Refined 300-165 Braindumps 2021
Your success in is our sole target and we develop all our in a way that facilitates the attainment of this target. Not only is our material the best you can find, it is also the most detailed and the most updated. for Cisco 300-165 are written to the highest standards of technical accuracy.
Online 300-165 free questions and answers of New Version:
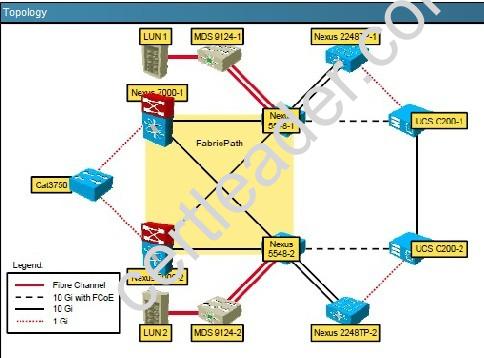
NEW QUESTION 1
Which command configures the aging time for VLAN 100 to 50 minutes?
- A. mac address-table aging-time 3000 vlan 100
- B. mac address-table aging-time 50
- C. mac address-table aging-time 300
- D. mac address-table aging-time 50 vlan 100
Answer: A
NEW QUESTION 2
Refer to the exhibit.
Which result of the configuration snippet is true?
- A. A VACL map in applied to VLAN 101 and VLAN 200
- B. VACL acl is applied to VLAN 100 through 200
- C. Acl is applied to all of the VLANs on the switch
- D. Global statistics are provided for the ACL map
Answer: B
NEW QUESTION 3
Which two Cisco Nexus platforms support Adapter FEX? (Choose two.)
- A. Cisco Nexus 7000 Series Switches
- B. Cisco Nexus 5000 Series Switches
- C. Cisco Nexus 5500 Series Switches
- D. Cisco Nexus 4000 Series Switches
- E. Cisco Nexus 2000 Series Fabric Extenders
Answer: CE
Explanation: At the access layer, the Adapter-FEX requires a FEX-enabled adapter on a server that connects to a parent device that supports virtualization of interfaces. The Adapter-FEX is supported on the following platforms:
• The Cisco Unified Computing System (UCS) platform supports Adapter-FEX between UCS servers and the UCS Fabric Interconnect.
• The Adapter-FEX is supported on the Cisco Nexus 5500 Series platform and on the Cisco Nexus 2200 Fabric Extender that is connected to a Cisco Nexus 5500 Series parent device. This implementation works on a variety of FEX-capable adapters, including the Cisco UCS P81E virtual interface card (VIC) adapter for the UCS C-Series platform and third party adapters such as the Broadcom BCM57712 Convergence Network Interface Card, that implement the virtual network tag (VNTag) technology.
Reference: http://www.cisco.com/c/en/us/td/docs/switches/datacenter/nexus5000/sw/operations/adapter_fex
/513_n1_1/ops_adapter_fex/ops_using_adapter_fex.html
NEW QUESTION 4
Which two protocols can be used to back up the configuration of a Cisco Nexus 5600 Series switch to a remote location? (Choose two.)
- A. NFS
- B. SCP
- C. SMB
- D. CIFS
- E. SFTP
Answer: BE
NEW QUESTION 5
What is the default Fibre Channel interface type for an FCIP virtual interface?
- A. TF
- B. E
- C. TE
- D. F
Answer: B
NEW QUESTION 6
Which statement about Cisco FabricPath is true?
- A. It is the best solution for interconnecting multiple data centers.
- B. It optimizes STP throughout the Layer 2 network.
- C. It is a simplified extension of Layer 3 networks across a single data center.
- D. The Cisco FabricPath domain appears as a single STP bridge, where each edge port uses the same MAC address.
Answer: D
Explanation: To have a loop-free topology for the CE/FabricPath hybrid network, the FabricPath network automatically displays as a single bridge to all connected CE devices. The STP domains do not cross into the FabricPath network. If multiple STP domains are defined, BPDUs and topology change notifications (TCNs) are localized to the domain. If a connected STP domain is multihomed to the FabricPath domain, a TCN must be able to reach to all devices in the STP domain through the FabricPath domain. As a result, the TCN is sent to the FabricPath domain through the IS-IS protocol data unit (PDU) by default.
Reference: http://www.cisco.com/en/US/docs/switches/datacenter/nexus5000/sw/mkt_ops_guides/513_n1_1/n5k_ops_fabricpath.html
NEW QUESTION 7
Which two advantages does FabricPath have over Spanning Tree in implementing a loop-free network topology design? (Choose two.)
- A. Blocked links can be brought in to service if active links fail.
- B. Convergence times are faster.
- C. Multipath forwarding is supported for unicast and multicast Layer 2 and Layer 3 traffic.
- D. Unknown unicast addresses are flooded in through the originating por
Answer: BC
NEW QUESTION 8
Which two features are required to implement a Layer 3 VXLAN gateway on the Cisco Nexus 5600 Series platform? (Choose two.)
- A. feature mpls
- B. feature nv overlay
- C. feature lldp
- D. feature eigrp
- E. feature vn-segment-vlan-based
Answer: BE
NEW QUESTION 9
Which implicit rules are applied to all IPv6 ACLs?
- A. deny icmp any any nd-na deny icmp any any nd-nspermit icmp any any router-advertisement permit icmp any any router-solicitation deny ipv6 any any
- B. deny icmp any any nd-na log deny icmp any any nd-ns log deny ipv6 any any log
- C. deny icmp any any router-advertisement log deny icmp any any router-solicitation log deny ipv6 any any log
- D. permit icmp any any nd-na permit icmp any any nd-nspermit icmp any any router-advertisement permit icmp any any router-solicitation deny ipv6 any any
Answer: D
NEW QUESTION 10
Which two actions are required before FIPS is configured in Cisco MDS? (Choose two.)
- A. Passwords must be a minimum of 10 characters in length.
- B. SNMP v2 or v3 must be enabled.
- C. Remote authentication must occur utilizing RADIUS/TACACS+.
- D. Disable VRRP.
- E. Delete all SSH server RSA key pairs.
- F. Delete all IKE policies utilizing MD5 or DES for encryption.
- G. Enable the FC-FIPS feature.
- H. Disable SS
Answer: DF
NEW QUESTION 11
Which two PIM modes on a Cisco Nexus 7000 Series switch require you to configure an RP? (Choose two)
- A. SDM
- B. DM
- C. ASM
- D. SSM
- E. BIDIR
Answer: CE
Explanation: Any Source Multicast (ASM) provides discovery of multicast sources. It builds a shared tree between sources and receivers of a multicast group and supports switching over to a source tree when a new receiver is added to a group. ASM mode requires that you configure an RP.
Single Source Multicast (SSM) builds a source tree originating at the designated router on the LAN segment that receives a request to join a multicast source. SSM mode does not require you to configure RPs. Source discovery must be accomplished through other means.
Bidirectional shared trees (Bidir) build a shared tree between sources and receivers of a multicast group but do not support switching over to a source tree when a new receiver is added to a group. Bidir mode requires that you configure an RP. Bidir forwarding does not require source discovery because only the shared tree is used.
Reference: https://www.cisco.com/c/en/us/td/docs/switches/datacenter/sw/5_x/nxos/ multicast/configuration/guide/n7k_multic_cli_5x/pim.html
NEW QUESTION 12
You are configuring OTV between two data centers. On which interfaces should the site VLAN allowed?
- A. the interfaces that connect to the aggregation switches
- B. the OTV overlay interfaces
- C. the interfaces that connect to the join interfaces
- D. the mgmt0 interfaces
Answer: A
NEW QUESTION 13
Refer to the exhibit.
Which two options are results of the configuration on the Cisco Nexus switch are true? (Choose two.)
- A. When the interface receives a packet triggering the violation, address learning is stopped and ingress traffic from the nonsecure MAC address is dropped
- B. When the interface receives a packet triggering the violation, a syslog message is logged, address learning continues, and all traffic continues, and traffic continues to forwarded
- C. Port security on the Ethernet 2/1 interface uses the dynamic method for MAC address learning
- D. When the interface receives a packet triggering the volition, the interface is error disable
- E. Port security on the Ethernet 2/1 interface users the sticky method for MAC address learning all traffic continue to be
Answer: AC
NEW QUESTION 14
When configuring PIM to support an OTV implementation, Which PIM configuration is supported in Cisco NX-OS?
- A. Switch(config-if)tt ip pirn ssm default
- B. switch(config-if)# ip pim sparse-mode
- C. Switch(config-if)tf ip pim spase-mode
- D. Switch(config-if)tf ip pim sparse-dense-mode
Answer: B
Explanation: https://www.cisco.com/c/en/us/td/docs/switches/datacenter/nexus9000/sw/6- x/multicast/configuration/guide/b_Cisco_Nexus_9000_Series_NXOS_ Multicast_Routing_Configuration_Guide/b_Cisco_Nexus_9000_Series_NXOS_ Multicast_Routing_Configuration_Guide_chapter_011.html
NEW QUESTION 15
DRAG DROP
Drag the description on the left to the most appropriate FCoE protocol or feature on the right.
Answer:
Explanation: ENODES: During FLOGI or FDISC, the ENode advertises the addressing modes it supports. If the FC switch supports an addressing mode that the ENode uses, the virtual link can be established, and the devices can communicate.
FIP: FIP is the set of control plane functions that enable discovery of FCoE-capable devices across FCoE passthrough switches and establishment of legal combinations of virtual links.
FCF: FCoE Initialization Protocol (FIP) is the FCoE control protocol responsible for establishing and maintaining Fibre Channel virtual links between pairs of FCoE devices (ENodes or FCFs). During the virtual link establishment phase, FIP first discovers FCoE VLANs and remote virtual FC interfaces; then it performs virtual link initialization functions (fabric login [FLOGI] and fabric discovery [FDISC], or exchange link parameters [ELP]) similar to their native Fibre Channel equivalents. After the virtual link is established, Fibre Channel payloads can be exchanged on the virtual link, and FIP remains in
the background to perform virtual link maintenance functions; it continuously verifies reachability between the two virtual FC interfaces on the Ethernet network, and it offers primitives to delete the virtual link in response to administrative actions to that effect. This document does not describe the virtual link maintenance functions of FIP.
NEW QUESTION 16
FabricPath switch-id is 25 and load-balance is configured for L3/L4 and rotate amount is 14 byte. What information is true about FabricPath switch-id?

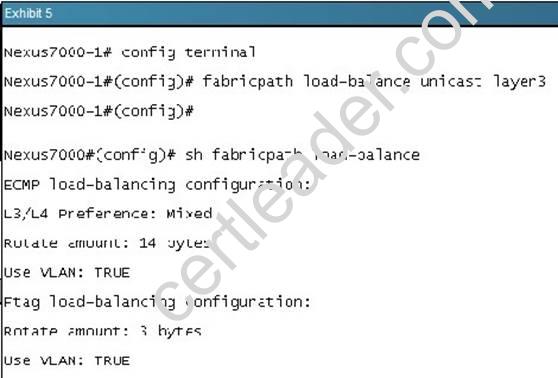
- A. FabricPath topology requires manual configuration of switch-id which has a range from 1 to 4095
- B. Every FabricPath must have a manually configured switch-id for it to form a FabricPath topology
- C. FabricPath topology requires manual configuration of switch-id which has a range from 1 to 4099
- D. You do not have to manually assign a switch ID unless you are running a virtual port channel plus (vPC+) because the system assigns a switch ID for you when you enable FabricPath
Answer: D
Explanation: fabricpath switch-id (vPC)
To configure a virtual port channel plus (vPC+) switch ID, use the fabricpath switch-id command. To remove the FabricPath switch from a vPC domain, use the no form of this command.
fabricpath switch-id switch-id
no fabricpath switch-id [ switch-id ] Usage Guidelines
You do not have to manually assign a switch ID (unless you are running a vPC+); the system assigns a switch ID for you when you enable FabricPath.
Note You must assign the same vPC+ switch ID to each of the two vPC+ peer devices before they can form an adjacency.
This command requires an Enhanced Layer 2 license. Examples
This example shows how to configure a vPC+ switch ID on a FabricPath-enabled device: switch# configure terminal
switch(config)# vpc domain 1
switch(config-vpc-domain)# fabricpath switch-id 1
Configuring fabricpath switch id will flap vPCs. Continue (yes/no)? [no]
NEW QUESTION 17
Which three types of interfaces are required when implementing VXLAN on a Cisco Nexus 9000 Series Switch? (Choose three.)
- A. overlay
- B. NVE
- C. management
- D. Ethernet
- E. ACI
- F. loopback
Answer: BDF
NEW QUESTION 18
Which three attributes encompass a local user account on a Cisco NX-OS device? (Choose three.)
- A. expiration date
- B. cisco-avpair
- C. password
- D. AAA server address
- E. user roles
- F. bind user DN
- G. user privileges
Answer: ACE
NEW QUESTION 19
Which policy-map action performs congestion avoidance?
- A. priority
- B. bandwidth
- C. queue-limit
- D. random-detect
Answer: D
Explanation: Congestion avoidance techniques monitor network traffic loads in an effort to anticipate and avoid congestion at common network bottlenecks. Congestion avoidance is achieved through packet dropping. Among the more commonly used congestion avoidance mechanisms is Random Early Detection (RED), which is optimum for high-speed transit networks. Cisco IOS QoS includes an implementation of RED that, when configured, controls when the router drops packets. If you do not configure Weighted Random Early Detection (WRED), the router uses the cruder default packet drop mechanism called tail drop.
Reference: http://www.cisco.com/c/en/us/td/docs/ios/12_2/qos/configuration/guide/fqos_c/qcfconav.html
NEW QUESTION 20
In Any Source Multicast groups which multicast enabled device supports shared trees?
- A. RP
- B. any router in the tree except for the RP
- C. first-hop router
- D. last-hop router
Answer: A
Recommend!! Get the Full 300-165 dumps in VCE and PDF From Certleader, Welcome to Download: https://www.certleader.com/300-165-dumps.html (New 286 Q&As Version)