Top Tips Of Improve 350-901 Braindump
Master the 350-901 Developing Applications using Cisco Core Platforms & APIs content and be ready for exam day success quickly with this Exambible 350-901 training. We guarantee it!We make it a reality and give you real 350-901 questions in our Cisco 350-901 braindumps.Latest 100% VALID Cisco 350-901 Exam Questions Dumps at below page. You can use our Cisco 350-901 braindumps and pass your exam.
Cisco 350-901 Free Dumps Questions Online, Read and Test Now.
NEW QUESTION 1
User report that they can no longer process transactions with the online ordering application, and the logging dashboard is displaying these messages.
Fri Jan 10 19:37:31.123 EST 2021 [FRONTEND] INFO: Incoming request to add item to cart from user 45834534858 Fri Jan 10 19:37:31 247 EST 2021 [BACKEND] INFO: Attempting to add item to cart
Fri Jan 10 19:37:31 250 EST 2021 [BACKEND] ERROR: Failed to add item: MYSQLDB ERROR: Connection refused What is causing the problem seen in these log messages?
- A. The database server container has crashed.
- B. The backend process is overwhelmed with too many transactions.
- C. The backend is not authorized to commit to the database.
- D. The user is not authorized to add the item to their cart.
Answer: A
NEW QUESTION 2
Refer to the exhibit. This script uses ciscoyang to configure two VRF instances on a Cisco IOS-XR device using the Yang NETCONF type. Which two words are required to complete the script? (Choose two.)
- A. ensure
- B. commit
- C. false
- D. replace
- E. none
Answer: CD
NEW QUESTION 3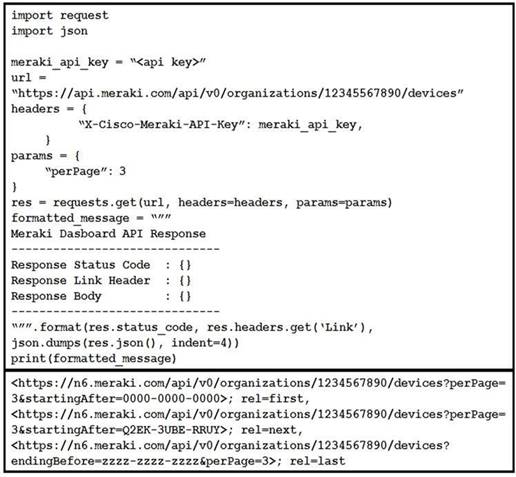
Refer to the exhibit. Which line of code must be added to this code snippet to allow an application to pull the next set of paginated items?
- A. requests.get(url, links=[‘next’][‘url’])
- B. requests.get(url, headers=links[‘next’][‘url’])
- C. requests.get(res.links[‘next’][‘url’], headers=headers)
- D. requests.get(res.headers.get(‘Link”)[‘next’][‘url’], headers=headers)
Answer: C
NEW QUESTION 4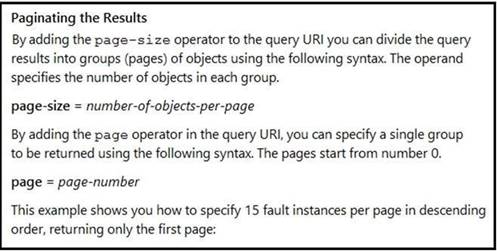
Refer to the exhibit. Many faults have occurred in the ACI environment and a sample of them needs to be examined. Which API call retrieves faults 30 through 45?
- A. GET https://apic-ip-address/api/class/faultInfo.json?order-by=faultinst.severity|desc&page=1&page-size=15
- B. GET https://apic-ip-address/api/class/faultInfo.json?order-by=faultinst.severity|desc&page=2&page-size=15
- C. GET https://apic-ip-address/api/class/faultInfo.json?order-by=faultinst.severity|desc&page=30
- D. GET https://apic-ip-address/api/class/faultInfo.json?order-by=faultinst.severity|desc&page=2&page-size=30
Answer: D
NEW QUESTION 5
The UCS Python SDK includes modules for Service Profile template creation. Which two UCS Service Profile template types are supported? (Choose two.)
- A. initial-template
- B. updating-template
- C. abstract-template
- D. attached-template
- E. base-template
Answer: AB
NEW QUESTION 6
The response from a server includes the header ETag: W/”7eb8b94419e371767916ef13e0d6e63d”. Which statement is true?
- A. The ETag has a Strong validator directive.
- B. The ETag has a Weak validator directive, which is an optional directive.
- C. The ETag has a Weak validator directive, which is a mandatory directive.
- D. The ETag has a Strong validator directive, which it is incorrectly formatted.
Answer: B
NEW QUESTION 7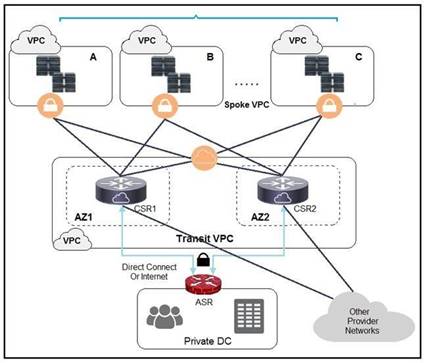
Refer to the exhibit. A company has extended networking from the data center to the cloud through Transit VPC. Which two statements describe the benefits of this approach? (Choose two.)
- A. Dynamic routing combined with multi-AZ- deployment creates a robust network infrastructure.
- B. VPC virtual gateways provide highly available connections to virtual networks.
- C. Dedicated VPC simplifies load balancing by combining internal and external web services.
- D. VPC virtual gateways provide more secure connections to virtual networks.
- E. Dedicated VPC simplifies routing by not combining this service with other shared services.
Answer: BD
NEW QUESTION 8
AppGigabitEthernet interface is used as data port for a container on a Cisco Catalyst 9000 Series Switch. Which two interface configuration options should be used? (Choose two.)
- A. trunk interface
- B. bridged virtual interface
- C. SPAN port
- D. management interface
- E. subinterface
Answer: AC
NEW QUESTION 9
An automated solution is needed to configure VMs in numerous cloud provider environments to connect the environments to an SDWAN. The SDWAN edge VM is provided as an image in each of the relevant clouds and can be given an identity and all required configuration via cloud-init without needing to log into the VM once online.
Which configuration management and/or automation tooling is needed for this solution?
- A. Ansible
- B. Ansible and Terraform
- C. NSO
- D. Terraform
- E. Ansible and NSO
Answer: E
NEW QUESTION 10
Refer to the exhibit. The cURL POST request creates an OAuth access token for authentication with FDM API requests. What is the purpose of the file “@token_data” that cURL is handling?
- A. This file is a container to log possible error responses in the request.
- B. This file is given as input to store the access token received from FDM.
- C. This file is used to send authentication related headers.
- D. This file contains raw data that is needed for token authentication.
Answer: B
NEW QUESTION 11
Which two strategies are used to protect personally identifiable information? (Choose two.)
- A. Encrypt data in transit.
- B. Encrypt hash values of data.
- C. Encrypt data at rest.
- D. Only hash usernames and passwords for efficient lookup.
- E. Only encrypt usernames and passwords for efficient lookup.
Answer: AB
NEW QUESTION 12
Which tow actions must be taken when an observable microservice application is developed? (Choose two.)
- A. Know the state of a single instance of a single service.
- B. Place “try/except” statement in code.
- C. Place log statements in the code.
- D. Use distributed tracing techniques.
- E. Deploy microservice to multiple datacenters.
Answer: BC
NEW QUESTION 13
Which two statements describe advantages of static code analysis over unit tests? (Choose two.)
- A. It checks for potential tainted data where input is not checked.
- B. It enforces proper coding standards and style.
- C. It performs a quick analysis of whether tests will pass or fail when run.
- D. It checks for race conditions in threaded applications.
- E. It estimates the performance of the code when run.
Answer: BC
NEW QUESTION 14
Refer to the exhibit. Which two functions are performed by the load balancer when it handles traffic originating from the Internet destined to an application hosted on the file server farm? (Choose two.)
- A. Terminate the TLS over the UDP connection from the router and originate an HTTPS connection to the selected server.
- B. Terminate the TLS over the UDP connection from the router and originate an HTTP connection to the selected server.
- C. Terminate the TLS over the TCP connection from the router and originate an HTTP connection to the selected server.
- D. Terminate the TLS over the TCP connection from the router and originate an HTTPS connection to the selected server.
- E. Terminate the TLS over the SCTP connection from the router and originate an HTTPS connection to the selected server.
Answer: DE
NEW QUESTION 15
Which database type should be used with highly structured data and provides support for ACID transactions?
- A. time series
- B. document
- C. graph
- D. relational
Answer: D
NEW QUESTION 16
A developer has completed the implementation of a REST API, but when it is executed, it returns a 401 error message. What must be done on the API to resolve the issue?
- A. Access permission to the resource must be granted, before the request.
- B. Configure new valid credentials.
- C. The requested API endpoint does not exist, and the request URL must be changed.
- D. Additional permission must be granted before the request can submitted.
Answer: D
NEW QUESTION 17
Which RFC5988 (Web Linking) relation type is used in the Link header to control pagination in APIs?
- A. rel=”index”
- B. rel=”page”
- C. rel=”next”
- D. rel=”section”
Answer: C
NEW QUESTION 18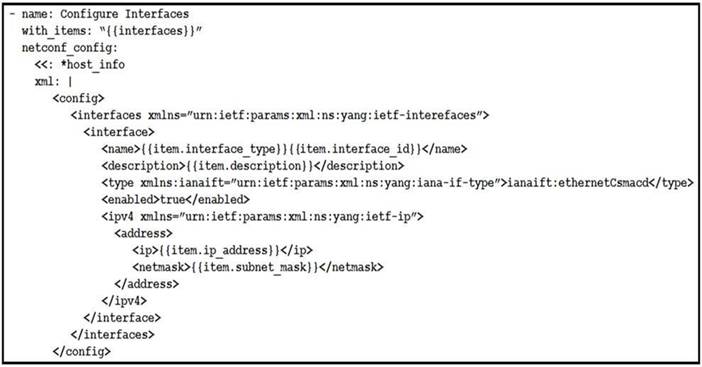
Refer to the exhibit. The Ansible playbook is using the netconf_module to configure an interface using a YANG model. As part of this workflow, which YANG models augment the interface?
- A. ietf-interfaces and ietf-ip
- B. iana-if-type and ietf-interfaces
- C. ietf-ip and openconfig-interface
- D. ietf-ip and iana-if-type
Answer: B
NEW QUESTION 19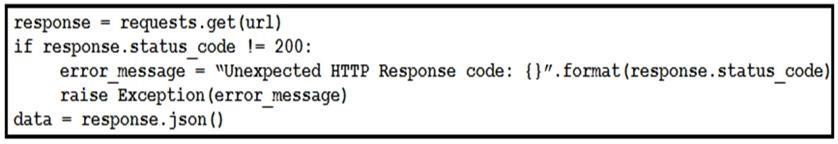
Refer to the exhibit. This snippet of a script has recently started exiting abnormally with an exception stating “Unexpected HTTP Response code: 429”. Which solution handles rate limiting by the remote API?
- A.

- B.
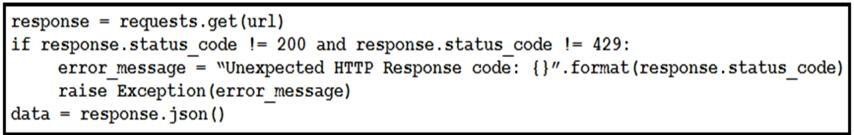
- C.
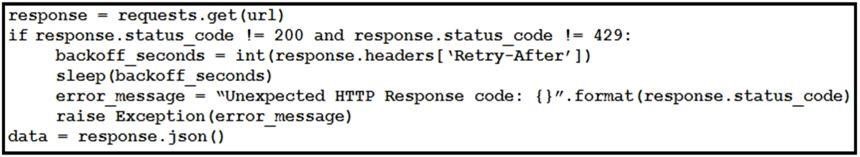
- D.
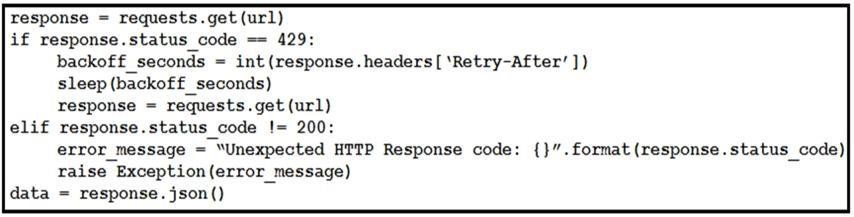
Answer: D
NEW QUESTION 20
Which database type should be used to store data received from model- driven telemetry?
- A. BigQuery database
- B. Time series database
- C. NoSQL database
- D. PostgreSQL database
Answer: B
NEW QUESTION 21
A user is receiving a 429 Too Many Requests error. Which scheme is the server employing that causes this error?
- A. rate limiting
- B. time outs
- C. caching
- D. redirection
Answer: A
NEW QUESTION 22
Application sometimes store configuration as constants in the code, which is a violation of strict separation of configuration from code. Where should application configuration be stored?
- A. environment variables
- B. YAML files
- C. Python libraries
- D. Dockerfiles
- E. INI files
Answer: B
NEW QUESTION 23
Which statement about microservices architecture is true?
- A. Applications are written in a single unit.
- B. It is a complex application composed of multiple independent parts.
- C. It is often a challenge to scale individual parts.
- D. A single faulty service can bring the whole application down.
Answer: B
NEW QUESTION 24
......
100% Valid and Newest Version 350-901 Questions & Answers shared by Allfreedumps.com, Get Full Dumps HERE: https://www.allfreedumps.com/350-901-dumps.html (New 0 Q&As)