Avant-garde GPEN Free Question For GIAC Certified Penetration Tester Certification
It is impossible to pass GIAC GPEN exam without any help in the short term. Come to Exambible soon and find the most advanced, correct and guaranteed GIAC GPEN practice questions. You will get a surprising result by our Up to date GIAC Certified Penetration Tester practice guides.
Also have GPEN free dumps questions for you:
NEW QUESTION 1
Which of the following nmap switches is used to perform ICMP netmask scanning?
- A. -PM
- B. -PB
- C. -PI
- D. -PS
Answer: A
NEW QUESTION 2
LM hash is one of the password schemes that Microsoft LAN Manager and Microsoft Windows versions prior to the Windows Vista use to store user passwords that are less than 15 characters long. If you provide a password seven characters or less, the second half of the LM hash is always
__________.
- A. 0xBBD3B435B51504FF
- B. 0xAAD3B435B51404FF
- C. 0xBBC3C435C51504EF
- D. 0xAAD3B435B51404EE
Answer: D
NEW QUESTION 3
You want to create a binary log file using tcpdump. Which of the following commands will you use?
- A. tcpdump -B
- B. tcpdump -dd
- C. tcpdump -w
- D. tcpdump –d
Answer: C
NEW QUESTION 4
Which of the following is an open source Web scanner?
- A. Nikto
- B. GFI LANguird
- C. NetRecon
- D. Internet scanner
Answer: A
NEW QUESTION 5
Which of the following is the correct sequence of packets to perform the 3-way handshake method?
- A. SYN, ACK, ACK
- B. SYN, ACK, SYN/ACK
- C. SYN, SYN/ACK, ACK
- D. SYN, SYN, ACK
Answer: C
NEW QUESTION 6
Adam, a malicious hacker, hides a hacking tool from a system administrator of his company by using Alternate Data Streams (ADS) feature. Which of the following statements is true in context with the above scenario?
- A. Alternate Data Streams is a feature of Linux operating syste
- B. Adam's system runs on Microsoft Windows 98 operating syste
- C. Adam is using FAT file syste
- D. Adam is using NTFS file syste
Answer: D
NEW QUESTION 7
Which of the following statements are true about session hijacking?
Each correct answer represents a complete solution. Choose all that apply.
- A. TCP session hijacking is when a hacker takes over a TCP session between two machine
- B. It is the exploitation of a valid computer session to gain unauthorized access to information or services in a computer syste
- C. Use of a long random number or string as the session key reduces session hijackin
- D. It is used to slow the working of victim's network resource
Answer: ABC
NEW QUESTION 8
What is the purpose of die following command:
nc.exe -I -p 2222 -e cmd.exe
- A. It is used to start a persistent listener linked to cmd.exe on port 2222 TCP
- B. It is used to start a listener linked to cmd.exe on port 2222 TCP
- C. It is used to start a listener linked to cmd.exe on port 2222 UDP
- D. It is used to start a persistent listener linked to cmd.exe on port 2222 UDP
Answer: C
NEW QUESTION 9
What is the most likely cause of the responses on lines 10 and 11 of the output below? 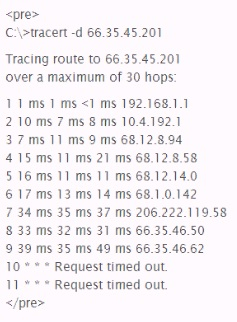
- A. The device at hop 10 silently drops UDP packets with a high destination por
- B. The device at hop 10 is down and not forwarding any requests at al
- C. The host running the tracer utility lost its network connection during the scan
- D. The devices at hops 10 and II did not return an "ICMP TTL Exceeded in Transit" messag
Answer: D
NEW QUESTION 10
Which of the following tools allows you to download World Wide Web sites from the Internet to a local computer?
- A. Netstat
- B. Netcraft
- C. HTTrack
- D. Cheops-ng
Answer: C
NEW QUESTION 11
You work as a Penetration Tester for the Infosec Inc. Your company takes the projects of security auditing. Recently, your company has assigned you a project to test the security of the we-aresecure. com network. Now, when you have finished your penetration testing, you find that the weare- secure.com server is highly vulnerable to SNMP enumeration. You advise the we-are-secure Inc. to turn off SNMP; however, this is not possible as the company is using various SNMP services on its remote nodes. What other step can you suggest to remove SNMP vulnerability?
Each correct answer represents a complete solution. Choose two.
- A. Change the default community string name
- B. Install antiviru
- C. Close port TCP 53.
- D. Upgrade SNMP Version 1 with the latest versio
Answer: AD
NEW QUESTION 12
Analyze the screenshot below, which of the following sets of results will be retrieved using this search? 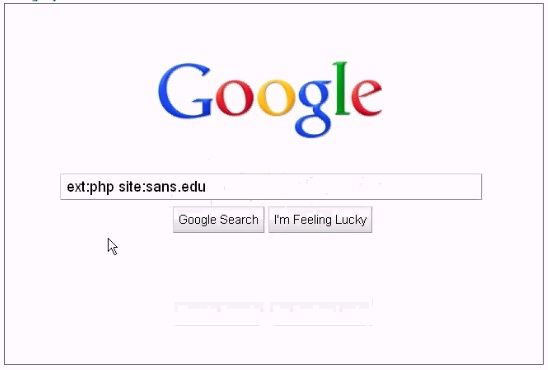
- A. Pages from the domain sans.edu that have external link
- B. Files of type .php from the domain sans.ed
- C. Pages that contain the term ext:php and slte.sans.ed
- D. Files of type .php that redirect to the sans.edu domai
Answer: A
NEW QUESTION 13
Which of the following tools is a wireless sniffer and analyzer that works on the Windows operating system?
- A. Void11
- B. Airsnort
- C. Kismet
- D. Aeropeek
Answer: D
NEW QUESTION 14
John works as a professional Ethical Hacker. He has been assigned a project to test the security of www.we-are-secure.com. He successfully performs a brute force attack on the We-are-secure server. Now, he suggests some countermeasures to avoid such brute force attacks on the We-aresecure server. Which of the following are countermeasures against a brute force attack?
Each correct answer represents a complete solution. Choose all that apply.
- A. The site should increase the encryption key length of the passwor
- B. The site should restrict the number of login attempts to only three time
- C. The site should force its users to change their passwords from time to tim
- D. The site should use CAPTCHA after a specific number of failed login attempt
Answer: BD
NEW QUESTION 15
What is the purpose of the following command?
C:\>wmic /node:[target IP] /user:[admin-user]
/password:[password] process call create [command]
- A. Running a command on a remote Windows machine
- B. Creating a service on a remote Windows machine
- C. Creating an admin account on a remote Windows machine
- D. Listing the running processes on a remote windows machine
Answer: D
NEW QUESTION 16
Your company has decided that the risk of performing a penetration test Is too great. You would like to figure out other ways to find vulnerabilities on their systems, which of the following is MOST likely to be a valid alternative?
- A. Network scope Analysis
- B. Baseline Data Reviews
- C. Patch Policy Review
- D. Configuration Reviews
Answer: A
NEW QUESTION 17
Which of the following tools allow you to perform HTTP tunneling?
Each correct answer represents a complete solution. Choose all that apply.
- A. BackStealth
- B. Tunneled
- C. Nikto
- D. HTTPort
Answer: ABD
NEW QUESTION 18
You have been contracted to map me network and try to compromise the servers for a client. Which of the following would be an example of scope creep' with respect to this penetration testing project?
- A. Disclosing information forbidden in the NDA
- B. Compromising a server then escalating privileges
- C. Being asked to compromise workstations
- D. Scanning network systems slowly so you are not detected
Answer: B
NEW QUESTION 19
......
Recommend!! Get the Full GPEN dumps in VCE and PDF From Allfreedumps.com, Welcome to Download: https://www.allfreedumps.com/GPEN-dumps.html (New 385 Q&As Version)