Update PT0-002 Practice Question For CompTIA PenTest+ Certification Exam Certification
Exam Code: PT0-002 (Practice Exam Latest Test Questions VCE PDF)
Exam Name: CompTIA PenTest+ Certification Exam
Certification Provider: CompTIA
Free Today! Guaranteed Training- Pass PT0-002 Exam.
Also have PT0-002 free dumps questions for you:
NEW QUESTION 1
A company becomes concerned when the security alarms are triggered during a penetration test. Which of the following should the company do NEXT?
- A. Halt the penetration test.
- B. Contact law enforcement.
- C. Deconflict with the penetration tester.
- D. Assume the alert is from the penetration test.
Answer: B
NEW QUESTION 2
A penetration tester conducted a vulnerability scan against a client’s critical servers and found the following: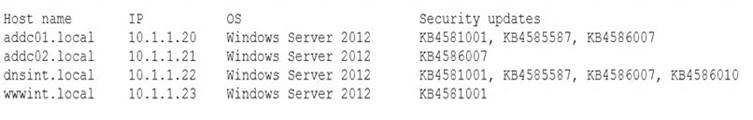
Which of the following would be a recommendation for remediation?
- A. Deploy a user training program
- B. Implement a patch management plan
- C. Utilize the secure software development life cycle
- D. Configure access controls on each of the servers
Answer: B
NEW QUESTION 3
A penetration tester would like to obtain FTP credentials by deploying a workstation as an on-path attack between the target and the server that has the FTP protocol. Which of the following methods would be the BEST to accomplish this objective?
- A. Wait for the next login and perform a downgrade attack on the server.
- B. Capture traffic using Wireshark.
- C. Perform a brute-force attack over the server.
- D. Use an FTP exploit against the server.
Answer: B
NEW QUESTION 4
A penetration tester has been given eight business hours to gain access to a client’s financial system. Which of the following techniques will have the highest likelihood of success?
- A. Attempting to tailgate an employee going into the client's workplace
- B. Dropping a malicious USB key with the company’s logo in the parking lot
- C. Using a brute-force attack against the external perimeter to gain a foothold
- D. Performing spear phishing against employees by posing as senior management
Answer: C
NEW QUESTION 5
A penetration tester recently completed a review of the security of a core network device within a corporate environment. The key findings are as follows:
• The following request was intercepted going to the network device: GET /login HTTP/1.1
Host: 10.50.100.16
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:31.0) Gecko/20100101 Firefox/31.0 Accept-Language: en-US,en;q=0.5
Connection: keep-alive
Authorization: Basic WU9VUilOQU1FOnNlY3JldHBhc3N3b3jk
• Network management interfaces are available on the production network.
• An Nmap scan returned the following: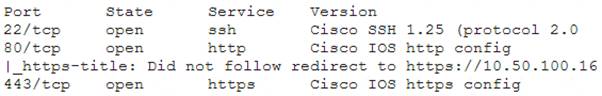
Which of the following would be BEST to add to the recommendations section of the final report? (Choose two.)
- A. Enforce enhanced password complexity requirements.
- B. Disable or upgrade SSH daemon.
- C. Disable HTTP/301 redirect configuration.
- D. Create an out-of-band network for management.
- E. Implement a better method for authentication.
- F. Eliminate network management and control interfaces.
Answer: CE
NEW QUESTION 6
You are a penetration tester reviewing a client’s website through a web browser. INSTRUCTIONS
Review all components of the website through the browser to determine if vulnerabilities are present. Remediate ONLY the highest vulnerability from either the certificate, source, or cookies.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
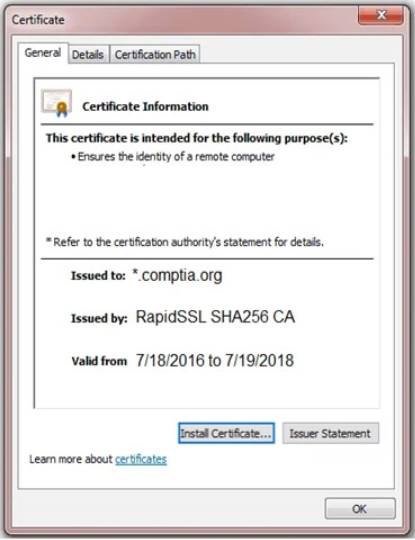
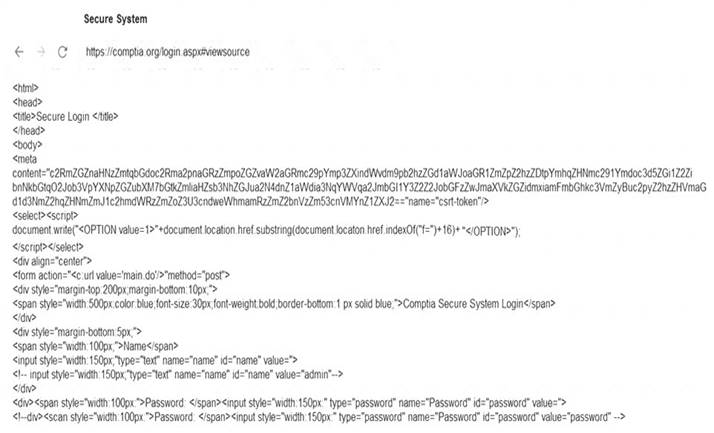
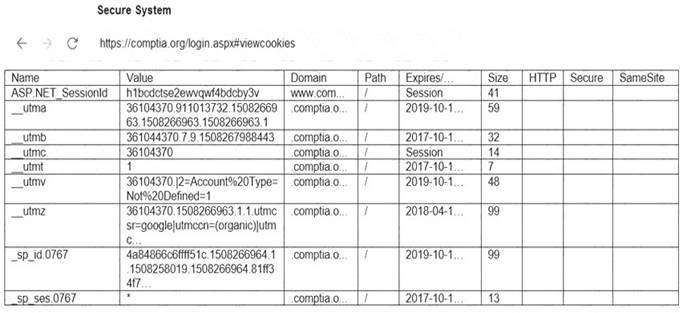
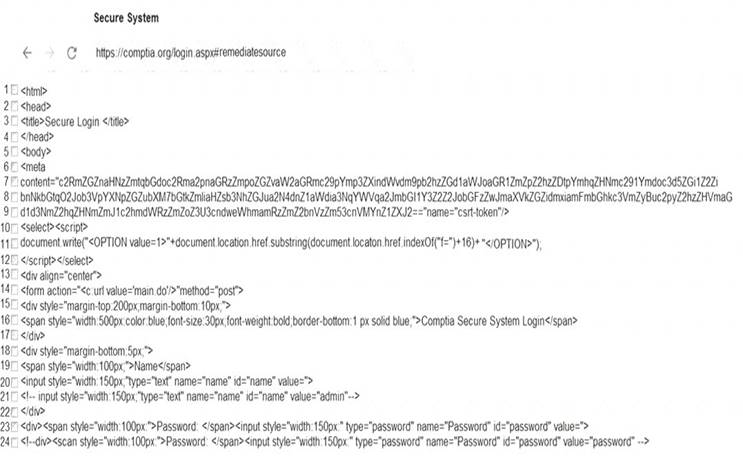
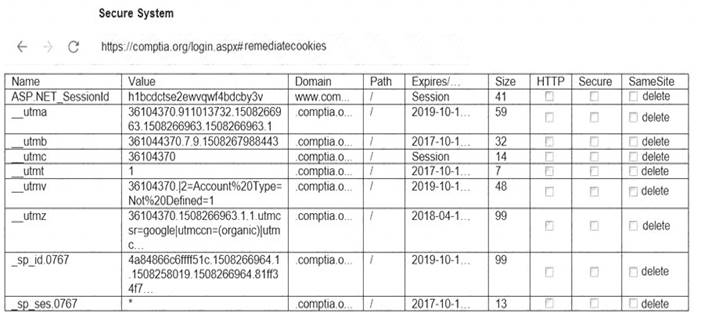
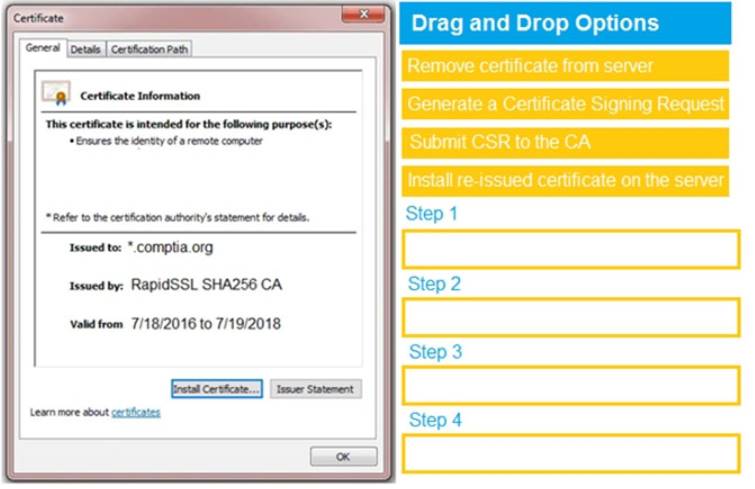
Solution:
Graphical user interface Description automatically generated
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 7
Which of the following documents describes specific activities, deliverables, and schedules for a penetration tester?
- A. NDA
- B. MSA
- C. SOW
- D. MOU
Answer: C
NEW QUESTION 8
A penetration tester discovers that a web server within the scope of the engagement has already been compromised with a backdoor. Which of the following should the penetration tester do NEXT?
- A. Forensically acquire the backdoor Trojan and perform attribution
- B. Utilize the backdoor in support of the engagement
- C. Continue the engagement and include the backdoor finding in the final report
- D. Inform the customer immediately about the backdoor
Answer: D
NEW QUESTION 9
A penetration tester runs the following command on a system:
find / -user root –perm -4000 –print 2>/dev/null
Which of the following is the tester trying to accomplish?
- A. Set the SGID on all files in the / directory
- B. Find the /root directory on the system
- C. Find files with the SUID bit set
- D. Find files that were created during exploitation and move them to /dev/null
Answer: C
NEW QUESTION 10
A penetration tester was able to gain access successfully to a Windows workstation on a mobile client’s laptop. Which of the following can be used to ensure the tester is able to maintain access to the system?
- A. schtasks /create /sc /ONSTART /tr C:\Temp\WindowsUpdate.exe
- B. wmic startup get caption,command
- C. crontab –l; echo “@reboot sleep 200 && ncat –lvp 4242 –e /bin/bash”) | crontab 2>/dev/null
- D. sudo useradd –ou 0 –g 0 user
Answer: B
NEW QUESTION 11
In the process of active service enumeration, a penetration tester identifies an SMTP daemon running on one of the target company’s servers. Which of the following actions would BEST enable the tester to perform phishing in a later stage of the assessment?
- A. Test for RFC-defined protocol conformance.
- B. Attempt to brute force authentication to the service.
- C. Perform a reverse DNS query and match to the service banner.
- D. Check for an open relay configuration.
Answer: C
NEW QUESTION 12
Which of the following provides a matrix of common tactics and techniques used by attackers along with recommended mitigations?
- A. NIST SP 800-53
- B. OWASP Top 10
- C. MITRE ATT&CK framework
- D. PTES technical guidelines
Answer: C
NEW QUESTION 13
Which of the following commands will allow a penetration tester to permit a shell script to be executed by the file owner?
- A. chmod u+x script.sh
- B. chmod u+e script.sh
- C. chmod o+e script.sh
- D. chmod o+x script.sh
Answer: A
NEW QUESTION 14
A penetration tester discovers during a recent test that an employee in the accounting department has been making changes to a payment system and redirecting money into a personal bank account. The penetration test was immediately stopped. Which of the following would be the BEST recommendation to prevent this type of activity in the future?
- A. Enforce mandatory employee vacations
- B. Implement multifactor authentication
- C. Install video surveillance equipment in the office
- D. Encrypt passwords for bank account information
Answer: B
NEW QUESTION 15
A penetration tester has been given an assignment to attack a series of targets in the 192.168.1.0/24 range, triggering as few alarms and countermeasures as possible.
Which of the following Nmap scan syntaxes would BEST accomplish this objective?
- A. nmap -sT -vvv -O 192.168.1.2/24 -PO
- B. nmap -sV 192.168.1.2/24 -PO
- C. nmap -sA -v -O 192.168.1.2/24
- D. nmap -sS -O 192.168.1.2/24 -T1
Answer: D
NEW QUESTION 16
......
P.S. Thedumpscentre.com now are offering 100% pass ensure PT0-002 dumps! All PT0-002 exam questions have been updated with correct answers: https://www.thedumpscentre.com/PT0-002-dumps/ (110 New Questions)