Cisco 100-105 Resource 2021
Realistic of 100-105 exam prep materials and answers for Cisco certification for IT professionals, Real Success Guaranteed with Updated 100-105 pdf dumps vce Materials. 100% PASS Cisco Interconnecting Cisco Networking Devices Part 1 (ICND1 v3.0) exam Today!
Check 100-105 free dumps before getting the full version:
NEW QUESTION 1
Which two commands must you apply to a router to configure it as a router-on-a-stick? (Choose two)
- A. vtp transparent
- B. encapsulation
- C. ip address
- D. spanning-tree portfast
- E. vtp domain
Answer: BC
NEW QUESTION 2
Which keyword in a NAT configuration enables the use of one outside IP address for multiple inside hosts?
- A. source
- B. static
- C. pool
- D. overload
Answer: D
NEW QUESTION 3
Which of the following are two local host characters?
- A. 32/prefix
- B. 255.255.255.0
- C. The administrative distance is 0
- D. Dynamically learned
Answer: AC
NEW QUESTION 4
Which value is calculated by the sender and receiver of a frame to determine whether the frame has been damaged in transit?
- A. the runt value
- B. the CRC value
- C. the giant value
- D. the collision value
Answer: B
NEW QUESTION 5
Which dynamic routing protocol uses only the hop count to determine the best path to a destination?
- A. IGRP
- B. RIP
- C. EIGRP
- D. OSPF
Answer: B
NEW QUESTION 6
When troubleshooting a LAN interface operating in full duplex mode, which error condition can be immediately ruled out?
- A. giants
- B. no buffers
- C. collisions
- D. ignored
- E. dribble condition
Answer: C
NEW QUESTION 7
Which Cisco IOS feature can dynamically assign IP addresses to hosts?
- A. DHCP Relay
- B. TFTP
- C. DNS
- D. DHCP
Answer: D
NEW QUESTION 8
In which circumstance is static routing most useful?
- A. on a stub network
- B. on a network with frequent routingchanges
- C. on a network that experiences frequent link failures
- D. on a large network that must share routes quickly between routers
Answer: A
NEW QUESTION 9
Instructions To configure the router (Gotha) click on the console host icon that is connected to a router by a serial console cable (shown in the diagram as a dashed black line).
You can click on the buttons below to view the different windows.
Each of the windows can be minimized by clicking on the [-]. You can also reposition a window by dragging it by the title bar.
The “Tab” key and most commands that use the “Control” or “Escape” keys are not supported and are not necessary to complete this simulation. The help command does not display all commands of the help system.
Scenario Central Florida Widgets recently installed a new router in their Gotha office. Complete the network installation by performing the initial router configurations and configuring RIPv2 routing using the router command line interface (CLI) on the Gotha router.
Configure the router per the following requirements: Name of the router is Gotha Enable-secret password is
mi222ke The password access user EXEC mode using the console is G8tors1 The password to allow telnet access to the router is dun63apIPv4 addresses must be configured as follows:
Ethernet network 209.165.201.0/27 – router has fourth assignable host address in subnet.
Serial network is 192.0.2.176/28 – router has last assignable host address in the subnet. Interface should be enabled. Routing protocol is RIPv2.
Attention: In practical examinations, please note the following, the actual information will prevail.
Name of the router is xxx
Enable. secret password is xxx
Password In access user EXEC mode using the console is xxx
The password to allow telnet access to the router is xxx
IP information
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
Router>enable Router#config terminal Router(config)#hostname Gotha
2) Enable-secret password (cisco10): Gotha(config)#enable secret mi222ke
3) Set the console password to G8tors1:
Gotha(config)#line console 0 Gotha(config-line)#password G8tors1 Gotha(config-line)#login Gotha(config-line)#exit
4) Set the Telnet password to dun63lap:
Gotha(config)#line vty 0 4 Gotha(config-line)#password dun63lap Gotha(config-line)#login Gotha(config-line)#exit
5) Configure Ethernet interface (on the right) of router Gotha: Ethernet network 209.165.201.0 /27 - Router has the fourth assignable host address in subnet. Ethernet Interface on router R2 is Fast Ethernet 0/0 as per the exhibit First we need to identify the subnet mask
Network: 209.165.201.0 /27 Subnet mask: /27: 27 bits = 8 + 8 + 8 + 3 =8(bits).8(bits).8(bits) .11100000
(3bits) =255.255.255.11100000 =11100000 = 128+64+32+0+0+0+0+0 = 224 Subnet mask: 255.255.255.224
Different subnet networks and there valid first and last assignable host address range for above subnet mask are Subnet Networks :::::: Valid Host address range :::::: Broadcast address
209.165.201.0 :::::: 209.165.201.1 - 209.165.201.30 ::::: 209.165.201.31
209.165.201.32 :::::: 209.165.201.33 - 209.165.201.62 ::::: 209.165.201.63
209.165.201.64 :::::: 209.165.201.65 - 209.165.201.94 :::::: 209.165.201.95
209.165.201.96 :::::: 209.165.201.97 - 209.165.201.126 :::::: 209.165.201.127
209.165.201.128 :::::: 209.165.201.129 - 209.165.201.158 :::::: 209.165.201.159
209.165.201.160 :::::: 209.165.201.161 - 209.165.201.190 :::::: 209.165.201.191
209.165.201.192 :::::: 209.165.201.193 - 209.165.201.222 :::::: 209.165.201.223
209. 165.201.224 :::::: 209.165.201.225 - 209.165.201.254 :::::: 209.165.201.255 Use above table information
for network 209.165.201.0 /27 to identify First assignable host address: 209.165.201.1 Last assignable host address: 209.165.201.30 Fourth assignable host address: 209.165.201.4
Assign the fourth assignable host address to Fa0/0 interface of Gotha router: Gotha(config)#interface Fa0/0 Gotha(config-if)#ip address 209.165.201.4 255.255.255.224
Gotha(config-if)#no shutdown Gotha(config-if)#exit
6) Configure Serial interface (on the left) of router Gotha: Serial Network is 192.0.2.176 /28 - Router has the last assignable host address in subnet. Serial Interface on R2 is Serial 0/0/0 as per the exhibit First we need to identify the subnet mask Network: 192.0.2.176 /28 Subnet mask: /28: 28bits = 8bits+8bits+8bits+4bits
=8(bits).8(bits).8(bits) .11110000 (4bits) =255.255.255.11100000 =11100000 = 128+64+32+16+0+0+0+0 =
240 Subnet mask: 255.255.255.240 Different subnet networks and there valid first and last assignable host address range for above subnet mask are Subnet Networks ::::: Valid Host address ::::::::::: Broadcast address
192.0.2.0 :::::: 192.0.2.1 - 192.0.2.14 ::::::: 192.0.2.15
192.0.2.16 ::::::: 192.0.2.17 - 192.0.2.30 ::::::: 192.0.2.31
192.0.2.32 :::::::: 192.0.2.33 - 192.0.2.46 :::::: 192.0.2.47
192.0.2.48 :::::: 192.0.2.49 - 192.0.2.62 ::::::: 192.0.2.64
192.0.2.64 ::::::: 192.0.2.65 - 192.0.2.78 ::::::: 192.0.2.79
192.0.2.80 :::::::: 192.0.2.81 - 192.0.2.94 :::::: 192.0.2.95
192.0.2.96 :::::: 192.0.2.97 - 192.0.2.110 ::::::: 192.0.2.111
192.0.2.112 ::::::: 192.0.2.113 - 192.0.2.126 ::::::: 192.0.2.127
192.0.2.128 :::::::: 192.0.2.129 - 192.0.2.142 :::::: 192.0.2.143
192.0.2.144 :::::: 192.0.2.145 - 192.0.2.158 ::::::: 192.0.2.159
192.0.2.160 ::::::: 192.0.2.161 - 192.0.2.174 ::::::: 192.0.2.175
192. 0.2.176 :::::::: 192.0.2.177 - 192.0.2.190 :::::: 192.0.2.191 and so on …. Use above table information for network 192.0.2.176 /28 to identify First assignable host address: 192.0.2.177 Last assignable host address: 192.0.2.190
We need to configure Last assignable host address (192.0.2.190) on serial 0/0/0 using the subnet mask 255.255.255.240 Assign the last assignable host address to S0/0/0 interface of Gotha router:
Gotha(config)#interface S0/0/0 (or use interface S0/0 if not successful)
Gotha(config-if)#ip address 192.0.2.190 255.255.255.240 Gotha(config-if)#no shutdown Gotha(config-if)#exit
7) Configure RIP v2 routing protocol:
Gotha(config)#router rip Gotha(config-router)#version 2 Gotha(config-router)#network 209.165.201.0 Gotha (config-router)#network 192.0.2.176 Gotha(config-router)#end Save the configuration: Gotha#copy
running-config startup-config Finally, you should use the ping command to verify all are working properly!
NEW QUESTION 10
Which two statements about syslog logging are true? (Choose two.)
- A. Messages are stored external to the device.
- B. The size of the log file is dependent on the resources of the device.
- C. Syslog logging is disabled by default.
- D. Messages can be erased when the device reboots.
- E. Messages are stored in the internal memory of the device.
Answer: AD
NEW QUESTION 11
Which field in a routing table entry is used to identify the immediate destination of a packet?
- A. next-hop
- B. metric
- C. administrative distance
- D. destination network
Answer: A
NEW QUESTION 12
Which command do you enter on a router running RIP so that it advertises a route on the same interface on which it received the route?
- A. no auto-summary
- B. no ip split-horizon
- C. passive-interface default
- D. ip rip v2-broadcast
Answer: B
NEW QUESTION 13
Which two steps are part of the IPv6 SLAAC address configuration process? (Choose two )
- A. The host uses the EUI-64 algorithm to calculate the first 64 bits of the destination IPv6 address
- B. The client performs duplicate address detection
- C. The router sends a solicitation message.
- D. The host sends a solicitation message
- E. The host combines the MAC addresses of the host and the router to generate a global unicast message.
Answer: AE
NEW QUESTION 14
A router with a default setting deployed, how will act if it received mistype command?
- A. Disable DNS look up
- B. Recognizing the command
- C. Try to resolve the command to an IP address
- D. Try to correct the command
- E. Show error message
Answer: C
NEW QUESTION 15
How does TCP differ from UDP? (Choose two.)
- A. TCP provides best effort delivery.
- B. TCP provides synchronized communication.
- C. TCP segments are essentially datagrams.
- D. TCP provides sequence numbering of packets.
- E. TCP uses broadcast delivery.
Answer: BD
Explanation:
Because TCP is a connection-oriented protocol responsible for ensuring the transfer of a datagram from the source to destination machine (end-to-end communications), TCP must receive communications messages from the destination machine to acknowledge receipt of the datagram. The term virtual circuit is usually used to refer to the handshaking that goes on between the two end machines, most of which are simple acknowledgment messages (either confirmation of receipt or a failure code) and datagram sequence numbers.
Rather than impose a state within the network to support the connection, TCP uses synchronized state between the two endpoints. This synchronized state is set up as part of an initial connection process, so TCP can be regarded as a connection-oriented protocol. Much of the protocol design is intended to ensure that each local state transition is communicated to, and acknowledged by, the remote party.
Reference: http://en.wikibooks.org/wiki/Communication_Networks/TCP_and_UDP_Protocols
NEW QUESTION 16
If you are in VLAN 10 and it gets a packet from VLAN 2 with 802.1q enabled, what does it do with the packet?
- A. Drops the packet
- B. forwards it to VLAN 2
- C. configures the port to handle traffic from VLAN 2
- D. adds it to the VLAN database
Answer: A
NEW QUESTION 17
Refer to the topology and switching table shown in the graphic.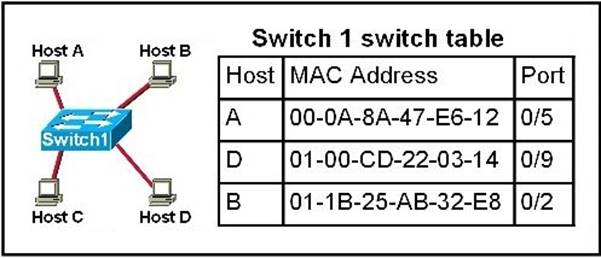
Host B sends a frame to Host C. What will the switch do with the frame?
- A. Drop the frame
- B. Send the frame out all ports except port 0/2
- C. Return the frame to Host B
- D. Send an ARP request for Host C
- E. Send an ICMP Host Unreachable message to Host B
- F. Record the destination MAC address in the switching table and send the frame directly to Host C
Answer: B
NEW QUESTION 18
Which value indicate the distance from the ntp authoritative time source?
- A. priority
- B. location
- C. layer
- D. stratum
Answer: D
NEW QUESTION 19
Which three statements about a mesh topology are true? (Choose Three)
- A. Every core device is connected to a distribution device.
- B. Every upstream distribution device is connected to an access switch
- C. Each access switch must be connected to exactly one upstream distribution device.
- D. Each access switch must be connected to at least one upstream distribution device and at least one core device D
- E. Each distribution device is connected to exactly one core device.
- F. Each access switch must be connected to at least two upstream distribution devices
Answer: ABF
NEW QUESTION 20
For which two protocols can PortFast alleviate potential host startup issues? (Choose two.)
- A. DHCP
- B. DNS
- C. OSPF
- D. RIP
- E. CDP
Answer: AE
NEW QUESTION 21
Which symptom most commonly indicates that two connecting interfaces are configured with a duplex mismatch?
- A. the spanning-tree process shutting down
- B. collisions on the interface
- C. an interface with a down/down status
- D. an interface with an up/down status
Answer: B
NEW QUESTION 22
Which commands display information about the Cisco IOS software version currently running on a router? (Choose three)
- A. show running-config
- B. show stacks
- C. show version
- D. show flash
- E. show protocols
- F. show IOS
Answer: ACD
NEW QUESTION 23
Which protocol uses a connection-oriented service to deliver files between end systems?
- A. TFTP
- B. DNS
- C. FTP
- D. SNMP
- E. RIP
Answer: C
Explanation:
TCP is an example of a connection-oriented protocol. It requires a logical connection to be
established between the two processes before data is exchanged. The connection must be maintained during the entire time that communication is taking place, then released afterwards. The process is much like a telephone call, where a virtual circuit is established-
-the caller must know the person's telephone number and the phone must be answered-- before the message can be delivered.
TCP/IP is also a connection-oriented transport with orderly release. With orderly release, any data remaining in the buffer is sent before the connection is terminated. The release is accomplished in a three-way handshake between client and server processes. The connection-oriented protocols in the OSI protocol suite, on the other hand, do not support orderly release. Applications perform any handshake necessary for ensuring orderly release.
Examples of services that use connection-oriented transport services are telnet, rlogin, and ftp.
NEW QUESTION 24
An administrator is working with the 192.168.4.0 netwrok, which has been subnetted with a /26 mask. Which two addresses can be assigned to hosts within the same subnet? (Choose two.)
- A. 192.168.4.67
- B. 192.168.4.61
- C. 192.168.4.128
- D. 192.168.4.132
- E. 192.168.4.125
- F. 192.168.4.63
Answer: AE
Explanation:
Only the values of host with 67 and 125 fall within the range of /26 CIDR subnet mask, all others lie beyond it.
NEW QUESTION 25
Which IPv4 address type can reach each node on a network?
- A. anaycast
- B. unicast
- C. multicast
- D. broadcast
Answer: B
NEW QUESTION 26
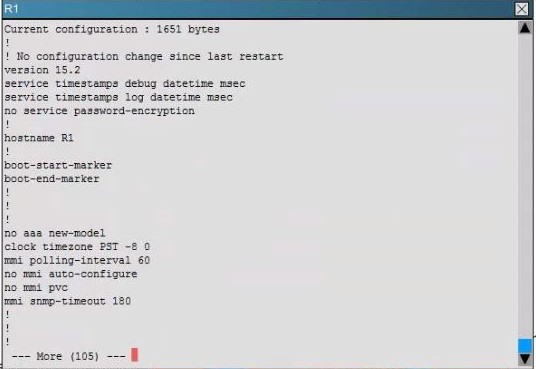
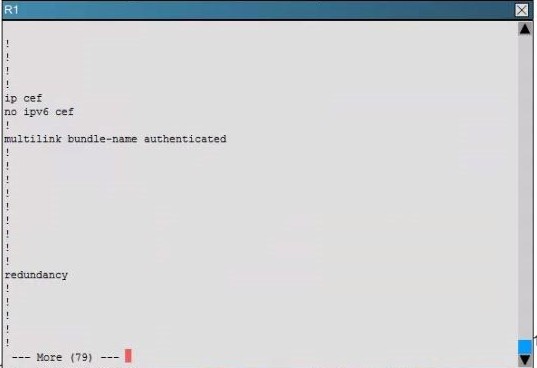
Scenario:
You are a junior network engineer for a financial company, and the main office network is experiencing network issues. Troubleshoot the network issues.
Router R1 connects the main office to the internet, and routers R2 and R3 are internal routers. NAT is enabled on router R1.
The routing protocol that is enabled between routers R1, R2 and R3 is RIPv2.
R1 sends the default route into RIPv2 for the internal routers to forward internet traffic to R1.
You have console access on R1, R2 and R3 devices. Use only show commands to troubleshoot the issues.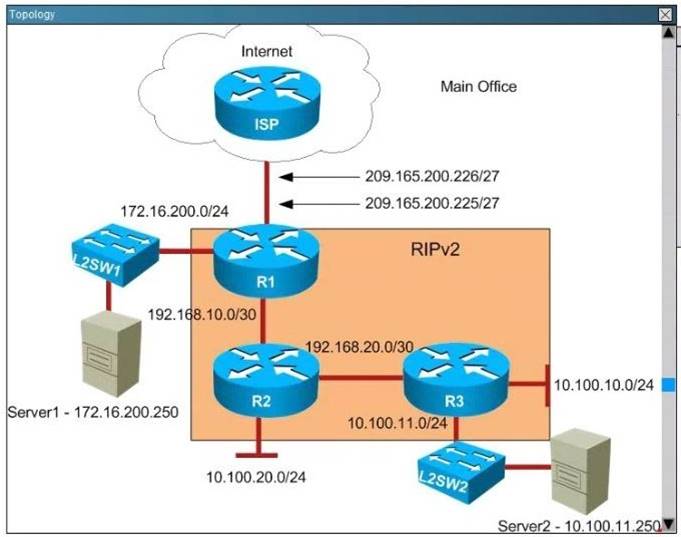
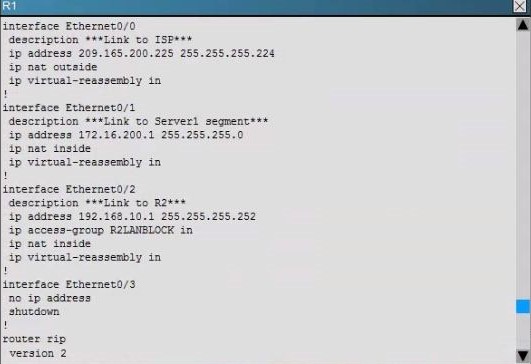
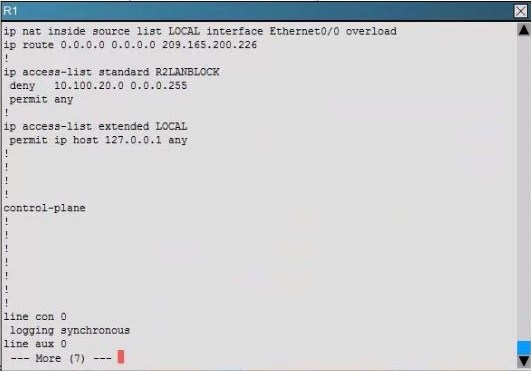
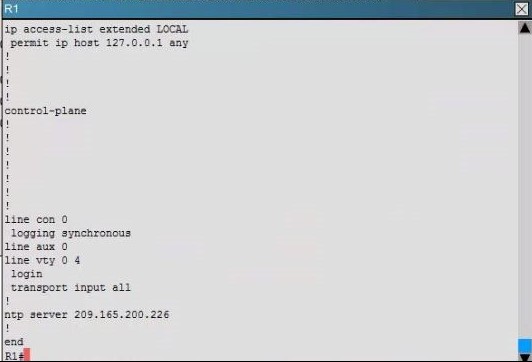
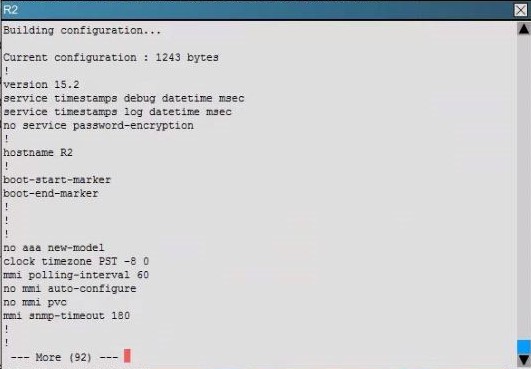
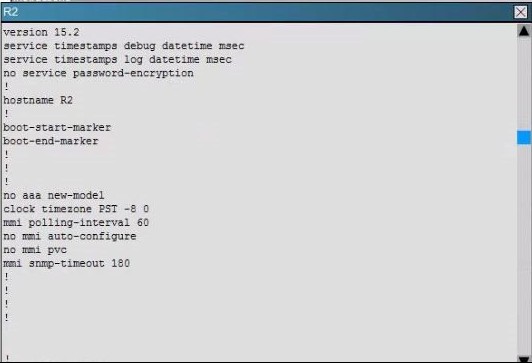
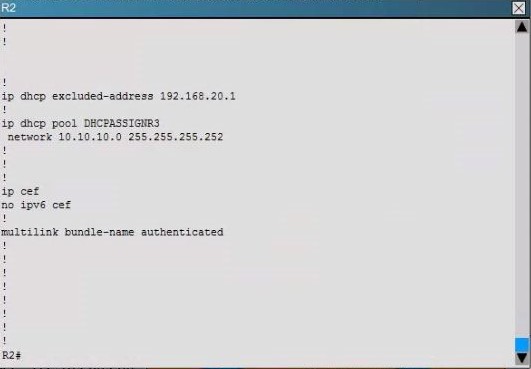
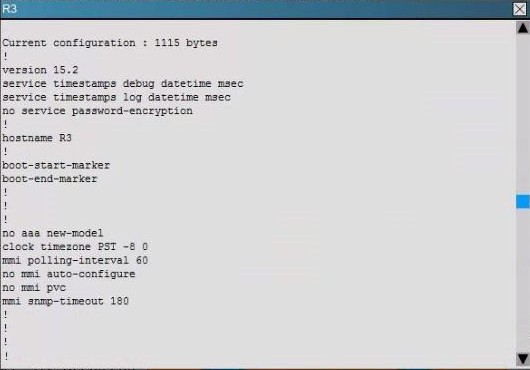
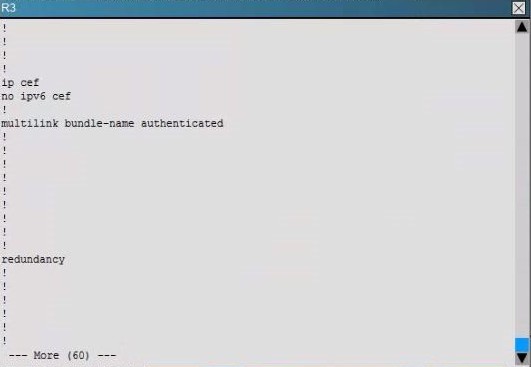
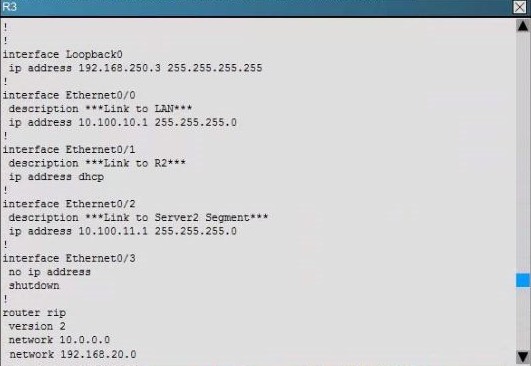
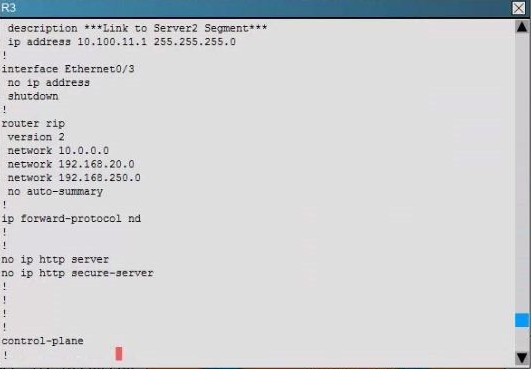
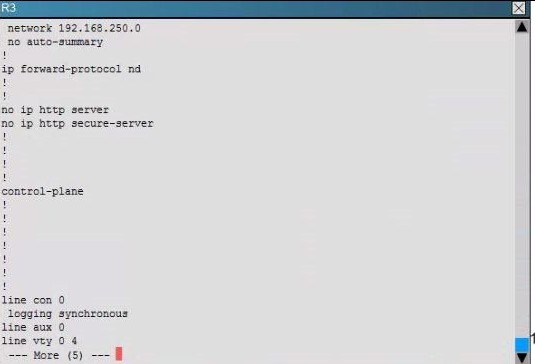
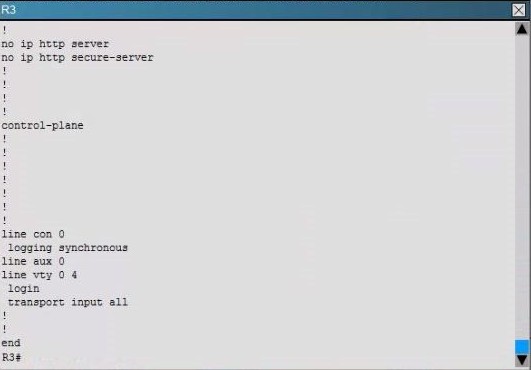
Users complain that they are unable to reach internet sites. You are troubleshooting internet connectivity problem at main office. Which statement correctly identifies the problem on Router R1?
- A. Interesting traffic for NAT ACL is incorrectly configured.
- B. NAT configurations on the interfaces are incorrectly configured
- C. NAT translation statement incorrectly configured.
- D. Only static NAT translation configured for the server, missing Dynamic NAT or Dynamic NAT overloading for internal networks.
Answer: B
Explanation: 
NEW QUESTION 27
......
Recommend!! Get the Full 100-105 dumps in VCE and PDF From Dumpscollection, Welcome to Download: http://www.dumpscollection.net/dumps/100-105/ (New 671 Q&As Version)