Top Tips Of Latest 312-50 Test Questions
Ucertify 312-50 Questions are updated and all 312-50 answers are verified by experts. Once you have completely prepared with our 312-50 exam prep kits you will be ready for the real 312-50 exam without a problem. We have Abreast of the times EC-Council 312-50 dumps study guide. PASSED 312-50 First attempt! Here What I Did.
Also have 312-50 free dumps questions for you:
NEW QUESTION 1
NSLookup is a good tool to use to gain additional information about a target network. What does the following command accomplish?
nslookup
> server <ipaddress>
> set type =any
> ls -d <target.com>
- A. Enables DNS spoofing
- B. Loads bogus entries into the DNS table
- C. Verifies zone security
- D. Performs a zone transfer
- E. Resets the DNS cache
Answer: D
Explanation:
If DNS has not been properly secured, the command sequence displayed above will perform a zone transfer.
NEW QUESTION 2
A remote user tries to login to a secure network using Telnet, but accidently types in an invalid user name or password. Which responses would NOT be preferred by an experienced Security Manager? (multiple answer)
- A. Invalid Username
- B. Invalid Password
- C. Authentication Failure
- D. Login Attempt Failed
- E. Access Denied
Answer: AB
Explanation:
As little information as possible should be given about a failed login attempt. Invalid username or password is not desirable.
NEW QUESTION 3
An Nmap scan shows the following open ports, and nmap also reports that the OS guessing results to match too many signatures hence it cannot reliably be identified:
21 ftp
23 telnet
80 http
443 https
What does this suggest ?
- A. This is a Windows Domain Controller
- B. The host is not firewalled
- C. The host is not a Linux or Solaris system
- D. The host is not properly patched
Answer: D
Explanation:
If the answer was A nmap would guess it, it holds the MS
signature database, the host not being firewalled makes no difference. The host is not linux or solaris, well it very well could be. The host is not properly patched? That is the closest; nmaps OS detection architecture is based solely off the TCP ISN issued by the operating systems TCP/IP stack, if the stack is modified to show output from randomized ISN's or if your using a program to change the ISN then OS detection will fail. If the TCP/IP IP ID's are modified then os detection could also fail, because the machine would most likely come back as being down.
NEW QUESTION 4
Where should a security tester be looking for information that could be used by an attacker against an organization? (Select all that apply)
- A. CHAT rooms
- B. WHOIS database
- C. News groups
- D. Web sites
- E. Search engines
- F. Organization’s own web site
Answer: ABCDEF
Explanation:
A Security tester should search for information everywhere that he/she can access. You never know where you find that small piece of information that could penetrate a strong defense.
NEW QUESTION 5
Matthew re-injects a captured wireless packet back onto the network. He does this hundreds of times within a second. The packet is correctly encrypted and Matthew assumes it is an ARP request packet. The wireless host responds with a stream of responses, all individually encrypted with different IVs. What is this attack most appropriately called?
- A. Spoof attack
- B. Replay attack
- C. Injection attack
- D. Rebound attack
Answer: B
Explanation:
A replay attack is a form of network attack in which a valid data transmission is maliciously or fraudulently repeated or delayed. This is carried out either by the originator or by an adversary who intercepts the data and retransmits it, possibly as part of a masquerade attack by IP packet substitution (such as stream cipher attack).
NEW QUESTION 6
You are the chief information officer for your company, a shipping company based out of Oklahoma City. You are responsible for network security throughout the home office and all branch offices. You have implemented numerous layers of security from logical to physical. As part of your procedures, you perform a yearly network assessment which includes vulnerability analysis, internal network scanning, and external penetration tests. Your main concern currently is the server in the DMZ which hosts a number of company websites. To see how the server appears to external users, you log onto a laptop at a Wi-Fi hot spot. Since you already know the IP address of the web server, you create a telnet session to
that server and type in the command: HEAD /HTTP/1.0
After typing in this command, you are presented with the following screen: What are you trying to do here?
- A. You are attempting to send an html file over port 25 to the web server.
- B. By typing in the HEAD command, you are attempting to create a buffer overflow on the web server.
- C. You are trying to open a remote shell to the web server.
- D. You are trying to grab the banner of the web serve
- E. *
Answer: D
NEW QUESTION 7
Fake Anti-Virus, is one of the most frequently encountered and persistent threats on the web. This malware uses social engineering to lure users into infected websites with a technique called Search Engine Optimization.
Once the Fake AV is downloaded into the user's computer, the software will scare them into believing their system is infected with threats that do not really exist, and then push users to purchase services to clean up the non-existent threats.
The Fake AntiVirus will continue to send these annoying and intrusive alerts until a payment is made.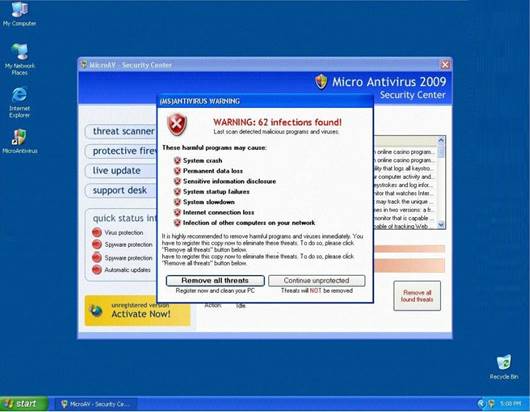
What is the risk of installing Fake AntiVirus?
- A. Victim's Operating System versions, services running and applications installed will be published on Blogs and Forums
- B. Victim's personally identifiable information such as billing address and credit card details, may be extracted and exploited by the attacker
- C. Once infected, the computer will be unable to boot and the Trojan will attempt to format the hard disk
- D. Denial of Service attack will be launched against the infected computer crashing other machines on the connected network
Answer: B
NEW QUESTION 8
Jim is having no luck performing a penetration test in company’s network. He is running the tests from home and has downloaded every security scanner that he could lay his hands on. Despite knowing the IP range of all the systems, and the exact network configuration, Jim is unable to get any useful results.
Why is Jim having these problems?
- A. Security scanners are not designed to do testing through a firewall.
- B. Security scanners cannot perform vulnerability linkage.
- C. Security scanners are only as smart as their database and cannot find unpublished vulnerabilities.
- D. All of the above.
Answer: D
Explanation:
The Security scanners available online are often to “outdated” to perform a live pentest against a victim.
NEW QUESTION 9
Bill is a security analyst for his company. All the switches used in the company's office are Cisco switches. Bill wants to make sure all switches are safe from ARP poisoning. How can Bill accomplish this?
- A. Bill can use the command: ip dhcp snooping.
- B. Bill can use the command: no ip snoop.
- C. Bill could use the command: ip arp no flood.
- D. He could use the command: ip arp no snoop.
Answer: A
NEW QUESTION 10
One of the most common and the best way of cracking RSA encryption is to being to derive the two prime numbers, which are used in the RSA PKI mathematical process. If the two numbers p and q are discovered through a process, then the private key can be derived.
- A. Factorization
- B. Prime Detection
- C. Hashing
- D. Brute-forcing
Answer: A
Explanation:
In April 1994, an international cooperative group of mathematicians and computer scientists solved a 17-year-old challenge problem, the factoring of a 129-digit number, called RSA-129, into two primes. That is, RSA-129 = 1143816257578888676692357799761466120102182
9672124236256256184293570693524573389783059
7123563958705058989075147599290026879543541
= 34905295108476509491478496199038 98133417764638493387843990820577 times
32769132993266709549961988190834 461413177642967992942539798288533.
Se more at http://en.wikipedia.org/wiki/RSA_Factoring_Challenge
NEW QUESTION 11
You work as security technician at ABC.com. While doing web application testing, you might be required to look through multiple web pages online which can take a long time. Which of the processes listed below would be a more efficient way of doing this type of validation?
- A. Use mget to download all pages locally for further inspection.
- B. Use wget to download all pages locally for further inspection.
- C. Use get* to download all pages locally for further inspection.
- D. Use get() to download all pages locally for further inspection.
Answer: B
Explanation:
Wget is a utility used for mirroring websites, get* doesn’t work, as for the actual FTP command to work there needs to be a space between get and * (ie. get *), get(); is just bogus, that’s a C function that’s written 100% wrong. mget is a command used from “within” ftp itself, ruling out A. Which leaves B use wget, which is designed for mirroring and download files, especially web pages, if used with the –R option (ie. wget –R www.ABC.com) it could mirror a site, all expect protected portions of course.
Note: GNU Wget is a free network utility to retrieve files from the World Wide Web using HTTP and FTP and can be used to make mirrors of archives and home pages thus enabling work in the background, after having logged off.
NEW QUESTION 12
A rootkit is a collection of tools (programs) that enable administrator-level access to a computer. This program hides itself deep into an operating system for malicious activity and is extremely difficult to detect. The malicious software operates in a stealth fashion by hiding its files, processes and registry keys and may be used to create a hidden directory or folder designed to keep out of view from a user's operating system and security software.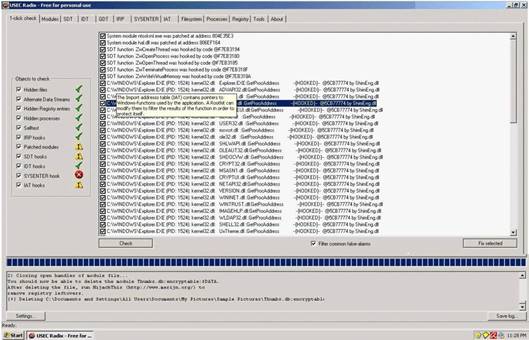
What privilege level does a rootkit require to infect successfully on a Victim's machine?
- A. User level privileges
- B. Ring 3 Privileges
- C. System level privileges
- D. Kernel level privileges
Answer: D
NEW QUESTION 13
You find the following entries in your web log. Each shows attempted access to either root.exe or cmd.exe. What caused this?
GET /scripts/root.exe?/c+dir GET /MSADC/root.exe?/c+dir
GET /c/winnt/system32/cmd.exe?/c+dir GET /d/winnt/system32/cmd.exe?/c+dir
GET /scripts/..%5c../winnt/system32/cmd.exe?/c+dir
GET /_vti_bin/..%5c../..%5c../..%5c../winnt/system32/cmd.exe?/c+dir GET /_mem_bin/..%5c../..%5c../..%5c../winnt/system32/cmd.exe?/c+dir GET
/msadc/..%5c../..%5c../..%5c/..xc1x1c../..xc1x1c../..xc1x1c../winnt/system32/cmd.exe?/c+di r
GET /scripts/..xc1x1c../winnt/system32/cmd.exe?/c+dir GET /scripts/..xc0/../winnt/system32/cmd.exe?/c+dir GET /scripts/..xc0xaf../winnt/system32/cmd.exe?/c+dir GET /scripts/..xc1x9c../winnt/system32/cmd.exe?/c+dir GET /scripts/..%35c../winnt/system32/cmd.exe?/c+dir GET /scripts/..%35c../winnt/system32/cmd.exe?/c+dir GET /scripts/..%5c../winnt/system32/cmd.exe?/c+dir GET /scripts/..%2f../winnt/system32/cmd.exe?/c+dir
- A. The Morris worm
- B. The PIF virus
- C. Trinoo
- D. Nimda
- E. Code Red
- F. Ping of Death
Answer: D
Explanation:
The Nimda worm modifies all web content files it finds. As a result, any user browsing web content on the system, whether via the file system or via a web server, may download a copy of the worm. Some browsers may automatically execute the downloaded copy, thereby, infecting the browsing system. The high scanning rate of the Nimda worm may also cause bandwidth denial-of-service conditions on networks with infected machines and allow intruders the ability to execute arbitrary commands within the Local System security context on machines running the unpatched versions of IIS.
NEW QUESTION 14
To what does “message repudiation” refer to what concept in the realm of email security?
- A. Message repudiation means a user can validate which mail server or servers a message was passed through.
- B. Message repudiation means a user can claim damages for a mail message that damaged their reputation.
- C. Message repudiation means a recipient can be sure that a message was sent from a particular person.
- D. Message repudiation means a recipient can be sure that a message was sent from a certain host.
- E. Message repudiation means a sender can claim they did not actually send a particular message.
Answer: E
Explanation:
A quality that prevents a third party from being able to prove that a communication between two other parties ever took place. This is a desirable quality if you do not want your communications to be traceable.
Non-repudiation is the opposite quality—a third party can prove that a communication between two other parties took place. Non-repudiation is desirable if you want to be able to trace your communications and prove that they occurred. Repudiation – Denial of message submission or delivery.
NEW QUESTION 15
"Testing the network using the same methodologies and tools employed by attackers" Identify the correct terminology that defines the above statement.
- A. Vulnerability Scanning
- B. Penetration Testing
- C. Security Policy Implementation
- D. Designing Network Security
Answer: B
NEW QUESTION 16
Which of the following is an attack in which a secret value like a hash is captured and then reused at a later time to gain access to a system without ever decrypting or decoding the hash.
- A. Replay Attacks
- B. Brute Force Attacks
- C. Cryptography Attacks
- D. John the Ripper Attacks
Answer: A
Explanation:
A replay attack is a form of network attack in which a valid data transmission is maliciously or fraudulently repeated or delayed. This is carried out either by the originator or by an adversary who intercepts the data and retransmits it.
NEW QUESTION 17
What is SYSKEY # of bits used for encryption?
- A. 40
- B. 64
- C. 128
- D. 256
Answer: C
Explanation:
System Key hotfix is an optional feature which allows stronger encryption of SAM. Strong encryption protects private account information by encrypting the password data using a 128-bit cryptographically random key, known as a password encryption key.
NEW QUESTION 18
A zone file consists of which of the following Resource Records (RRs)?
- A. DNS, NS, AXFR, and MX records
- B. DNS, NS, PTR, and MX records
- C. SOA, NS, AXFR, and MX records
- D. SOA, NS, A, and MX records
Answer: D
Explanation:
The zone file typically contains the following records: SOA – Start Of Authority
NS – Name Server record MX – Mail eXchange record A – Address record
NEW QUESTION 19
There are two types of honeypots- high and low interaction. Which of these describes a low interaction honeypot?
Select the best answers.
- A. Emulators of vulnerable programs
- B. More likely to be penetrated
- C. Easier to deploy and maintain
- D. Tend to be used for production
- E. More detectable
- F. Tend to be used for research
Answer: ACDE
Explanation:
A low interaction honeypot would have emulators of vulnerable programs, not the real programs.
A high interaction honeypot is more likely to be penetrated as it is running the real program and is more vulnerable than an emulator.
Low interaction honeypots are easier to deploy and maintain. Usually you would just use a program that is already available for download and install it. Hackers don't usually crash or destroy these types of programs and it would require little maintenance.
A low interaction honeypot tends to be used for production.
Low interaction honeypots are more detectable because you are using emulators of the real programs. Many hackers will see this and realize that they are in a honeypot.
A low interaction honeypot tends to be used for production. A high interaction honeypot tends to be used for research.
NEW QUESTION 20
What type of attack is shown here?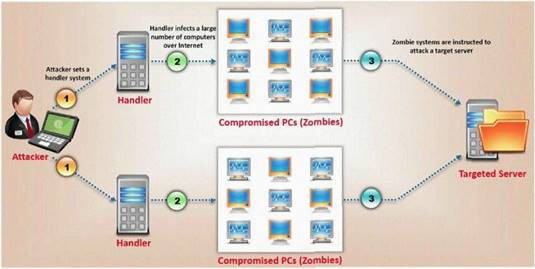
- A. Bandwidth exhaust Attack
- B. Denial of Service Attack
- C. Cluster Service Attack
- D. Distributed Denial of Service Attack
Answer: B
NEW QUESTION 21
You receive an e-mail with the following text message.
"Microsoft and HP today warned all customers that a new, highly dangerous virus has been discovered which will erase all your files at midnight. If there's a file called hidserv.exe on your computer, you have been infected and your computer is now running a hidden server that allows hackers to access your computer. Delete the file immediately. Please also pass this message to all your friends and colleagues as soon as possible."
You launch your antivirus software and scan the suspicious looking file hidserv.exe located in c:windows directory and the AV comes out clean meaning the file is not infected. You view the file signature and confirm that it is a legitimate Windows system file "Human Interface Device Service".
What category of virus is this?
- A. Virus hoax
- B. Spooky Virus
- C. Stealth Virus
- D. Polymorphic Virus
Answer: A
NEW QUESTION 22
____ is a tool that can hide processes from the process list, can hide files, registry entries, and intercept keystrokes.
- A. Trojan
- B. RootKit
- C. DoS tool
- D. Scanner
- E. Backdoor
Answer: B
Explanation:
Rootkits are tools that can hide processes from the process list, can hide files, registry entries, and intercept keystrokes.
NEW QUESTION 23
What is the key advantage of Session Hijacking?
- A. It can be easily done and does not require sophisticated skills.
- B. You can take advantage of an authenticated connection.
- C. You can successfully predict the sequence number generation.
- D. You cannot be traced in case the hijack is detected.
Answer: B
Explanation:
As an attacker you don’t have to steal an account and password in order to take advantage of an authenticated connection.
NEW QUESTION 24
Frederickson Security Consultants is currently conducting a security audit on the networks of Hawthorn Enterprises, a contractor for the Department of Defense. Since Hawthorn Enterprises conducts business daily with the federal government, they must abide by very stringent security policies. Frederickson is testing all of Hawthorn's physical and logical security measures including biometrics, passwords, and permissions. The federal government requires that all users must utilize random, non-dictionary passwords that must take at least 30 days to crack. Frederickson has confirmed that all Hawthorn employees use a random password generator for their network passwords. The Frederickson consultants have saved off numerous SAM files from Hawthorn's servers using Pwdump6 and are going to try and crack the network passwords. What method of attack is best suited
to crack these passwords in the shortest amount of time?
- A. Brute force attack
- B. Birthday attack
- C. Dictionary attack
- D. Brute service attack
Answer: A
NEW QUESTION 25
In an attempt to secure his wireless network, Bob implements a VPN to cover the wireless communications. Immediately after the implementation, users begin complaining about how slow the wireless network is. After benchmarking the network’s speed. Bob discovers that throughput has dropped by almost half even though the number of users has remained the same.
Why does this happen in the VPN over wireless implementation?
- A. The stronger encryption used by the VPN slows down the network.
- B. Using a VPN with wireless doubles the overhead on an access point for all direct client to access point communications.
- C. VPNs use larger packets then wireless networks normally do.
- D. Using a VPN on wireless automatically enables WEP, which causes additional overhead.
Answer: B
Explanation:
By applying VPN the access point will have to recalculate all headers destined for client and from clients twice.
NEW QUESTION 26
A simple compiler technique used by programmers is to add a terminator 'canary word' containing four letters NULL (0x00), CR (0x0d), LF (0x0a) and EOF (0xff) so that most string operations are terminated. If the canary word has been altered when the function returns, and the program responds by emitting an intruder alert into syslog, and then halts what does it indicate?
- A. The system has crashed
- B. A buffer overflow attack has been attempted
- C. A buffer overflow attack has already occurred
- D. A firewall has been breached and this is logged
- E. An intrusion detection system has been triggered
Answer: B
Explanation:
Terminator Canaries are based on the observation that most buffer overflows and stack smash attacks are based on certain string operations which end at terminators. The reaction to this observation is that the canaries are built of NULL terminators, CR, LF, and -1. The undesirable result is that the canary is known.
NEW QUESTION 27
......
P.S. Certshared now are offering 100% pass ensure 312-50 dumps! All 312-50 exam questions have been updated with correct answers: https://www.certshared.com/exam/312-50/ (765 New Questions)