Top Tips Of Up To Date H12-711_V3.0 Study Guides
We provide real H12-711_V3.0 exam questions and answers braindumps in two formats. Download PDF & Practice Tests. Pass HUAWEI H12-711_V3.0 Exam quickly & easily. The H12-711_V3.0 PDF type is available for reading and printing. You can print more and practice many times. With the help of our HUAWEI H12-711_V3.0 dumps pdf and vce product and material, you can easily pass the H12-711_V3.0 exam.
Check H12-711_V3.0 free dumps before getting the full version:
NEW QUESTION 1
Which of the following types of encryption technology can be divided into? (multiple choice)
- A. Symmetric encryption
- B. Symmetric encryption
- C. fingerprint encryption
- D. data encryption
Answer: AB
NEW QUESTION 2
About the packet iniptablesDescription of the transfer process, which of the following options is incorrect?
- A. When a packet enters the network card, it first goes to matchPREROUTINGchain
- B. If the destination address of the data packet is the local machine, the system will send the data packet toINPUTchain.
- C. If the destination address of the data packet is not the local machine, the system sends the data packet toOUTPUTchain
- D. If the destination address of the data packet is not the local machine, the system sends the data packet toFORWARDchain.
Answer: C
NEW QUESTION 3
As shown in the figure, the clientAand serverBestablished betweenTCPconnection, two places in the figure"?"The message sequence number should be which of the following?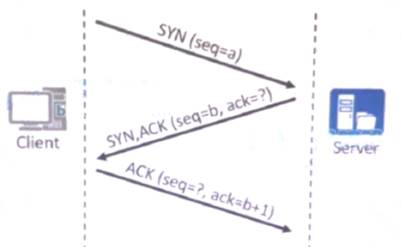
- A. a+1:a
- B. a:a+1
- C. b+1:b
- D. a+1:a+1
Answer: D
NEW QUESTION 4
SNMPWhat versions of the protocol are there? (multiple choice)
- A. SNMPv1
- B. SNMPv2b
- C. SNMPv2c
- D. SNMPv3
Answer: ACD
NEW QUESTION 5
On the surface, threats such as viruses, loopholes, and Trojan horses are the causes of information security incidents, but at the root, information security incidents are also closely related to people and the information system itself.
- A. True
- B. False
Answer: A
NEW QUESTION 6
aboutTCP/IPDescription of protocol stack packet decapsulation, which of the following is correct? (multiple choice)
- A. The data packet is first transmitted to the data link laye
- B. After parsing, the data link layer information is stripped, and the network layer information is known according to the parsing information, such as:IP
- C. transport layer (TCP) after receiving the data packet, the transport layer information is stripped after parsing, and the upper layer processing protocol is known according to the parsing information, such asUDP
- D. After the network layer receives the data packet, the network layer information is stripped after parsing, and the upper layer processing protocol is known according to the parsing information, such asHTTP
- E. After the application layer receives the data packet, the application layer information is stripped after parsing, and the final displayed user data is exactly the same as the data sent by the sender host
Answer: AD
NEW QUESTION 7
Which of the following are remote authentication methods? (multiple choice)
- A. RADIUS
- B. Local
- C. HWTACACS
- D. LLDP
Answer: AC
NEW QUESTION 8
Which of the following options are available for IPSec VPN peer authentication?
- A. Digital signature
- B. Digital certificate
- C. Digital envelope
- D. asymmetric key
Answer: ABC
NEW QUESTION 9
aboutNATAddress translation, which of the following statements is false?
- A. sourceNATconfiguration in technologyNATaddress pool, you can configure only one address poolIPaddress
- B. Address translation can be provided in the local area network according to the needs of usersFTP,WWW,Telnetand other services
- C. Some application layer protocols carry in the dataIPaddress information, make themNATWhen modifying the data in the upper layerIPAddress information
- D. for someTCP,UDPagreement (such asICMP,PPTP), cannot doNATconvert
Answer: D
NEW QUESTION 10
The key used by DES encryption is bits, while the key used by 3DES encryption is bits.
- A. 56168
- B. 64168
- C. 64128
- D. 56128
Answer: D
NEW QUESTION 11
When the user uses the session authentication method to trigger the firewall built-inPortalDuring authentication, users do not actively perform identity authentication, advanced service access, and device push"redirect"to the certification page
- A. True
- B. False
Answer: A
NEW QUESTION 12
In some scenarios, it is necessary toIPAddress conversion, but also to the purposeIPaddress translation, which of the following techniques is used in this scenario?
- A. two-wayNAT
- B. sourceNAT
- C. NAT-Server
- D. NAT ALG
Answer: A
NEW QUESTION 13
In the authentication policy of the firewall, ______ allows the user to not need to enter the user name and password, but can obtain the corresponding relationship between the user and the IP, so as to carry out policy management based on the user[fill in the blank]*
Solution:
Certification-free
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 14
Which of the following NAT technologies can implement a public network address to provide source address translation for multiple private network addresses ( )*
- A. NAPT
- B. NAT Server
- C. Easy-ipCT Jinglu
- D. NAT No-PAT
Answer: B
NEW QUESTION 15
When using passive mode to establish an FTP connection, the control channel uses port 20 and the data channel uses port 21. ( )[Multiple choice]*
- A. True
- B. False
Answer: B
NEW QUESTION 16
againstIPspoofing attack (IP Spoofing), which of the following is an error?
- A. IPSpoofing attacks are based onIPaddress trust relationship to initiate
- B. IPAfter a successful spoofing attack, the attacker can use forged arbitraryIPThe address impersonates a legitimate host to access key information
- C. The attacker needs to put the sourceIPlandaddress masquerading as a trusted host and sendSYNmarkNote the data segment request connection
- D. based onIPThe hosts in the trust relationship of the addresses can log in directly without entering password authentication.
Answer: C
NEW QUESTION 17
aboutVPN, which of the following statements is false?
- A. Virtual private network is cheaper than private line
- B. VPNTechnology necessarily involves encryption
- C. VPNTechnology is a technology that multiplexes logical channels on actual physical lines
- D. VPNThe emergence of technology allows traveling employees to remotely access internal corporate servers
Answer: B
NEW QUESTION 18
......
Recommend!! Get the Full H12-711_V3.0 dumps in VCE and PDF From Certleader, Welcome to Download: https://www.certleader.com/H12-711_V3.0-dumps.html (New 492 Q&As Version)