firewalls?
- A. SYN Scan
- B. Connect() scan
- C. XMAS Scan
- D. Null Scan
Answer: A
NEW QUESTION 8
Which one of the following acts makes reputational risk of poor security a reality because it requires public disclosure of any security breach that involves personal information if it is unencrypted or if it is reasonably believed that the information has been acquired by an unauthorized person?
- A. California SB 1386
- B. Sarbanes-Oxley 2002
- C. Gramm-Leach-Bliley Act (GLBA)
- D. USA Patriot Act 2001
Answer: A
NEW QUESTION 9
Wireshark is a network analyzer. It reads packets from the network, decodes them, and presents them in an easy-to-understand format. Which one of the following is the command-line version of Wireshark, which can be used to capture the live packets from the wire or to read the saved capture files?
- A. Tcpdump
- B. Capinfos
- C. Tshark
- D. Idl2wrs
Answer: B
NEW QUESTION 10
How many bits is Source Port Number in TCP Header packet?
- A. 48
- B. 32
- C. 64
- D. 16
Answer: D
NEW QUESTION 11
Traffic on which port is unusual for both the TCP and UDP ports?
- A. Port 81
- B. Port 443
- C. Port 0
- D. Port 21
Answer: C
NEW QUESTION 12
Which one of the following acts related to the information security in the US fix the responsibility of management for establishing and maintaining an adequate internal control structure and procedures for financial reporting?
- A. California SB 1386
- B. Sarbanes-Oxley 2002
- C. Gramm-Leach-Bliley Act (GLBA)
- D. USA Patriot Act 2001
Answer: B
NEW QUESTION 13
Meyer Electronics Systems just recently had a number of laptops stolen out of their office. On these laptops contained sensitive corporate information regarding patents and company strategies.
A month after the laptops were stolen, a competing company was found to have just developed products that almost exactly duplicated products that Meyer produces.
What could have prevented this information from being stolen from the laptops?
- A. SDW Encryption
- B. EFS Encryption
- C. DFS Encryption
- D. IPS Encryption
Answer: B
NEW QUESTION 14
Terri works for a security consulting firm that is currently performing a penetration test on First National Bank in Tokyo. Terri's duties include bypassing firewalls and switches to gain access to the network. Terri sends an IP packet to one of the company's switches with ACK bit and the source address of her machine set.
What is Terri trying to accomplish by sending this IP packet?
- A. Poison the switch's MAC address table by flooding it with ACK bits
- B. Enable tunneling feature on the switch
- C. Trick the switch into thinking it already has a session with Terri's computer
- D. Crash the switch with a DoS attack since switches cannot send ACK bits
Answer: C
NEW QUESTION 15
The SnortMain () function begins by associating a set of handlers for the signals, Snort receives. It does this using the signal () function. Which one of the following functions is used as a programspecific signal and the handler for this calls the DropStats() function to output the current Snort statistics?
- A. SIGUSR1
- B. SIGTERM
- C. SIGINT
- D. SIGHUP
Answer: A
NEW QUESTION 16
How many possible sequence number combinations are there in TCP/IP protocol?
- A. 320 billion
- B. 32 million
- C. 4 billion
- D. 1 billion
Answer: C
NEW QUESTION 17
George is a senior security analyst working for a state agency in Florida. His state's congress just passed a bill mandating every state agency to undergo a security audit annually. After learning what will be required, George needs to implement an IDS as soon as possible before the first audit occurs.
The state bill requires that an IDS with a "time-based induction machine" be used. What IDS feature must George implement to meet this requirement?
- A. Pattern matching
- B. Statistical-based anomaly detection
- C. Real-time anomaly detection
- D. Signature-based anomaly detection
Answer: C
NEW QUESTION 18
Which of the following protocols cannot be used to filter VoIP traffic?
- A. Media Gateway Control Protocol (MGCP)
- B. Real-time Transport Control Protocol (RTCP)
- C. Session Description Protocol (SDP)
- D. Real-Time Publish Subscribe (RTPS)
Answer: D
NEW QUESTION 19
John and Hillary works at the same department in the company. John wants to find out Hillary's
network password so he can take a look at her documents on the file server. He enables Lophtcrack program to sniffing mode. John sends Hillary an email with a link to Error! Reference source not found.
What information will he be able to gather from this?
- A. The SID of Hillary's network account
- B. The network shares that Hillary has permissions
- C. The SAM file from Hillary's computer
- D. Hillary's network username and password hash
Answer: D
NEW QUESTION 20
Which of the following attacks does a hacker perform in order to obtain UDDI information such as businessEntity, businesService, bindingTemplate, and tModel?
- A. Web Services Footprinting Attack
- B. Service Level Configuration Attacks
- C. URL Tampering Attacks
- D. Inside Attacks
Answer: A
NEW QUESTION 21
Choose the correct option to define the Prefix Length.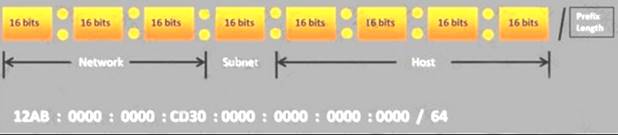
- A. Prefix Length = Subnet + Host portions
- B. Prefix Length = Network + Host portions
- C. Prefix Length = Network + Subnet portions
- D. Prefix Length = Network + Subnet + Host portions
Answer: C
NEW QUESTION 22
Which one of the following tools of trade is a commercial shellcode and payload generator written in Python by Dave Aitel?
- A. Microsoft Baseline Security Analyzer (MBSA)
- B. CORE Impact
- C. Canvas
- D. Network Security Analysis Tool (NSAT)
Answer: C
NEW QUESTION 23
Mason is footprinting an organization to gather competitive intelligence. He visits the company's website for contact information and telephone numbers but does not find any. He knows the entire staff directory was listed on their website 12 months. How can he find the directory?
- A. Visit Google’s search engine and view the cached copy
- B. Crawl and download the entire website using the Surfoffline tool and save them to his computer
- C. Visit the company's partners’ and customers' website for this information
- D. Use Way Back Machine in Archive.org web site to retrieve the Internet archive
Answer: D
NEW QUESTION 24
Identify the policy that defines the standards for the organizational network connectivity and security standards for computers that are connected in the organizational network.
- A. Information-Protection Policy
- B. Special-Access Policy
- C. Remote-Access Policy
- D. Acceptable-Use Policy
Answer: C
NEW QUESTION 25
Which one of the following log analysis tools is used for analyzing the server’s log files?
- A. Performance Analysis of Logs tool
- B. Network Sniffer Interface Test tool
- C. Ka Log Analyzer tool
- D. Event Log Tracker tool
Answer: C
NEW QUESTION 26
......
P.S. DumpSolutions.com now are offering 100% pass ensure ECSAv10 dumps! All ECSAv10 exam questions have been updated with correct answers: https://www.dumpsolutions.com/ECSAv10-dumps/ (201 New Questions)