The Secret Of GIAC GPEN Exam Engine
Exam Code: GPEN (Practice Exam Latest Test Questions VCE PDF)
Exam Name: GIAC Certified Penetration Tester
Certification Provider: GIAC
Free Today! Guaranteed Training- Pass GPEN Exam.
Free demo questions for GIAC GPEN Exam Dumps Below:
NEW QUESTION 1
Which of the following penetration testing phases involves gathering data from whois, DNS, and network scanning, which helps in mapping a target network and provides valuable information regarding the operating system and applications running on the systems?
- A. Post-attack phase
- B. Attack phase
- C. On-attack phase
- D. Pre-attack phase
Answer: D
NEW QUESTION 2
While reviewing traffic from a tcpdump capture, you notice the following commands being sent from a remote system to one of your web servers:
C:\>sc winternet.host.com create ncservicebinpath- "c:\tools\ncexe -I -p 2222 -e cmd.exe"
C:\>sc vJnternet.host.com query ncservice.
What is the intent of the commands?
- A. The first command creates a backdoor shell as a servic
- B. It is being started on TCP2222 using cmd.ex
- C. The second command verifies the service is created and itsstatu
- D. The first command creates a backdoor shell as a servic
- E. It is being started on UDP2222 using cmd.ex
- F. The second command verifies the service is created and itsstatu
- G. This creates a service called ncservice which is linked to the cmd.exe command andits designed to stop any instance of nc.exe being ru
- H. The second command verifiesthe service is created and its statu
- I. The first command verifies the service is created and its statu
- J. The secondcommand creates a backdoor shell as a servic
- K. It is being started on TCP 2222connected to cmd.ex
Answer: C
NEW QUESTION 3
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He performs a Teardrop attack on the we-are-secure server and observes that the server crashes. Which of the following is the most likely cause of the server crash?
- A. The spoofed TCP SYN packet containing the IP address of the target is filled in both the source and destination field
- B. The we-are-secure server cannot handle the overlapping data fragment
- C. The ICMP packet is larger than 65,536 byte
- D. Ping requests at the server are too hig
Answer: B
NEW QUESTION 4
Which of the following is a Windows-based tool that is used for the detection of wireless LANs using the IEEE 802.11a, 802.11b, and 802.11g standards and also detects wireless networks marking their relative position with a GPS?
- A. Kismet
- B. NetStumbler
- C. Ettercap
- D. Tcpdump
Answer: B
NEW QUESTION 5
You work as a professional Computer Hacking Forensic Investigator for DataEnet Inc. You want to investigate e-mail information of an employee of the company. The suspected employee is using an online e-mail system such as Hotmail or Yahoo. Which of the following folders on the local computer will you review to accomplish the task?
Each correct answer represents a complete solution. Choose all that apply.
- A. History folder
- B. Temporary Internet Folder
- C. Cookies folder
- D. Download folder
Answer: ABC
NEW QUESTION 6
You work as a Penetration Tester for the Infosec Inc. Your company takes the projects of security auditing. Recently, your company has assigned you a project to test the security of the we-aresecure. com Website. The we-are-secure.com Web server is using Linux operating system. When you port scanned the we-are-secure.com Web server, you got that TCP port 23, 25, and 53 are open. When you tried to telnet to port 23, you got a blank screen in response. When you tried to type the dir, copy, date, del, etc. commands you got only blank spaces or underscores symbols on the screen. What may be the reason of such unwanted situation?
- A. The we-are-secure.com server is using honeypo
- B. The we-are-secure.com server is using a TCP wrappe
- C. The telnet service of we-are-secure.com has corrupte
- D. The telnet session is being affected by the stateful inspection firewal
Answer: B
NEW QUESTION 7
Adam works as a professional Computer Hacking Forensic Investigator. He works with the local police. A project has been assigned to him to investigate an iPod, which was seized from a student of the high school. It is suspected that the explicit child pornography contents are stored in the iPod. Adam wants to investigate the iPod extensively. Which of the following operating systems will Adam use to carry out his investigations in more extensive and elaborate manner?
- A. MINIX 3
- B. Linux
- C. Windows XP
- D. Mac OS
Answer: D
NEW QUESTION 8
Which of the following does NOT use a proxy software to protect users?
- A. Stateful inspection
- B. Packet filtering
- C. Application layer gateway
- D. Circuit level proxy server
Answer: D
NEW QUESTION 9
Which of the following is possible in some SQL injection vulnerabilities on certain types of databases that affects the underlying server OS?
- A. Database structure retrieval
- B. Shell command execution
- C. Data manipulation
- D. Data query capabilities
Answer: A
Explanation:
Reference:
http://www.darkmoreops.com/2014/08/28/use-sqlmap-sql-injection-hack-website-database/
NEW QUESTION 10
You want to retrieve password files (stored in the Web server's index directory) from various Web sites. Which of the following tools can you use to accomplish the task?
- A. Nmap
- B. Sam spade
- C. Whois
- D. Google
Answer: D
NEW QUESTION 11
During a penetration test we determine that TCP port 22 is listening on a target host. Knowing that SSHD is the typical service that listens on that port we attempt to validate that assumption with an SSH client but our effort Is unsuccessful. It turns out that it is actually an Apache webserver listening on the port, which type of scan would have helped us to determine what service was listening on port 22?
- A. Version scanning
- B. Port scanning
- C. Network sweeping
- D. OS fingerprinting
Answer: C
NEW QUESTION 12
You want to run the nmap command that includes the host specification of 202.176.56-57.*. How many hosts will you scan?
- A. 1024
- B. 256
- C. 512
- D. 64
Answer: C
NEW QUESTION 13
In which of the following attacks does an attacker use packet sniffing to read network traffic between two parties to steal the session cookie?
- A. Cross-site scripting
- B. Session sidejacking
- C. ARP spoofing
- D. Session fixation
Answer: B
NEW QUESTION 14
Analyze the command output below. What information can the tester infer directly from the information shown? 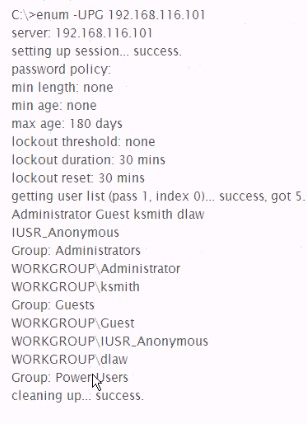
- A. The administrator account has no password
- B. Null sessions are enabled on the target
- C. The target host is running Linux with Samba services
- D. Account lockouts must be reset by the Administrator
Answer: C
NEW QUESTION 15
Which of the following is a tool for SSH and SSL MITM attacks?
- A. Ettercap
- B. Cain
- C. Dsniff
- D. AirJack
Answer: C
NEW QUESTION 16
168.1 200, which of the following would you see?
- A. Ping-n 1 192.168.1 200 on the compromised system
- B. A 'Destination host unreachable' error message on the compromised system
- C. A packet containing 'Packets: Sent - 1 Received = 1, Loss = 0 (0% loss) on yoursniffer
- D. An ICMP Echo packet on your sniffer containing the source address of the target
Answer: A
NEW QUESTION 17
Which of the following is NOT a Back orifice plug-in?
- A. BOSOCK32
- B. STCPIO
- C. BOPeep
- D. Beast
Answer: D
NEW QUESTION 18
You want to connect to your friend's computer and run a Trojan on it. Which of the following tools will you use to accomplish the task?
- A. Remoxec
- B. Hk.exe
- C. PSExec
- D. GetAdmin.exe
Answer: C
NEW QUESTION 19
......
Thanks for reading the newest GPEN exam dumps! We recommend you to try the PREMIUM Certshared GPEN dumps in VCE and PDF here: https://www.certshared.com/exam/GPEN/ (385 Q&As Dumps)