Far Out H12-711_V3.0 Testing Material For HCIA-Security V3.0 Certification
We provide real H12-711_V3.0 exam questions and answers braindumps in two formats. Download PDF & Practice Tests. Pass HUAWEI H12-711_V3.0 Exam quickly & easily. The H12-711_V3.0 PDF type is available for reading and printing. You can print more and practice many times. With the help of our HUAWEI H12-711_V3.0 dumps pdf and vce product and material, you can easily pass the H12-711_V3.0 exam.
Check H12-711_V3.0 free dumps before getting the full version:
NEW QUESTION 1
IPSEC VPNtechnology adoptionESPSecurity protocol encapsulation is not supportedNATcross becauseESPThe header of the message is encrypted
- A. True
- B. False
Answer: B
NEW QUESTION 2
In the architecture of PKI, ______ is the window for CA to face users, and is an extension of CA’s certificate issuance and management functions. He is responsible for accepting user’s certificate registration and revocation applications, reviewing employee identity information, and deciding Whether to submit an application to the CA to issue or revoke a digital certificate.[fill in the blank]*
Solution:
RA
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 3
Security policy conditions can be divided into multiple fields, such as source address, destination address, source port, destination port, etc.
"and"That is to say, this policy is hit only if the information in the packet matches all fields.
- A. True
- B. False
Answer: B
NEW QUESTION 4
In symmetric encryption algorithms, the algorithm is generally used on data communication channels, browsers or network links (). (fill in the blank)
Solution:
Stream cipher encryption
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 5
Which of the following options are suitable for business travelers to access the corporate intranet in the public network environment? ( )*
- A. L2 TP over IPSec VPN
- B. GER VPN
- C. MPLS VPN
- D. SSL VPN
Answer: AD
NEW QUESTION 6
Which of the following is false for a description of an intrusion detection system?.
- A. Intrusion detection system can collect a large amount of key information dynamically through network and computer.And can analyze and judge the current state of the entire system environment in time
- B. Once the intrusion detection system finds that there is a behavior that violates the security policy or the system has traces of being attacked, it can implement blocking operations.
- C. Intrusion detection system includes all hardware and software systems used for intrusion detection
- D. The immersion detection system can be linked with firewalls and switches, making it a powerful tool for firewalls"assistant", better and more precise control of traffic access between domains
Answer: C
NEW QUESTION 7
Using the ______ method of the Web proxy, the virtual gateway will encrypt the real URL that the user wants to access, and can adapt to different terminal types.[fill in the blank]*
Solution:
web rewrite
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 8
The steps of the security assessment method do not include which of the following?
- A. Manual audit
- B. Penetration testing
- C. Questionnaire
- D. data analysis
Answer: D
NEW QUESTION 9
Which of the following options are at risk from traffic-based attacks? (multiple choice)
- A. network down
- B. Server down
- C. data stolen
- D. The web page has been tampered with
Answer: AB
NEW QUESTION 10
Drag the phases of the cybersecurity emergency response on the left into the box on the right, and arrange them from top to bottom in the order of execution.[fill in the blank]*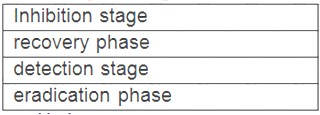
Solution:
3142
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 11
aboutNATConfiguration statement, which of the following is false?
- A. Configure sources in transparent modeNAT, the firewall does not supporteasy-ipWay
- B. in the address poolIPaddress can beNATserverpublic networkIPaddress overlap
- C. in the networkVoIPWhen doing business, no configuration is requiredNATALG
- D. Firewall does not supportESPandAHmessageNAPTconvert
Answer: D
NEW QUESTION 12
When an enterprise establishes its own information system, it checks each operation according to the authoritative standards formulated by the international, and can check whether its own information system is safe or not.
- A. True
- B. False
Answer: A
NEW QUESTION 13
Which of the following is true about the security policy configuration command?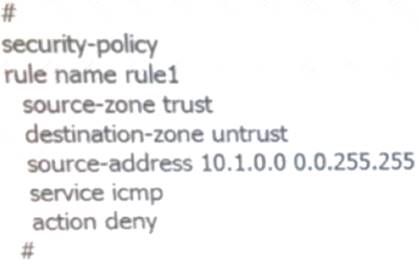
- A. prohibited fromtrustRegional accessuntrustarea and the destination address is 10.1.10.10hostICMPmessage
- B. prohibited fromtrustRegional accessuntrustarea and the destination address is10.1.0.0/16All hosts on the segmentICMPmessage
- C. prohibited fromtrustRegional accessuntrustregion and the source address is10.1.0.0/16All hosts from the network segmentICMPmessage
- D. prohibited fromtrustRegional accessuntrustregion and the source address is10.2.10.10All hosts from hostICMPmessage
Answer: C
NEW QUESTION 14
( ) is an "indirect intrusion attack. This attack mode is to virtually place a computer controlled by an intruder between two communicating computers in a network connection through various technical means. (fill in the blank)
Solution:
Man-in-the-middle attack
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 15
When A and B communicate with each other in data communication, if an asymmetric encryption algorithm is used for encryption, when A sends data to B, which of the following keys will be used for data encryption?
- A. A's public key
- B. A's private key
- C. B's public key
- D. B's private key
Answer: C
NEW QUESTION 16
In digital signature technology, we usually encrypt the digital fingerprint with the sender's ( ). (fill in the blank)
Solution:
Private key
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 17
In the construction of information security system, it is necessary to accurately describe the relationship between important aspects of security and system behavior through security models.
- A. True
- B. False
Answer: B
NEW QUESTION 18
......
Recommend!! Get the Full H12-711_V3.0 dumps in VCE and PDF From Downloadfreepdf.net, Welcome to Download: https://www.downloadfreepdf.net/H12-711_V3.0-pdf-download.html (New 492 Q&As Version)