Regenerate 300-375 Faq 2021
Passleader 300-375 Questions are updated and all 300-375 answers are verified by experts. Once you have completely prepared with our 300-375 exam prep kits you will be ready for the real 300-375 exam without a problem. We have Refresh Cisco 300-375 dumps study guide. PASSED 300-375 First attempt! Here What I Did.
Cisco 300-375 Free Dumps Questions Online, Read and Test Now.
NEW QUESTION 1
Which EAP type requires the use of device certificates?
- A. EAP-TLS
- B. EAP-FAST
- C. EAP-SSL
- D. PEAP
- E. LEAP
Answer: A
NEW QUESTION 2
Which two considerations must a network engineer have when planning for voice over wireless roaming? (Choose two.)
- A. Roaming with only 802.1x authentication requires full reauthentication.
- B. Full reauthentication introduces gaps in a voice conversation.
- C. Roaming occurs when e phone has seen at least four APs.
- D. Roaming occurs when the phone has reached -80 dBs or belo
Answer: AB
NEW QUESTION 3
A customer is concerned that radar is impacting the access point that service the wireless network in an office located near an airport. On which type of channel should you conduct spectrum analysis to identify if radar is impacting the wireless network?
- A. UNII-3 channels
- B. UNII-1 channels
- C. 802.11b channels
- D. 2.4 GHz channels
- E. UMII-2 channels
- F. Channels 1, 5, 9, 13
Answer: E
NEW QUESTION 4
A company is deploying wireless PCs on forklifts within its new 10,000-square-foot (3048-squaremeter) facility. The clients are configured for PEAP-MS-CHAPv2 with WPA TKIP. Users report that applications frequently drop when the clients roam between access points on the floor. A
professional site survey was completed. Which configuration change is recommended to improve the speed of client roaming?
- A. EAP-FAST
- B. EAP-TLS
- C. WPA AES
- D. WPA2 AES
Answer: D
Explanation:
Although the controller and APs support WLAN with SSID using WiFi Protected Access (WPA) and WPA2 simultaneously, it is common that some wireless client drivers cannot handle complex SSID settings. Whenever possible, Cisco recommends WPA2 only with Advanced Encryption Standard (AES). However, due to standards and mandatory WiFi Alliance certification process, TKIP support is required across future software versions. Keep the security policies simple for any SSID. Use a separate WLAN/SSID with WPA and Temporal Key Integrity Protocol (TKIP), and a separate one with WPA2 and Advanced Encryption Standard (AES). Since TKIP is being deprecated, Cisco recommends to use TKIP together with WEP, or to migrate out of TKIP completely and use PEAP, if possible.
NEW QUESTION 5
Access points at branch sites for a company are in FlexConncct mode and perform local switching, but they authenticate to the central RADIUS at headquarters. VPN connections to the headquarters have gone down, but each branch site has a local authentication server. Which three features on the wireless controller can be configured to maintain network operations if this situation reoccurs? (Choose three.)
- A. Put APs in FlexConnect Group for Remote Branches.
- B. Set Branch RADIUS as Primary.
- C. Put APs in AP Group Per Branch.
- D. Put APs in FlexConnect Group Per Branch.
- E. Set Branch RADIUS OS Secondary.
- F. Set HQ RADIUS a-s primar
Answer: AEF
NEW QUESTION 6
An engineer is trying to determine if an existing configuration deviates from the Cisco defaults while enabling PMF on a WLAN. Which set represents the default timer configuration for PMF?
- A. security pmf association-comeback 1 security pmf mandatory security pmf saquery-retry-time 100
- B. security pmf association-comeback 20 security pmf mandatory security pmf saquery-retry-time 600
- C. security pmf association-comeback 15 security pmf mandatory security pmf saquery-retry-time 200
- D. security pmf association-comeback 1 security pmf mandatory security pmf saquery-retry-time 200
Answer: D
NEW QUESTION 7
Which two events are possible outcomes of a successful RF jamming attack? (Choose two.)
- A. unauthentication association
- B. deauthentication multicast
- C. deauthentication broadcast
- D. disruption of WLAN services
- E. physical damage to AP hardware
Answer: DE
NEW QUESTION 8
Refer to the exhibit.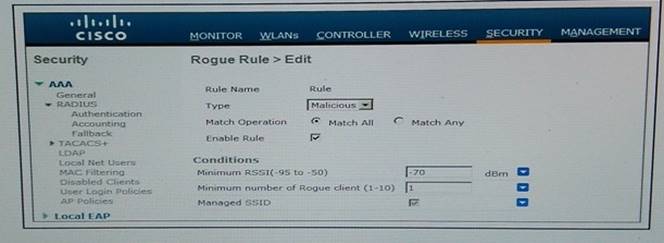
A WLAN with the SSID "Enterprise" is configured. Which rogue is marked as malicious?
- A. a rogue with two clients, broadcasting the SSID "Employee" heard at -50 dBm
- B. a rogue with no clients, broadcasting the SSID "Enterprise" heard at -50 dBm
- C. a rouge with two clients, broadcasting the SSID "Enterprise" heard at -80 dBm
- D. a rogue with two clients, broadcasting the SSID "Enterprise" heard at -50 dBm
Answer: C
NEW QUESTION 9
An engineer has configured central web authentication on the wireless network, but clients are receiving untrusted certificate errors on their internet browsers when directed to the guest splash page. Which file must be provided to an approved trusted certificate authority to fix this issue?
- A. EAP-TLS certificate generate by WLC
- B. CSR generated by identity Service Engine
- C. CSR generated by the WLC
- D. EAP-TLS certificate generated by the access point
Answer: B
NEW QUESTION 10
A new MSE with wIPS service has been installed and no alarm information appears to be reaching
the MSE from controllers.
What protocol must be allowed to reach the MSE from the controllers?
- A. NMSP
- B. SOAP/XML
- C. SNMP
- D. CAPWAP
Answer: B
NEW QUESTION 11
Refer to the exhibit.
An engineer has configured a BYOD policy that allows for printing on the WLAN utilizing Bonjour
services. However, the engineer cannot get printing working. The WLC firmware is 8.x. the printer is connected on the wired network where a few of the access points are also connected.
Which reason that printing is not working is true?
- A. Location-specific service is not enabled on the WLC.
- B. Secure Web Mode Cipher-Option SSLv2 is not enabled.
- C. mBNS and IGMP snooping is not enabled on the WLC.
- D. IGMP Query Interval value is too low.
- E. The number of mDNS services exceeds firmware limits.
Answer: A
NEW QUESTION 12
When you configure BYOD access to the network, you face increased security risks and challenges. Which challenge is resolved by deploying digital client certificates?
- A. managing the increase connected devices
- B. ensuring wireless LAN performance and reliability
- C. providing device choice and support
- D. enforcing company usage policies
Answer: D
NEW QUESTION 13
Which option determines which RADIUS server is preferred the most by the Cisco WLC?
- A. the Server Index (Priority) drop-down list
- B. the server status
- C. the server IP address
- D. the port number
Answer: A
NEW QUESTION 14
Which three WLAN polices can be controlled by using the Cisco IBNS on the Cisco WLC and Cisco Secure ACS? (Choose three.)
- A. QoS setting
- B. VLAN
- C. EAP type
- D. ACL
- E. authentication priority order
- F. NAC state
Answer: ABD
NEW QUESTION 15
An engineer is configuring a BYOD provisioning WLAN. Which two advanced WLAN settings are required? (Choose two)
- A. DHCP profiling
- B. DHCP address assignment
- C. passive client
- D. RADIUS NAC
- E. AAA override
Answer: DE
Explanation:
Allow AAA Override: Enabled NAC State: Radius NAC (selected)
https://www.cisco.com/c/en/us/support/docs/wireless/5500-series-wireless-controllers/113476- wireless-byod-ise-00.html
NEW QUESTION 16
An engineer is adding APs to an existing VoWLAN to allow for location based services. Which option
will the primary change be to the network?
- A. increased transmit power on all APs
- B. moving to a bridging model
- C. AP footprint
- D. cell overlap would decrease
- E. triangulation of devices
Answer: C
NEW QUESTION 17
Which security method does a Cisco guest wireless deployment that relies on Cisco ISE guest portal for user authentication use?
- A. Layer 2 and Layer 3
- B. Layer 2 only
- C. No security methods are needed to deploy CWA
- D. Layer 3 only
Answer: B
NEW QUESTION 18
Refer to the exhibit.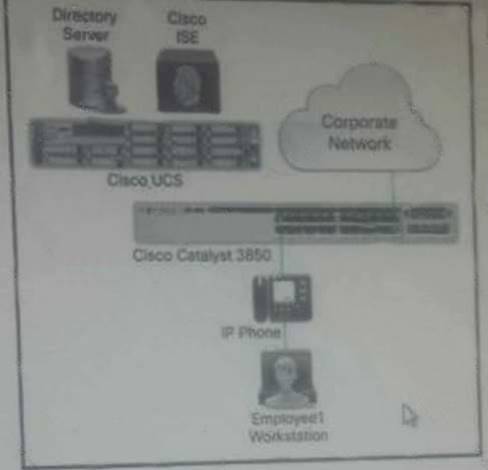
In this IBN topology, which device acts as the RADIUS server?
- A. directory server
- B. Cisco ISE
- C. Cisco UCS
- D. Cisco Catalyst 3850 Series Switch
Answer: D
NEW QUESTION 19
When implementing secure PCI wireless networks, which two are specific recommendations in the PCI DSS? (Choose two)
- A. Use a minimum 12-character random passphrase with WPA
- B. Segment logging events with other networking devices within the organization.
- C. Use VLAN based segmentation with MAC filters.
- D. Change default settings.
- E. Implement strong wireless authentication
Answer: DE
Explanation:
Wireless networks that are part of the CDE must comply with all PCI DSS requirements. This includes using a firewall (requirement 1.2.3) and making sure that additional rogue wireless devices have not been added to the CDE (requirement 11.1). In addition, PCI DSS compliance for systems that include WLANs as a part of the CDE requires extra attention to WLAN specific technologies and processes such as:
A. Physical security of wireless devices, B. Changing default passwords and settings on wireless devices, C. Logging of wireless access and intrusion prevention, D. Strong wireless authentication and encryption, E. Use of strong cryptography and security protocols, and F. Development and enforcement of wireless usage policies. This section will cover each of these requirements sequentially. https://www.pcisecuritystandards.org/pdfs/PCI_DSS_Wireless_Guidelines.pdf
NEW QUESTION 20
Which three authentication methods correctly describe digital certificate requirements when using EAP-TLS authentication? (Choose three)
- A. The client does not need the corresponding private key.
- B. The EAP-TLS is sent in cleartext when the root certificate is not installed.
- C. The certificate has to be X 509 Version 3.
- D. EAP-TLS requires a root certificate but not a user certificate.
- E. The certificate must be installed when the requested user is logged in to the machine.
- F. The subject name in the certificate must correspond to the user account name
Answer: CDE
Explanation:
https://www.cisco.com/en/US/tech/ CK7 22/ CK8 09/technologies_white_paper09186a008 009256b.shtml
The certificate has to be X.509 Version 3
EAP-TLS Machine Authentication requires both Active Directory and an Enterprise root C
A. In order
to acquire a certificate for EAP-TLS machine authentication,
For a client (using Windows XP professional, for example) to authenticate using EAP-TLS, the client must obtain a personal client certificate. This certificate must meet several requirements: Figure 5-1. Client Certificate and the Enhanced Key Usage Field. • The certificate has to be installed when the requested user is logged
https://www.cisco.com/en/US/tech/ CK7 22/ CK8 09/technologies_white_paper09186a008009256b.sht ml
NEW QUESTION 21
Refer to the exhibit.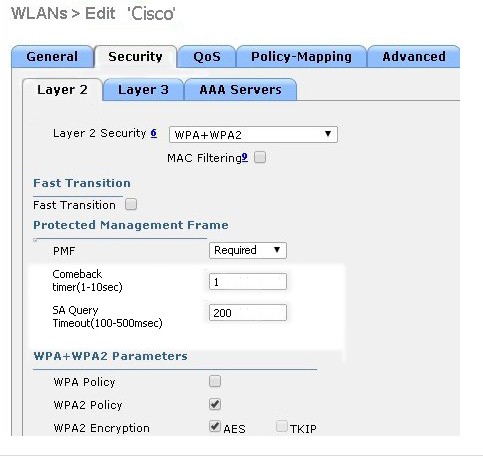
A customer is having problems with clients associating to me wireless network. Based on the configuration, which option describes the most likely cause of the issue?
- A. Both AES and TKIP must be enabled
- B. SA Query Timeout is set too low
- C. Comeback timer is set too low
- D. PME is set to "required"
- E. MAC Filtering must be enabled
Answer: E
NEW QUESTION 22
Which option describes the purpose of configuring switch peer groups?
- A. enforces RF profiles
- B. enables location services
- C. restricts roaming traffic to certain switches
- D. allows template based configuration changes
Answer: C
NEW QUESTION 23
......
Recommend!! Get the Full 300-375 dumps in VCE and PDF From Simply pass, Welcome to Download: https://www.simply-pass.com/Cisco-exam/300-375-dumps.html (New 124 Q&As Version)