Rebirth Check Point Certified Security Administrator 156-215.80 Test
Cause all that matters here is passing the Check-Point 156-215.80 exam. Cause all that you need is a high score of 156-215.80 Check Point Certified Security Administrator exam. The only one thing you need to do is downloading Passleader 156-215.80 exam study guides now. We will not let you down with our money-back guarantee.
Also have 156-215.80 free dumps questions for you:
NEW QUESTION 1
Which one of the following is the preferred licensing model? Select the Best answer.
- A. Local licensing because it ties the package license to the IP-address of the gateway and has no dependency of the Security Management Server.
- B. Central licensing because it ties the package license to the IP-address of the Security Management Server and has no dependency of the gateway.
- C. Local licensing because it ties the package license to the MAC-address of the gateway management interface and has no Security Management Server dependency.
- D. Central licensing because it ties the package license to the MAC-address of the Security Management Server Mgmt-interface and has no dependency of the gateway.
Answer: B
Explanation:
Central License
A Central License is a license attached to the Security Management server IP address, rather than the gatewa IP address. The benefits of a Central License are:
Only one IP address is needed for all licenses.
A license can be taken from one gateway and given to another.
The new license remains valid when changing the gateway IP address. There is no need to create and install a new license.
NEW QUESTION 2
Katie has been asked to do a backup on the Blue Security Gateway. Which command would accomplish this in the Gaia CLI?
- A. Blue > add local backup
- B. Expert&Blue#add local backing
- C. Blue > set backup local
- D. Blue > add backup local
Answer: D
NEW QUESTION 3
Which rule is responsible for the user authentication failure?
- A. Rule 4
- B. Rule 6
- C. Rule 3
- D. Rule 5
Answer: C
NEW QUESTION 4
What does the “unknown” SIC status shown on SmartConsole mean?
- A. The SMS can contact the Security Gateway but cannot establish Secure Internal Communication.
- B. SIC activation key requires a reset.
- C. The SIC activation key is not known by any administrator.
- D. There is no connection between the Security Gateway and SMS.
Answer: D
Explanation:
The most typical status is Communicating. Any other status indicates that the SIC communication is problematic. For example, if the SIC status is Unknown then there is no connection between the Gateway an the Security Management server. If the SIC status is Not Communicating, the Security Management server is able to contact the gateway, but SIC communication cannot be established.
NEW QUESTION 5
Examine the following Rule Base.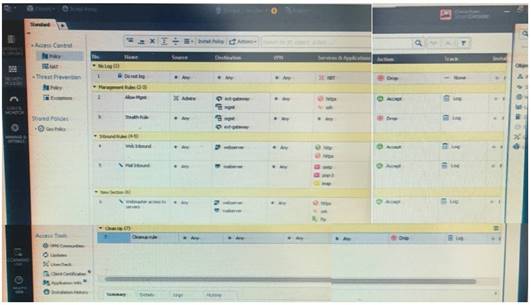
What can we infer about the recent changes made to the Rule Base?
- A. Rule 7 was created by the 'admin' administrator in the current session
- B. 8 changes have been made by administrators since the last policy installation
- C. The rules 1, 5 and 6 cannot be edited by the 'admin' administrator
- D. Rule 1 and object webserver are locked by another administrator
Answer: D
Explanation:
On top of the print screen there is a number "8" which consists for the number of changes made and not saved. Session Management Toolbar (top of SmartConsole)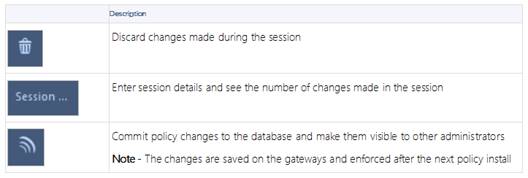
NEW QUESTION 6
Fill in the blank: When LDAP is integrated with Check Point Security Management, it is then referred to as ______
- A. UserCheck
- B. User Directory
- C. User Administration
- D. User Center
Answer: B
Explanation:
Check Point User Directory integrates LDAP, and other external user management technologies, with the Check Point solution. If you have a large user count, we recommend that you use an external user management database such as LDAP for enhanced Security Management Server performance.
NEW QUESTION 7
Which authentication scheme requires a user to possess a token?
- A. TACACS
- B. SecurID
- C. Check Point password
- D. RADIUS
Answer: B
Explanation:
SecurID
SecurID requires users to both possess a token authenticator and to supply a PIN or password References:
NEW QUESTION 8
Due to high CPU workload on the Security Gateway, the security administrator decided to purchase a new multicore CPU to replace the existing single core CPU. After installation, is the administrator required to perform any additional tasks?
- A. Go to clash-Run cpstop | Run cpstart
- B. Go to clash-Run cpconfig | Configure CoreXL to make use of the additional Cores | Exit cpconfig | Reboot Security Gateway
- C. Administrator does not need to perform any tas
- D. Check Point will make use of the newly installed CPU and Cores
- E. Go to clash-Run cpconfig | Configure CoreXL to make use of the additional Cores | Exit cpconfig | Reboot Security Gateway | Install Security Policy
Answer: B
NEW QUESTION 9
In what way is Secure Network Distributor (SND) a relevant feature of the Security Gateway?
- A. SND is a feature to accelerate multiple SSL VPN connections
- B. SND is an alternative to IPSec Main Mode, using only 3 packets
- C. SND is used to distribute packets among Firewall instances
- D. SND is a feature of fw monitor to capture accelerated packets
Answer: C
NEW QUESTION 10
Choose the Best place to find a Security Management Server backup file named backup_fw, on a Check Point Appliance.
- A. /var/log/Cpbackup/backups/backup/backup_fw.tgs
- B. /var/log/Cpbackup/backups/backup/backup_fw.tar
- C. /var/log/Cpbackup/backups/backups/backup_fw.tar
- D. /var/log/Cpbackup/backups/backup_fw.tgz
Answer: D
Explanation:
Gaia's Backup feature allows backing up the configuration of the Gaia OS and of the Security Management server database, or restoring a previously saved configuration. The configuration is saved to a .tgz file in the following directory:
Gaia OS Version Hardware
Local Directory R75.40 - R77.20
Check Point appliances
/var/log/CPbackup/backups/ Open Server
/var/CPbackup/backups/ R77.30
Check Point appliances
/var/log/CPbackup/backups/ Open Server
NEW QUESTION 11
Mesh and Star are two types of VPN topologies. Which statement below is TRUE about these types of communities?
- A. A star community requires Check Point gateways, as it is a Check Point proprietary technology.
- B. In a star community, satellite gateways cannot communicate with each other.
- C. In a mesh community, member gateways cannot communicate directly with each other.
- D. In a mesh community, all members can create a tunnel with any other member.
Answer: D
NEW QUESTION 12
Which of the following commands can be used to remove site-to-site IPSEC Security Associations (SA)?
- A. vpn tu
- B. vpn ipsec remove -l
- C. vpn debug ipsec
- D. fw ipsec tu
Answer: A
Explanation:
vpn tu
Description Launch the TunnelUtil tool which is used to control VPN tunnels.
Usage vpn tu vpn tunnelutil Example vpn tu Output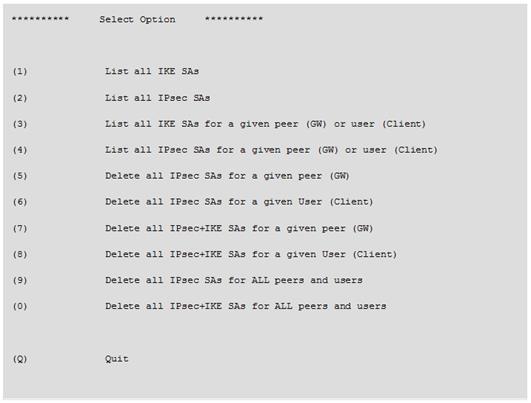
NEW QUESTION 13
Fill in the blank: Licenses can be added to the License and Contract repository _____.
- A. From the User Center, from a file, or manually
- B. From a file, manually, or from SmartView Monitor
- C. Manually, from SmartView Monitor, or from the User Center
- D. From SmartView Monitor, from the User Center, or from a file
Answer: A
NEW QUESTION 14
What is the BEST command to view configuration details of all interfaces in Gaia CLISH?
- A. ifconfig -a
- B. show interfaces
- C. show interfaces detail
- D. show configuration interface
Answer: D
NEW QUESTION 15
What needs to be configured if the NAT property ‘Translate destination on client side’ is not enabled in Global properties?
- A. A host route to route to the destination IP
- B. Use the file local.arp to add the ARP entries for NAT to work
- C. Nothing, the Gateway takes care of all details necessary
- D. Enabling ‘Allow bi-directional NAT’ for NAT to work correctly
Answer: C
NEW QUESTION 16
Which SmartConsole tab is used to monitor network and security performance?
- A. Manage Seeting
- B. Security Policies
- C. Gateway and Servers
- D. Logs and Monitor
Answer: C
NEW QUESTION 17
To enforce the Security Policy correctly, a Security Gateway requires:
- A. a routing table
- B. awareness of the network topology
- C. a Demilitarized Zone
- D. a Security Policy install
Answer: B
Explanation:
The network topology represents the internal network (both the LAN and the DMZ) protected by the gateway. The gateway must be aware of the layout of the network topology to:
Correctly enforce the Security Policy.
Ensure the validity of IP addresses for inbound and outbound traffic.
Configure a special domain for Virtual Private Networks.
NEW QUESTION 18
Tom has connected to the R80 Management Server remotely using SmartConsole and is in the process of making some Rule Base changes, when he suddenly loses connectivity. Connectivity is restored shortly afterward. What will happen to the changes already made:
- A. Tom’s changes will have been stored on the Management when he reconnects and he will not lose any of this work.
- B. Tom will have to reboot his SmartConsole computer, and access the Management cache store on that computer, which is only accessible after a reboot.
- C. Tom’s changes will be lost since he lost connectivity and he will have to start again.
- D. Tom will have to reboot his SmartConsole computer, clear the cache and restore changes.
Answer: A
NEW QUESTION 19
What action can be performed from SmartUpdate R77?
- A. upgrade_export
- B. fw stat -1
- C. cpinfo
- D. remote_uninstall_verifier
Answer: C
NEW QUESTION 20
DLP and Geo Policy are examples of what type of Policy?
- A. Standard Policies
- B. Shared Policies
- C. Inspection Policies
- D. Unified Policies
Answer: B
Explanation:
The Shared policies are installed with the Access Control Policy.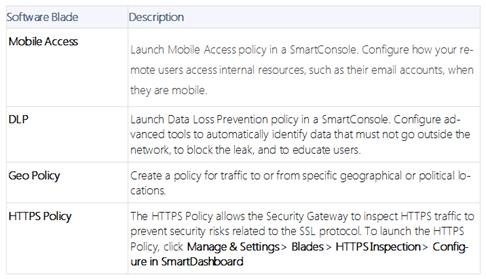
NEW QUESTION 21
You want to verify if there are unsaved changes in GAiA that will be lost with a reboot. What command can be used?
- A. show unsaved
- B. show save-state
- C. show configuration diff
- D. show config-state
Answer: D
NEW QUESTION 22
Fill in the blank: The tool ____ generates a R80 Security Gateway configuration report.
- A. infoCP
- B. infoview
- C. cpinfo
- D. fw cpinfo
Answer: C
Explanation:
CPInfo is an auto-updatable utility that collects diagnostics data on a customer's machine at the time of execution and uploads it to Check Point servers (it replaces the standalone cp_uploader utility for uploading files to Check Point servers).
The CPinfo output file allows analyzing customer setups from a remote location. Check Point support engineers can open the CPinfo file in a demo mode, while viewing actual customer Security Policies and Objects. This allows the in-depth analysis of customer's configuration and environment settings.
When contacting Check Point Support, collect the cpinfo files from the Security Management server and Security Gateways involved in your case.
NEW QUESTION 23
Which Check Point software blade prevents malicious files from entering a network using virus signatures and anomaly-based protections from ThreatCloud?
- A. Firewall
- B. Application Control
- C. Anti-spam and Email Security
- D. Antivirus
Answer: D
Explanation:
The enhanced Check Point Antivirus Software Blade uses real-time virus signatures and anomaly-based protections from ThreatCloud™, the first collaborative network to fight cybercrime, to detect and block malware at the gateway before users are affected.
NEW QUESTION 24
How many sessions can be opened on the Management Server at the same time?
- A. Unlimited, One per each licensed Gateway
- B. One
- C. Unlimited, Multiple per administrator
- D. Unlimited, One per administrator
Answer: D
NEW QUESTION 25
......
Thanks for reading the newest 156-215.80 exam dumps! We recommend you to try the PREMIUM 2passeasy 156-215.80 dumps in VCE and PDF here: https://www.2passeasy.com/dumps/156-215.80/ (485 Q&As Dumps)