Printable CompTIA 220-1102 Exam Guide Online
Our pass rate is high to 98.9% and the similarity percentage between our 220-1102 study guide and real exam is 90% based on our seven-year educating experience. Do you want achievements in the CompTIA 220-1102 exam in just one try? I am currently studying for the CompTIA 220-1102 exam. Latest CompTIA 220-1102 Test exam practice questions and answers, Try CompTIA 220-1102 Brain Dumps First.
Online 220-1102 free questions and answers of New Version:
NEW QUESTION 1
A laptop that was in the evidence room of a police station is missing. Which of the following is the best reason to refer to chain of custody documentation?
- A. To determine which party had the machine and when.
- B. To remotely wipe sensitive data from the machine.
- C. To gather the information needed to replace the machine.
- D. To alert the owner that the password needs to be changed.
Answer: A
Explanation:
Chain of custody documentation is a record of the sequence of custody, control, transfer, analysis, and disposition of physical or electronic evidence. It is important to maintain a chain of custody to ensure the integrity and authenticity of the evidence, and to prevent tampering or contamination. If a laptop that was in the evidence room of a police station is missing, the best reason to refer to chain of custody documentation is to determine which party had the machine and when. This can help to identify the possible suspects, locate the missing laptop, and verify if the evidence on the laptop was compromised or not
NEW QUESTION 2
When trying to access a secure internal network, the user receives an error messaging stating, "There is a problem with this website's security certificate." The user reboots the desktop and tries to access the website again, but the issue persists. Which of the following should the user do to prevent this error from reoccurring?
- A. Reimage the system and install SSL.
- B. Install Trusted Root Certificate.
- C. Select View Certificates and then Install Certificate.
- D. Continue to access the website.
Answer: C
Explanation:
The error message indicates that the website’s security certificate is not trusted by the user’s device, which may prevent the user from accessing the secure internal network. To resolve this issue, the user can view the certificate details and install it on the device, which will add it to the trusted root certificate store. Reimaging the system and installing SSL, installing Trusted Root Certificate, or continuing to access the website are not recommended solutions, as they may compromise the security of the device or the network.
NEW QUESTION 3
A technician is working on a way to register all employee badges and associated computer IDs. Which of the following options should the technician use in order to achieve this objective?
- A. Database system
- B. Software management
- C. Active Directory description
- D. Infrastructure as a Service
Answer: A
Explanation:
A database system is a software application that allows storing, organizing, and managing data in a structured way. A database system can be used to register all employee badges and associated computer IDs by creating a table or a record for each employee that contains their badge number, computer ID, name, and other relevant information. A database system can also facilitate searching, updating, and deleting data as needed. Software management is a general term that refers to the process of planning, developing, testing, deploying, and maintaining software applications. It does not directly address the issue of registering employee badges and computer IDs. Active Directory description is a field in Active Directory that can be used to store additional information about an object, such as a user or a computer. It is not a software application that can be used to register employee badges and computer IDs by itself. Infrastructure as a Service (IaaS) is a cloud computing model that provides servers, storage, networking, and software over the internet. It does not directly address the issue of registering employee badges and computer IDs either.
https://www.idcreator.com/
https://www.alphacard.com/photo-id-systems/card-type/employee-badges
NEW QUESTION 4
A technician needs to reimage a desktop in an area without network access. Which of the following should the technician use? (Select two).
- A.
 USB
USB - B. PXE
- C. Optical media
- D. Partition
- E. Boot record
- F. SMB
Answer: AC
Explanation:
A technician needs to reimage a desktop in an area without network access, which means that the technician cannot use network-based methods such as PXE or SMB to deploy the image. Therefore, the technician should use offline methods that involve removable media such as USB or optical media. USB and optical media are common ways to store and transfer system images, and they can be used to boot the desktop and initiate the reimaging process. The technician will need to create a bootable USB or optical media that contains the system image and the imaging software, and then insert it into the desktop and change the boot order in the BIOS or UEFI settings. The technician can then follow the instructions on the screen to reimage the desktop
NEW QUESTION 5
Which of the following is an advantage of using WPA2 instead of WPA3?
- A. Connection security
- B. Encryption key length
- C. Device compatibility
- D. Offline decryption resistance
Answer: C
Explanation:
Device compatibility is an advantage of using WPA2 instead of WPA3. WPA2 is the previous version of the Wi-Fi Protected Access protocol, which provides security and encryption for wireless networks. WPA3 is the latest version, which offers improved security features, such as stronger encryption, enhanced protection against brute-force attacks, and easier configuration. However, WPA3 is not backward compatible with older devices that only support WPA2 or earlier protocols. Therefore, using WPA3 may limit the range of devices that can connect to the wireless network. Connection security, encryption key length, and offline decryption resistance are advantages of using WPA3 instead of WPA2. References:
✑ Official CompTIA learning resources CompTIA A+ Core 1 and Core 2, page 24
✑ CompTIA A+ Certification All-in-One Exam Guide (Exams 220-1101 & …, page 1000
NEW QUESTION 6
A technician is installing new network equipment in a SOHO and wants to ensure the equipment is secured against external threats on the Internet. Which of the following actions should the technician do FIRST?
- A. Lock all devices in a closet.
- B. Ensure all devices are from the same manufacturer.
- C. Change the default administrative password.
- D. Install the latest operating system and patches
Answer: C
Explanation:
The technician should change the default administrative password FIRST to ensure the network equipment is secured against external threats on the Internet. Changing the default administrative password is a basic security measure that can help prevent unauthorized access to the network equipment. Locking all devices in a closet is a physical security measure that can help prevent theft or damage to the devices, but it does not address external threats on the Internet. Ensuring all devices are from the same manufacturer is not a security measure and does not address external threats on the Internet. Installing the latest operating system and patches is important for maintaining the security of the network equipment, but it is not the first action the technician should take1
NEW QUESTION 7
A user in a corporate office reports the inability to connect to any network drives. No other users have reported this issue. Which of the following is the MOST likely reason the user is having this issue?
Solution:
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 8
A user requested that the file permissions on a Linux device be changed to only allow access to a certain group of users. Which of the following commands should be used to complete the user's request?
- A.
 cat
cat - B. chmod
- C. pwd
- D. cacls
Answer: B
Explanation:
The chmod command is used to change the permissions of files and directories in Linux. It can grant or revoke read, write, and execute permissions for the owner, the group, and others. To change the file permissions to only allow access to a certain group of users, the chmod command can use either the symbolic or the numeric mode. For example, to give read and write permissions to the group and no permissions to others, the command can be:
chmod g+rw,o-rwx filename or
chmod 660 filename
References: 1 Chmod Command in Linux (File Permissions) | Linuxize(https://linuxize.com/post/chmod-command-in-linux/)2 How To Change File or Directory Permissions in Linux | Tom’s Hardware(https://www.tomshardware.com/how- to/change-file-directory-permissions-linux).
NEW QUESTION 9
DRAG DROP
A customer recently experienced a power outage at a SOHO. The customer does not think the components are connected properly. A print job continued running for several minutes after the power failed, but the customer was not able to interact with the computer. Once the UPS stopped beeping, all functioning devices also turned off. In case of a future power failure, the customer wants to have the most time available to save cloud documents and shut down the computer without losing any data.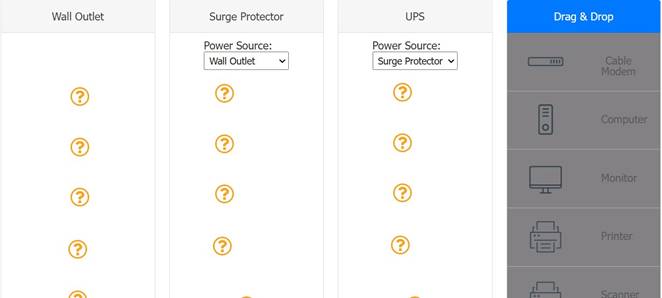
Solution:
UPS > Surge protector = Computer, wifi router, cable modem Surge protector = wallOutlet , printer and scanner
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 10
A technician needs to manually set an IP address on a computer that is running macOS. Which of the following commands should the technician use?
- A. ipconfig
- B. ifconfig
- C. arpa
- D. ping
Answer: B
Explanation:
ifconfig is a command-line utility that allows you to configure network interfaces on macOS and other Unix-like systems1. To set an IP address using ifconfig, you need to know the name of the network interface you want to configure (such as en0 or en1), and the IP address you want to assign (such as 192.168.0.150). You also need to use sudo to run the command with administrative privileges2. The syntax of the command is:
sudo ifconfig interface address
For example, to set the IP address of en1 to 192.168.0.150, you would type: sudo ifconfig en1 192.168.0.150
You may also need to specify other parameters such as subnet mask, gateway, or DNS servers, depending on your network configuration3. The other commands are not directly related to setting an IP address on macOS. ipconfig is a similar command for Windows systems4, arpa is a domain name used for reverse DNS lookup, and ping is a command for testing network connectivity.
NEW QUESTION 11
A user's iPhone was permanently locked after several failed log-in attempts. Which of the following authentication methods are needed to restore access, applications, and data to the device?
- A. Fingerprint and pattern
- B. Facial recognition and PIN code
- C. Primary account and password
- D. Recovery contact and recovery key
Answer: D
Explanation:
If a user’s iPhone is permanently locked after several failed log-in attempts, the user will need to use the recovery contact and recovery key to restore access, applications, and data to the device. The recovery contact is a trusted person who can receive a verification code from Apple and share it with the user. The recovery key is a 28- character code that the user created when setting up two-factor authentication for their Apple ID. The user will need to enter both the verification code and the recovery key on another device or computer to unlock their iPhone. This method will erase the iPhone and restore it from the iCloud backup
Apple ID. The user will need to enter both the verification code and the recovery key on another device or computer to unlock their iPhone. This method will erase the iPhone and restore it from the iCloud backup
NEW QUESTION 12
A company-owned mobile device is displaying a high number of ads, receiving data-usage limit notifications, and experiencing slow response. After checking the device, a technician notices the device has been jailbroken. Which of the following should the technician do next?
- A. Run an antivirus and enable encryption.
- B. Restore the defaults and reimage the corporate OS.
- C. Back up the files and do a system restore.
- D. Undo the jailbreak and enable an antivirus.
Answer: B
Explanation:
The best course of action for the technician is to restore the defaults and reimage the corporate OS on the device. This will remove the jailbreak and any unauthorized or malicious apps that may have been installed on the device, as well as restore the security features and policies that the company has set for its devices. This will also ensure that the device can receive the latest updates and patches from the manufacturer and the company, and prevent any data leakage or compromise from the device.
Jailbreaking is a process of bypassing the built-in security features of a device to install software other than what the manufacturer has made available for that device1. Jailbreaking allows the device owner to gain full access to the root of the operating system and access all the features1. However, jailbreaking also exposes the device to various risks, such as:
✑ The loss of warranty from the device manufacturers2.
✑ Inability to update software until a jailbroken version becomes available2.
✑ Increased security vulnerabilities32.
✑ Decreased battery life2.
✑ Increased volatility of the device2. Some of the signs of a jailbroken device are:
Some of the signs of a jailbroken device are:
✑ A high number of ads, which may indicate the presence of adware or spyware on the device3.
✑ Receiving data-usage limit notifications, which may indicate the device is sending or receiving data in the background without the user’s knowledge or consent3.
✑ Experiencing slow response, which may indicate the device is running unauthorized or malicious apps that consume resources or interfere with the normal functioning of the device3.
✑ Finding apps or icons that the user did not install or recognize, such as Cydia, which is a storefront for jailbroken iOS devices1.
The other options are not sufficient or appropriate for dealing with a jailbroken device. Running an antivirus and enabling encryption may not detect or remove all the threats or vulnerabilities that the jailbreak has introduced, and may not restore the device to its original state or functionality. Backing up the files and doing a system restore may not erase the jailbreak or the unauthorized apps, and may also backup the infected or compromised files. Undoing the jailbreak and enabling an antivirus may not be possible or effective, as the jailbreak may prevent the device from updating or installing security software, and may also leave traces of the jailbreak or the unauthorized apps on the device.
References:
✑ CompTIA A+ Certification Exam Core 2 Objectives4
✑ CompTIA A+ Core 2 (220-1102) Certification Study Guide5
✑ What is Jailbreaking & Is it safe? - Kaspersky1
✑ Is Jailbreaking Safe? The ethics, risks and rewards involved - Comparitech3
✑ Jailbreaking : Security risks and moving past them2
NEW QUESTION 13
A department manager submits a help desk ticket to request the migration of a printer's port utilization from USB to Ethernet so multiple users can access the printer. This will be a new network printer, thus a new IP address allocation is required. Which of the following should happen immediately before network use is authorized?
- A. Document the date and time of the change.
- B. Submit a change request form.
- C. Determine the risk level of this change.
- D. Request an unused IP address.
Answer: B
Explanation:
A change request form is a document that describes the proposed change, the reason for the change, the impact of the change, and the approval process for the change. A change request form is required for any planned changes to the network, such as adding a new network printer, to ensure that the change is authorized, documented, and communicated to all stakeholders. Submitting a change request form should happen immediately before network use is authorized, as stated in the Official CompTIA A+ Core 2 Study Guide. The other options are either too late (documenting the date and time of the change) or too early (determining the risk level of the change and requesting an unused IP address) in the change management process.
change) or too early (determining the risk level of the change and requesting an unused IP address) in the change management process.
NEW QUESTION 14
A user created a file on a shared drive and wants to prevent its data from being accidentally deleted by others. Which of the following applications should the technician use to assist the user with hiding the file?
- A. Device Manager
- B. Indexing Options
- C. File Explorer
- D. Administrative Tools
Answer: C
Explanation:
The technician should use the File Explorer application to assist the user with hiding the file 1. The user can right-click the file and select Properties. In the Properties dialog box, select the Hidden check box, and then click OK 1.
NEW QUESTION 15
A change advisory board authorized a setting change so a technician is permitted to implement the change. The technician successfully implemented the change. Which of the following should be done NEXT?
- A. Document the date and time of change.
- B. Document the purpose of the change.
- C. Document the risk level.
- D. Document findings of the sandbox test.
Answer: A
Explanation:
After implementing a change authorized by the change advisory board (CAB), the technician should document the date and time of change as part of the post- implementation review. This helps to track the change history, verify the success of the change, and identify any issues or incidents caused by the change1. Documenting the purpose of the change, the risk level, and the findings of the sandbox test are all part of the pre-implementation activities that should be done before submitting the change request to the CAB2.
References: 2: https://www.manageengine.com/products/service-desk/itil-change-management/cab-change-advisory-board.html 1: https://www.servicenow.com/content/dam/servicenow-assets/public/en-us/doc-type/success/quick-answer/change-advisory-board-setup.pdf
NEW QUESTION 16
A company-owned mobile device is displaying a high number of ads, receiving data-usage limit notifications, and experiencing slow response. After checking the device, a technician notices the device has been jailbroken. Which of the following should the technician do next?
- A. Run an antivirus and enable encryption.
- B.
 Restore the defaults and reimage the corporate OS.
Restore the defaults and reimage the corporate OS. - C. Back up the files and do a system restore.
- D. Undo the jailbreak and enable an antivirus.
Answer: B
Explanation:
Jailbreaking a device exposes it to various security risks, such as malware, data theft, network attacks, and service disruption1234. Running an antivirus and enabling encryption may not be enough to remove the threats and restore the device’s functionality. Undoing the jailbreak may not be possible or effective, depending on the method used. Backing up the files and doing a system restore may preserve the jailbreak and the associated problems. The best option is to erase the device and reinstall the original operating system that is compatible with the corporate policies and standards. This will ensure that the device is clean, secure, and compliant25.
References: 1 What is Jailbreaking & Is it safe? - Kaspersky(https://www.kaspersky.com/resource-center/definitions/what-is- jailbreaking). 2 Jailbreak Detection: Why is jailbreaking a potential security risk? -
Cybersecurity ASEE(https://cybersecurity.asee.co/blog/what-is-jailbreaking/). 3 Jailbreaking Information for iOS Devices | University IT(https://uit.stanford.edu/service/mydevices/jailbreak)4 What does it mean to jailbreak your phone—and is it legal? - Microsoft(https://www.microsoft.com/en-us/microsoft-365-life- hacks/privacy-and-safety/what-is-jailbreaking-a-phone). 5 Resetting a corporate laptop back to a personal laptop… Enterprise vs Pro - Windows 10(https://community.spiceworks.com/topic/2196812-resetting-a-corporate-laptop-back-to-
a-personal-laptop-enterprise-vs-pro).
NEW QUESTION 17
A user tries to access commonly used web pages but is redirected to unexpected websites. Clearing the web browser cache does not resolve the issue. Which of the following should a technician investigate NEXT to resolve the issue?
- A. Enable firewall ACLs.
- B. Examine the localhost file entries.
- C. Verify the routing tables.
- D. Update the antivirus definitions.
Answer: B
Explanation:
A possible cause of the user being redirected to unexpected websites is that the localhost file entries have been modified by malware or hackers to point to malicious or unwanted websites. The localhost file is a text file that maps hostnames to IP addresses and can override DNS settings. By examining the localhost file entries, a technician can identify and remove any suspicious or unauthorized entries that may cause the redirection issue. Enabling firewall ACLs may not resolve the issue if the firewall rules do not block the malicious or unwanted websites. Verifying the routing tables may not resolve the issue if the routing configuration is correct and does not affect the web traffic. Updating the antivirus definitions may help prevent future infections but may not remove the existing malware or changes to the localhost file. References: CompTIA A+ Core 2 (220-1002) Certification Exam Objectives Version 4.0, Domain 1.3
NEW QUESTION 18
A technician needs to recommend the best backup method that will mitigate ransomware attacks. Only a few files are regularly modified, however, storage space is a concern. Which of the following backup methods would BEST address these concerns?
- A. Full
- B.
 Differential
Differential - C. Off-site
- D. Grandfather-father-son
Answer: B
Explanation:
The differential backup method would best address these concerns. Differential backups only back up files that have changed since the last full backup, which means that only a few files would be backed up each time. This would help to mitigate the risk of ransomware attacks, as only a few files would be affected if an attack occurred. Additionally, differential backups require less storage space than full backups.
NEW QUESTION 19
A new employee was hired recently. Which of the following documents will the new employee need to sign before being granted login access to the network?
Solution:
A new employee will need to sign an AUP before being granted login access to the network. An AUP is an Acceptable Use Policy that defines the rules and guidelines for using network resources and services in an organization. An AUP typically covers topics such as security, privacy, ethics, compliance and liability issues related to network usage. An AUP helps protect the organization and its users from legal, regulatory and reputational risks associated with network activities. An MSDS is a Material Safety Data Sheet that provides information about hazardous substances and how to handle them safely. An MSDS is not related to network access or usage. A EULA is an End User License Agreement that specifies the terms and conditions for using a software product or service. A EULA is usually provided by software vendors or developers and does not apply to network access or usage in general. A UAC is a User Account Control that is a security feature that prompts users for permission or confirmation before performing certain actions that require elevated privileges or affect system settings. A UAC is not a document that needs to be signed by users but a mechanism that helps prevent unauthorized changes or malware infections on a system. References: CompTIA A+ Core 2 (220-1002) Certification Exam Objectives Version 4.0, Domain 5.1
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 20
......
Thanks for reading the newest 220-1102 exam dumps! We recommend you to try the PREMIUM DumpSolutions.com 220-1102 dumps in VCE and PDF here: https://www.dumpsolutions.com/220-1102-dumps/ (757 Q&As Dumps)