The Far Out Guide To JN0-1332 Training Tools
It is impossible to pass Juniper JN0-1332 exam without any help in the short term. Come to Ucertify soon and find the most advanced, correct and guaranteed Juniper JN0-1332 practice questions. You will get a surprising result by our Avant-garde Security Design. Specialist (JNCDS-SEC) practice guides.
Check JN0-1332 free dumps before getting the full version:
NEW QUESTION 1
You are asked to design an automated vulnerability scanner that can actively check to see which ports are open and report on the findings. Which Junker Networks product would you use in this scenario7
- A. Security Director
- B. Log Director
- C. Policy Enforcer
- D. JSA
Answer: C
NEW QUESTION 2
Refer to the Exhibit.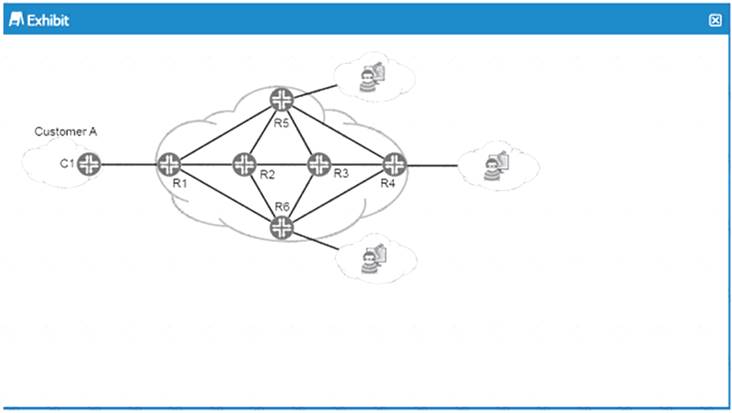
You are asked to provide a proposal for security elements in the service provider network shown in the exhibit. You must provide DOoS protection for Customer A from potential upstream attackers.
Which statements correct in this scenario?
- A. You should implement DDoS protection to drop offending traffic on the edge devices closest to the destination of the attack.
- B. You should implement DDoS protection to drop offending traffic on the edge devices closest to the source of the attack.
- C. You should implement DDoS protection to drop offending traffic on the core devices.
- D. You should implement DDoS protection to drop offending traffic on the customer edge device.
Answer: C
NEW QUESTION 3
You are a security architect for a small managed service provider. The marketing team has proposed providing firewall services to the customers.
The requirements for the solution are shown below
-- The customer must be able 10 manage their own security device.
-- You must provide segmentation using Layer 2 and Layer 3.
-- You need to implement dynamic routing
-- You need to provide UTM services
in this scenario. which product would you select to provide the firewall services?
- A. cSRX
- B. vSRX
- C. vMX
- D. vQFX
Answer: D
NEW QUESTION 4
You are asked to recommend a client remote access solution that provides direct network access and is the most secure When connection type accomplishes this task?
- A. GRE
- B. SSH
- C. PPTP
- D. IPsec
Answer: B
NEW QUESTION 5
A new virus is sheading across the Internet, with the potential to affect your customer's network
Which two statements describe how Policy Enforcer interacts with other devices to ensure that the network is protected in this scenario? (Choose two.)
- A. Policy Enforcer pulls security intelligence feeds from Juniper ATP Cloud to apply to SRX Series devices
- B. Policy Enforcer pulls security policies from Juniper ATP cloud and apples them to SRX Series devices
- C. Policy Enforcer automates the enrollment of SRX Series devices with Jumper ATP Cloud
- D. Security Director pulls security intelligence feeds from Juniper ATP Cloud and applies them to Policy Enforcer
Answer: B
NEW QUESTION 6
What are two considerations when performing a risk assessment for assets in a data center? (Choose two.)
- A. Insurance is a viable mitigation strategy when performing risk assessment calculations
- B. Exposure of assets could have larger economic impact man loss of assets
- C. Migration of a data center to a cloud prouder increases economic impact of asset loss
- D. Migration of a data center to a cloud provider reduces the economic impact of asset exposure
Answer: C
NEW QUESTION 7
You are asked to segment the networks connected to an SRX Series device into distinct logical groups with different security requirements.
How would you accomplish this task?
- A. Define different NAT policies for each network segment.
- B. Define different security policies for each network segment.
- C. Define different intrusion prevention policies for each network segment.
- D. Define different security zones for each network segment
Answer: B
NEW QUESTION 8
You must implement a solution to deploy end-to-end security services on network elements. Which solution will accomplish this task?
- A. Security Director
- B. Network Director
- C. JSA
- D. SRX Series devices
Answer: C
NEW QUESTION 9
You are asked to perform a risk assessment for a core layer switch in your data center. After analyze the Annual loss Expectancy (ALE) for this switch, you conclude that the risk remediation strategy involves purchasing insurance to protect against losses due to compromise or failure.
This scenario describes which risk remediation strategy?
- A. risk transfer
- B. risk mitigation
- C. risk avoidance
- D. risk acceptance
Answer: D
NEW QUESTION 10
You arc asked to proud a design proposal to secure a service provider's network against IP spoofing As part of your design, you must ensure that only traffic sourced from the same subnet is followed on the
customer-facing interfaces. Which solution will satisfy this requirement?
- A. BGP with source of origin community
- B. unicast RPF with strict mode
- C. unicast RPF with loose mode
- D. BGP labeled-unicast using the resolve-vpn option
Answer: B
NEW QUESTION 11
When two security services process a packet whether it is being processed in the first-packet path or the fast path? (Choose two.)
- A. screen options
- B. ALG
- C. route lookup
- D. policy lookup
Answer: CD
NEW QUESTION 12
What are two characteristics of an overlay network design? (Choose two.)
- A. The overlay network contains per-tenant state
- B. The overlay network uses tunnels to transfer traffic.
- C. The physical network contains per-tenant state.
- D. The physical network uses tunnels to transfer traffic
Answer: A
NEW QUESTION 13
When designing the security for a service provider core router, you are asked to add a firewall fitter on the to0 interface in this scenario, which two protocols would you want to allow through the filter? (Choose two.)
- A. LLDP
- B. SSH
- C. BGP
- D. STP
Answer: AC
NEW QUESTION 14
Which firewall service is used as a first line of defense and often used by a security device to protect itself?
- A. intrusion prevention system
- B. unified Threat management
- C. network address translation
- D. stateless firewall filter
Answer: A
NEW QUESTION 15
You are designing a service provider network. As part of your design you must ensure that the OSPF, BGP, and RSVP protocol communications are secured using the same authentication method. Which authentication protocol will accomplish this task?
- A. HMAC-MD5
- B. simple authentication
- C. SHA-RSA
- D. SHA-256
Answer: B
NEW QUESTION 16
......
100% Valid and Newest Version JN0-1332 Questions & Answers shared by Certleader, Get Full Dumps HERE: https://www.certleader.com/JN0-1332-dumps.html (New 65 Q&As)