All About Simulation 156-215.80 Preparation Exams
Cause all that matters here is passing the Check-Point 156-215.80 exam. Cause all that you need is a high score of 156-215.80 Check Point Certified Security Administrator exam. The only one thing you need to do is downloading Pass4sure 156-215.80 exam study guides now. We will not let you down with our money-back guarantee.
Also have 156-215.80 free dumps questions for you:
NEW QUESTION 1
Fill in the blank: The command _____ provides the most complete restoration of a R80 configuration.
- A. upgrade_import
- B. cpconfig
- C. fwm dbimport -p <export file>
- D. cpinfo -recover
Answer: A
Explanation:
(Should be "migrate import")
"migrate import" Restores backed up configuration for R80 version, in previous versions the command was " upgrade_import ".
NEW QUESTION 2
To install a brand new Check Point Cluster, the MegaCorp IT department bought 1 Smart-1 and 2 Security Gateway Appliances to run a cluster. Which type of cluster is it?
- A. Full HA Cluster
- B. High Availability
- C. Standalone
- D. Distributed
Answer: B
NEW QUESTION 3
Vanessa is expecting a very important Security Report. The Document should be sent as an attachment via
e-m ail. An e-mail with Security_report.pdf file was delivered to her e-mail inbox. When she opened the PDF file, she noticed that the file is basically empty and only few lines of text are in it. The report is missing some graphs, tables and links. Which component of SandBlast protection is her company using on a Gateway?
- A. SandBlast Threat Emulation
- B. SandBlast Agent
- C. Check Point Protect
- D. SandBlast Threat Extraction
Answer: D
NEW QUESTION 4
Kofi, the administrator of the ABC Corp network wishes to change the default Gaia WebUI Portal port number currently set on the default HTTPS port. Which CLISH commands are required to be able to change this TCP port?
- A. set web ssl-port <new port number>
- B. set Gaia-portal <new port number>
- C. set Gaia-portal https-port <new port number>
- D. set web https-port <new port number>
Answer: A
Explanation:
In Clish
Connect to command line on Security Gateway / each
Log in to Clish.
Set the desired port (e.g., port 4434):
Cluster member.
HostName> set web ssl-port <Port_Number>
Save the changes:
HostName> save config
Verify that the configuration was saved:
[Expert@HostName]# grep 'httpd:ssl_port' /config/db/initial References:
NEW QUESTION 5
Fill in the blank: The ____ collects logs and sends them to the ____.
- A. Log server; security management server
- B. Log server; Security Gateway
- C. Security management server; Security Gateway
- D. Security Gateways; log server
Answer: D
NEW QUESTION 6
In SmartEvent, what are the different types of automatic reactions that the administrator can configure?
- A. Mail, Block Source, Block Event Activity, External Script, SNMP Trap
- B. Mail, Block Source, Block Destination, Block Services, SNMP Trap
- C. Mail, Block Source, Block Destination, External Script, SNMP Trap
- D. Mail, Block Source, Block Event Activity, Packet Capture, SNMP Trap
Answer: A
NEW QUESTION 7
The IT Management team is interested in the new features of the Check Point R80 Management and wants to upgrade but they are concerned that the existing R77.30 Gaia Gateways cannot be managed by R80 because it is so different. As the administrator responsible for the Firewalls, how can you answer or confirm these concerns?
- A. R80 Management contains compatibility packages for managing earlier versions of Check Point Gateways prior to R80. Consult the R80 Release Notes for more information.
- B. R80 Management requires the separate installation of compatibility hotfix packages for managing the earlier versions of Check Point Gateways prior to R80. Consult the R80 Release Notes for more information.
- C. R80 Management was designed as a completely different Management system and so can only monitor Check Point Gateways prior to R80.
- D. R80 Management cannot manage earlier versions of Check Point Gateways prior to R80. Only R80 and above Gateways can be manage
- E. Consult the R80 Release Notes for more information.
Answer: A
NEW QUESTION 8
Which of the following describes how Threat Extraction functions?
- A. Detect threats and provides a detailed report of discovered threats
- B. Proactively detects threats
- C. Delivers file with original content
- D. Delivers PDF versions of original files with active content removed
Answer: B
NEW QUESTION 9
What is the Transport layer of the TCP/IP model responsible for?
- A. It transports packets as datagrams along different routes to reach their destination.
- B. It manages the flow of data between two hosts to ensure that the packets are correctly assembled and delivered to the target application.
- C. It defines the protocols that are used to exchange data between networks and how host programs interact with the Application layer.
- D. It deals with all aspects of the physical components of network connectivity and connects with different network types.
Answer: B
NEW QUESTION 10
Review the rules. Assume domain UDP is enabled in the implied rules.
What happens when a user from the internal network tries to browse to the internet using HTTP? The user:
- A. can connect to the Internet successfully after being authenticated.
- B. is prompted three times before connecting to the Internet successfully.
- C. can go to the Internet after Telnetting to the client authentication daemon port 259.
- D. can go to the Internet, without being prompted for authentication.
Answer: D
NEW QUESTION 11
What Check Point technologies deny or permit network traffic?
- A. Application Control DLP
- B. Packet Filtering, Stateful Inspection, Application Layer Firewall
- C. ACL SandBlast, MPT
- D. IPS, Mobile Threat Protection
Answer: B
NEW QUESTION 12
Which directory holds the SmartLog index files by default?
- A. $SMARTLOGDIR/data
- B. $SMARTLOG/dir
- C. $FWDIR/smartlog
- D. $FWDIR/log
Answer: A
NEW QUESTION 13
Fill in the blank: The R80 utility fw monitor is used to troubleshoot _______
- A. User data base corruption
- B. LDAP conflicts
- C. Traffic issues
- D. Phase two key negotiation
Answer: C
Explanation:
Check Point's FW Monitor is a powerful built-in tool for capturing network traffic at the packet level. The Monitor utility captures network packets at multiple capture points along the FireWall inspection chains. These captured packets can be inspected later using the WireShark
NEW QUESTION 14
The CPD daemon is a Firewall Kernel Process that does NOT do which of the following?
- A. Secure Internal Communication (SIC)
- B. Restart Daemons if they fail
- C. Transfer messages between Firewall processes
- D. Pulls application monitoring status
Answer: D
NEW QUESTION 15
Which utility shows the security gateway general system information statistics like operating system information and resource usage, and individual software blade statistics of VPN, Identity Awareness and DLP?
- A. cpconfig
- B. fw ctl pstat
- C. cpview
- D. fw ctl multik stat
Answer: C
Explanation:
CPView Utility is a text based built-in utility that can be run ('cpview' command) on Security Gateway / Security Management Server / Multi-Domain Security Management Server. CPView Utility shows statistical data that contain both general system information (CPU, Memory, Disk space) and information for different Software Blades (only on Security Gateway). The data is continuously updated in easy to access views.
NEW QUESTION 16
Sally has a Hot Fix Accumulator (HFA) she wants to install on her Security Gateway which operates with GAiA, but she cannot SCP the HFA to the system. She can SSH into the Security Gateway, but she has never been able to SCP files to it. What would be the most likely reason she cannot do so?
- A. She needs to edit /etc/SSHd/SSHd_config and add the Standard Mode account.
- B. She needs to run sysconfig and restart the SSH process.
- C. She needs to edit /etc/scpusers and add the Standard Mode account.
- D. She needs to run cpconfig to enable the ability to SCP files.
Answer: C
NEW QUESTION 17
Which policy type has its own Exceptions section?
- A. Thread Prevention
- B. Access Control
- C. Threat Emulation
- D. Desktop Security
Answer: A
Explanation:
The Exceptions Groups pane lets you define exception groups. When necessary, you can create exception groups to use in the Rule Base. An exception group contains one or more defined exceptions. This option facilitates ease-of-use so you do not have to manually define exceptions in multiple rules for commonly required exceptions. You can choose to which rules you want to add exception groups. This means they can be added to some rules and not to others, depending on necessity.
NEW QUESTION 18
Your users are defined in a Windows 2008 R2 Active Directory server. You must add LDAP users to a Client Authentication rule. Which kind of user group do you need in the Client Authentication rule in R77?
- A. External-user group
- B. LDAP group
- C. A group with a genetic user
- D. All Users
Answer: B
NEW QUESTION 19
To ensure that VMAC mode is enabled, which CLI command you should run on all cluster members? Choose the best answer.
- A. fw ctl set int fwha vmac global param enabled
- B. fw ctl get int fwha vmac global param enabled; result of command should return value 1
- C. cphaprob –a if
- D. fw ctl get int fwha_vmac_global_param_enabled; result of command should return value 1
Answer: B
NEW QUESTION 20
Which is NOT an encryption algorithm that can be used in an IPSEC Security Association (Phase 2)?
- A. AES-GCM-256
- B. AES-CBC-256
- C. AES-GCM-128
Answer: B
NEW QUESTION 21
Choose what BEST describes the reason why querying logs now is very fast.
- A. New Smart-1 appliances double the physical memory install
- B. Indexing Engine indexes logs for faster search results
- C. SmartConsole now queries results directly from the Security Gateway
- D. The amount of logs been store is less than the usual in older versions
Answer: B
NEW QUESTION 22
Review the following screenshot and select the BEST answer.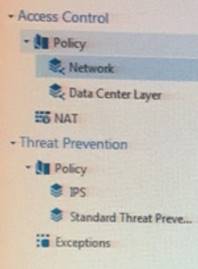
- A. Data Center Layer is an inline layer in the Access Control Policy.
- B. By default all layers are shared with all policies.
- C. If a connection is dropped in Network Layer, it will not be matched against the rules in Data Center Layer.
- D. If a connection is accepted in Network-layer, it will not be matched against the rules in Data Center Layer.
Answer: C
NEW QUESTION 23
Fill in the blank: The R80 feature _____ permits blocking specific IP addresses for a specified time period.
- A. Block Port Overflow
- B. Local Interface Spoofing
- C. Suspicious Activity Monitoring
- D. Adaptive Threat Prevention
Answer: C
Explanation:
Suspicious Activity Rules Solution
Suspicious Activity Rules is a utility integrated into SmartView Monitor that is used to modify access privileges upon detection of any suspicious network activity (for example, several attempts to gain unauthorized access).
The detection of suspicious activity is based on the creation of Suspicious Activity rules. Suspicious Activity rules are Firewall rules that enable the system administrator to instantly block suspicious connections that are not restricted by the currently enforced security policy. These rules, once set (usually with an expiration date), can be applied immediately without the need to perform an Install Policy operation
NEW QUESTION 24
Traffic from source 192.168.1.1 is going to www.google.com. The Application Control Blade on the gateway is inspecting the traffic. Assuming acceleration is enable which path is handling the traffic?
- A. Slow Path
- B. Medium Path
- C. Fast Path
- D. Accelerated Path
Answer: A
NEW QUESTION 25
......
100% Valid and Newest Version 156-215.80 Questions & Answers shared by Dumps-hub.com, Get Full Dumps HERE: https://www.dumps-hub.com/156-215.80-dumps.html (New 485 Q&As)