All About Download PT0-002 Preparation Exams
Our pass rate is high to 98.9% and the similarity percentage between our PT0-002 study guide and real exam is 90% based on our seven-year educating experience. Do you want achievements in the CompTIA PT0-002 exam in just one try? I am currently studying for the CompTIA PT0-002 exam. Latest CompTIA PT0-002 Test exam practice questions and answers, Try CompTIA PT0-002 Brain Dumps First.
Online PT0-002 free questions and answers of New Version:
NEW QUESTION 1
Appending string values onto another string is called:
- A. compilation
- B. connection
- C. concatenation
- D. conjunction
Answer: C
NEW QUESTION 2
Which of the following would MOST likely be included in the final report of a static application-security test that was written with a team of application developers as the intended audience?
- A. Executive summary of the penetration-testing methods used
- B. Bill of materials including supplies, subcontracts, and costs incurred during assessment
- C. Quantitative impact assessments given a successful software compromise
- D. Code context for instances of unsafe type-casting operations
Answer: C
NEW QUESTION 3
A penetration tester is testing input validation on a search form that was discovered on a website. Which of the following characters is the BEST option to test the website for vulnerabilities?
- A. Comma
- B. Double dash
- C. Single quote
- D. Semicolon
Answer: C
NEW QUESTION 4
A penetration tester has obtained shell access to a Windows host and wants to run a specially crafted binary for later execution using the wmic.exe process call create function. Which of the following OS or filesystem mechanisms is MOST likely to support this objective?
- A. Alternate data streams
- B. PowerShell modules
- C. MP4 steganography
- D. PsExec
Answer: D
NEW QUESTION 5
Which of the following web-application security risks are part of the OWASP Top 10 v2017? (Choose two.)
- A. Buffer overflows
- B. Cross-site scripting
- C. Race-condition attacks
- D. Zero-day attacks
- E. Injection flaws
- F. Ransomware attacks
Answer: BE
Explanation:
A01-Injection
A02-Broken Authentication A03-Sensitive Data Exposure A04-XXE
A05-Broken Access Control A06-Security Misconfiguration A07-XSS
A08-Insecure Deserialization
A09-Using Components with Known Vulnerabilities A10-Insufficient Logging & Monitoring
NEW QUESTION 6
A penetration tester received a .pcap file to look for credentials to use in an engagement. Which of the following tools should the tester utilize to open and read the .pcap file?
- A. Nmap
- B. Wireshark
- C. Metasploit
- D. Netcat
Answer: B
NEW QUESTION 7
A consulting company is completing the ROE during scoping. Which of the following should be included in the ROE?
- A. Cost ofthe assessment
- B. Report distribution
- C. Testing restrictions
- D. Liability
Answer: B
NEW QUESTION 8
A compliance-based penetration test is primarily concerned with:
- A. obtaining Pll from the protected network.
- B. bypassing protection on edge devices.
- C. determining the efficacy of a specific set of security standards.
- D. obtaining specific information from the protected network.
Answer: C
NEW QUESTION 9
The results of an Nmap scan are as follows:
Starting Nmap 7.80 ( https://nmap.org ) at 2021-01-24 01:10 EST Nmap scan report for ( 10.2.1.22 )
Host is up (0.0102s latency). Not shown: 998 filtered ports Port State Service
80/tcp open http
|_http-title: 80F 22% RH 1009.1MB (text/html)
|_http-slowloris-check:
| VULNERABLE:
| Slowloris DoS Attack
| <..>
Device type: bridge|general purpose
Running (JUST GUESSING) : QEMU (95%)
OS CPE: cpe:/a:qemu:qemu
No exact OS matches found for host (test conditions non-ideal).
OS detection performed. Please report any incorrect results at https://nmap.org/submit/. Nmap done: 1 IP address (1 host up) scanned in 107.45 seconds
Which of the following device types will MOST likely have a similar response? (Choose two.)
- A. Network device
- B. Public-facing web server
- C. Active Directory domain controller
- D. IoT/embedded device
- E. Exposed RDP
- F. Print queue
Answer: AB
NEW QUESTION 10
A penetration tester has been hired to perform a physical penetration test to gain access to a secure room within a client’s building. Exterior reconnaissance identifies two entrances, a WiFi guest network, and multiple security cameras connected to the Internet.
Which of the following tools or techniques would BEST support additional reconnaissance?
- A. Wardriving
- B. Shodan
- C. Recon-ng
- D. Aircrack-ng
Answer: C
NEW QUESTION 11
Which of the following describe the GREATEST concerns about using third-party open-source libraries in application code? (Choose two.)
- A. The libraries may be vulnerable
- B. The licensing of software is ambiguous
- C. The libraries’ code bases could be read by anyone
- D. The provenance of code is unknown
- E. The libraries may be unsupported
- F. The libraries may break the application
Answer: AC
NEW QUESTION 12
A penetration tester ran an Nmap scan on an Internet-facing network device with the –F option and found a few open ports. To further enumerate, the tester ran another scan using the following command:
nmap –O –A –sS –p- 100.100.100.50
Nmap returned that all 65,535 ports were filtered. Which of the following MOST likely occurred on the second scan?
- A. A firewall or IPS blocked the scan.
- B. The penetration tester used unsupported flags.
- C. The edge network device was disconnected.
- D. The scan returned ICMP echo replies.
Answer: A
NEW QUESTION 13
Which of the following tools would be MOST useful in collecting vendor and other security-relevant information for IoT devices to support passive reconnaissance?
- A. Shodan
- B. Nmap
- C. WebScarab-NG
- D. Nessus
Answer: B
NEW QUESTION 14
A penetration tester ran the following commands on a Windows server: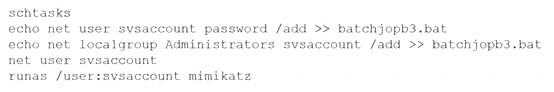
Which of the following should the tester do AFTER delivering the final report?
- A. Delete the scheduled batch job.
- B. Close the reverse shell connection.
- C. Downgrade the svsaccount permissions.
- D. Remove the tester-created credentials.
Answer: D
NEW QUESTION 15
During a penetration test, you gain access to a system with a limited user interface. This machine appears to have access to an isolated network that you would like to port scan.
INSTRUCTIONS
Analyze the code segments to determine which sections are needed to complete a port scanning script. Drag the appropriate elements into the correct locations to complete the script.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
Solution:
A picture containing shape Description automatically generated

A picture containing treemap chart Description automatically generated
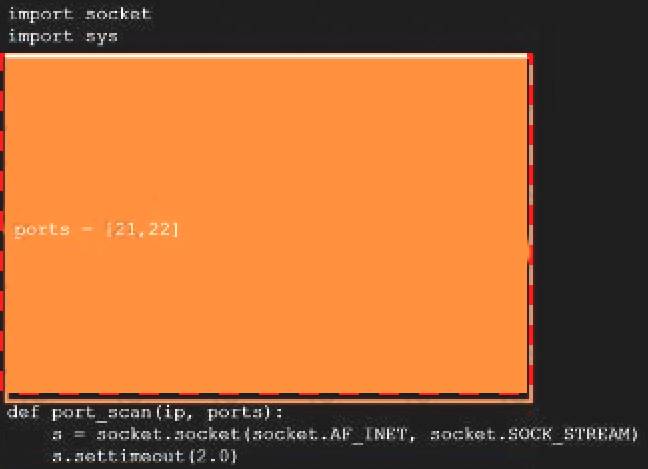
Text Description automatically generated
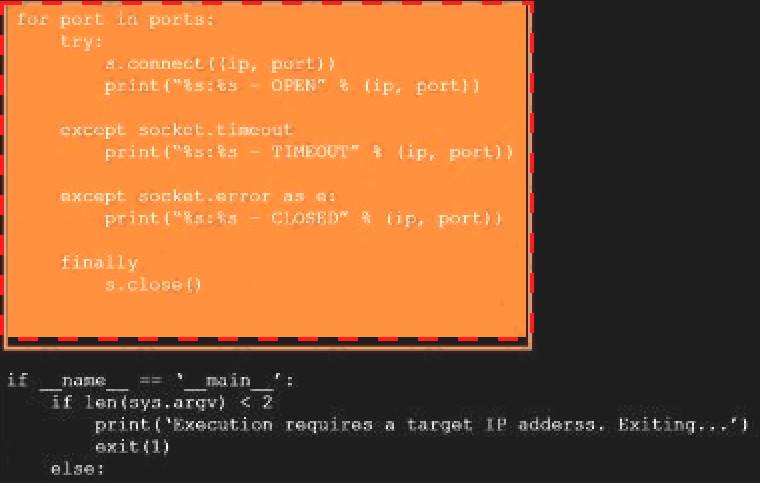
Graphical user interface Description automatically generated
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 16
......
P.S. Easily pass PT0-002 Exam with 110 Q&As Dumps-files.com Dumps & pdf Version, Welcome to Download the Newest Dumps-files.com PT0-002 Dumps: https://www.dumps-files.com/files/PT0-002/ (110 New Questions)