Downloadable Check-Point 156-215.80 Practice Online
Our pass rate is high to 98.9% and the similarity percentage between our 156-215.80 study guide and real exam is 90% based on our seven-year educating experience. Do you want achievements in the Check-Point 156-215.80 exam in just one try? I am currently studying for the Check-Point 156-215.80 exam. Latest Check-Point 156-215.80 Test exam practice questions and answers, Try Check-Point 156-215.80 Brain Dumps First.
Also have 156-215.80 free dumps questions for you:
NEW QUESTION 1
VPN gateways must authenticate to each other prior to exchanging information. What are the two types of credentials used for authentication?
- A. 3DES and MD5
- B. Certificates and IPsec
- C. Certificates and pre-shared secret
- D. IPsec and VPN Domains
Answer: C
NEW QUESTION 2
While enabling the Identity Awareness blade the Identity Awareness wizard does not automatically detect the windows domain. Why does it not detect the windows domain?
- A. Security Gateways is not part of the Domain
- B. SmartConsole machine is not part of the domain
- C. SMS is not part of the domain
- D. Identity Awareness is not enabled on Global properties
Answer: B
Explanation:
To enable Identity Awareness:
Log in to SmartDashboard.
From the Network Objects tree, expand the Check Poinbtranch.
Double-click the Security Gateway on which to enable Identity Awareness.
In the Software Blades section, select Identity Awarenesosn the Network Security tab. The Identity Awareness Configuration wizard opens.
Select one or more options. These options set the methods for acquiring identities of managed and unmanaged assets.
AD Query - Lets the Security Gateway seamlessly identify Active Directory users and computers.
Browser-Based Authentication - Sends users to a Web page to acquire identities from unidentified users. If Transparent Kerberos Authentication is configured, AD users may be identified transparently.
Terminal Servers - Identify users in a Terminal Server environment (originating from one IP address).
See Choosing Identity Sources.
Note - When you enable Browser-Based Authentication on a Security Gateway that is on an IP Series appliance, make sure to set the Voyager management application port to a port other than 443 or 80.
Click Next.
The Integration With Active Directory window opens.
When SmartDashboard is part of the domain, SmartDashboard suggests this domain automatically. If you select this domain, the system creates an LDAP Account Unit with alolf the domain controllers in the organization's Active Directory.
NEW QUESTION 3
You noticed that CPU cores on the Security Gateway are usually 100% utilized and many packets were dropped. You don’t have a budget to perform a hardware upgrade at this time. To optimize drops you decide to use Priority Queues and fully enable Dynamic Dispatcher. How can you enable them?
- A. fw ctl multik dynamic_dispatching on
- B. fw ctl multik dynamic_dispatching set_mode 9
- C. fw ctl multik set_mode 9
- D. fw ctl miltik pq enable
Answer: C
NEW QUESTION 4
Fill in the blank: Service blades must be attached to a _____ .
- A. Security Gateway
- B. Management container
- C. Management server
- D. Security Gateway container
Answer: A
NEW QUESTION 5
Your company enforces a strict change control policy. Which of the following would be MOST effective for quickly dropping an attacker's specific active connection?
- A. Change the Rule Base and install the Policy to all Security Gateways
- B. Block Intruder feature of SmartView Tracker
- C. Intrusion Detection System (IDS) Policy install
- D. SAM – Suspicious Activity Rules feature of SmartView Monitor
Answer: B
NEW QUESTION 6
When using Monitored circuit VRRP, what is a priority delta?
- A. When an interface fails the priority changes to the priority delta
- B. When an interface fails the delta claims the priority
- C. When an interface fails the priority delta is subtracted from the priority
- D. When an interface fails the priority delta decides if the other interfaces takes over
Answer: C
NEW QUESTION 7
The Firewall kernel is replicated multiple times, therefore:
- A. The Firewall kernel only touches the packet if the connection is accelerated
- B. The Firewall can run different policies per core
- C. The Firewall kernel is replicated only with new connections and deletes itself once the connection times out
- D. The Firewall can run the same policy on all cores
Answer: D
NEW QUESTION 8
Which of the following is NOT an attribute of packer acceleration?
- A. Source address
- B. Protocol
- C. Destination port
- D. Application Awareness
Answer: D
NEW QUESTION 9
Which of the following is NOT an option to calculate the traffic direction?
- A. Incoming
- B. Internal
- C. External
- D. Outgoing
Answer: D
NEW QUESTION 10
Fill in the blanks: In the Network policy layer, the default action for the Implied last rule is ___ all traffic. However, in the Application Control policy layer, the default action is _____ all traffic.
- A. Accept; redirect
- B. Accept; drop
- C. Redirect; drop
- D. Drop; accept
Answer: D
NEW QUESTION 11
In order to modify Security Policies the administrator can use which of the following tools? Select the BEST answer.
- A. Command line of the Security Management Server or mgmt_cli.exe on any Windows computer.
- B. SmartConsole and WebUI on the Security Management Server.
- C. mgmt_cli or WebUI on Security Gateway and SmartConsole on the Security Management Server.
- D. SmartConsole or mgmt_cli on any computer where SmartConsole is installed.
Answer: D
NEW QUESTION 12
Can multiple administrators connect to a Security Management Server at the same time?
- A. No, only one can be connected
- B. Yes, all administrators can modify a network object at the same time
- C. Yes, every administrator has their own username, and works in a session that is independent of other administrators
- D. Yes, but only one has the right to write
Answer: C
NEW QUESTION 13
You want to define a selected administrator's permission to edit a layer. However, when you click the + sign in the “Select additional profile that will be able edit this layer” you do not see anything. What is the most likely cause of this problem? Select the BEST answer.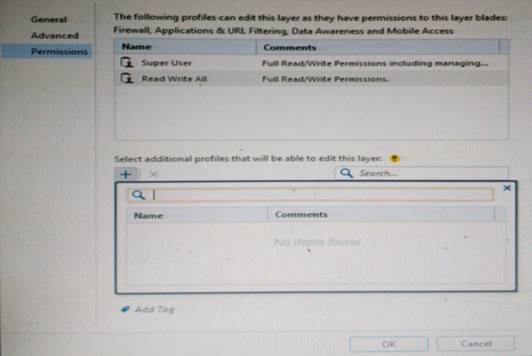
- A. “Edit layers by Software Blades” is unselected in the Permission Profile
- B. There are no permission profiles available and you need to create one first.
- C. All permission profiles are in use.
- D. “Edit layers by selected profiles in a layer editor” is unselected in the Permission profile.
Answer: B
NEW QUESTION 14
Which Check Point software blade provides visibility of users, groups and machines while also providing access control through identity-based policies?
- A. Firewall
- B. Identity Awareness
- C. Application Control
- D. URL Filtering
Answer: B
Explanation:
Check Point Identity Awareness Software Blade provides granular visibility of users, groups and machines, providing unmatched application and access control through the creation of accurate, identity-based policies. Centralized management and monitoring allows for policies to be managed from a single, unified console.
NEW QUESTION 15
Which two of these Check Point Protocols are used by ?
- A. ELA and CPD
- B. FWD and LEA
- C. FWD and CPLOG
- D. ELA and CPLOG
Answer: B
NEW QUESTION 16
When using GAiA, it might be necessary to temporarily change the MAC address of the interface eth 0 to 00:0C:29:12:34:56. After restarting the network the old MAC address should be active. How do you configure this change?
- A. As expert user, issue these commands:# IP link set eth0 down# IP link set eth0 addr 00:0C:29:12:34:56# IP link set eth0 up
- B. Edit the file /etc/sysconfig/netconf.C and put the new MAC address in the field(conf:(conns:(conn:hwaddr (“00:0C:29:12:34:56”)
- C. As expert user, issue the command:# IP link set eth0 addr 00:0C:29:12:34:56
- D. Open the WebUI, select Network > Connections > eth0. Place the new MAC address in the field Physical Address, and press Apply to save the settings.
Answer: C
NEW QUESTION 17
Which of the following is NOT a back up method?
- A. Save backup
- B. System backup
- C. snapshot
- D. Migrate
Answer: A
Explanation:
The built-in Gaia backup procedures:
Snapshot Management
System Backup (and System Restore)
Save/Show Configuration (and Load Configuration)
Check Point provides three different procedures for backing up (and restoring) the operating system and networking parameters on your appliances.
Snapshot (Revert)
Backup (Restore)
upgrade_export (Migrate) References:
NEW QUESTION 18
Which of the following uses the same key to decrypt as it does to encrypt?
- A. Asymmetric encryption
- B. Dynamic encryption
- C. Certificate-based encryption
- D. Symmetric encryption
Answer: D
NEW QUESTION 19
Which of the following actions do NOT take place in IKE Phase 1?
- A. Peers agree on encryption method.
- B. Diffie-Hellman key is combined with the key material to produce the symmetrical IPsec key.
- C. Peers agree on integrity method.
- D. Each side generates a session key from its private key and peer's public key.
Answer: B
NEW QUESTION 20
When attempting to start a VPN tunnel, in the logs the error 'no proposal chosen' is seen numerous times. No other VPN-related log entries are present. Which phase of the VPN negotiations has failed?
- A. IKE Phase 1
- B. IPSEC Phase 2
- C. IPSEC Phase 1
- D. IKE Phase 2
Answer: D
NEW QUESTION 21
Which type of Endpoint Identity Agent includes packet tagging and computer authentication?
- A. Full
- B. Light
- C. Custom
- D. Complete
Answer: A
Explanation:
Endpoint Identity Agents – dedicated client agents installed on users’ computers that acquire and report identities to the Security Gateway.
NEW QUESTION 22
After the initial installation the First Time Configuration Wizard should be run. Select the BEST answer.
- A. First Time Configuration Wizard can be run from the Unified SmartConsole.
- B. First Time Configuration Wizard can be run from the command line or from the WebUI.
- C. First time Configuration Wizard can only be run from the WebUI.
- D. Connection to the internet is required before running the First Time Configuration wizard.
Answer: B
Explanation:
Check Point Security Gateway and Check Point Security Management require running the First Time Configuration Wizard in order to be configured correctly. The First Time Configuration Wizard is available in Gaia Portal and also through CLI.
To invoke the First Time Configuration Wizard through CLI, run the config_system command from the Exp shell.
NEW QUESTION 23
Phase 1 of the two-phase negotiation process conducted by IKE operates in a_____ mode.
- A. Main
- B. Authentication
- C. Quick
- D. High Alert
Answer: A
NEW QUESTION 24
Which of the following is NOT a method used by Identity Awareness for acquiring identity?
- A. RADIUS
- B. Active Directory Query
- C. Remote Access
- D. Certificates
Answer: D
NEW QUESTION 25
......
Thanks for reading the newest 156-215.80 exam dumps! We recommend you to try the PREMIUM Certshared 156-215.80 dumps in VCE and PDF here: https://www.certshared.com/exam/156-215.80/ (485 Q&As Dumps)