How Many Questions Of 220-1102 Testing Software
It is impossible to pass CompTIA 220-1102 exam without any help in the short term. Come to Pass4sure soon and find the most advanced, correct and guaranteed CompTIA 220-1102 practice questions. You will get a surprising result by our Regenerate CompTIA A+ Certification Exam: Core 2 practice guides.
Free demo questions for CompTIA 220-1102 Exam Dumps Below:
NEW QUESTION 1
Which of the following filesystem types does macOS use?
- A. ext4
- B. exFAT
- C. NTFS
- D. APFS
Answer: D
Explanation:
APFS stands for Apple File System and it is the default filesystem type for macOS since High Sierra (10.13) version1. APFS is optimized for flash storage and supports features such as encryption, snapshots, cloning, and space sharing1.
NEW QUESTION 2
An administrator has submitted a change request for an upcoming server deployment. Which of the following must be completed before the change can be approved?
- A. Risk analysis
- B. Sandbox testing
- C. End user acceptance
- D. Lessons learned
Answer: A
Explanation:
A risk analysis must be completed before a change request for an upcoming server deployment can be approved 1 Risk analysis is an important step in the change management process because it helps identify and mitigate potential risks before changes are implemented. Once the risks have been analyzed and the appropriate measures have been taken to minimize them, the change can be approved and implemented.
Risk analysis is an important step in the change management process because it helps identify and mitigate potential risks before changes are implemented. Once the risks have been analyzed and the appropriate measures have been taken to minimize them, the change can be approved and implemented.
NEW QUESTION 3
A PC is taking a long time to boot. Which of the following operations would be best to do to resolve the issue at a minimal expense? (Select two).
- A. Installing additional RAM
- B. Removing the applications from startup
- C. Installing a faster SSD
- D. Running the Disk Cleanup utility
- E. Defragmenting the hard drive
- F. Ending the processes in the Task Manager
Answer: BD
Explanation:
Removing the applications from startup can improve the boot time of a PC by reducing the number of programs that load automatically when the PC starts. Some applications may add themselves to the startup list without the user’s knowledge or consent, which can slow down the PC’s performance. Running the Disk Cleanup utility can also improve the boot time of a PC by deleting unnecessary or temporary files that take up disk space and affect the PC’s speed. Disk Cleanup can also remove old system files that may cause conflicts or errors during booting. Installing additional RAM, installing a faster SSD, defragmenting the hard drive, and ending the processes in the Task Manager are not operations that would be best to do to resolve the issue of slow boot time at a minimal expense, as they may require purchasing new hardware or software, or may have negative impacts on other aspects of the PC’s performance.
consent, which can slow down the PC’s performance. Running the Disk Cleanup utility can also improve the boot time of a PC by deleting unnecessary or temporary files that take up disk space and affect the PC’s speed. Disk Cleanup can also remove old system files that may cause conflicts or errors during booting. Installing additional RAM, installing a faster SSD, defragmenting the hard drive, and ending the processes in the Task Manager are not operations that would be best to do to resolve the issue of slow boot time at a minimal expense, as they may require purchasing new hardware or software, or may have negative impacts on other aspects of the PC’s performance.
NEW QUESTION 4
A technician connects an additional monitor to a PC using a USB port. The original HDMI monitor is mounted to the left of the new monitor. When moving the mouse to the right from the original monitor to the new monitor, the mouse stops at the end of the screen on the original monitor. Which
of the following will allow the mouse to correctly move to the new monitor?
- A. Rearranging the monitor's position in display settings
- B. Swapping the cables for the monitors
- C. Using the Ctrl+AIt+> to correct the display orientation
- D. Updating the display drivers for the video card
Answer: B
Explanation:
The correct answer is B. Swapping the cables for the monitors. When the second monitor is connected with the HDMI port, it is necessary to swap the cables for the monitors so that the mouse can move from the original monitor to the new monitor. This is because the HDMI port is designed to only support one monitor, and the mouse will not be able to move from one to the other without the cables being swapped.
According to CompTIA A+ Core 2 documents, "When connecting multiple displays to a system, the cables used to connect the displays must be swapped between the displays. For example, if a monitor is connected to a system using a VGA cable, the VGA cable must be moved to the next display to allow the mouse to move between the two displays."
NEW QUESTION 5
Which of the following file extensions should a technician use for a PowerShell script?
- A.
 .ps1
.ps1 - B. .py
- C. .sh
- D. .bat
- E. .cmd
Answer: A
Explanation:
A PowerShell script is a plain text file that contains one or more PowerShell commands. Scripts have a .ps1 file extension and can be run on your computer or in a remote session. PowerShell scripts can be used to automate tasks and change settings on Windows devices. To create and run a PowerShell script, you need a text editor (such as Visual Studio Code or Notepad) and the PowerShell Integrated Scripting Environment (ISE) console. You also need to enable the correct execution policy to allow scripts to run on your system
NEW QUESTION 6
A customer calls the help desk asking for instructions on how to modify desktop wallpaper. Which of the following Windows 10 settings should the technician recommend?
- A. Personalization
- B. Apps
- C. Updates
- D. Display
Answer: A
Explanation:
Personalization is a Windows 10 setting that allows a user to modify the desktop wallpaper, as well as other aspects of the appearance and behavior of the desktop, such as colors, themes, sounds, etc. Apps is a Windows 10 setting that allows a user to manage the installed applications and their features. Updates is a Windows 10 setting that allows a user to check for and install the latest updates for the OS and other components. Display is a Windows 10 setting that allows a user to adjust the screen resolution, brightness, orientation, etc. Verified References: https://www.comptia.org/blog/windows-10-settings https://www.comptia.org/certifications/a
NEW QUESTION 7
A user receives a notification indicating the antivirus protection on a company laptop is out of date. A technician is able to ping the user's laptop. The technician checks the antivirus parent servers and sees the latest signatures have been installed. The technician then checks the user's laptop and finds the antivirus engine and definitions are current. Which of the following has MOST likely occurred?
- A. Ransomware
- B. Failed OS updates
- C. Adware
- D. Missing system files
Answer: B
Explanation:
The most likely reason for the antivirus protection on a company laptop being out of date is failed OS updates1. Antivirus software relies on the operating system to function properly. If the operating system is not up-to-date, the antivirus software may not function properly and may not be able to receive the latest virus definitions and updates2. Therefore, it is important to keep the operating system up-to-date to ensure the antivirus software is functioning properly2.
NEW QUESTION 8
During a recent flight an executive unexpectedly received several dog and cat pictures while trying to watch a movie via in-flight Wi-Fi on an iPhone. The executive has no records of any contacts sending pictures like these and has not seen these pictures before. To BEST resolve this issue, the executive should:
- A. set AirDrop so that transfers are only accepted from known contacts
- B. completely disable all wireless systems during the flight
- C. discontinue using iMessage and only use secure communication applications
- D. only allow messages and calls from saved contacts
Answer: A
Explanation:
To best resolve this issue, the executive should set AirDrop so that transfers are only accepted from known contacts (option A). AirDrop is a feature on iOS devices that allows users to share files, photos, and other data between Apple devices. By setting AirDrop so that it only accepts transfers from known contacts, the executive can ensure that unwanted files and photos are not sent to their device. Additionally, the executive should ensure that the AirDrop setting is only enabled when it is necessary, as this will protect their device from any unwanted files and photos.
NEW QUESTION 9
A police officer often leaves a workstation for several minutes at a time. Which of the following is the BEST way the officer can secure the workstation quickly when walking away?
- A. Use a key combination to lock the computer when leaving.
- B. Ensure no unauthorized personnel are in the area.
- C. Configure a screensaver to lock the computer automatically after approximately 30 minutes of inactivity.
- D. Turn off the monitor to prevent unauthorized visibility of information.
Answer: A
Explanation:
The BEST way to secure the workstation quickly when walking away is to use a key combination to lock the computer when leaving1
NEW QUESTION 10
A technician is troubleshooting a lack of outgoing audio on a third-party Windows 10 VoIP application, The PC uses a USB microphone connected to a powered hub. The technician verifies the microphone works on the PC using Voice Recorder. Which of the following should the technician do to solve the issue?
- A. Remove the microphone from the USB hub and plug it directly into a USB port on the PC.
- B. Enable the microphone under Windows Privacy settings to allow desktop applications to access it.
- C. Delete the microphone from Device Manager and scan for new hardware,
- D. Replace the USB microphone with one that uses a traditional 3.5mm plug.
Answer: B
Explanation:
In Windows 10, there are privacy settings that control access to certain devices, such as microphones, cameras, and other input devices. If the microphone is not enabled under these privacy settings, the VoIP application may not have access to it, causing a lack of outgoing audio. The technician can go to the Windows 10 Settings menu, select the Privacy submenu, and under App permissions, select Microphone. The technician should then turn on the toggle switch for the VoIP application to allow it to access the microphone.
The technician can go to the Windows 10 Settings menu, select the Privacy submenu, and under App permissions, select Microphone. The technician should then turn on the toggle switch for the VoIP application to allow it to access the microphone.
Removing the microphone from the USB hub and plugging it directly into a USB port on the PC may or may not solve the issue, as the issue could be related to the privacy settings. Deleting the microphone from Device Manager and scanning for new hardware may also not solve the issue, as the issue could be related to the privacy settings. Replacing the USB microphone with one that uses a traditional 3.5mm plug is not recommended, as it would require purchasing a new microphone and may not solve the issue.
NEW QUESTION 11
A hotel's Wi-Fi was used to steal information on a corporate laptop. A technician notes the following security log: SRC: 192.168.1.1/secrets.zip Protocol SMB >> DST: 192.168.1.50/capture The technician analyses the following Windows firewall information:
SRC: 192.168.1.1/secrets.zip Protocol SMB >> DST: 192.168.1.50/capture The technician analyses the following Windows firewall information: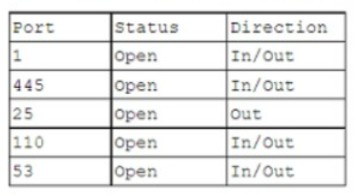
Which of the following protocols most likely allowed the data theft to occur?
- A. 1
- B. 53
- C. 110
- D. 445
Answer: D
Explanation:
The protocol that most likely allowed the data theft to occur is SMB over TCP port 445. SMB is a network file sharing protocol that enables access to files, printers, and other resources on a network. Port 445 is used by SMB to communicate directly over TCP without the need for NetBIOS, which is an older and less secure protocol. The security log shows that the source IP address 192.168.1.1 sent a file named secrets.zip using SMB protocol to the destination IP address 192.168.1.50, which captured the file. The Windows firewall information shows that port 445 is enabled for inbound and outbound traffic, which means that it is not blocked by the firewall. Therefore, port 445 is the most likely port that was exploited by the attacker to steal the data from the corporate laptop.
References:
✑ SMB port number: Ports 445, 139, 138, and 137 explained1
✑ What is an SMB Port + Ports 445 and 139 Explained2
✑ CompTIA A+ Certification Exam Core 2 Objectives3
NEW QUESTION 12
An administrator has submitted a change request for an upcoming server deployment. Which of the following must be completed before the change can be approved?
- A. Risk analysis
- B. Sandbox testing
- C. End user acceptance
- D. Lessons learned
Answer: A
Explanation:
Risk analysis is the process of identifying and evaluating the potential threats and impacts of a change on the system, network, or service. It is an essential step before approving a change request, as it helps to determine the level of risk, the mitigation strategies, and the contingency plans. Risk analysis also helps to prioritize the change requests based on their urgency and importance12.
References: 1 The Change Request Process and Best Practices(https://www.processmaker.com/blog/it-change-request-process-best- practices/)2 Risk Assessment and Analysis Methods: Qualitative and Quantitative(https://www.isaca.org/resources/isaca-journal/issues/2021/volume-2/risk- assessment-and-analysis-methods).
NEW QUESTION 13
A technician is replacing the processor in a desktop computer prior to opening the computer, the technician wants to ensure the internal components are protected. Which of the following safety procedures would BEST protect the components in the PC? (Select TWO).
- A. Utilizing an ESD strap
- B. Disconnecting the computer from the power source
- C. Placing the PSU in an antistatic bag
- D. Ensuring proper ventilation
- E. Removing dust from the ventilation fans
- F. Ensuring equipment is grounded
Answer: AC
Explanation:
The two safety procedures that would best protect the components in the PC are:
✑ Utilizing an ESD strap
✑ Placing the PSU in an antistatic bag
https://www.professormesser.com/free-a-plus-training/220-902/computer-safety- procedures-2/
https://www.skillsoft.com/course/comptia-a-core-2-safety-procedures-environmental-impacts-cbdf0f2c-61c0-4f4a-a659-dc98f1f00158
NEW QUESTION 14
A technician is trying to connect to a user's laptop in order to securely install updates. Given the following information about the laptop: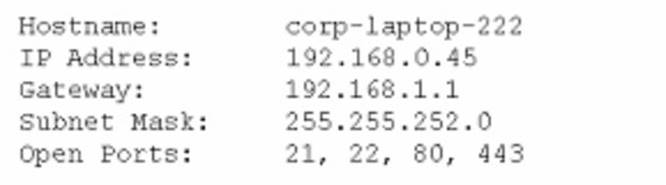
Which of the following should the technician do to connect via RDP?
- A. Confirm the user can ping the default gateway.
- B. Change the IP address on the user's laptop.
- C. Change the subnet mask on the user's laptop.
- D. Open port 3389 on the Windows firewall.
Answer: D
Explanation:
In order to connect to a user’s laptop via RDP, the technician should open port 3389 on the Windows firewall. This is because RDP uses port 3389 for communication12. The other options are not necessary or relevant for establishing an RDP connection. ✑ Confirming the user can ping the default gateway is not required for RDP, as it
✑ Confirming the user can ping the default gateway is not required for RDP, as it
only tests the network connectivity between the user’s laptop and the router. RDP works over the internet, so the technician should be able to ping the user’s laptop directly using its IP address3.
✑ Changing the IP address on the user’s laptop is not needed for RDP, as long as
the IP address is valid and not conflicting with another device on the network. The user’s laptop has a valid IP address of 192.168.0.45, which belongs to the same subnet as the gateway (192.168.0.1) and the subnet mask (255.255.255.0)4.
✑ Changing the subnet mask on the user’s laptop is not required for RDP, as long as
the subnet mask matches the network configuration. The user’s laptop has a correct subnet mask of 255.255.255.0, which defines a network with 254 possible hosts4.
References:
1: [What is RDP and How Does It Work? - CompTIA] 2: CompTIA A+ Certification Exam Core 2 Objectives - CompTIA 3: [Ping (networking utility) - Wikipedia] 4: [IP address - Wikipedia] : What is RDP and How Does It Work? - CompTIA : CompTIA A+ Certification Exam Core 2 Objectives - CompTIA : Ping (networking utility) - Wikipedia) : IP address - Wikipedia
NEW QUESTION 15
A technician is working on a Windows 10 PC that has unwanted applications starting on boot. Which of the following tools should the technician use to disable applications on startup?
Solution:
Task Manager is the best tool to use to disable applications on startup in Windows 10. Task Manager is a built-in utility that shows the current processes, performance, and users on a system. It also has a Startup tab that lists the applications that run on boot and their impact on the system. The technician can use Task Manager to disable or enable any application on startup by right-clicking on it and selecting the appropriate option. System Configuration, Performance Monitor, and Group Policy Editor are other tools that can be used to manage system settings, but they are not as simple or convenient as Task Manager for this task. References:
✑ Official CompTIA learning resources CompTIA A+ Core 1 and Core 2, page 13
✑ CompTIA A+ Complete Study Guide: Core 1 Exam 220-1101 and Core 2 Exam …, page 103
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 16
A Windows user reported that a pop-up indicated a security issue. During inspection, an antivirus system identified malware from a recent download, but it was unable to remove the malware. Which of the following actions would be BEST to remove the malware while also preserving the user's files?
- A. Run the virus scanner in an administrative mode.
- B. Reinstall the operating system.
- C. Reboot the system in safe mode and rescan.
- D. Manually delete the infected files.
Answer: C
Explanation:
Rebooting the system in safe mode will limit the number of programs and processes running, allowing the antivirus system to more effectively identify and remove the malware. Rescanning the system will allow the antivirus system to identify and remove the malware while preserving the user's files.
NEW QUESTION 17
Which of the following would most likely be used to extend the life of a device?
- A. Battery backup
- B. Electrostatic discharge mat
- C. Proper ventilation
- D. Green disposal
Answer: C
Explanation:
Proper ventilation is a factor that can extend the life of a device by preventing overheating and thermal damage to the device’s components. Proper ventilation means ensuring that there is enough airflow around and inside the device to dissipate heat and maintain a suitable temperature for optimal performance. Proper ventilation can be achieved by using fans, heat sinks, vents, or liquid cooling systems, as well as avoiding placing the device near heat sources or in enclosed spaces. Battery backup, electrostatic discharge mat, and green disposal are not factors that can extend the life of a device.
NEW QUESTION 18
A user's company phone was stolen. Which of the following should a technician do next?
- A. Perform a low-level format.
- B. Remotely wipe the device.
- C. Degauss the device.
- D. Provide the GPS location of the device.
Answer: B
Explanation:
Remotely wiping the device is the best option to prevent unauthorized access to the company data stored on the phone. A low-level format, degaussing, or providing the GPS location of the device are not feasible or effective actions to take in this scenario.
References: The Official CompTIA A+ Core 2 Study Guide1, page 315.
NEW QUESTION 19
A technician installed Windows 10 on a workstation. The workstation only has 3.5GB of usable RAM, even though the technician installed 8GB. Which of the following is the MOST likely reason this system is not utilizing all the
available RAM?
- A. The system is missing updates.
- B. The systems utilizing a 32-bit OS.
- C. The system's memory is failing.
- D. The system requires BIOS updates.
Answer: B
Explanation:
The most likely reason that the system is not utilizing all the available RAM is that it is running a 32-bit OS. A 32-bit OS can only address up to 4GB of RAM, and some of that is reserved for hardware and system use1. Therefore, even if the technician installed 8GB of RAM, the system can only use around 3.5GB of usable RAM. To use the full 8GB of RAM, the technician would need to install a 64-bit OS, which can address much more memory2. The system missing updates, the system’s memory failing, or the system requiring BIOS updates are not likely to cause this issue.
References: 2: https://support.microsoft.com/en-us/windows/windows-10-system-
requirements-6d4e9a79-66bf-7950-467c-795cf0386715 1: https://www.makeuseof.com/tag/unlock-64gb-ram-32-bit-windows-pae-patch/
NEW QUESTION 20
......
Recommend!! Get the Full 220-1102 dumps in VCE and PDF From Allfreedumps.com, Welcome to Download: https://www.allfreedumps.com/220-1102-dumps.html (New 757 Q&As Version)