Microsoft 70-414 Practice Test 2021
Your success in is our sole target and we develop all our in a way that facilitates the attainment of this target. Not only is our material the best you can find, it is also the most detailed and the most updated. for Microsoft 70-414 are written to the highest standards of technical accuracy.
Also have 70-414 free dumps questions for you:
NEW QUESTION 1
Your network contains five Active Directory forests.
You plan to protect the resources in all of the forests by using Active Directory Rights Management Services (AD RMS).
Users in one of the forests will access the protected resources.
You need to identify the minimum number of AD RMS clusters required for the planned deployment. What should you identify?
- A. five licensing clusters and one root cluster
- B. one licensing cluster
- C. one root cluster
- D. five root clusters and one licensing cluster
Answer: D
NEW QUESTION 2
Your network contains an Active Directory domain named contoso.com. All servers run Windows Server 2012 R2. System Center 2012 R2 Virtual Machine Manager (VMM) is deployed to the domain.
In VMM, you create a host group named HostGroup1. You add a 16-node Hyper-V failover cluster to HostGroup1. From Windows PowerShell, you run the following commands: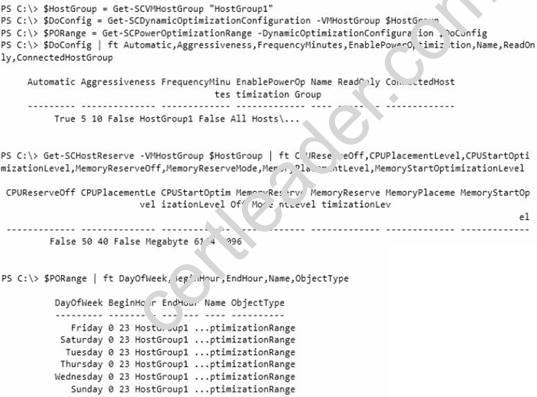
Use the drop-down menus to select the answer choice that completes each statement.
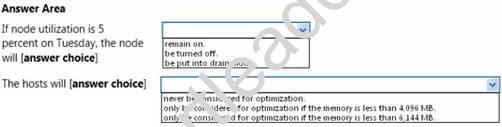
Answer:
Explanation: 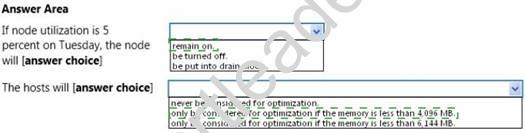
NEW QUESTION 3
You need to recommend a configuration for the CA extensions of Northwind Traders that meets the certificate revocation requirement of Customer1.
What should you recommend? To answer, select the appropriate prefix of the target location for the each extension settings in the answer area.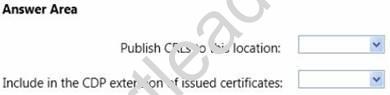
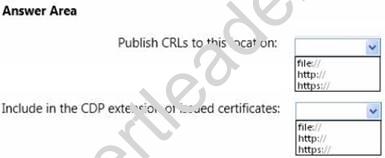
Answer:
Explanation: 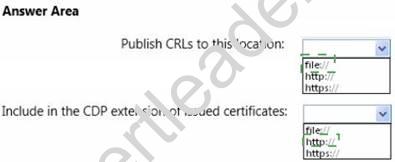
NEW QUESTION 4
You have a service template to deploy Appl. You are evaluating the use of Network Load Balancing (NLB) for the front-end servers used by Appl.
You need to recommend which component must be added to the service template. What should you recommend?
- A. Guest OS profile
- B. A host profile
- C. A capability profile
- D. A VIP template
Answer: D
Explanation: 
NEW QUESTION 5
Your network contains two servers named Server1 and Server2 that run Windows Server 2012.
Server1 has the iSCSI Target Server role service installed and is configured to have five iSCSI virtual disks. You install the Multipath I/O (MPIO) feature on Server2.
From the MPIO snap-in, you add support for iSCSI devices.
You need to ensure that Server2 can connect to the five iSCSI disks. The solution must ensure that Server2 uses MPIO to access the disks.
Which three actions should you perform?
To answer, move the three appropriate actions from the list of actions to the answer area and arrange them in the correct order.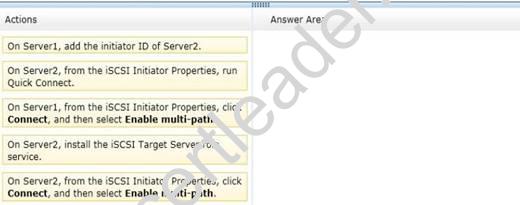
Answer:
Explanation: 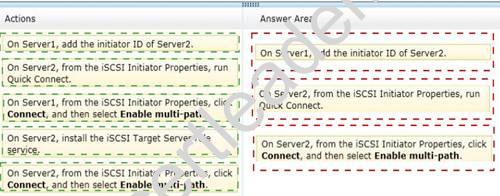
NEW QUESTION 6
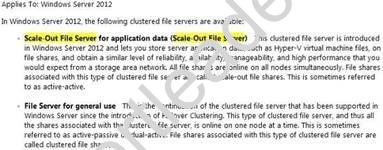
You need to recommend which type of clustered file server and which type of file share must be used in the Hyper-V cluster that hosts App2.
The solution must meet the technical requirements and the security requirements. What should you recommend?
- A. A scale-out file server that uses an NFS share
- B. A file server that uses an SMB share
- C. A scale-out file server that uses an SMB share
- D. A file server that uses an NFS share
Answer: C
Explanation: 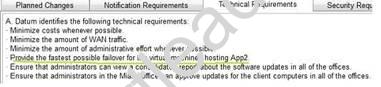
NEW QUESTION 7
You plan to delegate the management of virtual machines to five groups by using Microsoft System Center 2012 Virtual Machine Manager (VMM).
The network contains 20 Hyper-V hosts in a host group named HostGroup1. You identify the requirements for each group as shown in the following table.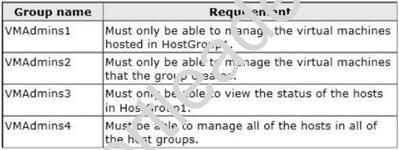
You need to identify which user role must be assigned to each group. Which user roles should you identify?
To answer, drag the appropriate user role to the correct group in the answer area. Each user role may be used once, more than once, or not at all. Additionally, you may need to drag the split bar between panes or scroll to view content.
Answer:
Explanation: 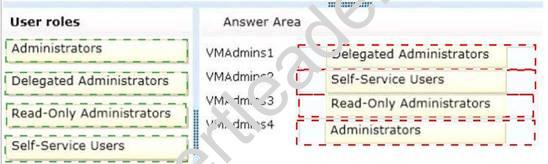
Explanation: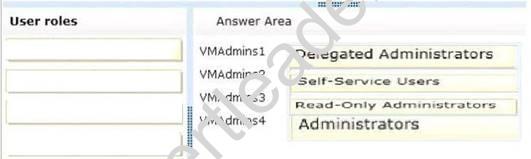
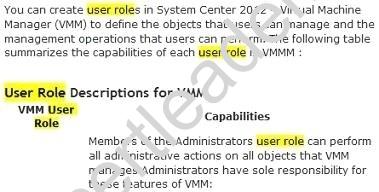
References:
http://mountainss.wordpress.com/2011/11/19/user-roles-in-system-center-virtual-machine-manager-2012/
http://technet.microsoft.com/en-us/library/gg696971.aspx
NEW QUESTION 8
You need to recommend a design that meets the technical requirements for managing the Hyper-V hosts by using VMM.
What should you recommend? To answer, select the appropriate options in the answer area.
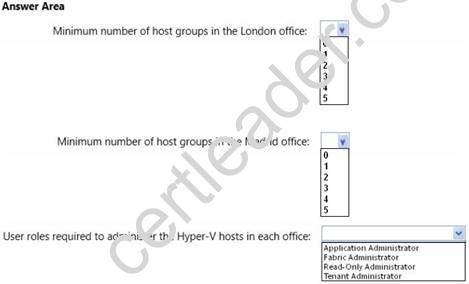
Answer:
Explanation: 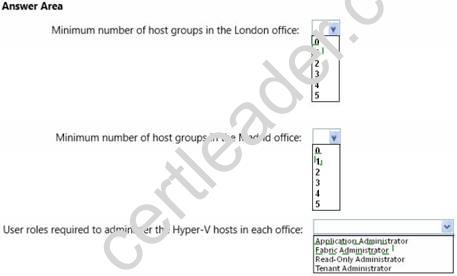
NEW QUESTION 9
Your company has an office in New York.
Many users connect to the office from home by using the Internet.
You deploy an Active Directory Certificate Services (AD CS) infrastructure that contains an enterprise certification authority (CA) named CA1. CA1 is only available from hosts on the internal network.
You need to ensure that the certificate revocation list (CRL) is available to all of the users. What should you do? (Each correct answer presents part of the solution. Choose all that apply.)
- A. Create a scheduled task that copies the CRL files to a Web server.
- B. Run the Install-ADCSWebEnrollment cmdlet.
- C. Run the Install-EnrollmentPolicyWebService cmdlet.
- D. Deploy a Web server that is accessible from the Internet and the internal network.
- E. Modify the location of the Authority Information Access (AIA).
- F. Modify the location of the CRL distribution point (CDP).
Answer: DF
Explanation: Explanation:
CRLs will be located on Web servers which are Internet facing. CRLs will be accessed using the HTTP retrieval protocol.
CRLs
will be accessed using an external URL of http://dp1.pki.contoso.com/pki
F: To successfully authenticate an Internet Protocol over Secure Hypertext Transfer Protocol
(IP-HTTPS)-based connection, DirectAccess clients must be able to check for certificate revocation of the secure sockets layer (SSL) certificate submitted by the DirectAccess server. To successfully perform intranet detection, DirectAccess clients must be able to check for certificate revocation of the SSL certificate submitted by the network location server. This procedure describes how to do the following:
Create a Web-based certificate revocation list (CRL) distribution point using Internet Information Services (IIS)
Configure permissions on the CRL distribution shared folder Publish the CRL in the CRL distribution shared folder
NEW QUESTION 10
Your company has a main office and a branch office.
You plan to implement a failover cluster named Cluster1 to host an application named App1. The data of
App1 will replicate to all of the nodes in Cluster1.
Cluster1 will contain two servers. The servers will be configured as shown in the following table.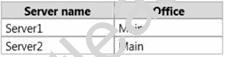
The cluster nodes will not use shared storage.
The branch office contains two file servers named Server3 and Server4.
You need to ensure that App1 fails over automatically to another server if a single node in Cluster1 fails. What should you do?
More than one answer choice may achieve the goal. Select the BEST answer.
- A. Add Server3 as a node in Cluster1.
- B. Add Server1, Server2, and Server3 to a Network Load Balancing (NLB) cluster.
- C. Add Server3 and Server4 to a new failover cluster named Cluster2. Install App1 on Cluster2.
- D. Add Server3 as a file share witness for Cluster1.
Answer: D
NEW QUESTION 11
Your network contains two Hyper-V hosts named Host1 and Host2. Host1 contains a virtual machine named VM1. Host2 contains a virtual machine named VM2. VM1 and VM2 run Windows Server 2012 R2.
You install the Network Load Balancing feature on VM1 and VM2. You need to ensure that the virtual machines are configured to support Network Load Balancing (NLB).
Which virtual machine settings should you configure on VM1 and VM2?
- A. DHCP guard
- B. MAC address
- C. Router guard
- D. Port mirroring
Answer: B
Explanation: Explanation:
When MAC addresses are not assigned to virtual machines, it could cause network problems.
NEW QUESTION 12
You administer an Active Directory Domain Services environment. There are no certification authorities (CAs) in the environment.
You plan to implement a two-tier CA hierarchy with an offline root CA.
You need to ensure that the issuing CA is not used to create additional subordinate CAs. What should you do?
- A. In the CAPolicy.inf file for the issuing CA, enter the following constraint: PathLength=1
- B. In the CAPolicy.inf file for the root CA, enter the following constraint: PathLength=1
- C. In the CAPolicy.inf file for the root CA, enter the following constraint: PathLength=2
- D. In the CAPolicy.inf file for the issuing CA, enter the following constraint:PathLength=2
Answer: B
Explanation: Explanation:
You can use the CAPolicy.inf file to define the PathLength constraint in the Basic Constraints extension of the root CA certificate. Setting the PathLength basic constraint allows you to limit the path length of the CA hierarchy by specifying how many tiers of subordinate CAs can exist beneath the root. A PathLength of 1 means there can be at most one tier of CAs beneath the root. These subordinate CAs will have a PathLength basic constraint of 0, which means that they cannot issue any subordinate CA certificates.
NEW QUESTION 13
Your network contains five servers that run Windows Server 2012. You install the Hyper-V server role on the servers. You create an external virtual network switch on each server.
You plan to deploy five virtual machines to each Hyper-V server. Each virtual machine will have a virtual network adapter that is connected to the external virtual network switch and that has a VLAN identifier of 1.
Each virtual machine will run Windows Server 2012. All of the virtual machines will run the identical web application.
You plan to install the Network Load Balancing (NLB) feature on each virtual machine and join each virtual machine to an NLB cluster. The cluster will be configured to use unicast only.
You need to ensure that the NLB feature can distribute connections across all of the virtual machines.
What should you do?
- A. From the properties of each virtual machine, add a second virtual network adapte
- B. Connect the new virtual network adapters to the external virtual network switc
- C. Configure the new virtual network adapters to use a VLAN identifier of 2.
- D. On each Hyper-V server, create a new private virtual network switc
- E. From the properties of each virtual machine, add a second virtual network adapte
- F. Connect the new virtual network adapters to the new private virtual network switches.
- G. On each Hyper-V server, create a new external virtual network switc
- H. From the properties of each virtual machine, add a second virtual network adapte
- I. Connect the new virtual network adapters to the new external virtual network switches.
- J. From the properties of each virtual machine, enable MAC address spoofing for the existing virtual network adapter.
Answer: D
Explanation: MAC spoofing
The changing of the assigned MAC address may allow the bypassing of access control lists on servers or routers, either hiding a computer on a network or allowing it to impersonate another network device.
A user may wish to legitimately spoof the MAC address of a previous hardware device in order to reacquire connectivity after hardware failure.
NEW QUESTION 14
You are planning the deployment of System Center 2012 Virtual Machine Manager (VMM).
You need to identify which additional System Center 2012 product is required to meet the virtualization requirements.
What should you include in the recommendation?
- A. App Controller
- B. Operations Manager
- C. Configuration Manager
- D. Service Manager
Answer: B
NEW QUESTION 15
Your network contains an Active Directory domain named contoso.com. The domain contains a member server named Server 1. Server1 runs Windows Server 2012 R2 and has the Hyper-V server role installed. You create an external virtual switch named Switch1.
Switch1 has the following configurations:
Connection type: External network
Single-root I/O virtualization (SR-IOV): Enabled Ten virtual machines connect to Switch1.
You need to ensure that all of the virtual machines that connect to Switch1 are isolated from the external network and can connect to each other only. The solution must minimize network downtime for the virtual machines.
What should you do?
- A. Remove Switch1 and recreate Switch1 as an internal network.
- B. Change the Connection type of Switch1 to Private network.
- C. Change the Connection type of Switch1 to Internal network.
- D. Remove Switch1 and recreate Switch1 as a private network.
Answer: B
Explanation: You can change the connection type of a virtual switch from the virtual switch manager without having to remove it.
A private virtual network is isolated from all external network traffic on the virtualization server, as well any network traffic between the management operating system and the external network.
This type of network is useful when you need to create an isolated networking environment, such as an isolated test domain.
NEW QUESTION 16
Your network contains an Active Directory domain named contoso.com. You deploy Active Directory Certificate Services (AD CS). You plan to deploy 100 external Web servers that will be publicly accessible and will require Secure Sockets Layer (SSL) certificates.
You also plan to deploy 50,000 certificates for secure email exchanges with Internet-based recipients. You need to recommend a certificate services solution for the planned deployment.
What should you recommend? More than one answer choice may achieve the goal. Select the BEST answer.
- A. Deploy a certification authority (CA) that is subordinate to an external root CA.
- B. Purchase 50,100 certificates from a trusted third-party root certification authority (CA).
- C. Distribute a copy of the root certification authority (CA) certificate to external relying parties.
- D. Instruct each user to request a Secure Email certificate from a trusted third-party root CA, and then purchase 100 Web server certificates.
Answer: A
Explanation: 
100% Valid and Newest Version 70-414 Questions & Answers shared by Exambible, Get Full Dumps HERE: https://www.exambible.com/70-414-exam/ (New 270 Q&As)