A Review Of Approved 156-215.80 Simulations
Ucertify 156-215.80 Questions are updated and all 156-215.80 answers are verified by experts. Once you have completely prepared with our 156-215.80 exam prep kits you will be ready for the real 156-215.80 exam without a problem. We have Renew Check-Point 156-215.80 dumps study guide. PASSED 156-215.80 First attempt! Here What I Did.
Free 156-215.80 Demo Online For Check-Point Certifitcation:
NEW QUESTION 1
Fill in the blank: A ____ VPN deployment is used to provide remote users with secure access to internal corporate resources by authenticating the user through an internet browser.
- A. Clientless remote access
- B. Clientless direct access
- C. Client-based remote access
- D. Direct access
Answer: A
Explanation:
Clientless - Users connect through a web browser and use HTTPS connections. Clientless solutions usually supply access to web-based corporate resources.
NEW QUESTION 2
What are the two types of address translation rules?
- A. Translated packet and untranslated packet
- B. Untranslated packet and manipulated packet
- C. Manipulated packet and original packet
- D. Original packet and translated packet
Answer: D
Explanation:
NAT Rule Base
The NAT Rule Base has two sections that specify how the IP addresses are translated:
Original Packet
Translated Packet References:
NEW QUESTION 3
Fill in the blank: The R80 SmartConsole, SmartEvent GUI client, and _____ consolidate billions of logs and shows them as prioritized security events.
- A. SmartMonitor
- B. SmartView Web Application
- C. SmartReporter
- D. SmartTracker
Answer: B
Explanation:
Event Analysis with SmartEvent
The SmartEvent Software Blade is a unified security event management and analysis solution that delivers real-time, graphical threat management information. SmartConsole, SmartView Web Application, and the SmartEvent GUI client consolidate billions of logs and show them as prioritized security events so you can immediately respond to security incidents, and do the necessary actions to prevent more attacks. You can customize the views to monitor the events that are most important to you. You can move from a high level view to detailed forensic analysis in a few clicks. With the free-text search and suggestions, you can quickly run data analysis and identify critical security events.
NEW QUESTION 4
Of all the Check Point components in your network, which one changes most often and should be backed up most frequently?
- A. SmartManager
- B. SmartConsole
- C. Security Gateway
- D. Security Management Server
Answer: C
NEW QUESTION 5
In SmartView Tracker, which rule shows when a packet is dropped due to anti-spoofing?
- A. Rule 0
- B. Blank field under Rule Number
- C. Rule 1
- D. Cleanup Rule
Answer: A
NEW QUESTION 6
Bob and Joe both have Administrator Roles on their Gaia Platform. Bob logs in on the WebUI and then Joe logs in through CLI. Choose what BEST describes the following scenario, where Bob and Joe are both logged in:
- A. When Joe logs in, Bob will be log out automatically.
- B. Since they both are log in on different interfaces, they both will be able to make changes.
- C. If Joe tries to make changes, he won't, database will be locked.
- D. Bob will be prompt that Joe logged in.
Answer: C
NEW QUESTION 7
Which message indicates IKE Phase 2 has completed successfully?
- A. Quick Mode Complete
- B. Aggressive Mode Complete
- C. Main Mode Complete
- D. IKE Mode Complete
Answer: A
NEW QUESTION 8
Fill in the blank: With the User Directory Software Blade, you can create R80 user definitions on a(an) ______ Server.
- A. NT domain
- B. SMTP
- C. LDAP
- D. SecurID
Answer: C
NEW QUESTION 9
Tom has been tasked to install Check Point R80 in a distributed deployment. Before Tom installs the systems this way, how many machines will he need if he does NOT include a SmartConsole machine in his calculations?
- A. One machine, but it needs to be installed using SecurePlatform for compatibility purposes.
- B. One machine
- C. Two machines
- D. Three machines
Answer: C
Explanation:
One for Security Management Server and the other one for the Security Gateway.
NEW QUESTION 10
Customer’s R80 management server needs to be upgraded to R80.10. What is the best upgrade method when the management server is not connected to the Internet?
- A. Export R80 configuration, clean install R80.10 and import the configuration
- B. CPUSE online upgrade
- C. CPUSE offline upgrade
- D. SmartUpdate upgrade
Answer: C
NEW QUESTION 11
In the Check Point three-tiered architecture, which of the following is NOT a function of the Security Management Server (Security Management Server)?
- A. Display policies and logs on the administrator's workstation.
- B. Verify and compile Security Policies.
- C. Processing and sending alerts such as SNMP traps and email notifications.
- D. Store firewall logs to hard drive storage.
Answer: A
NEW QUESTION 12
What protocol is specifically used for clustered environments?
- A. Clustered Protocol
- B. Synchronized Cluster Protocol
- C. Control Cluster Protocol
- D. Cluster Control Protocol
Answer: D
NEW QUESTION 13
You find that Users are not prompted for authentication when they access their Web servers, even though you have created an HTTP rule via User Authentication. Choose the BEST reason why.
- A. You checked the cache password on desktop option in Global Properties.
- B. Another rule that accepts HTTP without authentication exists in the Rule Base.
- C. You have forgotten to place the User Authentication Rule before the Stealth Rule.
- D. Users must use the SecuRemote Client, to use the User Authentication Rule.
Answer: B
NEW QUESTION 14
Fill in the blank: A ____ is used by a VPN gateway to send traffic as if it were a physical interface.
- A. VPN Tunnel Interface
- B. VPN community
- C. VPN router
- D. VPN interface
Answer: A
Explanation:
Route Based VPN
VPN traffic is routed according to the routing settings (static or dynamic) of the Security Gateway operating system. The Security Gateway uses a VTI (VPN Tunnel Interface) to send the VPN traffic as if it were a physical interface. The VTIs of Security Gateways in a VPN community connect and can support dynamic routing protocols.
NEW QUESTION 15
What is the command to see cluster status in cli expert mode?
- A. fw ctl stat
- B. clusterXL stat
- C. clusterXL status
- D. cphaprob stat
Answer: A
NEW QUESTION 16
Which of the following is NOT a component of Check Point Capsule?
- A. Capsule Docs
- B. Capsule Cloud
- C. Capsule Enterprise
- D. Capsule Workspace
Answer: C
NEW QUESTION 17
Which back up utility captures the most information and tends to create the largest archives?
- A. backup
- B. snapshot
- C. Database Revision
- D. migrate export
Answer: B
NEW QUESTION 18
If the first packet of an UDP session is rejected by a security policy, what does the firewall send to the client?
- A. Nothing
- B. TCP FIN
- C. TCP RST
- D. ICMP unreachable
Answer: A
NEW QUESTION 19
What key is used to save the current CPView page in a filename format cpview_"cpview process ID".cap"number of captures"?
- A. S
- B. W
- C. C
- D. Space bar
Answer: B
NEW QUESTION 20
Fill in the blanks. There are _____ types of software containers ______
- A. Three; security managemen
- B. Security Gateway and endpoint security.
- C. Three; Security Gateway, endpoint Security, and gateway management.
- D. Two; security management and endpoint security
- E. Two; endpoint security and Security Gateway
Answer: A
NEW QUESTION 21
What Identity Agent allows packet tagging and computer authentication?
- A. Endpoint Security Client
- B. Full Agent
- C. Light Agent
- D. System Agent
Answer: B
NEW QUESTION 22
Two administrators Dave and Jon both manage R80 Management as administrators for ABC Corp. Jon logged into the R80 Management and then shortly after Dave logged in to the same server. They are both in the Security Policies view. From the screenshots below, why does Dave not have the rule no.6 in his SmartConsole view even though Jon has it his in his SmartConsole view?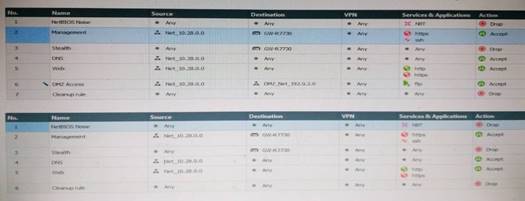
- A. Jon is currently editing rule no.6 but has Published part of his changes.
- B. Dave is currently editing rule no.6 and has marked this rule for deletion.
- C. Dave is currently editing rule no.6 and has deleted it from his Rule Base.
- D. Jon is currently editing rule no.6 but has not yet Published his changes.
Answer: D
Explanation:
When an administrator logs in to the Security Management Server through SmartConsole, a new editing session starts. The changes that the administrator makes during the session are only available to that administrator. Other administrators see a lock icon on object and rules that are being edited. To make changes available to all administrators, and to unlock the objects and rules that are being edited, the administrator must publish the session.
NEW QUESTION 23
What is the default method for destination NAT?
- A. Destination side
- B. Source side
- C. Server side
- D. Client side
Answer: D
NEW QUESTION 24
Which feature in R77 permits blocking specific IP addresses for a specified time period?
- A. Suspicious Activity Monitoring
- B. HTTP Methods
- C. Local Interface Spoofing
- D. Block Port Overflow
Answer: A
NEW QUESTION 25
......
Recommend!! Get the Full 156-215.80 dumps in VCE and PDF From Dumps-files.com, Welcome to Download: https://www.dumps-files.com/files/156-215.80/ (New 485 Q&As Version)