Updated SY0-501 Dump 2021
Exam Code: SY0-501 (Practice Exam Latest Test Questions VCE PDF)
Exam Name: CompTIA Security+ Certification Exam
Certification Provider: CompTIA
Free Today! Guaranteed Training- Pass SY0-501 Exam.
CompTIA SY0-501 Free Dumps Questions Online, Read and Test Now.
NEW QUESTION 1
During a data breach cleanup, it is discovered that not all of the sites involved have the necessary data wiping tools. The necessary tools are quickly distributed to the required technicians, but when should this problem BEST be revisited?
- A. Reporting
- B. Preparation
- C. Mitigation
- D. Lessons Learned
Answer: D
NEW QUESTION 2
Which of the following is used to validate the integrity of data?
- A. CBC
- B. Blowfish
- C. MD5
- D. RSA
Answer: C
NEW QUESTION 3
A supervisor in your organization was demoted on Friday afternoon. The supervisor had the ability to modify the contents of a confidential database, as well as other managerial permissions. On Monday morning, the database administrator reported that log files indicated that several records were missing from the database. Which of the following risk mitigation strategies should have been implemented when the supervisor was demoted?
- A. Incident management
- B. Routine auditing
- C. IT governance
- D. Monthly user rights reviews
Answer: D
NEW QUESTION 4
A company is developing a new system that will unlock a computer automatically when an authorized user sits in front of it, and then lock the computer when the user leaves. The user does not have to perform any action for this process to occur. Which of the following technologies provides this capability?
- A. Facial recognition
- B. Fingerprint scanner
- C. Motion detector
- D. Smart cards
Answer: A
NEW QUESTION 5
An analyst wants to implement a more secure wireless authentication for office access points. Which of the following technologies allows for encrypted authentication of wireless clients over TLS?
- A. PEAP
- B. EAP
- C. WPA2
- D. RADIUS
Answer: A
Explanation:
EAP by itself is only an authentication framework.
PEAP (Protected Extensible Authentication Protocol) fully encapsulates EAP and is designed to work within a TLS (Transport Layer Security) tunnel that may be encrypted but is authenticated. The primary motivation behind the creation of PEAP was to help correct the deficiencies discovered within EAP since that protocol assumes that the communications channel is protected. As a result, when EAP messages are able to be
discovered in the “clear” they do not provide the protection that was assumed when the protocol was originally authored.
PEAP, EAP-TTLS, and EAP-TLS “protect” inner EAP authentication within SSL/TLS sessions.
NEW QUESTION 6
Refer to the following code: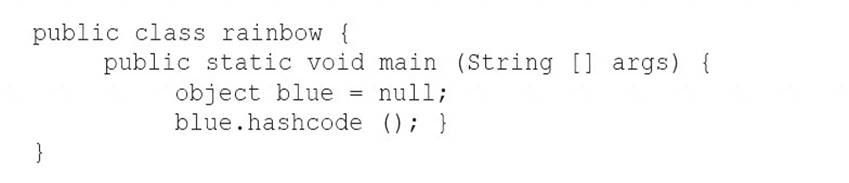
Which of the following vulnerabilities would occur if this is executed?
- A. Page exception
- B. Pointer deference
- C. NullPointerException
- D. Missing null check
Answer: D
NEW QUESTION 7
Joe, a user, wants to send Ann, another user, a confidential document electronically. Which of the following should Joe do to ensure the document is protected from eavesdropping?
- A. Encrypt it with Joe’s private key
- B. Encrypt it with Joe’s public key
- C. Encrypt it with Ann’s private key
- D. Encrypt it with Ann’s public key
Answer: D
NEW QUESTION 8
A security analyst has received the following alert snippet from the HIDS appliance: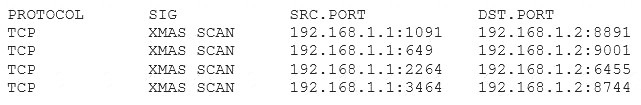
Given the above logs, which of the following is the cause of the attack?
- A. The TCP ports on destination are all open
- B. FIN, URG, and PSH flags are set in the packet header
- C. TCP MSS is configured improperly
- D. There is improper Layer 2 segmentation
Answer: B
NEW QUESTION 9
A company is using a mobile device deployment model in which employees use their personal devices for work at their own discretion. Some of the problems the company is encountering include the following: There is no standardization.
There is no standardization. Employees ask for reimbursement for their devices.
Employees ask for reimbursement for their devices. Employees do not replace their devices often enough to keep them running efficiently.
Employees do not replace their devices often enough to keep them running efficiently.  The company does not have enough control over the devices.
The company does not have enough control over the devices.
Which of the following is a deployment model that would help the company overcome these problems?
- A. BYOD
- B. VDI
- C. COPE
- D. CYOD
Answer: D
NEW QUESTION 10
A company’s loss control department identifies theft as a recurring loss type over the past year. Based on the department’s report, the Chief Information Officer (CIO) wants to detect theft of datacenter equipment. Which of the following controls should be implemented?
- A. Biometrics
- B. Cameras
- C. Motion detectors
- D. Mantraps
Answer: C
NEW QUESTION 11
A vulnerability scanner that uses its running service’s access level to better assess vulnerabilities across multiple assets within an organization is performing a:
- A. Credentialed scan.
- B. Non-intrusive scan.
- C. Privilege escalation test.
- D. Passive scan.
Answer: A
NEW QUESTION 12
Malware that changes its binary pattern on specific dates at specific times to avoid detection is known as a (n):
- A. armored virus
- B. logic bomb
- C. polymorphic virus
- D. Trojan
Answer: C
NEW QUESTION 13
Which of the following scenarios BEST describes an implementation of non-repudiation?
- A. A user logs into a domain workstation and access network file shares for another department
- B. A user remotely logs into the mail server with another user's credentials
- C. A user sends a digitally signed email to the entire finance department about an upcoming meeting
- D. A user access the workstation registry to make unauthorized changes to enable functionality within an application
Answer: C
NEW QUESTION 14
A security administrator is developing training for corporate users on basic security principles for personal email accounts. Which of the following should be mentioned as the MOST secure way for password recovery?
- A. Utilizing a single Qfor password recovery
- B. Sending a PIN to a smartphone through text message
- C. Utilizing CAPTCHA to avoid brute force attacks
- D. Use a different e-mail address to recover password
Answer: B
NEW QUESTION 15
A business sector is highly competitive, and safeguarding trade secrets and critical information is paramount. On a seasonal basis, an organization employs temporary hires and contractor personnel to accomplish its mission objectives. The temporary and contract personnel require access to network resources only when on the clock. Which of the following account management practices are the BEST ways to manage these accounts?
- A. Employ time-of-day restrictions.
- B. Employ password complexity.
- C. Employ a random key generator strategy.
- D. Employ an account expiration strategy.
- E. Employ a password lockout policy
Answer: D
NEW QUESTION 16
Ann, a customer, is reporting that several important files are missing from her workstation. She recently
received communication from an unknown party who is requesting funds to restore the files. Which of the following attacks has occurred?
- A. Ransomware
- B. Keylogger
- C. Buffer overflow
- D. Rootkit
Answer: A
NEW QUESTION 17
A company wants to host a publicly available server that performs the following functions:  Evaluates MX record lookup
Evaluates MX record lookup Can perform authenticated requests for A and AAA records
Can perform authenticated requests for A and AAA records  Uses RRSIG
Uses RRSIG
Which of the following should the company use to fulfill the above requirements?
- A. DNSSEC
- B. SFTP
- C. nslookup
- D. dig
- E. LDAPS
Answer: A
Explanation:
DNS Security Extensions (DNSSEC) provides, among other things, cryptographic authenticity of responses using Resource Record Signatures (RRSIG) and authenticated denial of existence using Next-Secure (NSEC) and Hashed-NSEC records (NSEC3).
NEW QUESTION 18
The IT department needs to prevent users from installing untested applications. Which of the following would provide the BEST solution?
- A. Job rotation
- B. Least privilege
- C. Account lockout
- D. Antivirus
Answer: B
NEW QUESTION 19
Ann. An employee in the payroll department, has contacted the help desk citing multiple issues with her device, including: Slow performance
Slow performance Word documents, PDFs, and images no longer opening
Word documents, PDFs, and images no longer opening  A pop-up
A pop-up
Ann states the issues began after she opened an invoice that a vendor emailed to her. Upon opening the invoice, she had to click several security warnings to view it in her word processor. With which of the following is the device MOST likely infected?
- A. Spyware
- B. Crypto-malware
- C. Rootkit
- D. Backdoor
Answer: D
NEW QUESTION 20
AChief Information Officer (CIO) has decided it is not cost effective to implement safeguards against a known vulnerability. Which of the following risk responses does this BEST describe?
- A. Transference
- B. Avoidance
- C. Mitigation
- D. Acceptance
Answer: D
NEW QUESTION 21
A security administrator is trying to encrypt communication. For which of the following reasons should administrator take advantage of the Subject Alternative Name (SAM) attribute of a certificate?
- A. It can protect multiple domains
- B. It provides extended site validation
- C. It does not require a trusted certificate authority
- D. It protects unlimited subdomains
Answer: B
NEW QUESTION 22
Which of the following can be provided to an AAA system for the identification phase?
- A. Username
- B. Permissions
- C. One-time token
- D. Private certificate
Answer: A
NEW QUESTION 23
A penetration tester is crawling a target website that is available to the public. Which of the following represents the actions the penetration tester is performing?
- A. URL hijacking
- B. Reconnaissance
- C. White box testing
- D. Escalation of privilege
Answer: B
NEW QUESTION 24
A company hires a third-party firm to conduct an assessment of vulnerabilities exposed to the Internet. The firm informs the company that an exploit exists for an FTP server that had a version installed from eight years ago. The company has decided to keep the system online anyway, as no upgrade exists form the vendor.
Which of the following BEST describes the reason why the vulnerability exists?
- A. Default configuration
- B. End-of-life system
- C. Weak cipher suite
- D. Zero-day threats
Answer: B
NEW QUESTION 25
A technician is investigating a potentially compromised device with the following symptoms:  Browser slowness
Browser slowness Frequent browser crashes
Frequent browser crashes  Hourglass stuck
Hourglass stuck New search toolbar
New search toolbar Increased memory consumption
Increased memory consumption
Which of the following types of malware has infected the system?
- A. Man-in-the-browser
- B. Spoofer
- C. Spyware
- D. Adware
Answer: D
NEW QUESTION 26
Which of the following cryptography algorithms will produce a fixed-length, irreversible output?
- A. AES
- B. 3DES
- C. RSA
- D. MD5
Answer: D
NEW QUESTION 27
A security analyst is updating a BIA document. The security analyst notices the support vendor's time to replace a server hard drive went from eight hours to two hours. Given these new metrics, which of the following can be concluded? (Select TWO)
- A. The MTTR is faster.
- B. The MTTR is slower.
- C. The RTO has increased.
- D. The RTO has decreased.
- E. The MTTF has increased.
- F. The MTTF has decreased.
Answer: AD
NEW QUESTION 28
An auditor wants to test the security posture of an organization by running a tool that will display the following: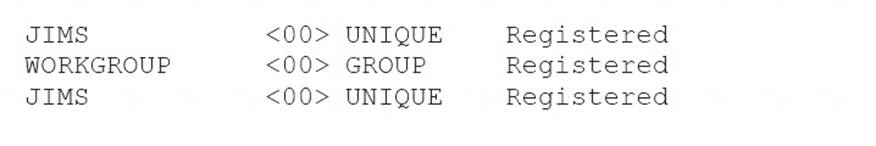
Which of the following commands should be used?
- A. nbtstat
- B. nc
- C. arp
- D. ipconfig
Answer: A
NEW QUESTION 29
A development team has adopted a new approach to projects in which feedback is iterative and multiple iterations of deployments are provided within an application’s full life cycle. Which of the following software development methodologies is the development team using?
- A. Waterfall
- B. Agile
- C. Rapid
- D. Extreme
Answer: B
NEW QUESTION 30
Which of the following could occur when both strong and weak ciphers are configured on a VPN concentrator? (Select TWO)
- A. An attacker could potentially perform a downgrade attack.
- B. The connection is vulnerable to resource exhaustion.
- C. The integrity of the data could be at risk.
- D. The VPN concentrator could revert to L2TP.
- E. The IPSec payload reverted to 16-bit sequence numbers.
Answer: AE
NEW QUESTION 31
......
Thanks for reading the newest SY0-501 exam dumps! We recommend you to try the PREMIUM 2passeasy SY0-501 dumps in VCE and PDF here: https://www.2passeasy.com/dumps/SY0-501/ (544 Q&As Dumps)