Pinpoint Check-Point 156-215.80 Training Tools Online
It is more faster and easier to pass the Check-Point 156-215.80 exam by using Actual Check-Point Check Point Certified Security Administrator questuins and answers. Immediate access to the Far out 156-215.80 Exam and find the same core area 156-215.80 questions with professionally verified answers, then PASS your exam with a high score now.
Free 156-215.80 Demo Online For Check-Point Certifitcation:
NEW QUESTION 1
When a packet arrives at the gateway, the gateway checks it against the rules in the top Policy Layer, sequentially from top to bottom, and enforces the first rule that matches a packet. Which of the following statements about the order of rule enforcement is true?
- A. If the Action is Accept, the gateway allows the packet to pass through the gateway.
- B. If the Action is Drop, the gateway continues to check rules in the next Policy Layer down.
- C. If the Action is Accept, the gateway continues to check rules in the next Policy Layer down.
- D. If the Action is Drop, the gateway applies the Implicit Clean-up Rule for that Policy Layer.
Answer: C
NEW QUESTION 2
You have successfully backed up your Check Point configurations without the OS information. What command would you use to restore this backup?
- A. restore_backup
- B. import backup
- C. cp_merge
- D. migrate import
Answer: A
NEW QUESTION 3
Which repositories are installed on the Security Management Server by SmartUpdate?
- A. License and Update
- B. Package Repository and Licenses
- C. Update and License and Contract
- D. License and Contract and Package Repository
Answer: D
NEW QUESTION 4
Which of the following is NOT a component of a Distinguished Name?
- A. Organization Unit
- B. Country
- C. Common name
- D. User container
Answer: D
Explanation:
Distinguished Name Components
CN=common name, OU=organizational unit, O=organization, L=locality, ST=state or province, C=country name
NEW QUESTION 5
MyCorp has the following NAT rules. You need to disable the NAT function when Alpha-internal networks try to reach the Google DNS (8.8.8.8) server.
What can you do in this case?
- A. Use manual NAT rule to make an exception
- B. Use the NAT settings in the Global Properties
- C. Disable NAT inside the VPN community
- D. Use network exception in the Alpha-internal network object
Answer: D
NEW QUESTION 6
Which feature is NOT provided by all Check Point Mobile Access solutions?
- A. Support for IPv6
- B. Granular access control
- C. Strong user authentication
- D. Secure connectivity
Answer: A
Explanation:
Types of Solutions
Enterprise-grade, secure connectivity to corporate resources.
Strong user authentication.
Granular access control. References:
NEW QUESTION 7
Look at the following screenshot and select the BEST answer.
- A. Clients external to the Security Gateway can download archive files from FTP_Ext server using FTP.
- B. Internal clients can upload and download any-files to FTP_Ext-server using FTP.
- C. Internal clients can upload and download archive-files to FTP_Ext server using FTP.
- D. Clients external to the Security Gateway can upload any files to the FTP_Ext-server using FTP.
Answer: A
NEW QUESTION 8
Why would an administrator see the message below?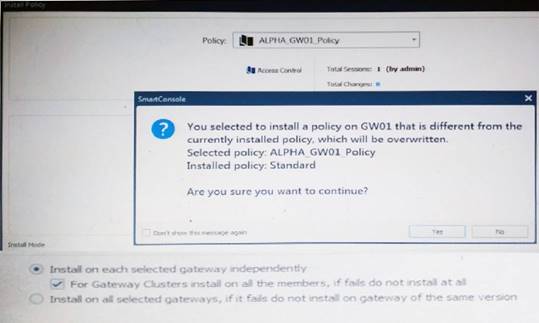
- A. A new Policy Package created on both the Management and Gateway will be deleted and must be packed up first before proceeding.
- B. A new Policy Package created on the Management is going to be installed to the existing Gateway.
- C. A new Policy Package created on the Gateway is going to be installed on the existing Management.
- D. A new Policy Package created on the Gateway and transferred to the management will be overwritten bythe Policy Package currently on the Gateway but can be restored from a periodic backup on the Gateway.
Answer: B
NEW QUESTION 9
AdminA and AdminB are both logged in on SmartConsole. What does it mean if AdminB sees a locked icon on a rule? Choose the BEST answer.
- A. Rule is locked by AdminA, because the save bottom has not been press.
- B. Rule is locked by AdminA, because an object on that rule is been edited.
- C. Rule is locked by AdminA, and will make it available if session is published.
- D. Rule is locked by AdminA, and if the session is saved, rule will be available
Answer: C
NEW QUESTION 10
Fill in the blank: The ____ is used to obtain identification and security information about network users.
- A. User Directory
- B. User server
- C. UserCheck
- D. User index
Answer: A
NEW QUESTION 11
The system administrator of a company is trying to find out why acceleration is not working for the traffic. The traffic is allowed according to the rule base and checked for viruses. But it is not accelerated. What is the most likely reason that the traffic is not accelerated?
- A. There is a virus foun
- B. Traffic is still allowed but not accelerated
- C. The connection required a Security server
- D. Acceleration is not enabled
- E. The traffic is originating from the gateway itself
Answer: D
NEW QUESTION 12
There are two R77.30 Security Gateways in the Firewall Cluster. They are named FW_A and FW_B. The cluster is configured to work as HA (High availability) with default cluster configuration. FW_A is configured to have higher priority than FW_B. FW_A was active and processing the traffic in the morning. FW_B was standby. Around 1100 am, its interfaces went down and this caused a failover. FW_B became active. After an hour, FW_A’s interface issues were resolved and it became operational. When it re-joins the cluster, will it become active automatically?
- A. No, since “maintain current active cluster member” option on the cluster object properties is enabled by default
- B. No, since “maintain current active cluster member” option is enabled by default on the Global Properties
- C. Yes, since “Switch to higher priority cluster member” option on the cluster object properties is enabled by default
- D. Yes, since “Switch to higher priority cluster member” option is enabled by default on the Global Properties
Answer: A
Explanation:
What Happens When a Security Gateway Recovers?
In a Load Sharing configuration, when the failed Security Gateway in a cluster recovers, all connections are redistributed among all active members. High Availability and Load Sharing in ClusterXL ClusterXL Administration Guide R77 Versions | 31 In a High Availability configuration, when the failed Security Gateway in a cluster recovers, the recovery method depends on the configured cluster setting. The options are:
• Maintain Current Active Security Gateway means that if one member passes on control to a lower priority member, control will be returned to the higher priority member only if the lower priority member fails. This mode is recommended if all members are equally capable of processing traffic, in order to minimize the number of failover events.
• Switch to Higher Priority Security Gateway means that if the lower priority member has control and the higher priority member is restored, then control will be returned to the higher priority member. This mode is recommended if one member is better equipped for handling connections, so it will be the default Security Gateway.
NEW QUESTION 13
Fill in the blank: To build an effective Security Policy, use a _____ and _____ rule.
- A. Cleanup; stealth
- B. Stealth; implicit
- C. Cleanup; default
- D. Implicit; explicit
Answer: A
NEW QUESTION 14
ABC Corp has a new administrator who logs into the Gaia Portal to make some changes. He realizes that even though he has logged in as an administrator, he is unable to make any changes because all configuration options are greyed out as shown in the screenshot image below. What is the likely cause for this?
- A. The Gaia /bin/confd is locked by another administrator from a SmartConsole session.
- B. The database is locked by another administrator SSH session.
- C. The Network address of his computer is in the blocked hosts.
- D. The IP address of his computer is not in the allowed hosts.
Answer: B
Explanation:
There is a lock on top left side of the screen. B is the logical answer.
NEW QUESTION 15
In Logging and Monitoring, the tracking options are Log, Detailed Log and Extended Log. Which of the following options can you add to each Log, Detailed Log and Extended Log?
- A. Accounting
- B. Suppression
- C. Accounting/Suppression
- D. Accounting/Extended
Answer: C
NEW QUESTION 16
What component of R80 Management is used for indexing?
- A. DBSync
- B. API Server
- C. fwm
- D. SOLR
Answer: D
NEW QUESTION 17
Which is a suitable command to check whether Drop Templates are activated or not?
- A. fw ctl get int activate_drop_templates
- B. fwaccel stat
- C. fwaccel stats
- D. fw ctl templates –d
Answer: B
NEW QUESTION 18
On R80.10 when configuring Third-Party devices to read the logs using the LEA (Log Export API) the default Log Server uses port:
- A. 18210
- B. 18184
- C. 257
- D. 18191
Answer: B
NEW QUESTION 19
Which tool CANNOT be launched from SmartUpdate R77?
- A. IP Appliance Voyager
- B. snapshot
- C. GAiA WebUI
- D. cpinfo
Answer: B
NEW QUESTION 20
Administrator Kofi has just made some changes on his Management Server and then clicks on the Publish button in SmartConsole but then gets the error message shown in the screenshot below.
Where can the administrator check for more information on these errors?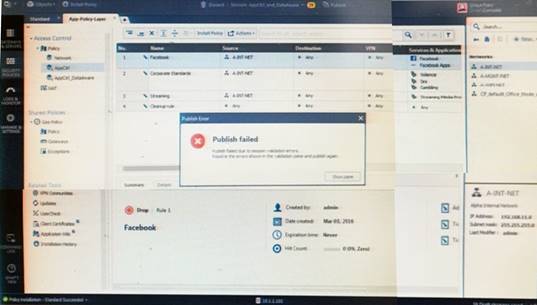
- A. The Log and Monitor section in SmartConsole
- B. The Validations section in SmartConsole
- C. The Objects section in SmartConsole
- D. The Policies section in SmartConsole
Answer: B
Explanation:
Validation Errors
The validations pane in SmartConsole shows configuration error messages. Examples of errors are object names that are not unique, and the use of objects that are not valid in the Rule Base.
To publish, you must fix the errors.
NEW QUESTION 21
Which of the following commands is used to verify license installation?
- A. Cplic verify license
- B. Cplic print
- C. Cplic show
- D. Cplic license
Answer: B
NEW QUESTION 22
Which utility allows you to configure the DHCP service on GAIA from the command line?
- A. ifconfig
- B. dhcp_cfg
- C. sysconfig
- D. cpconfig
Answer: C
Explanation:
Sysconfig Configuration Options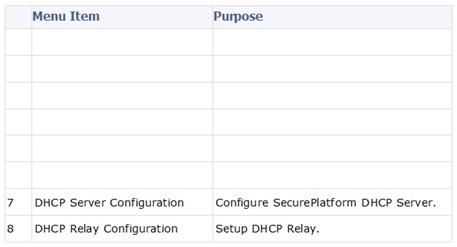
NEW QUESTION 23
What is the SOLR database for?
- A. Used for full text search and enables powerful matching capabilities
- B. Writes data to the database and full text search
- C. Serves GUI responsible to transfer request to the DLE server
- D. Enables powerful matching capabilities and writes data to the database
Answer: A
NEW QUESTION 24
WeBControl Layer has been set up using the settings in the following dialogue: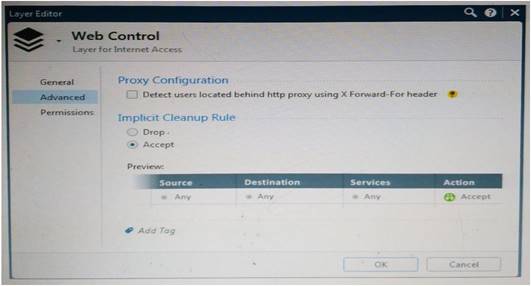
Consider the following policy and select the BEST answer.
- A. Traffic that does not match any rule in the subpolicy is dropped.
- B. All employees can access only Youtube and Vimeo.
- C. Access to Youtube and Vimeo is allowed only once a day.
- D. Anyone from internal network can access the internet, expect the traffic defined in drop rules 5.2, 5.5 and 5.6.
Answer: D
Explanation:
Policy Layers and Sub-Policies
R80 introduces the concept of layers and sub-policies, allowing you to segment your policy according to your network segments or business units/functions. In addition, you can also assign granular privileges by layer or sub-policy to distribute workload and tasks to the most qualified administrators
With layers, the rule base is organized into a set of security rules. These set of rules or layers, are inspected in the order in which they are defined, allowing control over the rule base flow and the security functionalities that take precedence. If an “accept” action is performed across a layer, the inspection will continue to the next layer. For example, a compliance layer can be created to overlay across a cross-section of rules.
Sub-policies are sets of rules that are created for a specific network segment, branch office or business unit, so if a rule is matched, inspection will continue through this subset of rules before it moves on to the next rule.
Sub-policies and layers can be managed by specific administrators, according to their permissions profiles. This facilitates task delegation and workload distribution.
NEW QUESTION 25
......
Recommend!! Get the Full 156-215.80 dumps in VCE and PDF From 2passeasy, Welcome to Download: https://www.2passeasy.com/dumps/156-215.80/ (New 485 Q&As Version)