Top Tips Of Avant-garde GPEN Free Download
Cause all that matters here is passing the GIAC GPEN exam. Cause all that you need is a high score of GPEN GIAC Certified Penetration Tester exam. The only one thing you need to do is downloading Ucertify GPEN exam study guides now. We will not let you down with our money-back guarantee.
Free GPEN Demo Online For GIAC Certifitcation:
NEW QUESTION 1
You are conducting a penetration test for a private company located in the UK. The scope
extends to all internal and external hosts controlled by the company. You have gathered necessary hold-harmless and non-disclosure agreements. Which action by your group can incur criminal liability under the computer Misuse Act of 1990?
- A. Sending crafted packets to internal hosts in an attempt to fingerprint the operatingsystems
- B. Recovering the SAM database of the domain server and attempting to crackpasswords
- C. Installing a password sniffing program on an employee's personal computer withoutconsent
- D. Scanning open ports on internal user workstations and exploiting vulnerableapplications
Answer: B
NEW QUESTION 2
TCP/IP stack fingerprinting is the passive collection of configuration attributes from a remote device during standard layer 4 network communications. The combination of parameters may then be used to infer the remote operating system (OS fingerprinting), or incorporated into a device fingerprint. Which of the following Nmap switches can be used to perform TCP/IP stack fingerprinting?
- A. nmap -O -p
- B. nmap -sS
- C. nmap -sU -p
- D. nmap –sT
Answer: A
NEW QUESTION 3
Which of the following is the default port value of beast Trojan?
- A. 6666
- B. 2222
- C. 3333
- D. 1111
Answer: A
NEW QUESTION 4
Adam is a novice Internet user. He is using Google search engine to search documents of his interest. Adam wants to search the text present in the link of a Website. Which of the following operators will he use in his query to accomplish the task?
- A. inanchor
- B. info
- C. link
- D. site
Answer: A
NEW QUESTION 5
While scanning a remote system that is running a web server with a UDP scan and monitoring the scan with a sniffer, you notice that the target is responding with ICMP Port Unreachable only once a second What operating system is the target likely running?
- A. Linux
- B. Windows
- C. OpenBSD
- D. Mac OS X
Answer: A
NEW QUESTION 6
Which of the following standards is used in wireless local area networks (WLANs)?
- A. IEEE 802.4
- B. IEEE 802.3
- C. IEEE 802.11b
- D. IEEE 802.5
Answer: C
NEW QUESTION 7
Which of following tasks can be performed when Nikto Web scanner is using a mutation technique?
Each correct answer represents a complete solution. Choose all that apply.
- A. Guessing for password file name
- B. Sending mutation payload for Trojan attac
- C. Testing all files with all root directorie
- D. Enumerating user names via Apach
Answer: ACD
NEW QUESTION 8
Which of the following is the number of bits of encryption that 64-bit Wired Equivalent Privacy (WEP) effectively provides?
- A. 64
- B. 40
- C. 60
- D. 44
Answer: A
Explanation:
Reference:
http://en.wikipedia.org/wiki/Wired_Equivalent_Privacy
NEW QUESTION 9
Which of the following federal laws are related to hacking activities?
Each correct answer represents a complete solution. Choose three.
- A. 18 U.S.
- B. 1030
- C. 18 U.S.
- D. 1028
- E. 18 U.S.
- F. 2510
- G. 18 U.S.
- H. 1029
Answer: ACD
NEW QUESTION 10
You work as a Network Administrator for Tech-E-book Inc. You are configuring the ISA Server
2006 firewall to provide your company with a secure wireless intranet. You want to accept inbound mail delivery though an SMTP server. What basic rules of ISA Server do you need to configure to accomplish the task.
- A. Network rules
- B. Publishing rules
- C. Mailbox rules
- D. Access rules
Answer: B
NEW QUESTION 11
You suspect that a firewall or IPS exists between you and the target machine. Which nmap option will elicit responses from some firewalls and IPSs while being silently dropped by the target, thus confirming the existence of a firewall or IPS?
- A. –Traceroute
- B. –Firewalk
- C. –Badsum
- D. --SF
Answer: B
NEW QUESTION 12
You work as a Network Administrator in the Secure Inc. Your company is facing various network attacks due to the insecure wireless network. You are assigned a task to secure your wireless network. For this, you have turned off broadcasting of the SSID. However, the unauthorized users are still able to connect to the wireless network. Which of the following statements can be the reason for this issue?
Each correct answer represents a complete solution. Choose all that apply.
- A. You have forgotten to turn off DHC
- B. You are using WPA2 security schem
- C. The SSID is still sent inside both client and AP packet
- D. You are using the default SSI
Answer: ACD
NEW QUESTION 13
You are pen testing a Windows system remotely via a raw netcat shell. You want to get a listing of all the local users in the administrators group, what command would you use?
- A. Net account administrators
- B. Net user administrators
- C. Net localgroup administrators
- D. Net localuser administrators
Answer: C
NEW QUESTION 14
In which of the following attacks is a malicious packet rejected by an IDS, but accepted by the host system?
- A. Insertion
- B. Evasion
- C. Fragmentation overwrite
- D. Fragmentation overlap
Answer: B
NEW QUESTION 15
Which of the following are the countermeasures against WEP cracking? Each correct answer represents a part of the solution. Choose all that apply.
- A. Using a 16 bit SSI
- B. Changing keys ofte
- C. Using the longest key supported by hardwar
- D. Using a non-obvious ke
Answer: BCD
NEW QUESTION 16
You are pen testing a Linux target from your windows-based attack platform. You just moved a script file from the windows system to the Linux target, but it will not execute properly. What is the most likely problem?
- A. The byte length is different on the two machines
- B. End of-line characters are different on the two machines
- C. The file must have become corrupt during transfer
- D. ASCII character sets are different on the two machines
Answer: A
NEW QUESTION 17
Which of the following best explains why you would warn to clear browser slate (history. cache, and cookies) between examinations of web servers when you've been trapping and altering values with a non-transparent proxy?
- A. Values trapped and stored in the browser will reveal the techniques you've used toexamine the web server
- B. Trapping and changing response values is beneficial for web site testing but usingthe same cached values in your browser will prevent you from being able to changethose value
- C. Trapping and changing response values is beneficial for web site testing but willcause browser instability if not cleare
- D. Values trapped and changed in the proxy, such as a cookie, will be stored by thebrowser and may impact further testin
Answer: D
NEW QUESTION 18
168.116.9 Is an IP address forvvww.scanned-server.com. Why are the results from the two scans, shown below, different?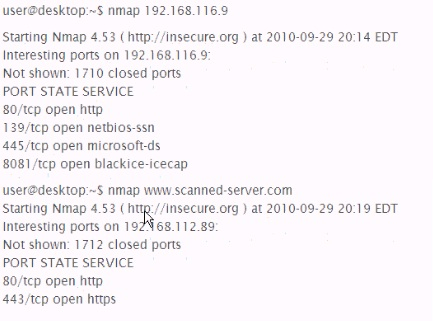
- A. John.pot
- B. John conf
- C. John.rec
- D. John.ini
Answer: C
NEW QUESTION 19
......
P.S. Easily pass GPEN Exam with 385 Q&As Surepassexam Dumps & pdf Version, Welcome to Download the Newest Surepassexam GPEN Dumps: https://www.surepassexam.com/GPEN-exam-dumps.html (385 New Questions)